Your SOC is overwhelmed, and the traditional “first in, first out” alert queue is failing you. The answer isn’t more analysts. It’s a smarter alert triage prioritization process. By embedding context and risk scoring directly into the workflow, you transform chaos into a manageable, defensible system.
This approach slashes mean time to respond (MTTR), dramatically reduces analyst burnout, and ensures the most critical threats never get buried. We’ve seen it turn teams from reactive firefighters into proactive hunters. The methodology is proven, and the tools exist. Here’s how to rebuild your process from the ground up.
Strategic Insights
- Context Matters: Raw alerts are just noise. Automatically enrich alerts with threat intelligence, asset value, and user context before analysts review them. This turns confusion into clarity.
- Prioritize by Business Risk: Don’t rely only on Critical/High/Medium/Low labels. Use risk scoring based on asset importance, attacker behavior, and business impact to focus on what truly matters.
- Automate Routine Work: Automate Tier-1 validation, enrichment, and common false-positive closures. This frees senior analysts to handle complex, high-risk incidents where human judgment is essential.
The Broken Queue: Why “First In, First Out” Fails MSSPs

We’ve all lived it. The SIEM dashboard blinks red, a relentless stream of alerts from dozens of client environments. EDR pings, cloud configuration warnings flash, phishing reports stack up. The team operates on instinct, tackling whatever landed most recently, hoping nothing critical slips through.
This isn’t a process, it’s chaos. Industry data confirms the crisis: 62% of alerts are disregarded, and 55% of teams have missed critical threats due to poor prioritization. The cost isn’t just operational, it’s reputational. Every missed SLA erodes client trust. The old model, built for hundreds of daily alerts, collapses under thousands.
It creates a constant state of triage, where the goal is just to keep up, not to get ahead. Analysts burn out, institutional knowledge walks out the door, and the business can’t scale. Something fundamental has to change in how we decide what to work on first.
MSSP Alert Triage Process Explained
A mature mssp alert triage process explained is a multi-stage pipeline designed for consistency across clients and security systems. It converts raw signals into actionable intelligence for incident response teams.
Core stages:
- Deduplication: Correlate alerts from network monitoring systems, endpoint detection tools, and cloud environment sources to reduce noise.
- Automated enrichment: Pull contextual information from identity platforms, threat repositories, and asset inventories.
- Behavioral analytics: Apply anomaly detection and behavioral analysis to highlight real cyber threats.
- Human review: AI SOC analysts and Level 1 (L1) staff validate findings before alert escalation to Level 2 (L2).
This structured alert management model shortens response timelines, improves team coordination, and ensures security professionals focus on meaningful response activities rather than repetitive noise.
How Security Alerts Are Prioritized
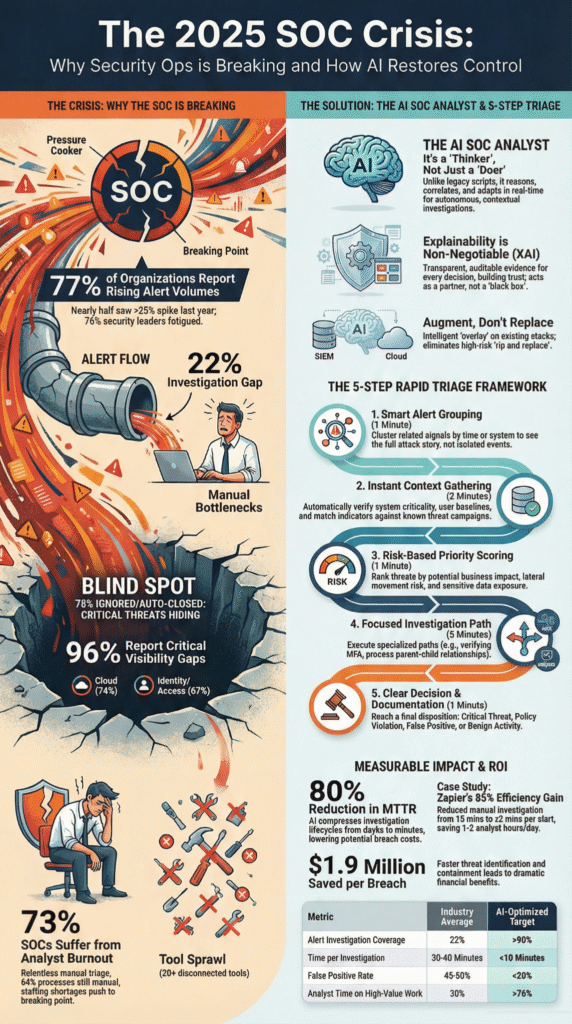
Credits: ForeverAnonymus
Effective prioritization depends on risk scoring, not vendor severity labels. Mature Security Operations Centers score alerts using business impact and likelihood derived from threat data and contextual information.
| Factor | What It Measures | Data Sources | Impact on Response |
| Asset Criticality | Business value of affected system | CMDB, identity platforms | Drives alert thresholds |
| Detection Confidence | Strength of detection technologies | EDR, intrusion detection systems | Guides alert escalation |
| Threat Context | Known malicious indicators | threat intelligence platforms | Improves threat detection |
| Exposure Level | External attack surface risk | cloud environment, S3 buckets, security group | Shapes response timelines |
Risk-based alert categorization helps security teams improve response times, reduce alert fatigue, and strengthen overall security posture.
Building a Process That Fights Fatigue
Reducing alert fatigue soc is a priority because repetitive investigations push security professionals into burnout. Repetitive investigations, constant context switching, and noisy security tools push security professionals into burnout. The fix is process design, not just hiring.
“The process begins the moment an alert lands. Analysts need to verify if the signal is real or just noise. Once analysts validate the alert, they classify it… Analysts prioritize the threat based on possible exposure, the asset involved, and available threat intelligence. Early classification shapes everything that follows and helps the team avoid wasting time on false positives or low-impact events.” – Legit Security
Modern Security Operations Centers reduce fatigue by embedding Artificial Intelligence, automated tuning, and automated analysis directly into alert triage. AI SOC analysts powered by generative AI and LLM technology handle repetitive review, while humans focus on threat hunting and complex incident response.
Strong investigation checklists, security training, and regular training and drills also improve confidence and reduce cognitive load. When response activities are clear and response timelines predictable, security teams stay sharp and incident lifecycle management becomes sustainable.
Security Alert Validation Techniques
Before prioritization, security alert validation techniques act as the quality gate. Mature incident response systems filter noise using layered automated investigation features, which should be part of a regular mssp alert handling process review to ensure the system remains effective against new threats.
Key validation controls:
- Reputation checks: Query threat intelligence platforms and threat repositories for IPs, hashes, and domains.
- Behavioral analytics: Compare activity against baselines from network monitoring systems.
- Sandboxing & Packet capture: Validate suspicious files and Network connection summaries.
- Platform correlation: Use Graylog Security, Sigma rules, and platform-specific saved searches to confirm detections.
Strong alert validation improves anomaly detection accuracy, reduces false positives, and accelerates alert escalation decisions. The result is cleaner alert management and faster, more confident incident response.
Defining Alert Severity Levels
Clear severity definitions align incident categorization across clients and security vendors. Mature MSSPs map severity directly to risk scoring and response timelines.
Critical alerts indicate confirmed cyber threats affecting high-value assets and require immediate incident response. High severity reflects strong threat detection signals needing urgent review. Medium covers suspicious activity requiring investigation, while Low includes informational events and known benign patterns.
“Not all alerts deserve equal attention. Prioritize based on actual risk to your organization, considering business impact potential, lateral movement possibilities, sensitive data exposure, and whether exploits are available in the wild. This 10-minute process replaces lengthy manual investigations, enabling teams to handle significantly more alerts without sacrificing quality.” – Dropzone AI
Embedding severity logic into automated analysis removes analyst subjectivity and standardizes alert thresholds. This consistency helps Level 1 (L1) analysts close more alerts independently while ensuring Level 2 (L2) teams focus on complex cases.
The outcome is faster Mean Time to Conclusion and improved security posture across the entire incident lifecycle.
The Force Multipliers: Intelligence and Automation
Security teams cannot outscale alert volume through hiring alone. The real multiplier is tight integration between threat intelligence, automation, and modern security tools.
When monitoring systems trigger alerts, automated investigation features should immediately enrich events using threat data, identity context, and cloud environment telemetry. Platforms like Prophet AI and other AI SOC analysts use generative AI to correlate signals across security systems in seconds.
This machine-human partnership improves threat detection accuracy, shortens response times, and reduces dwell times. Security professionals then focus on strategic threat hunting and high-value incident response rather than manual data gathering, dramatically improving SOC efficiency and resilience.
Using Threat Intelligence for Triage
Operational using threat intelligence triage must live directly inside the workflow. This embedded intelligence provides instant context, allowing incident response teams to see campaign links and behavioral data in a single view. When analysts review alerts, they should see threat data from threat repositories, campaign links, and behavioral analytics in one view.
This reduces manual lookups and improves alert categorization accuracy. Integrated intelligence also supports better automated tuning and anomaly detection across network monitoring systems and endpoint detection and response platforms.
Security teams using intelligence-driven triage typically reduce unnecessary alert escalation and improve response timelines. The result is faster, more confident incident response and a stronger security posture against an evolving threat landscape.
Automating Alert Enrichment and Triage
The most significant time sink in traditional triage is manual enrichment. Automating alert enrichment and triage tackles this head-on by using risk based alert prioritization to score threats based on actual business impact.
Through integrations with SOAR platforms, you can create workflows that trigger the moment an alert is generated.
These workflows can automatically query the client’s identity platform to get user role and login history. They can pull asset details from a CMDB to determine criticality. They can launch a sandbox analysis of a suspicious file. All of this data is appended to the alert before a human gets involved.
For clear-cut cases, like an alert from a known vulnerability scanner IP or a repeated false-positive pattern, the workflow can even autonomously close the alert with a documented rationale.
This level of automation is how teams achieve metrics like investigating alerts in under 10 minutes. It’s not about working faster, it’s about having the right information immediately available.
From Process to Practice: The MSSP Advantage
Implementing a robust using threat intelligence triage process is the single biggest lever an MSSP has to improve efficiency, margins, and client satisfaction. It transforms your service from a reactive cost center into a proactive, value-driven partnership.
It transforms your service from a reactive cost center into a proactive, value-driven partnership. For us at MSSP Security, this isn’t theoretical. It’s the foundation of how we deliver consistent, high-quality protection.
We build client-specific playbooks that codify their risk tolerance and critical assets. We integrate their tools into our automated enrichment pipelines. We train our analysts on the risk-based model, so everyone is aligned.
The result is a transparent, defensible process where clients can see why we prioritized one alert over another, based on their business. It reduces their risk and our operational overhead. It’s a win-win built on a process that actually works under pressure.
MSSP Alert Handling Process Review

Continuous review keeps the alert triage workflow aligned with a changing threat landscape. Security teams should regularly measure operational health across the incident lifecycle, specifically by defining alert severity levels to ensure consistency.Examine performance of detection technologies, automated tuning effectiveness, and quality of contextual information.
Look for bottlenecks in alert escalation, gaps in behavioral analytics, or weak spots in cloud environment coverage. Regular tuning of Sigma rules, Graylog Security pipelines, and automated analysis ensures monitoring systems stay accurate.
Ongoing reviews reduce dwell times, strengthen security posture, and keep incident response teams operating at peak efficiency.
FAQ
How does alert triage improve response times in busy security teams?
Effective alert triage helps security teams focus on the most urgent Cyber threats first. By using contextual information, behavioral analytics, and clear alert thresholds, Security Operations Centers reduce wasted effort.
This structured alert triage workflow speeds incident response, improves response timelines, and ensures incident response teams spend time on real risks instead of low-value noise.
What role does Artificial Intelligence play in modern alert triage workflows?
Artificial Intelligence supports alert triage by automating analysis across security systems and monitoring systems. AI SOC analysts use LLM technology and generative AI to process threat data, flag anomaly detection patterns, and assist with alert categorization.
This reduces manual workload for security professionals while improving threat detection accuracy and helping security teams maintain stronger security posture under pressure.
How can teams reduce alert fatigue without missing real cyber threats?
Security teams reduce alert fatigue by combining automated tuning, alert validation, and smart alert management. Detection technologies like endpoint detection and response and intrusion detection systems filter noise early.
Adding investigation checklists, security training, and clear alert escalation paths helps incident response teams stay focused, improving response activities while keeping dwell times and burnout under control.
Why is contextual information critical for accurate alert prioritization?
Contextual information gives security professionals the full picture behind each alert. Pulling data from identity platforms, threat intelligence platforms, and network monitoring systems improves behavioral analysis and alert categorization.
This context helps incident response systems make smarter decisions, reduces unnecessary alert escalation, and strengthens overall security posture across an expanding attack surface and cloud environment.
Your Path to a Clearer Queue
A chaotic alert queue can be fixed. The method is proven: collect and deduplicate alerts, enrich them with context, score them by actual business risk, and automate the routine tasks. This turns analysts from overwhelmed into effective.
The right tools and approach exist. You can keep struggling or build a smarter system. Start by automating one piece of enrichment. The clarity it brings will show you the next step.
Ready to make your alert triage a strength? We can help build that process.
References
- https://www.legitsecurity.com/aspm-knowledge-base/triage-cyber-security
- https://www.dropzone.ai/glossary/alert-triage-in-2025-the-complete-guide-to-90-faster-investigations
Related Articles
- https://msspsecurity.com/operations-delivery-mechanisms/
- https://msspsecurity.com/mssp-alert-handling-process-review/
- https://msspsecurity.com/mssp-alert-triage-process-explained/
- https://msspsecurity.com/how-security-alerts-are-prioritized/
- https://msspsecurity.com/reducing-alert-fatigue-soc/
- https://msspsecurity.com/security-alert-validation-techniques/
- https://msspsecurity.com/risk-based-alert-prioritization/
- https://msspsecurity.com/using-threat-intelligence-triage/
- https://msspsecurity.com/automating-alert-enrichment-triage/
- https://msspsecurity.com/defining-alert-severity-levels/
