SOC Analyst Daily Activities: Inside Modern Security Operations Centers

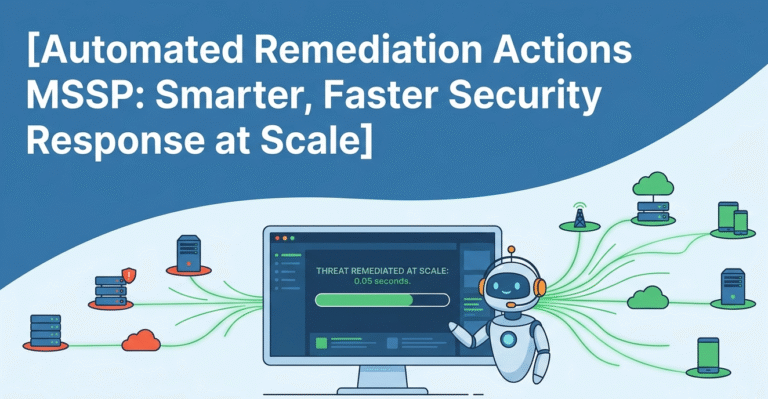
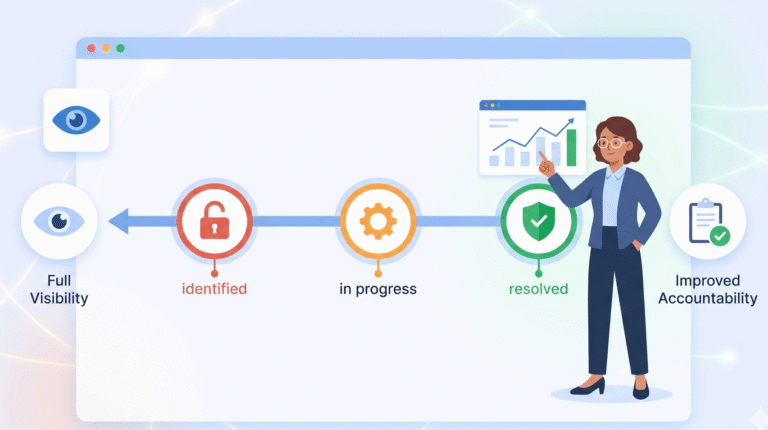
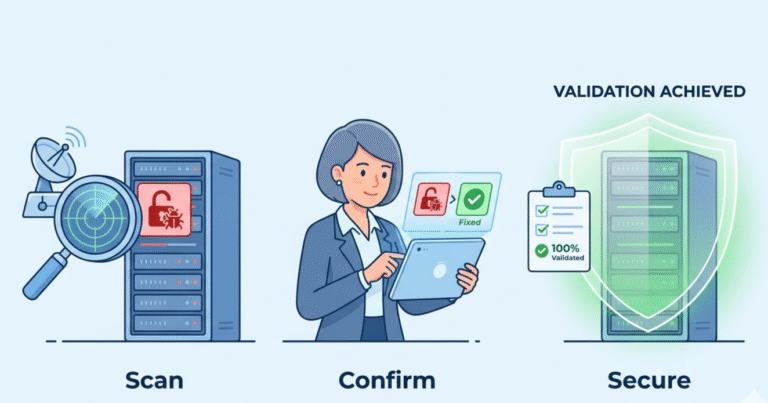
SOC analyst daily activities focus on monitoring security systems, investigating alerts, and responding to potential threats. In MSSP Security operations, we handle multiple client environments, so prioritization and accuracy are very important. Each day involves reviewing logs, checking alerts, and…