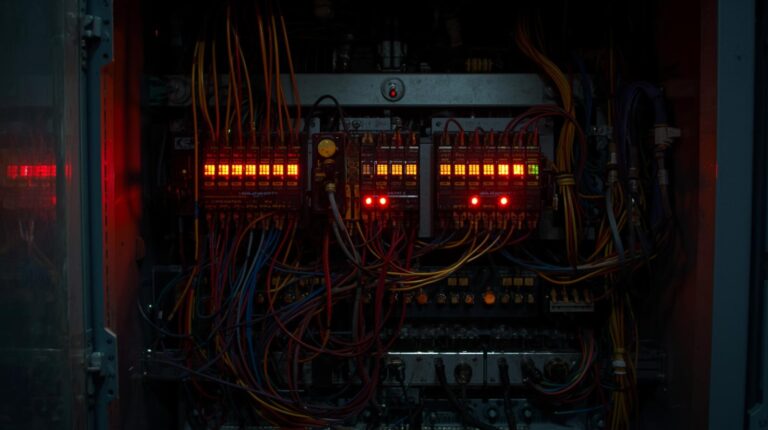
Purdue Model Security Monitoring Shields Your Industrial Network

The Purdue Model security monitoring is a practical blueprint for industrial security. It segments your operational technology into clear zones, creating defensible layers. This gives you the visibility to spot problems before they escalate. Forget the abstract theory. This guide…