Security Awareness Training Management Cuts Phishing Clicks by 86%
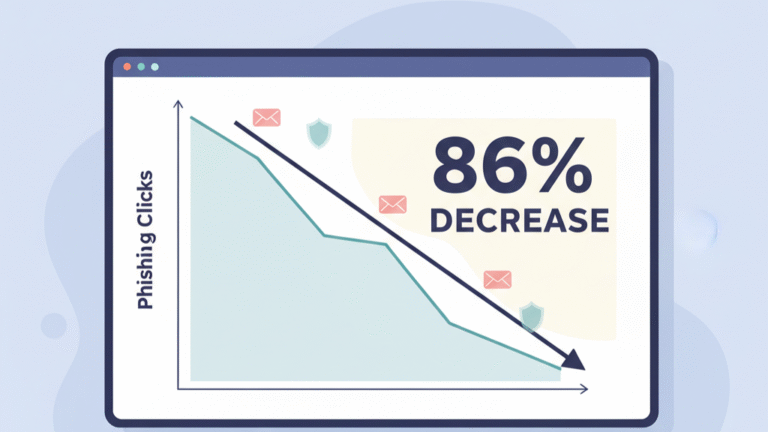
Yes, training works. Consider this: in one year, consistent security awareness training management reduced the average phishing click rate from 33% to just 4%, based on data from over 67 million simulations. That’s an 86% improvement. The goal isn’t to…