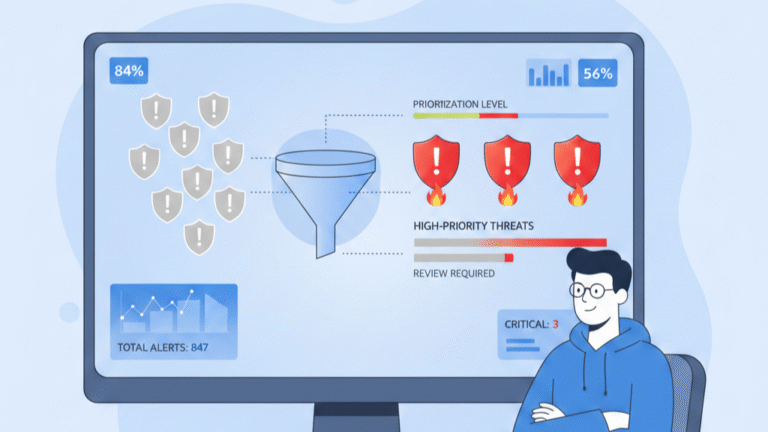
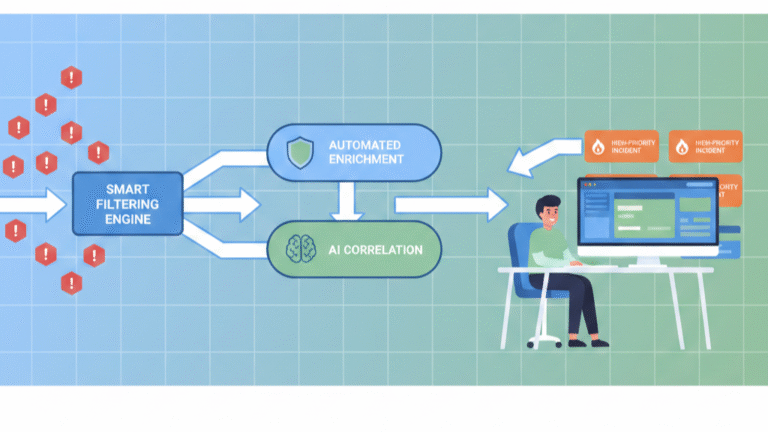
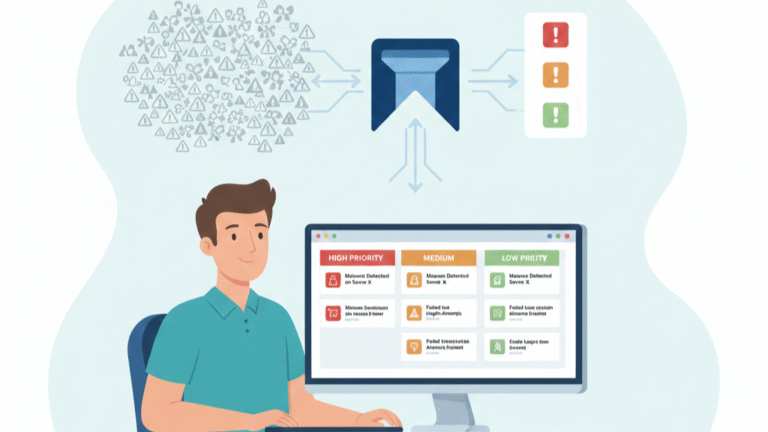
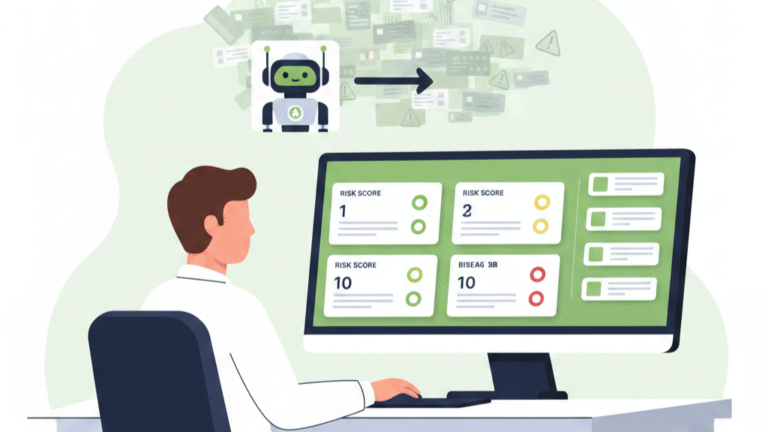
Defining Alert Severity Levels That Reduce Noise

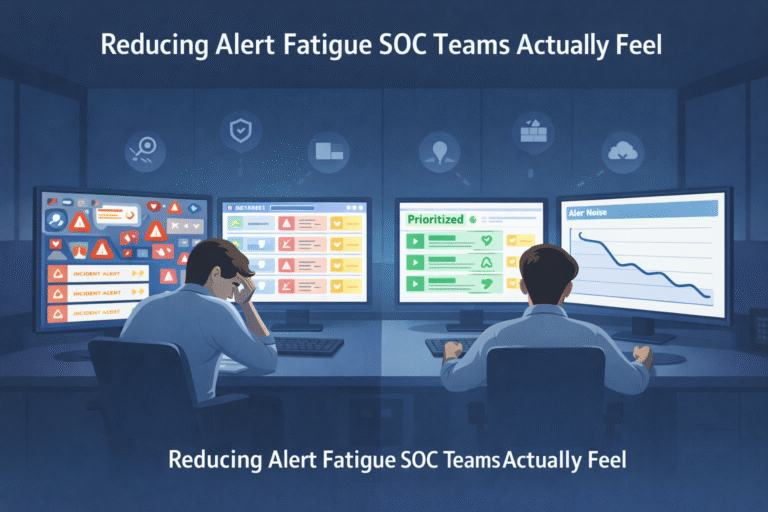
You’re woken up at 3 a.m. by a blaring alarm. Your heart races. Is it a full-blown data breach or just a server hiccup? Without a clear system to tell the difference, every alert feels like a five-alarm fire. That’s…