A security response playbook helps teams handle cyber incidents quickly and without confusion. When attacks happen, every minute counts, and unclear actions can make things worse. That’s why having a structured response process is essential.
This guide explains what a security response playbook is and how it improves security operations. If you want faster and more effective incident response and what is security response playbook, keep reading.
Key Insights: What is Security Response Playbook Essentials
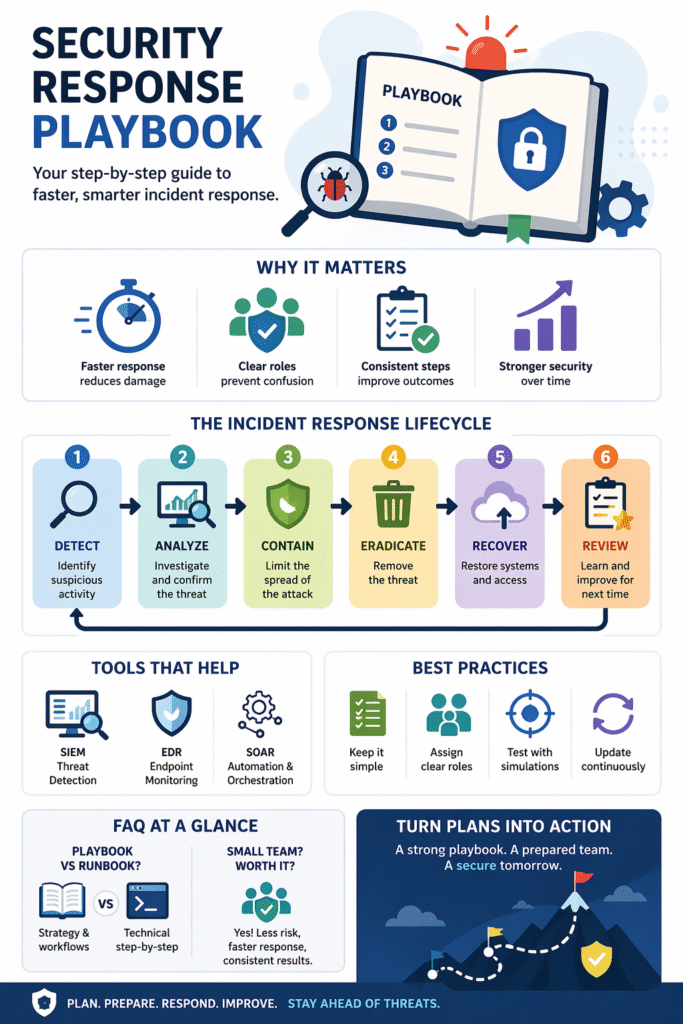
A security response playbook ensures teams act quickly, consistently, and with clear direction during incidents.
- Faster response reduces damage
- Clear roles prevent confusion
- Consistent steps improve outcomes
What Is a Security Response Playbook?
A security response playbook is a set of predefined, step-by-step instructions used to respond to cybersecurity incidents. It guides teams through each stage of an incident so they know exactly what to do.
“The goal of incident response is to handle the situation in a way that limits damage and reduces recovery time and costs.” – Wikipedia
Instead of reacting differently each time, teams follow a structured process that reduces delays and mistakes. Playbooks can be customized for different threats like a phishing incident response playbook, malware, or data breaches, making them practical for real-world use
Core Phases of a Security Response Playbook
Credits: NetworkExploit
Every playbook follows a simple lifecycle, often modeled after successful security response playbook examples used in the industry:
| Phase | What Happens |
| Detect | Identify suspicious activity |
| Analyze | Investigate and confirm the threat |
| Contain | Limit the spread of the attack |
| Eradicate | Remove the threat |
| Recover | Restore systems and access |
| Review | Learn and improve for next time |
Why Security Response Playbooks Matter
Without a playbook, incident response can be slow and inconsistent. Teams may miss critical steps or struggle with unclear responsibilities.
“A well-defined incident response capability allows an organization to respond to incidents in a systematic manner, ensuring that the appropriate steps are taken to minimize the impact on the organization.” – Journal of Cybersecurity and Information Management
A well-defined playbook helps:
- Reduce response time
- Minimize damage
- Improve team coordination
- Ensure repeatable processes
In high-pressure situations, having clear incident response playbooks makes a significant difference in how effectively a breach is contained.
Tools & Best Practices

To make playbooks effective, organizations rely on the right tools and approaches:
Common tools:
- SIEM for threat detection
- EDR for endpoint monitoring
- SOAR for automation
Best practices:
- Keep playbooks simple and clear
- Assign roles for each step
- Test regularly with simulations
- Update based on new threats
FAQ
What is the main purpose of a security response playbook?
The primary purpose is to standardize how security incidents are handled. It provides clear guidance so teams can act quickly, reduce uncertainty, and limit the impact of threats without relying on ad hoc decisions.
How often should security response playbooks be updated?
Playbooks should be reviewed regularly and updated whenever there are significant changes, such as new threat patterns, tool upgrades, or after major incidents. Continuous improvement ensures the playbook stays relevant and effective.
Can small organizations benefit from security response playbooks?
Yes, even small teams gain significant value. A well-defined playbook helps reduce mistakes, improves response speed, and ensures consistent handling of incidents without requiring large resources or complex systems.
What is the difference between a playbook and a runbook?
A playbook focuses on the overall incident response strategy, including decision-making, workflows, and coordination. A runbook is more technical and detailed, providing step-by-step instructions for specific tasks or system-level actions.
Security Response Playbook Conclusion: Turning Plans into Action
A security response playbook turns complex incident response into a clear and manageable process. By following structured steps, teams can act faster, reduce risks, and handle incidents with confidence. The key is simplicity, consistency, and continuous improvement.
If you want to strengthen your security operations and respond faster to threats, work with MSSP experts to build and optimize your security response playbooks.
References
- https://en.wikipedia.org/wiki/Computer_security_incident_management
- https://www.nist.gov/publications/computer-security-incident-handling-guide
