We watched an analyst waste forty minutes on a false alarm yesterday. He jumped between six screens for a “high severity” ransomware alert. It was just a clumsy admin tool. While he worked, three more alarms piled up. This is alert triage today: a grind that misses real attacks.
A modern MSSP doesn’t work harder, it works smarter. You need a systematic funnel to turn millions of noisy alerts into just a few real incidents. The workflow below shows how to actually scale. Read on to see MSSP alert triage process explained.
The Main Points
- Speed cuts risk. Faster validation means less time for an attacker.
- Fatigue is a data issue. Group and enrich alerts automatically before they reach people.
- Automate the simple tasks. Let your team tackle complex threats.
How does the MSSP alert triage workflow actually function?
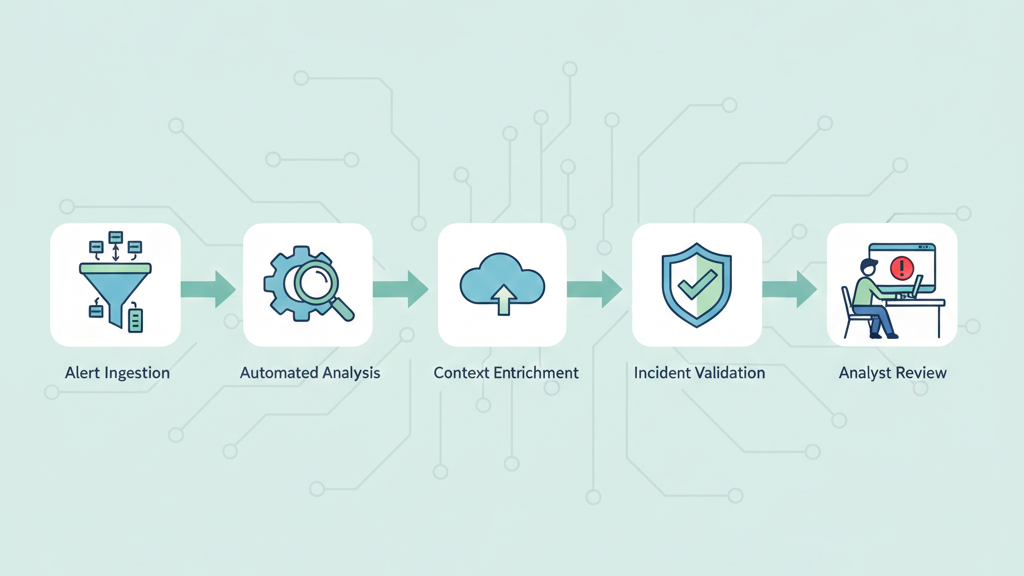
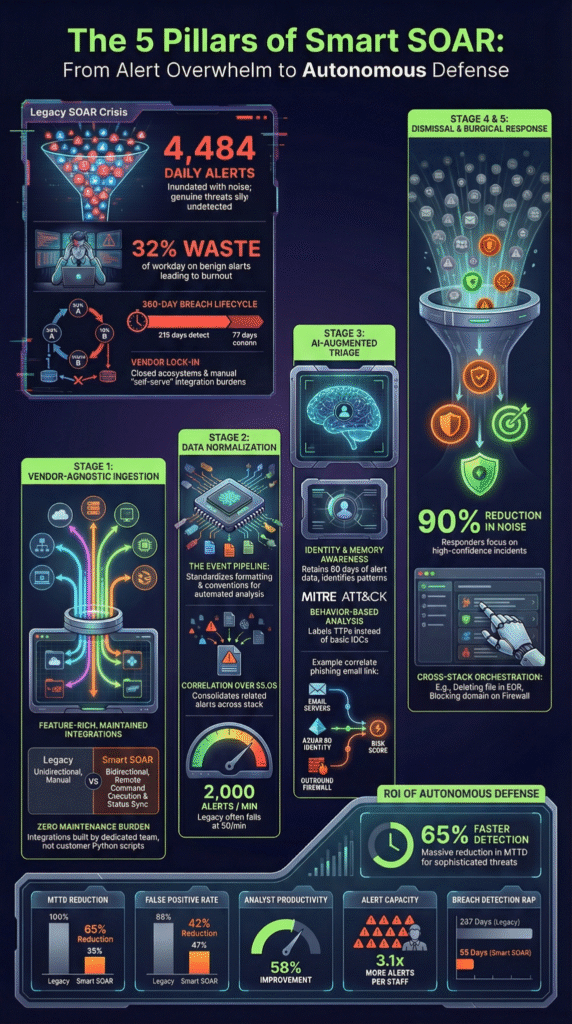
Our MSSP triage workflow is a filter, but we run it. We take in the flood of SIEM and EDR alerts and start sorting. First, we collect everything, no signal ignored. Then we categorize and tag the chaos: phishing attempts, suspicious logins. A structured alert triage prioritization process comes next, scoring each alert’s risk using live threat intel.
“Alert triage, a key process within Security Operations Centers (SOCs), entails the systematic evaluation, prioritization, and response to security alerts. It’s a crucial mechanism for discerning the potential impact and urgency of each alert, enabling security teams to allocate resources effectively, focusing on the biggest threats first. At its core, the alert triage process involves swiftly assessing the threat level of a security alert and determining the appropriate course of action.” – Radiant Security
The real work is investigation. We pull context from different tools to separate real threats from false alarms. Based on what we find, we respond or escalate. Finally, we loop back, tuning the detection rules so the system gets smarter.
This funnel turns overwhelming alert volume into clear, actionable intelligence. It’s how we move teams from constant firefighting to controlled defense.
Why is speed the most critical KPI for MSSP triage?

Speed is everything in triage. We think about dwell time, that silent clock starting when an attacker gets in. A slow, manual process gives them days, even weeks, to move through a network. We’ve seen it happen.
“The alert triage process typically involves four key steps: Classification: Categorizing alerts based on attack type, affected systems, or threat indicators. Validation: Determining whether an alert represents a legitimate security concern. Prioritization: Ranking alerts by severity, business impact, and urgency. […] Effective alert triage serves as the foundation of successful security operations, transforming overwhelming alert noise into prioritized intelligence.” – VMRay
The business cost of that delay is brutal. Conducting a regular mssp alert handling process review helps identify where these delays occur. Every minute spent manually checking hashes or logs adds millions to the final breach bill. For an MSSP, speed isn’t about panic.
For an MSSP, speed isn’t about panic. It’s engineered efficiency, cutting the mean time to conclusion from hours down to minutes. That’s our focus. We’ve watched analysts drown in alert queues, their sharpness fading with every false alarm they close. Their effectiveness decays. Our job is to build systems that stop that clock faster.
| Metric | Manual-Heavy Process | Optimized MSSP Triage |
| Average Investigation Time | 30–45 Minutes | 3–11 Minutes |
| Alert Coverage & Review | ~20-25% (due to fatigue) | 100% Automated Triage |
| Primary Analyst Focus | Data Gathering & Lookups | Contextual Decision-Making |
| Critical Risk | Missed medium/low alerts that signal advanced threats | Focus maintained on validated, high-risk incidents |
How do MSSPs solve the alert fatigue crisis for good?

Alert fatigue isn’t burnout from hard work. It’s numbness from doing work that rarely matters. We see this often when reviewing MSSP environments: analysts grind through hundreds of alerts knowing most are noise. The traditional Tier 1 model creates the problem by feeding teams isolated, context-free events. The fix isn’t tougher analysts, it’s smarter inputs.
When we help MSSPs audit and select tools, the biggest gains come from changing triage. Instead of raw alerts, modern workflows bundle related events into one clear narrative. A failed login, odd process, and suspicious outbound connection may look harmless alone. Correlated with user context and threat intelligence, they form a credible incident.
Effective teams typically rely on:
- Smart Grouping
- Automated Enrichment
- Behavioral Baselines
- Unified Context
With higher-fidelity incidents, analysts focus on real investigations. We’ve seen productivity rise quickly when MSSPs implement the right stack.
What are the silent pitfalls that wreck endpoint triage?
Endpoint triage carries risks that many teams underestimate. In our work reviewing workflows, the biggest failure we see isn’t technical, it’s how security alerts are prioritized under pressure. Teams naturally chase “Critical” alerts while quieter Medium or Low signals get pushed aside.
A strange scheduled task or unusual service install may look harmless, but these subtle indicators often point to persistence.
Context blindness is another frequent problem. We’ve audited environments where analysts reviewed a suspicious process tree without checking network activity. On its own, certutil.exe can look routine. With network telemetry, it may reveal payload delivery. Without automatic correlation, analysts are working half-blind.
Finally, knowledge evaporation quietly erodes efficiency. When false positives aren’t documented, teams repeat the same investigations. Strong MSSPs capture and reuse triage decisions so effort compounds instead of resets.
FAQ
How does alert triage improve response times in SOC operations?
Alert triage improves response times by prioritizing the right security incidents first. Instead of treating every alert equally, the triage process filters noise, reduces false positives, and highlights real cyber threats.
In modern Security Operations Centers, this structured alert triage workflow helps the Security Team focus faster, strengthen the overall security posture, and streamline incident response without overwhelming human teams.
What role does artificial intelligence play in modern alert triage?
Artificial Intelligence now supports alert triage through automated analysis and smarter detection logic. AI agents review alert volume, enrich contextual information, and assist incident classification before human teams engage.
Many Managed Security Service Providers use Autonomous SOC concepts and SOAR Platforms to improve threat detection accuracy, reduce alert fatigue, and maintain consistent security operations across complex client environments.
Why do many MSSPs struggle with high alert volumes?
Many Managed Security Service Providers struggle because alert ingestion grows faster than Security Team capacity. Expanding threat landscape activity, noisy intrusion detection systems, and poorly tuned SIEM platforms inflate alert volumes.
Without strong alert management, alert validation, and automated analysis, Security Operations Centers face growing false positives, slower response times, and reduced visibility into real online attacks.
How can teams reduce false positives during endpoint investigation?
Reducing false positives requires better contextual information during endpoint investigation. Effective triage process design combines endpoint detection and response data, behavioral analysis, and threat intelligence feeds. Security tools should support alert categorization and automated correlation so incident response teams see the full picture.
This approach improves alert coverage, lowers the False Negative Rate, and strengthens cybersecurity posture.
Moving forward with a process that works
A good alert triage process isn’t about frantic reactions. It’s about a clear system that helps your team focus. You need tools that handle volume, workflows that prioritize context, and a commitment to tuning out the noise.
Our consulting can help build that. We guide MSSPs on product selection, auditing, and stack optimization to create a clear, efficient operation.
Ready to reduce the fatigue? Let’s discuss your triage process and build that clarity. Schedule a consultation.
References
- https://radiantsecurity.ai/learn/soc-alert-triage/
- https://www.vmray.com/alert-triage/
