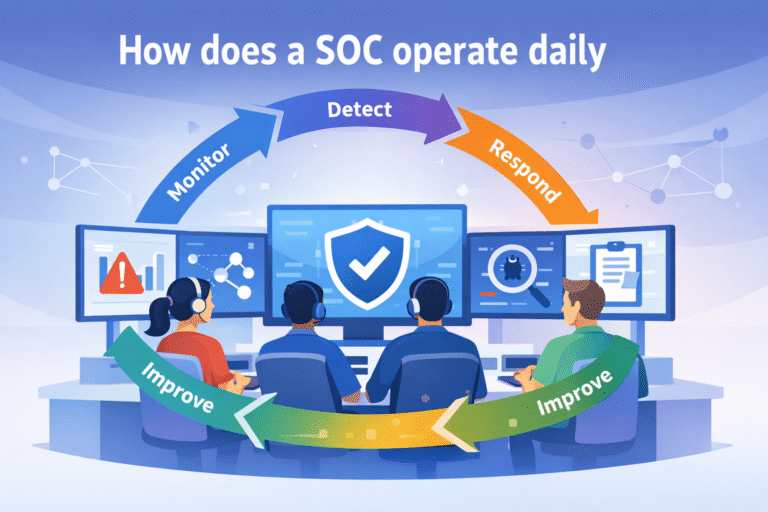
4 Habits Behind Optimizing Security Operations Workflow
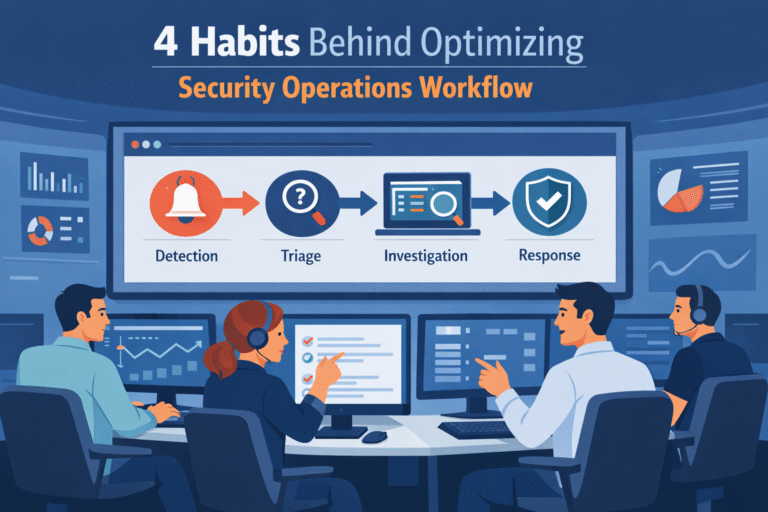
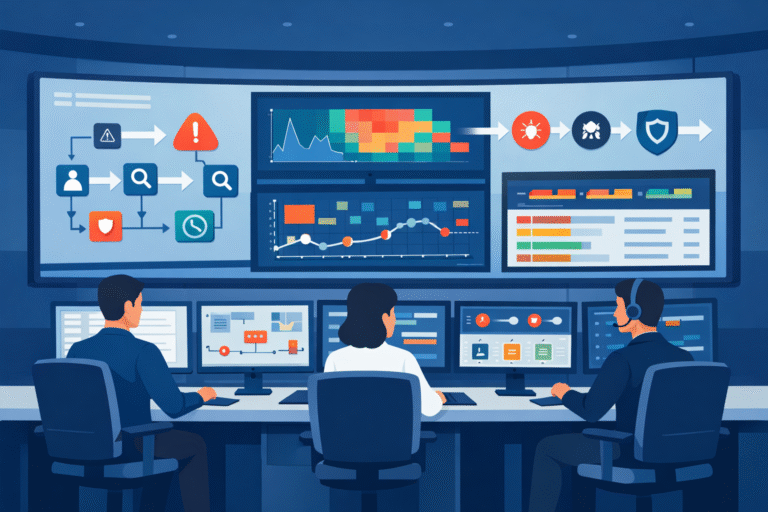
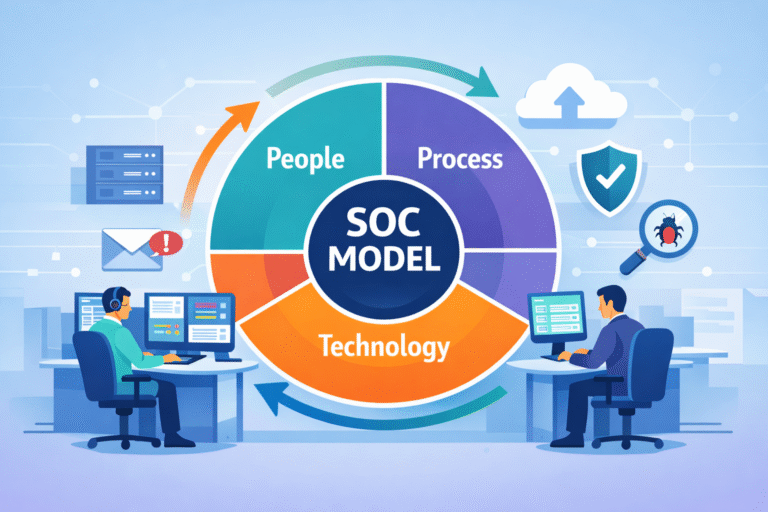
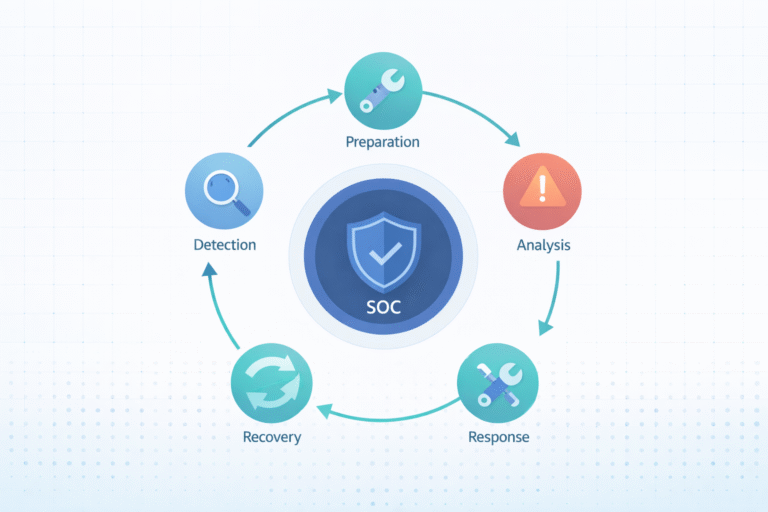
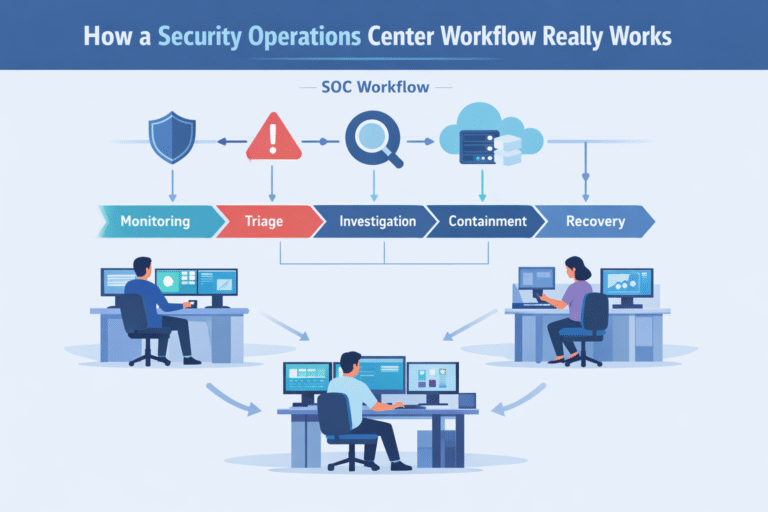
Optimizing security operations workflow starts with fixing the process, not blaming the analysts. When the workflow is unclear, teams lose time deciding what to check first. A clear path for each alert changes that. It tells analysts what comes next…