Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

The Purdue Model security monitoring is a practical blueprint for industrial security. It segments your…
ICS incident response planning is the use of the Incident Command System to manage cyber…

Choosing an OT security monitoring provider in California means prioritizing safety, uptime, and regulatory alignment…
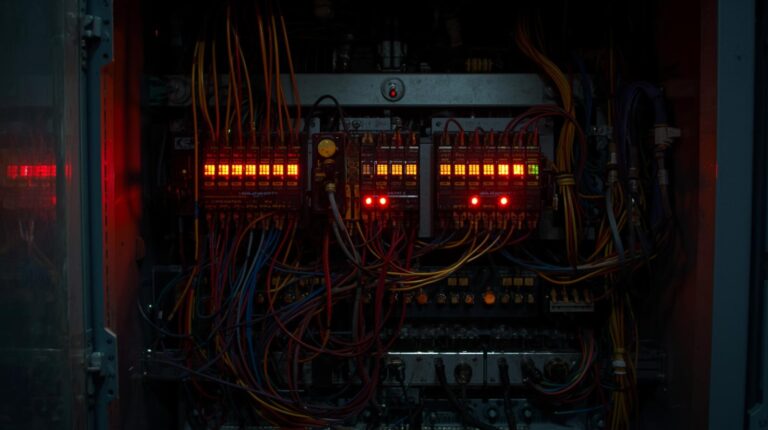
Detecting OT-specific threats and vulnerabilities requires passive, protocol-aware monitoring. Industrial systems prioritize safety and uptime,…