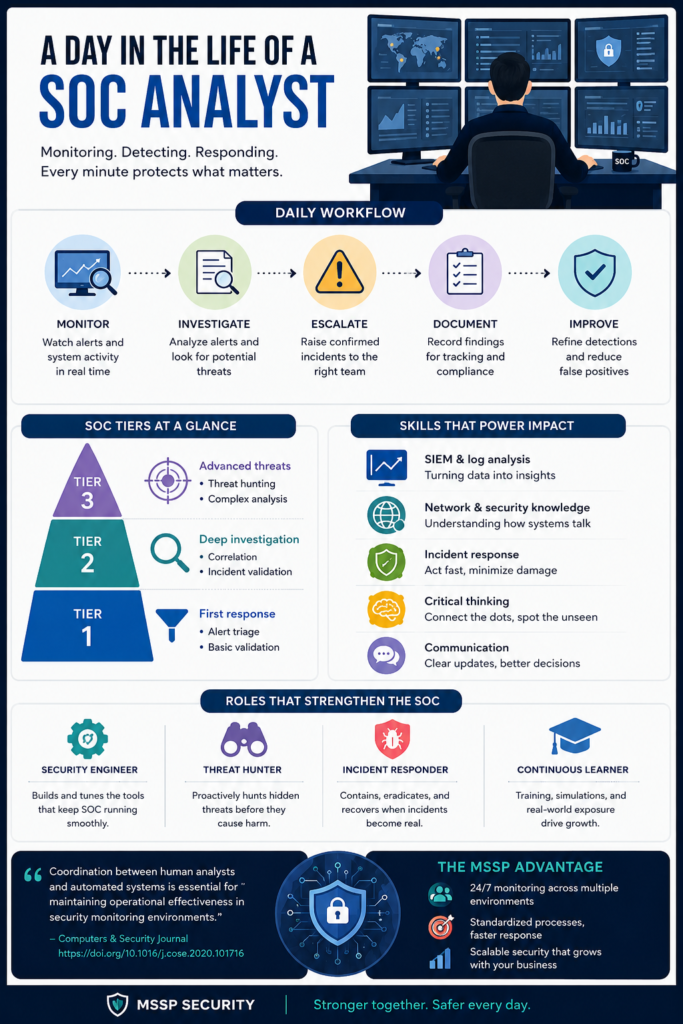
SOC analyst daily activities focus on monitoring security systems, investigating alerts, and responding to potential threats. In MSSP Security operations, we handle multiple client environments, so prioritization and accuracy are very important. Each day involves reviewing logs, checking alerts, and deciding which incidents need escalation.
The work is continuous and detail-oriented, combining technical analysis with quick decision-making. This section explains how SOC teams operate in real situations and how each role contributes to overall cybersecurity defense. Keep reading to see how SOC responsibilities are structured in practice.
What We Learn From Daily SOC Operations (And Why It Matters)
Simple overview of daily focus:
- Monitor security alerts in real time
- Investigate suspicious activities
- Escalate validated incidents
How SOC Teams Stay Connected in Real Time
SOC roles function like interconnected layers rather than isolated jobs. Analysts detect issues, engineers maintain systems, and responders handle incidents.
“Decisions must be made rapidly under uncertainty, and the consequences of errors can be severe.” – ResearchGate
In MSSP Security operations, we apply this coordination daily across multiple client infrastructures, ensuring information flows quickly between teams without delay.
Breaking Down SOC Responsibilities by Level
SOC work is structured into tiers to manage complexity, specifically defining the SOC analyst tier 1, 2, and 3 responsibilities to ensure efficient escalation.
| Tier | Main Focus | Core Responsibility |
| Tier 1 | First response | Alert triage and filtering |
| Tier 2 | Investigation | Deep analysis and validation |
| Tier 3 | Advanced defense | Threat hunting and complex cases |
This structure helps MSSP environments handle high volumes of alerts without losing precision or response quality.
Skills That Shape a Strong SOC Analyst
Credits: Tech with Jono
SOC analysts rely on both technical ability and structured thinking; cultivating security analyst roles and expertise directly affects the quality and depth of every investigation.
Core abilities include:
- SIEM and log analysis
- Network security fundamentals
- Incident response workflows
- Critical reasoning under pressure
- Clear documentation and reporting
- Basic scripting for automation
These skills help analysts turn raw data into actionable security decisions.
Proactive Defense Through Threat Hunting
Threat hunting goes beyond alerts, it focuses on discovering hidden risks before they escalate.
We often build hypotheses from unusual behavior patterns or historical anomalies. In MSSP Security, this approach strengthens visibility across multiple client environments at once.
“Most transitions begin by deploying AI to handle the Tier 1 alert triage backlog.” – Prophet Security
Engineering the SOC Behind the Scenes
Security engineers ensure that SOC systems function smoothly, coordinating with various roles within the security operations center to maintain high-performance environments.
Their responsibilities include:
- SIEM tuning and optimization
- Security tool integration
- Automation of detection rules
- Performance monitoring
Without this layer, analysts would struggle with inefficient or noisy alert systems, especially in MSSP environments managing diverse infrastructures.
When Incidents Become Real: Response in Action
Incident responders step in when threats are confirmed. Their role focuses on containment and recovery.
Key responsibilities:
- Malware analysis and containment
- System recovery coordination
- Evidence collection
- Communication during incidents
In MSSP Security, responders often manage incidents across different organizations, making structured decision-making critical.
Growing Expertise Inside MSSP Security Teams

Instead of relying on static training, MSSP environments focus on continuous exposure and real-case learning.
Development typically includes:
- Simulation-based SOC training
- Threat intelligence practice
- Live incident handling
- Platform-specific mastery
This approach builds analysts who can adapt quickly across multiple threat landscapes.
FAQ
What does a SOC analyst actually do every day?
They monitor security alerts, investigate suspicious activity, and escalate confirmed threats. In MSSP environments, this work spans multiple clients, requiring strong prioritization and structured workflows.
Why is SOC work considered continuous instead of task-based?
Because cyber threats operate 24/7. Analysts must constantly review alerts, validate events, and respond in real time, making the work ongoing rather than fixed.
How does MSSP Security change SOC operations?
MSSP Security centralizes monitoring across multiple organizations, allowing analysts to handle diverse environments while following standardized security processes.
Do SOC analysts only focus on technical tasks?
No. Communication, documentation, and analytical reasoning are equally important. Analysts must clearly explain incidents and collaborate across teams.
Closing Perspective: Why SOC Analyst Daily Activities Define Modern Defense
The effectiveness of modern cyber defense hinges on the daily precision of SOC analysts. By integrating monitoring and response into a unified framework, MSSP Security transforms fragmented data into resilient protection.
To refine your operational maturity, reduce tool sprawl, and optimize your security stack with expert guidance backed by 15 years of experience, explore our tailored consulting services. Build a tech stack that aligns with your goals and stays ahead of emerging risks. Explore MSSP Security Services
References
- https://www.researchgate.net/publication/400856429_Before_the_Vicious_Cycle_Starts_Preventing_Burnout_Across_SOC_Roles_Through_Flow-Aligned_Design
- https://www.prophetsecurity.ai/blog/soc-tiers-are-out-how-ai-is-flattening-soc-tier-1-2-3
