Inside an MSSP SOC workflow is a structured, always-on model that detects, triages, investigates, and responds to threats using people, process, and tools like SIEM, EDR, and SOAR. We see more organizations turning to MSSPs because building an internal SOC is expensive and talent is limited.
The market keeps growing as ransomware and compliance demands rise. In our work auditing MSSPs, we focus on what really happens behind the dashboards, from alert intake to post-incident lessons. This guide walks through how the workflow actually runs day to day. Keep reading to see how it works in practice.
Inside an MSSP SOC Workflow: Key Insights
- A modern MSSP SOC workflow follows a structured, NIST aligned lifecycle from detection to recovery, optimized for low MTTD and MTTR.
- Mature SOCs rely on AI driven triage, SOAR automation tools, and strong analyst shift handovers to reduce false positives and dwell time.
- MSSP Security combines 24/7 monitoring, compliance reporting, and scalable incident response without the cost burden of a full in house SOC.
Security Operations Center Workflow
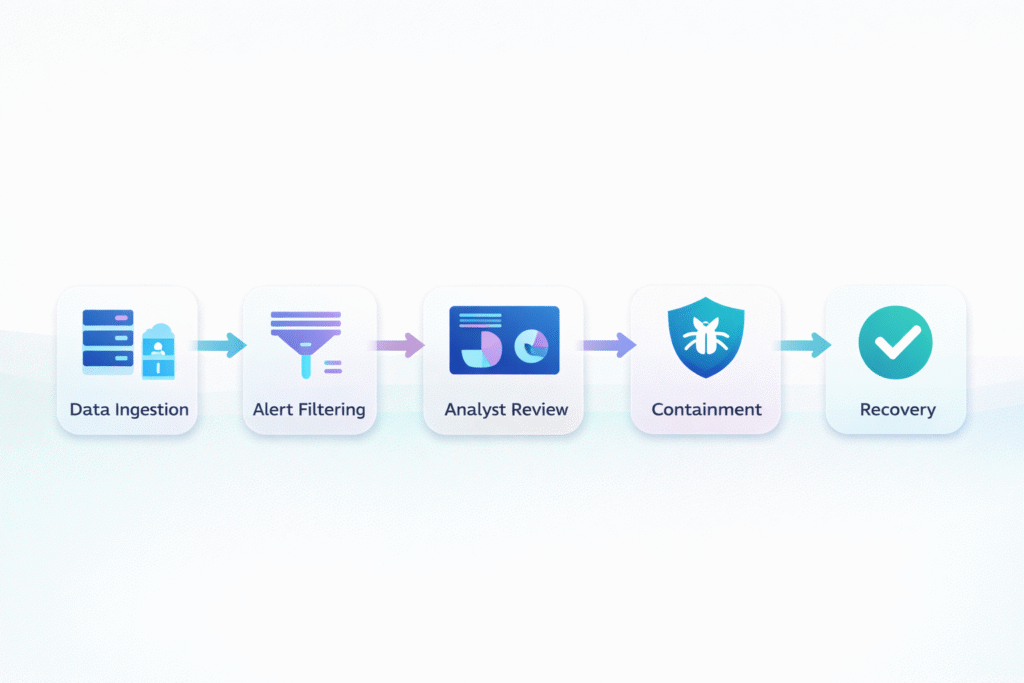
A security operations center workflow is simply a repeatable path: collect signals, validate what matters, escalate real threats, then recover systems while tracking how fast you did it.
In most SOCs we work with, the process starts with heavy log aggregation. Firewalls, endpoints, cloud workloads, and identity tools all stream events into a central pipeline. Industry research backs this up. Faster detection consistently reduces breach costs, so the early stages of the workflow carry real financial weight.
When we assess MSSPs in the field, the scale becomes obvious. Mid-sized environments often shrink millions of raw events into 500–5,000 alerts a day after filtering. We’ve seen what happens without structure.
Most mature SOC workflows still follow a clear backbone:
- Event ingestion and correlation
- Identification and alert validation
- Threat triage and severity prioritization
- Escalation across defined tiers
This structure keeps teams focused on outcomes. It shortens dwell time, supports measurable MTTD tracking, and helps MSSPs prove their process works under pressure.
MSSP SOC Process Flow Diagram
Most MSSP SOC diagrams look familiar. They follow a clear process flow diagram from detection to recovery, often shaped by frameworks like NIST On slides, the flow feels neat and predictable. In real operations, it’s messier. During our audits, we watch these diagrams play out in live environments.
Monitoring tools stream data into a SIEM, alerts appear, and automation kicks in fast. We’ve helped teams add enrichment layers that pull quick context, like unusual login times or rare outbound connections. In strong setups, this alone clears the bulk of false positives before an analyst steps in.
The stages rarely change, but what happens inside them does. Tool choices, integrations, and maturity all shape the outcome. Detection might rely on EDR or XDR stacks. Validation often leans on automation and light AI filtering. The real proving ground is later, when response begins.
That’s where we look closely:
- Can endpoints be isolated in seconds?
- Are clean backups ready to restore?
- Do playbooks hold up under pressure?
We tie each phase to KPIs and SLAs. A diagram should reflect a working promise, not just a clean drawing.
How Does A SOC Operate Daily
Credits: MyDFIR
A SOC runs on shifts, usually 24/7, reflecting how teams operate daily with rotations every 8 to 12 hours. The day often starts with a quick look back. Tier 1 analysts review overnight alerts, close obvious phishing cases, and open tickets that need deeper review. As noted by the research,
“A typical day for a SOC Analyst is dynamic and challenging, filled with various tasks to ensure the security of an organization’s information systems.” – SANS Institute
When something feels off, it moves up. Tier 2 analysts pull in endpoint and network data to add context. If a case turns truly complex, like suspected new malware, Tier 3 steps in with deeper analysis. We see this layered model in most MSSPs we audit, even though the tools and titles vary.
But daily SOC work isn’t just reacting to alerts. The quiet hours are filled with proactive tasks that keep risk down and posture steady. Strong teams use that time well, especially when supported by the right tooling choices.
Typical daily activities include:
- Threat hunting across logs and endpoints
- Reviewing identity access for zero-trust alignment
- Checking patch status on new vulnerabilities
One area we always examine is shift handover. Weak handoffs lose context fast. The better SOCs document open cases, note suspicious patterns, and flag audit needs so nothing slips between shifts.
Typical SOC Workflow Steps Explained
A typical SOC workflow follows a simple path: prepare, identify, contain, eradicate, recover, then learn. Preparation sets the tone. It’s not flashy, but it matters most.
| Stage | Primary Goal | Example Actions |
| Preparation | Ensure readiness before incidents | Test playbooks, validate backups, define roles |
| Identification | Detect and validate real threats | SIEM alerts, anomaly detection, triage filtering |
| Containment | Limit damage quickly | Isolate endpoints, disable accounts |
| Eradication | Remove root causes | Malware removal, patch vulnerabilities |
| Recovery | Restore normal operations | System restoration, integrity validation |
| Lessons Learned | Improve future response | Incident review, playbook updates |
Teams need tested playbooks, working backups, and clear roles. In our audits, weak prep almost always shows up later during incidents. Strong planning, on the other hand, makes response feel calm and controlled.
Once systems are ready, detection takes over. Modern stacks push logs into SIEM platforms, where automation and light AI help surface real anomalies. From there, the flow becomes action driven:
- Containment: isolate devices or lock accounts quickly
- Eradication: remove root causes, not just symptoms
- Recovery: restore clean systems and validate integrity
The last step is reflection. We always look for a real lessons-learned loop. Teams that review incidents, adjust playbooks, and refine tooling usually see response times shrink over time.
Security Incident Lifecycle SOC
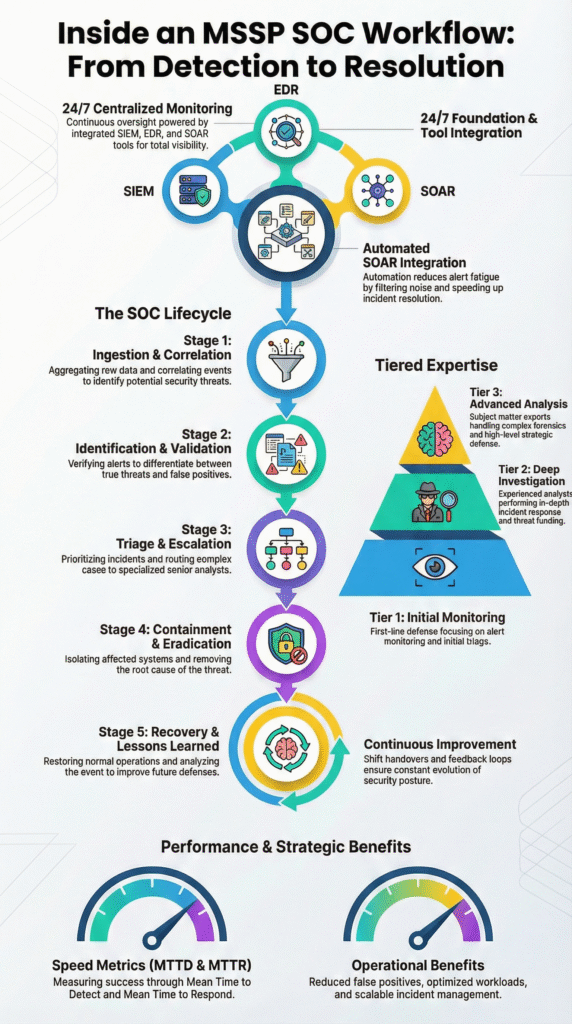
The security incident lifecycle in a SOC often mirrors frameworks like NIST, but in practice it’s all about measurement. Every phase gets tracked, from the first alert to the final report.
When we review MSSP operations, we look closely at how they define and measure each step. The lifecycle usually starts with alert validation, followed by severity scoring. That early decision shapes everything that follows, especially escalation paths.
Once severity is clear, response accelerates. High-impact incidents quickly pull in senior analysts and sometimes leadership. We’ve seen ransomware cases where minutes matter, and structure makes the difference.
Containment actions isolate the threat, eradication removes root causes, and recovery restores clean operations. Communication runs alongside all of this, especially for client-facing MSSPs.
Most teams track a few core metrics:
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Escalation accuracy
One area we always emphasize is the post-incident review. Teams that skip it often repeat mistakes. The strongest SOCs treat reviews as feedback loops that sharpen detection rules and improve future hunts.
Understanding SOC Operations Model
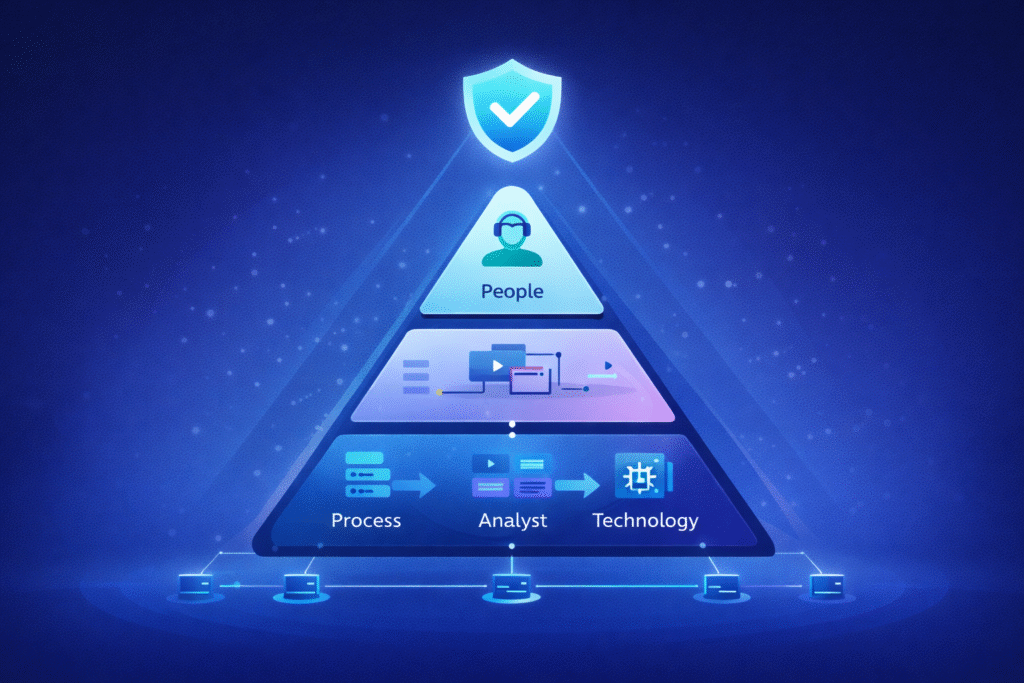
To understand a SOC operations model, it helps to look at three parts together: people, technology, and process. Miss one, and the model breaks down fast.
Many organizations try building internal SOCs, then run into staffing and cost pressure. The talent gap is real. That’s one reason we see more companies leaning on MSSPs instead of running everything in-house.
A mature model also blends defense with testing. Blue teams handle monitoring and response, while red teams simulate attacks to expose gaps. Some organizations add purple team exercises to connect both sides.
When done well, test results feed directly into daily detection rules. We often advise MSSPs to treat this feedback loop as part of product selection, not just a security exercise.
At scale, the model gets more complex:
- Monitoring multiple clients at once
- Managing compliance reporting
- Onboarding new tenants smoothly
From what we see in audits, strong MSSPs win through discipline. Tools matter, but governance matters more. Repeatable triage, clear reporting, and structured reviews let operations grow without quality slipping.
Visualizing SOC Monitoring Workflow
Visualizing a SOC monitoring workflow makes complex activity easier to follow. Instead of raw logs, teams see patterns. Dashboards usually combine feeds from SIEM platforms, endpoints, and cloud tools into one place.
But we’ve learned that visuals only help if the logic behind them is solid. In our audits, we often find dashboards that look impressive but hide weak correlation rules underneath.
Strong visualizations focus on clarity, not decoration. We help MSSPs shape views that show relationships between signals. For example, a firewall alert tied to an unusual login becomes more meaningful when shown together.
Matching activity against known indicators also adds fast context. The goal is helping analysts move from noise to understanding in seconds.
Effective dashboards usually highlight:
- Correlated events across tools
- Indicator matches and enrichment context
- Metrics like dwell time and response speed
When watching a live SOC dashboard, it feels less like charts and more like motion. Data turns into decisions quickly. That clarity helps analysts act faster and gives MSSP leaders something concrete to show when discussing SLAs or performance.
Optimizing Security Operations Workflow
Optimizing a security operations workflow usually starts with one problem: too much noise. False positives drain time and energy, and we see this in almost every MSSP assessment. Analysts get flooded with alerts that lead nowhere, which slows real response. As highlighted by Blog,
“Security analysts are currently overwhelmed by the number of security alerts they face each day. Increasingly complex and fragmented security infrastructures (too many point products from different vendors) are often the culprit.” – CSO Online
The first step is improving triage quality so fewer weak signals reach human eyes. Better triage often comes from smarter tooling choices. Behavioral analytics and UEBA can filter out obvious anomalies that aren’t real threats. After that, automation plays a bigger role.
We’ve helped MSSPs test SOAR workflows that handle routine actions automatically, like isolating endpoints or collecting artifacts. When done right, these changes noticeably shrink response times.
Optimization tends to revolve around a few levers:
- Detection rule tuning and cleanup
- Automation for repeatable playbooks
- Regular maturity reviews
One pattern we see is that strong teams treat optimization as ongoing work. They revisit incidents, refine detection logic, and test controls through hunting or purple exercises. Over time, that steady tuning leads to faster containment and cleaner investigations.
24/7 SOC Monitoring Process
A 24/7 SOC monitoring process is really about continuity. Threats don’t follow office hours, so coverage can’t either. Most MSSPs run overlapping shifts to keep visibility steady across time zones. We often pay close attention to how those shifts connect, because weak handovers quietly create gaps even when staffing looks strong on paper.
The monitoring itself never pauses. Data streams in constantly from networks, endpoints, and cloud platforms. In mature environments, that data is enriched in real time with external threat intelligence.
We’ve helped MSSPs evaluate integrations that make this enrichment useful instead of noisy. When done well, analysts get context fast without digging through multiple tools.
Strong 24/7 models usually depend on:
- Clear shift handover routines
- Defined escalation paths
- Enforced SLA targets
For MSSPs, this model becomes the core service layer. Continuous coverage shortens attacker dwell time and creates a reliable audit trail. We often remind clients that always-on monitoring isn’t just a feature anymore. It’s the baseline expectation for modern security operations.
FAQ
How does an MSSP SOC workflow handle false positives at scale?
A mature MSSP SOC workflow reduces false positives through layered filtering and smarter threat triage steps. Analysts use event correlation rules, AI-driven triage, and behavioral analytics to filter weak alerts early. Continuous tuning, UEBA insights, and clear severity prioritization help reduce fatigue. Over time, this improves dwell time and creates a cleaner, more reliable alert investigation flow.
What makes 24/7 SOC shifts sustainable for long-term operations?
Sustainable 24/7 SOC shifts rely on strong handovers and clear escalation paths. Teams rotate across tiered roles, including Tier 1 monitoring, Tier 2 investigation, and Tier 3 deep analysis. Automation, structured ticketing, and clear IR team coordination reduce burnout. When processes are consistent and communication is strong, teams can maintain continuous monitoring without sacrificing response quality.
How do SOC teams measure success beyond MTTD and MTTR?
Strong SOC teams look beyond MTTD and MTTR when measuring success. They also track dwell time, false positive rates, and escalation accuracy. Many use KPI dashboards to monitor containment speed and investigation quality. Some teams also measure automation impact and communication clarity to ensure the security operations center process delivers real operational value.
Where does threat hunting fit inside the incident detection lifecycle?
Threat hunting expands the incident detection lifecycle by looking beyond triggered alerts. Teams use SIEM analysis, XDR threat hunting, and IOC matching to uncover hidden activity. Red and purple team exercises often guide improvements. These efforts strengthen detection logic and help analysts validate alerts faster as threat actor behaviors evolve.
How do MSSPs balance compliance with operational scalability?
MSSPs balance compliance and scale by standardizing workflows across clients. They align monitoring with regulatory frameworks while keeping operations efficient. Many combine compliance reporting, audit trails, and cloud posture checks into repeatable processes. This approach supports growth while maintaining governance, allowing outsourced SOC models to stay both scalable and accountable.
Inside an MSSP SOC Workflow: What It Means for You
Inside an MSSP SOC workflow, structure, automation, and human expertise work together to detect threats faster and recover with precision. When done right, the workflow moves beyond monitoring into disciplined, measurable defense. For MSSPs refining their model or stack, execution matters more than theory.
We offer consulting tailored for MSSPs, from product selection to stack optimization and integration clarity. With deep field experience and proven frameworks, we help teams align tools with outcomes. Explore how MSSP Security can support your SOC strategy.
References
- https://www.csoonline.com/article/569483/managing-risk-resources-and-results-with-soar-solutions.html
- https://www.sans.org/blog/how-to-become-a-soc-analyst
Related Articles
- https://msspsecurity.com/security-operations-center-workflow/
- https://msspsecurity.com/mssp-soc-process-flow-diagram/
- https://msspsecurity.com/how-does-a-soc-operate-daily/
- https://msspsecurity.com/typical-soc-workflow-steps-explained/
- https://msspsecurity.com/security-incident-lifecycle-soc/
- https://msspsecurity.com/understanding-soc-operations-model/
- https://msspsecurity.com/visualizing-soc-monitoring-workflow/
- https://msspsecurity.com/optimizing-security-operations-workflow/
- https://msspsecurity.com/24/7-soc-monitoring-process/
