Creating Effective SOAR Playbooks: A Practical Guide for Modern Security Teams
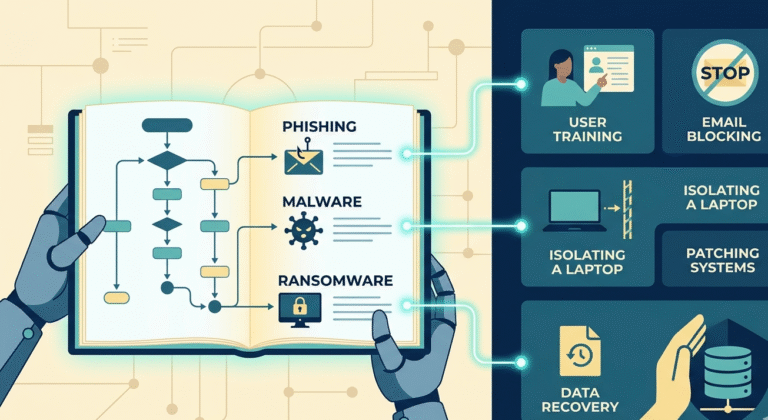
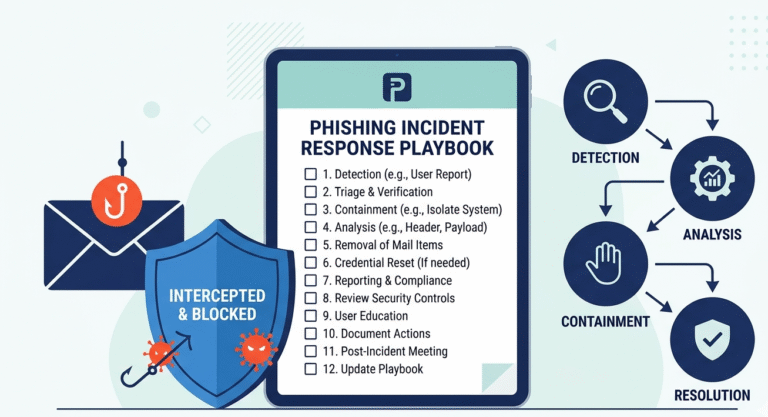
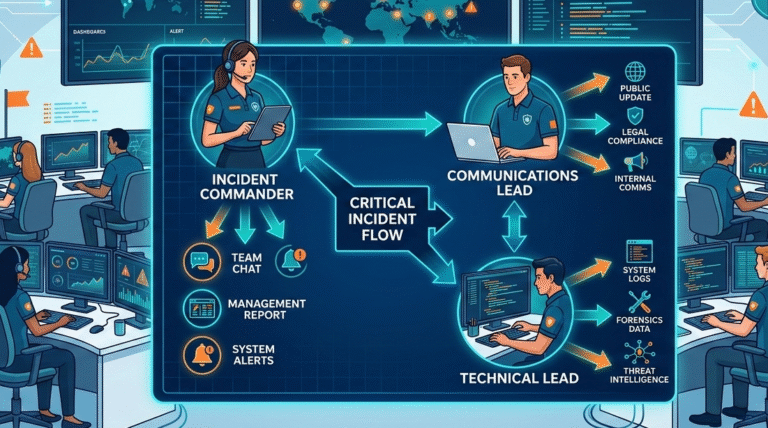
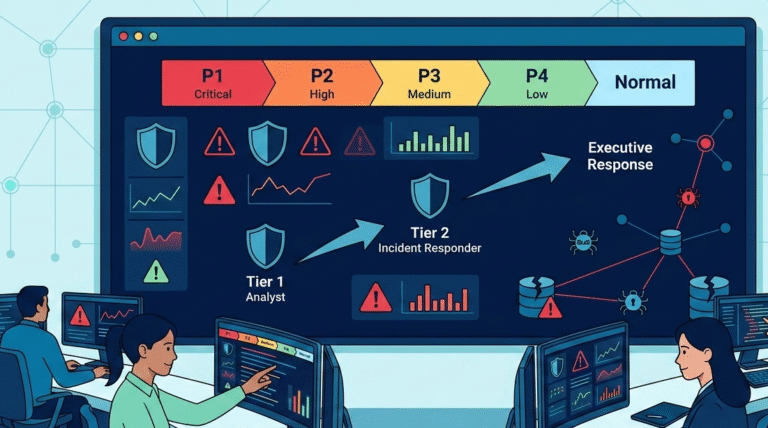
Security teams today face constant pressure to respond quickly while managing an overwhelming number of alerts. Without structure, response efforts often become inconsistent and inefficient. SOAR playbooks help solve this by turning complex processes into clear, repeatable workflows. From our…