Escalating Critical Security Events: Where Teams Fail
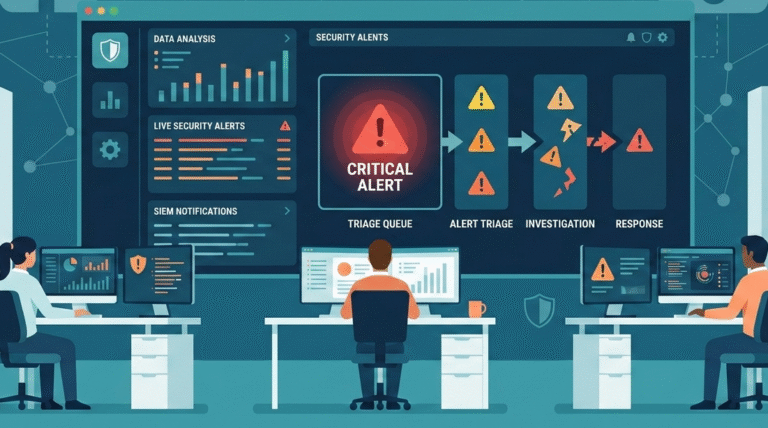
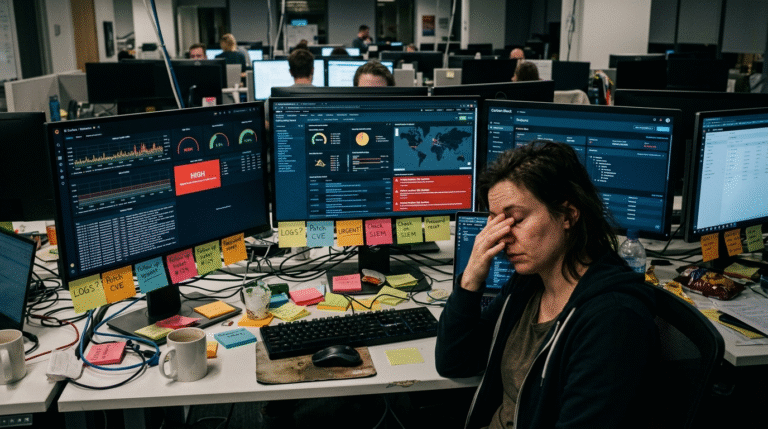
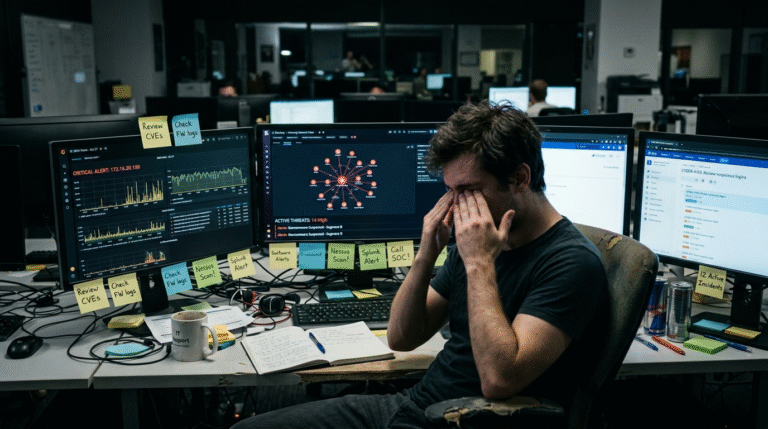
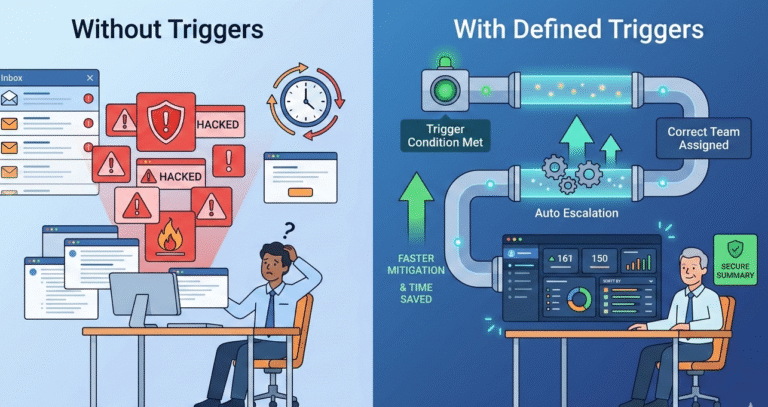
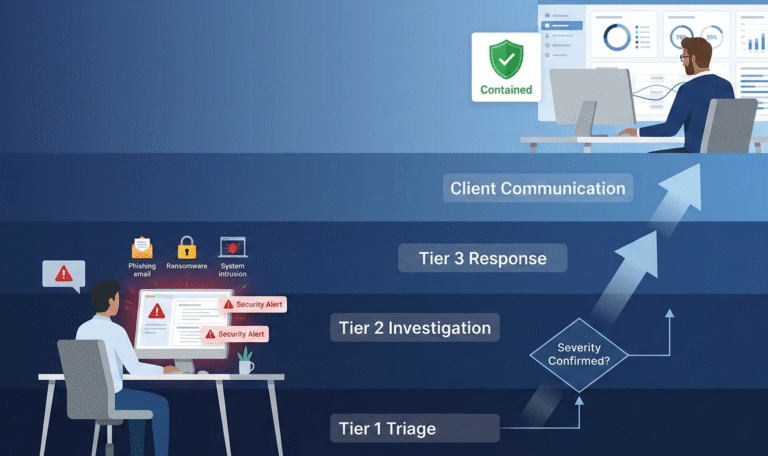
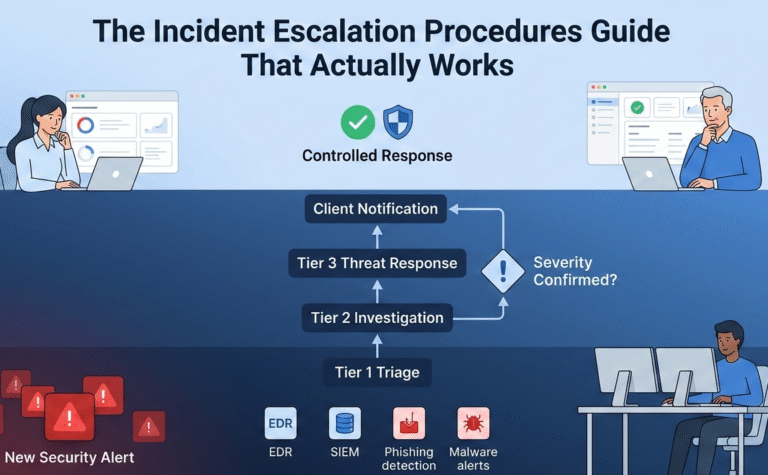
Your security tools are working. They’re generating the alerts. The real breakdown happens in the silent minutes after, when an analyst isn’t sure who should act. Most security incidents fail at escalation. Signals rot in queues while attackers, like SCATTERED…