Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
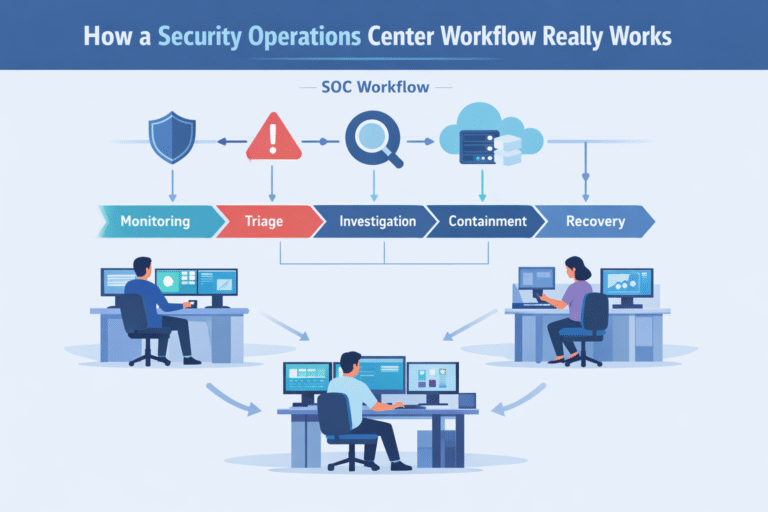
Security operations center workflow is the structured process teams use to detect, triage, investigate, and…

Operations & delivery mechanisms in an MSSP SOC define how threats move from detection to…

Annual training doesn’t work. You know it, your team knows it, and the data screams…

You can reducing human error risk security by accepting that people will always make mistakes…