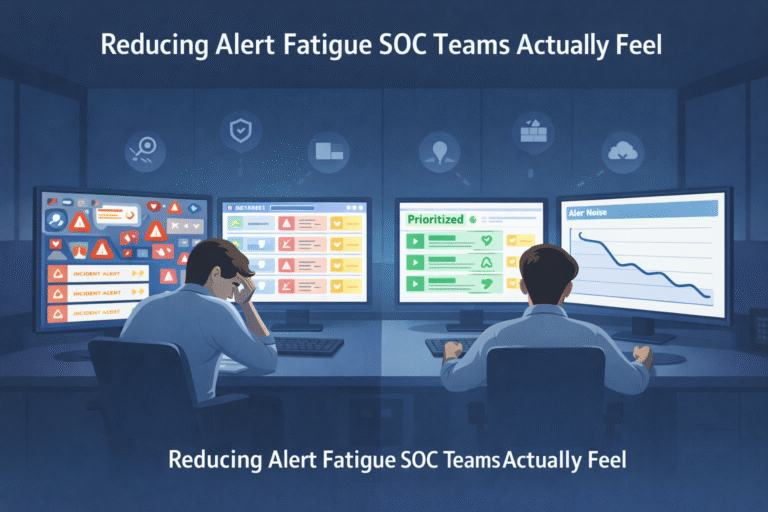
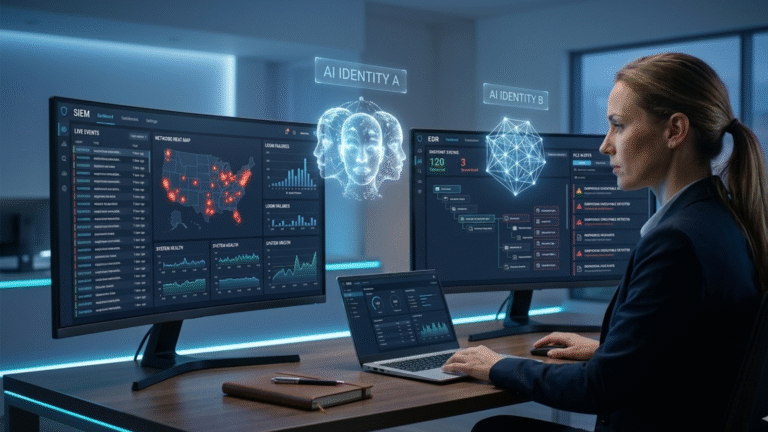
Using Threat Intelligence Triage to Cut Fatigue
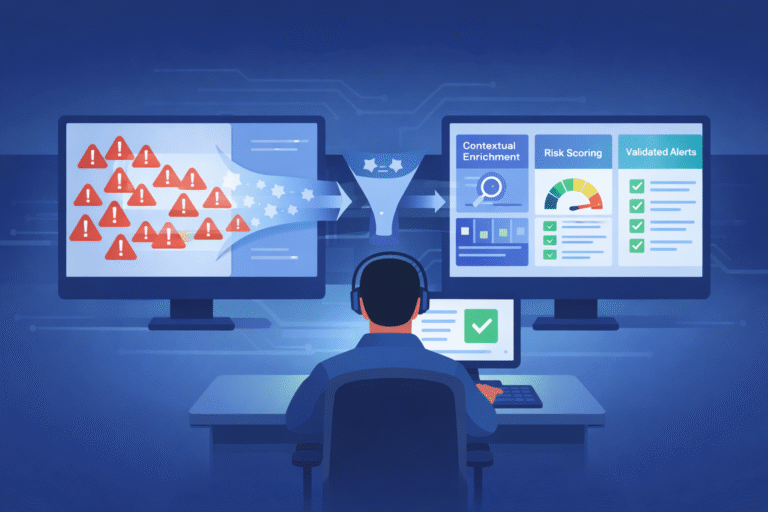
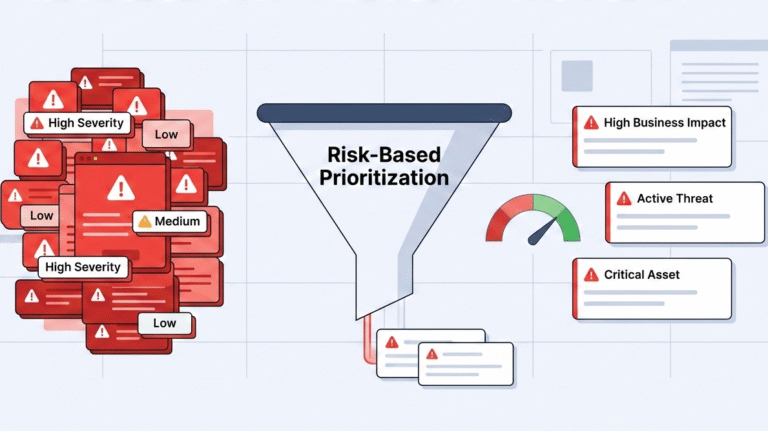
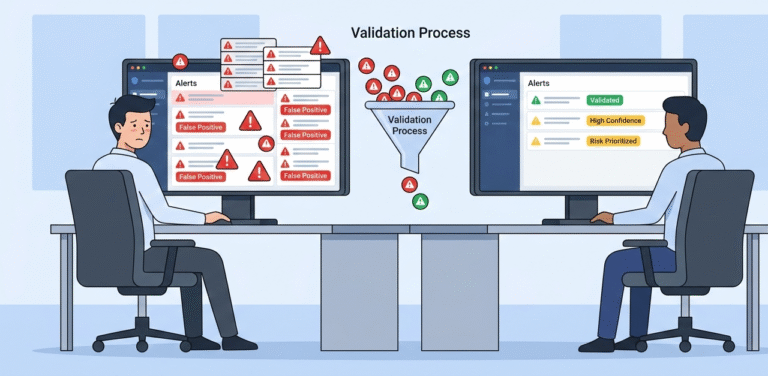
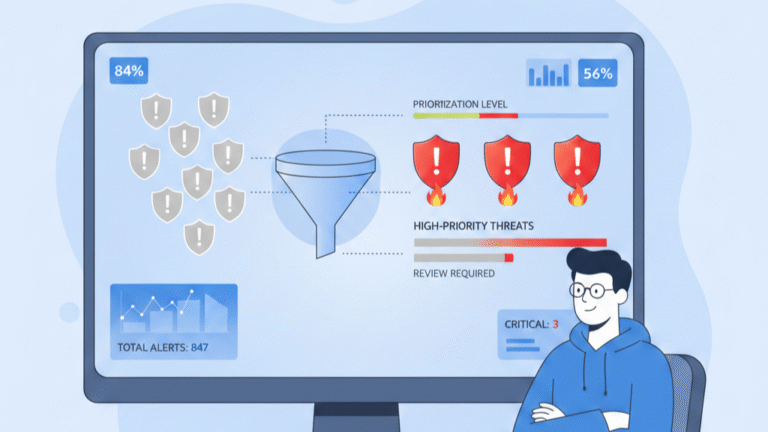
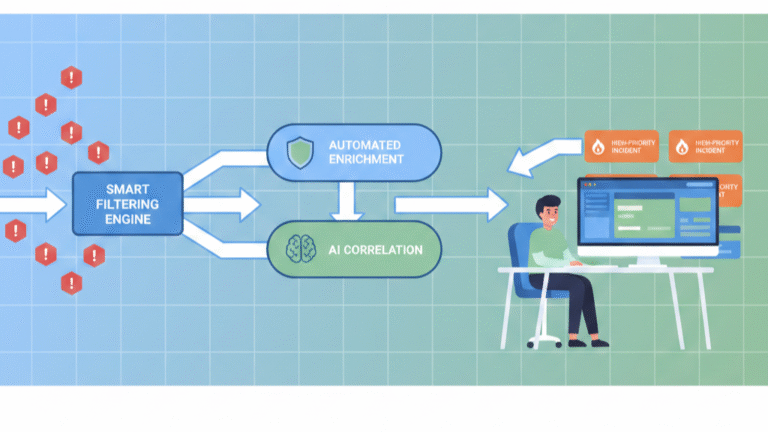
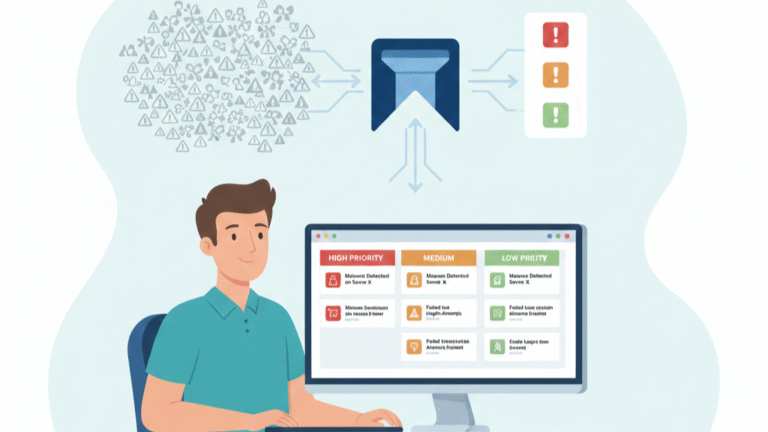
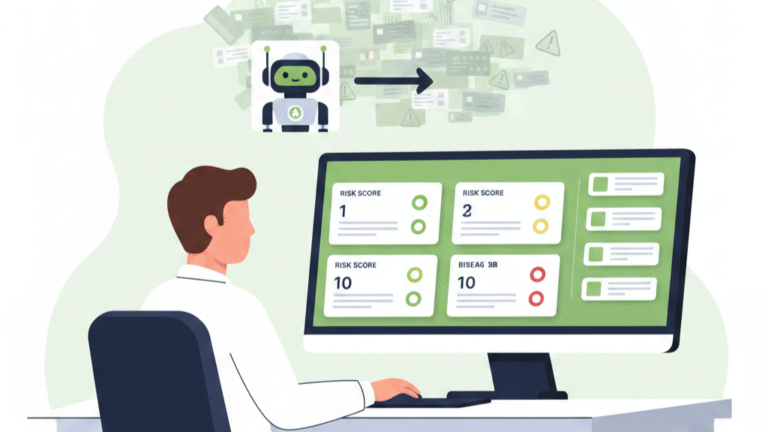
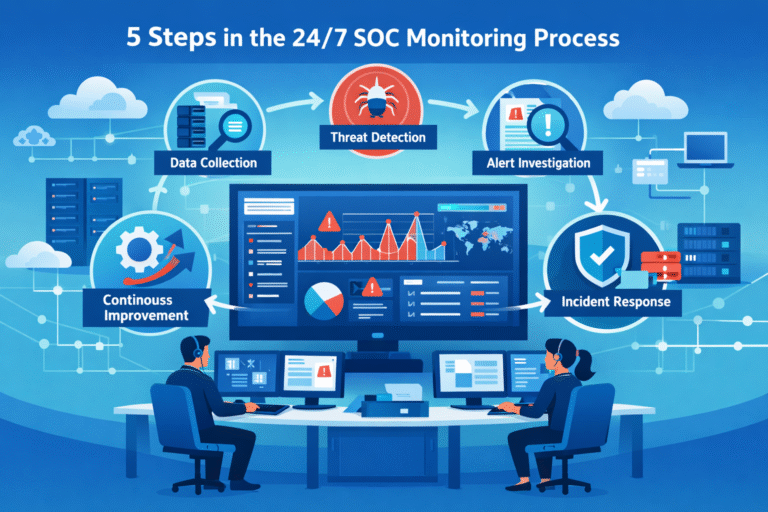
Using threat intelligence triage cuts through alert noise. It uses external data, like known malware or attacker methods, to quickly validate alarms. Good programs see false positives drop by 30%. This turns a flood of data into a short list…