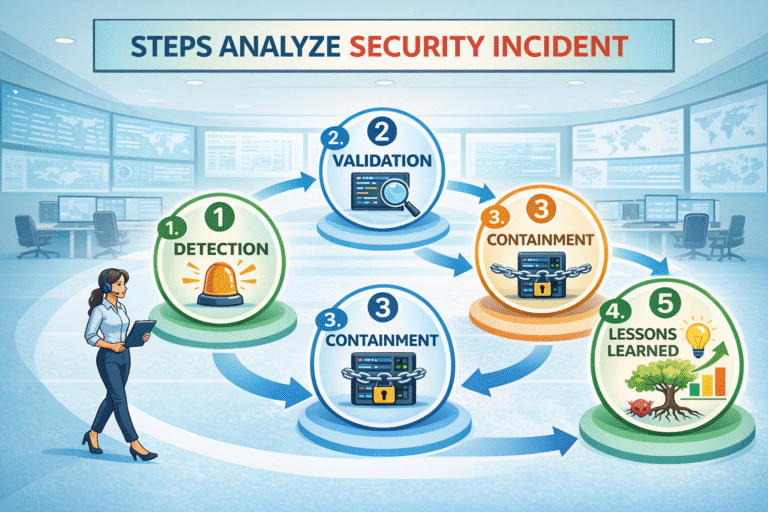
Why Documenting Incident Investigation Findings Matters
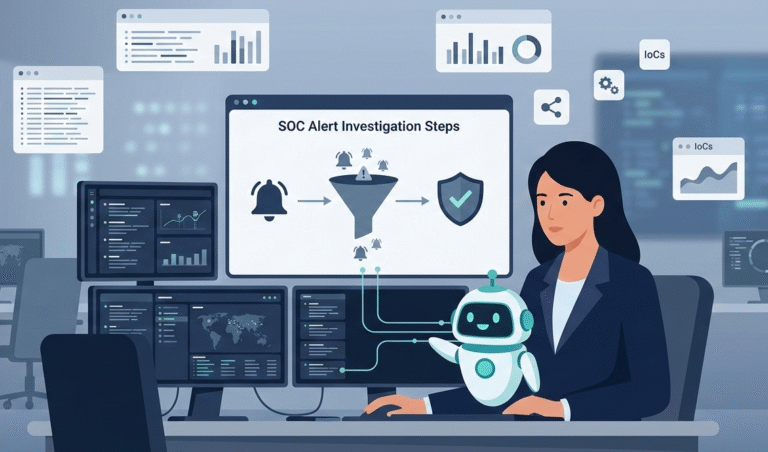
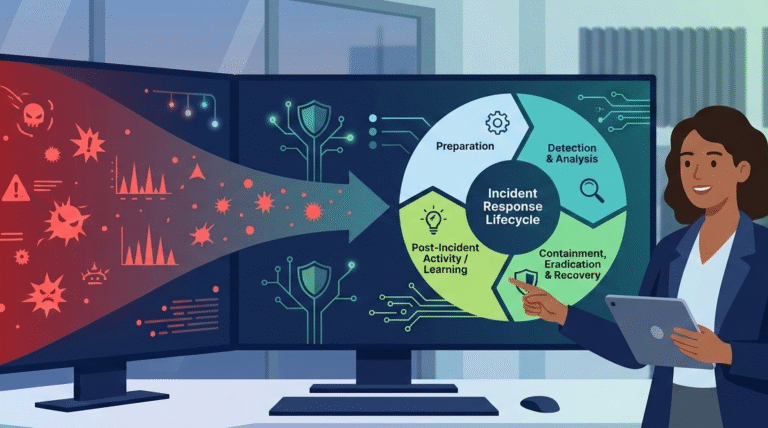
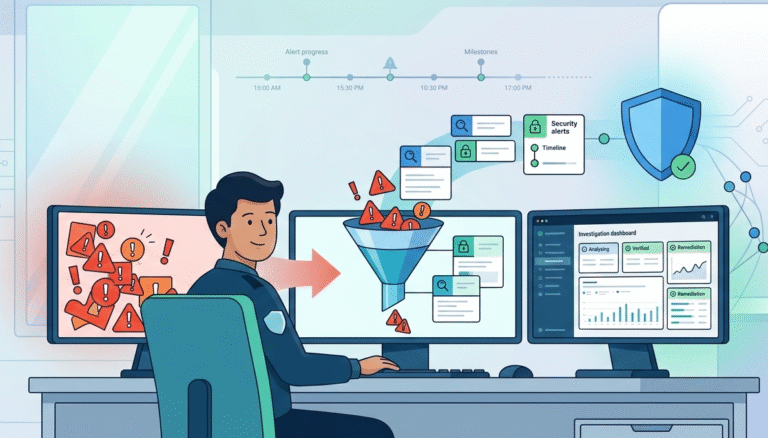
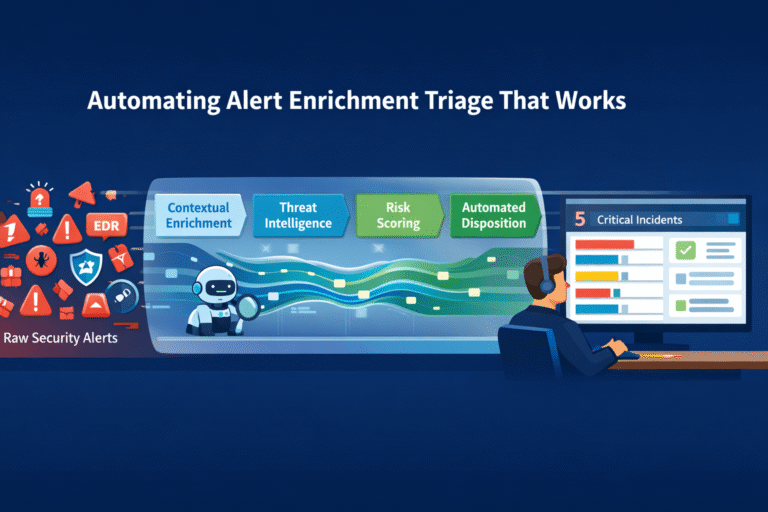
Documenting incident investigation findings does one essential thing: it turns a chaotic event into a structured plan for prevention. It’s the difference between reacting to a single failure and building a system that can’t fail the same way twice. A…