Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
You just had another incident. The adrenaline is fading, leaving behind that familiar dread: the report. It feels like a blame assignment, a paperwork chore that never stops the same thing from happening again. We get it. A proper incident analysis reporting template isn’t about bureaucracy.
It’s a structured conversation with your future self, designed to replace chaos with clarity and fear with facts. It’s the tool that transforms reactive firefighting into proactive resilience. Keep reading to learn how to build one that your team will actually use, not just endure and know the incident analysis reporting template.
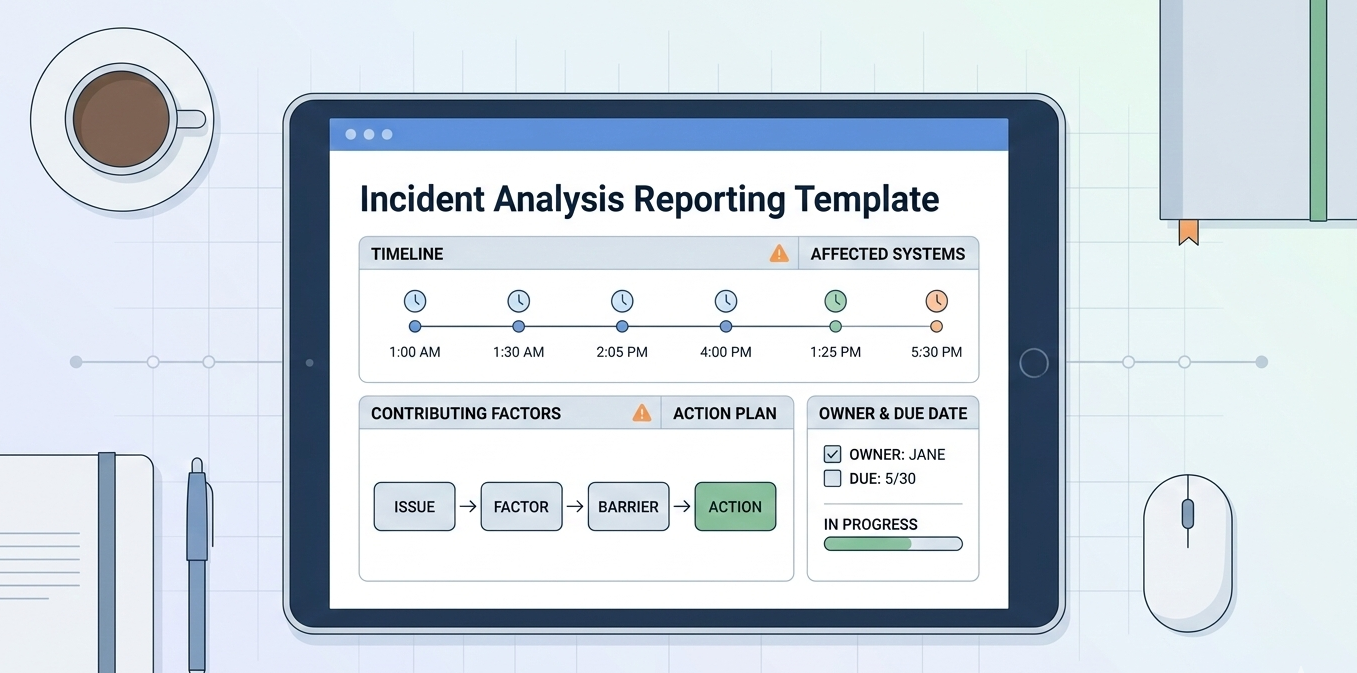
When the alert sounds, confusion reigns. A good template cuts through that. Its first job is to capture the cold, hard facts, creating a shared source of truth before memories blur.
“An Incident Report Template is a standardized document used to capture the details of security incidents. It helps organizations systematically address incidents and learn from them… Ensuring all relevant details of the incident are recorded [is crucial] for understanding its severity.” – Trio MDM Blog
Start with the basic who, what, when, and where. Follow structured incident investigation analysis stepsto capture precise timestamps and affected systems. This is the incident’s fingerprint.
Finally, quantify the impact. How many users? Minutes of downtime? Scope of data exposure? These numbers translate technical failure into business risk, speaking to leaders in a language they understand. This factual baseline makes everything that follows possible.
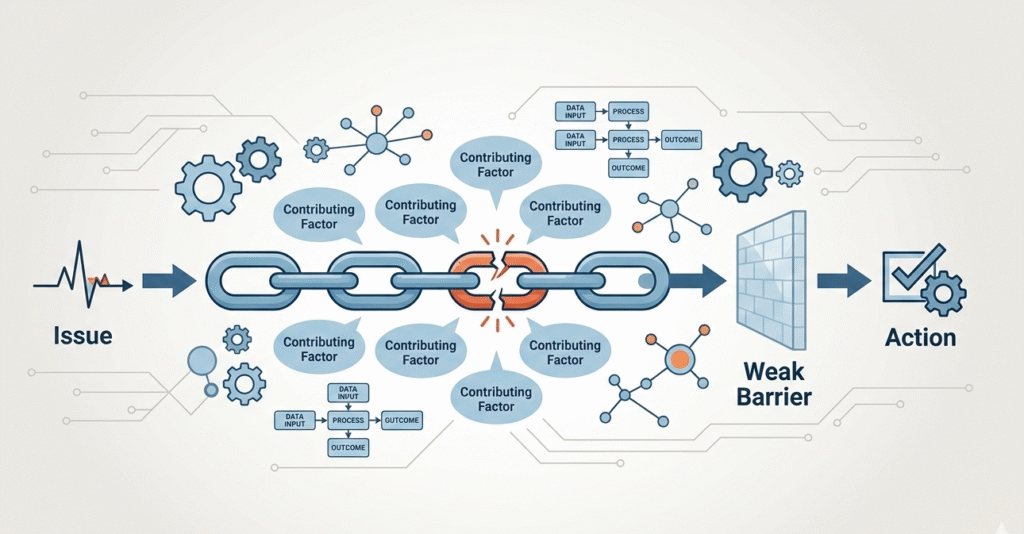
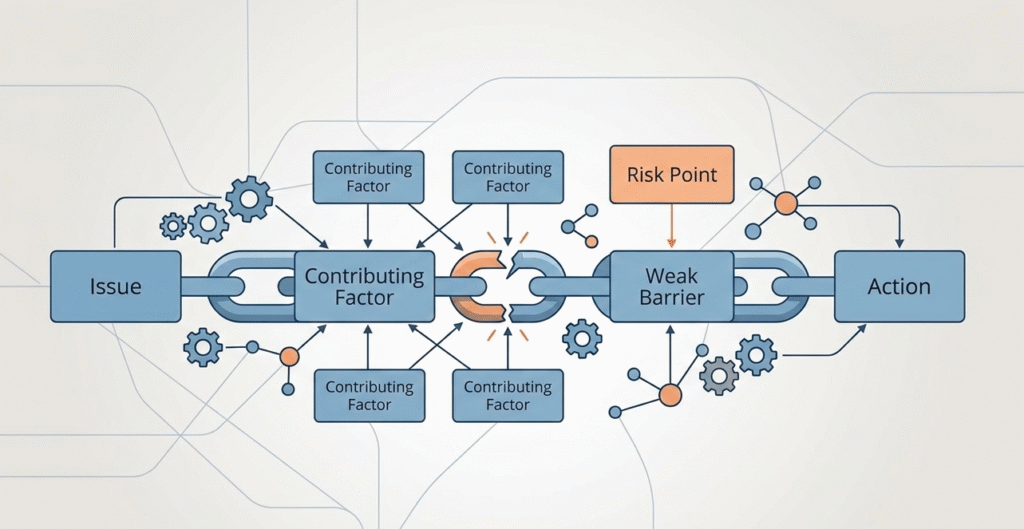
Chasing a single root cause can be a trap. In complex systems, failure is usually a chain of events. Your template should guide teams to uncover the full chain, the contributing factors that lined up.
The “5 Whys” technique is common, but it must be done rigorously. Don’t stop at the technical symptom. Server crashed from memory leak? Why? Bug in the purge job. Why? Untested deployment script. Why? Inadequate peer review. Now you’re improving process, not just patching code.
Another method is barrier analysis. For each step in your incident timeline, ask what defenses failed. Was the monitoring alert missing? Was the runbook unclear? This reveals systemic gaps in your safeguards. The goal is learning, not blaming. A template framed around “contributing factors” rather than “root cause” fosters this blameless investigation.
| Timeline Event | Immediate Issue | Contributing Factor | Failed or Missing Barrier | Preventive Action |
| 14:32 – Latency alert | Memory spike | Purge job bug | No automated memory threshold alert | Add memory alert at 85% usage |
| 14:35 – API errors | Service crash | Untested deployment script | No deployment checklist validation | Implement mandatory deployment checklist |
| 14:37 – Escalation delay | Slow response | Unclear ownership | Outdated runbook | Update runbook with on-call roles |
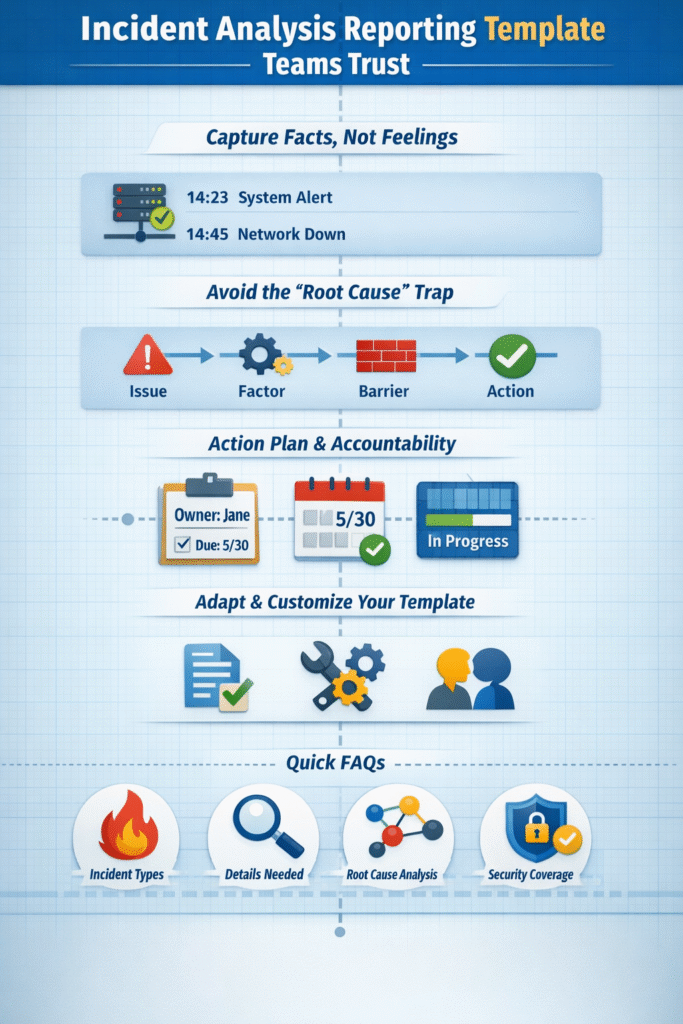
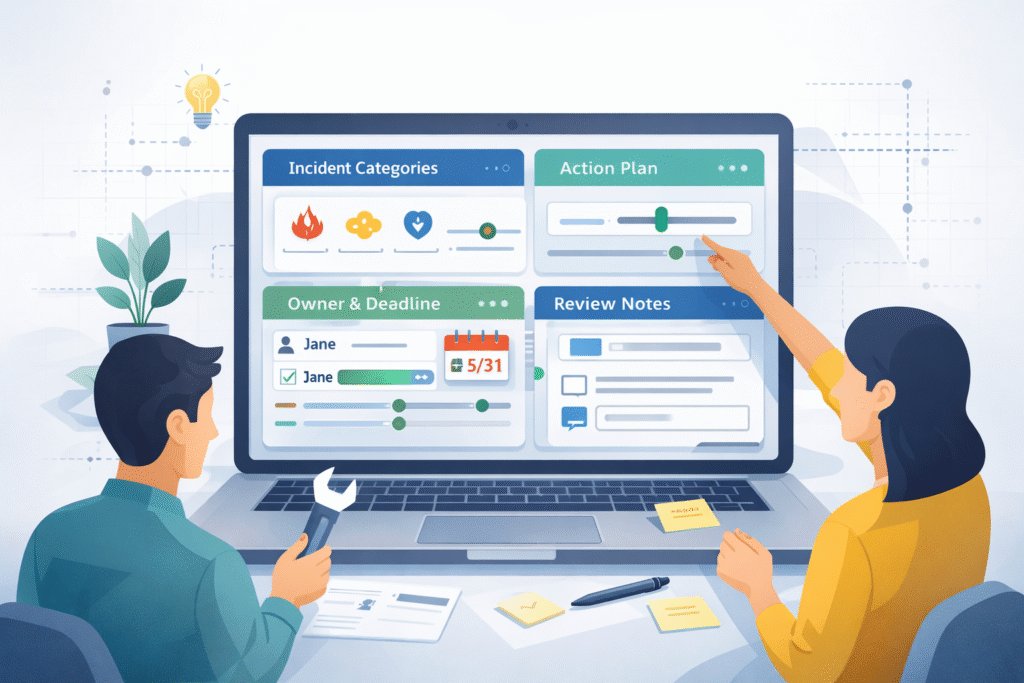
An analysis without follow-through is a waste of everyone’s time. When documenting incident investigation findings, the most vital part of your template is the action plan. This is where insight becomes improvement.
“Documentation is not optional and can be a life saver. If the incident is considered a criminal act, your documentation will be used to press charges against suspects… Documentation should answer the questions: Who, What, When, Where, Why, and How?” – Cynet Security Blog
Vague promises like “improve monitoring” are useless. Actions must be specific, assigned, and dated. “Implement Prometheus alert for cache memory >85% on Service X. Owner: Jane. Due: 5/30.” This creates real accountability.
We see teams succeed when they treat the report as a ticket generator. The action items feed directly into project trackers. The incident isn’t “closed” until the preventive fixes are validated. This closes the loop, proving the analysis mattered and building trust in the entire process.
We’ve reviewed dozens of incident reports from MSSPs evaluating new tools, and the same pattern shows up: generic templates miss the questions that actually matter. Instead of downloading a standard form, teams get better results when they shape the template around their own past incidents.
If the same clarification keeps coming up during audits, that should become a required field. In our consulting work helping MSSPs select and audit security products, we emphasize the importance of using SIEM EDR investigation data as one of the essentials
Culture matters just as much as structure. Templates should point to system breakdowns, not individual mistakes. When teams feel safe documenting missteps, the analysis gets sharper. The strongest templates we’ve seen work in two modes: quick logging during the incident, then deeper review once the pressure fades.
Start by listing your incident categories, from workplace incidents to security incidents and system incidents. A solid Incident Report Template should include clear input fields, incident timeline, affected systems, responsible parties, and a follow-up actions section.
Make sure it supports root cause analysis and corrective actions. Keep it simple, practical, and easy to update in formats like Google Docs, Microsoft Word, or Adobe PDF.
For workplace incidents, include worker injuries, occupational illnesses, property damage, near misses, or workplace violence. Document immediate actions, emergency response procedures, affected users or departments, and resolution steps. Add preventive measures and preventive actions to stop repeat issues.
An employee incident report should clearly show who was involved, what happened, and how safety teams will develop and implement improvements.
Root cause analysis strengthens incident management by moving beyond surface problems. Use methods like Five Whys, fault tree analysis, or barrier analysis during incident investigation.
Combine this with impact analysis and data aggregation for trend analysis. When you document findings in your incident report document template, you create clear corrective actions and follow-up actions that improve incident-management procedures over time.
A security incident report template should address information security risks such as encryption keys exposure, security level breaches, or broader system incidents. Include affected systems, incident timeline, immediate actions, and impact analysis.
If relevant, document external reporter details, incident channel communication, and email distributions. Clear change history and resolution steps help support a strong security incident management program.
An incident analysis reporting template, done right, isn’t paperwork, it’s the blueprint for a learning organization. It transforms “what happened” into “what we learned” and “what we’ll change,” building resilience with every challenge.
We offer expert MSSP consulting to streamline operations, reduce tool sprawl, and improve service quality. With 15+ years and 48K+ projects, we provide vendor-neutral selection, PoC support, stack optimization, and actionable guidance. Join us