Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

You simulating real world attacks safely to find security gaps before real attackers do. Think…

Your last penetration test report likely won’t pass an audit. Most standards, like PCI DSS…

Forget vendors that just sell you a pass-fail report. You need choosing penetration testing vendor…
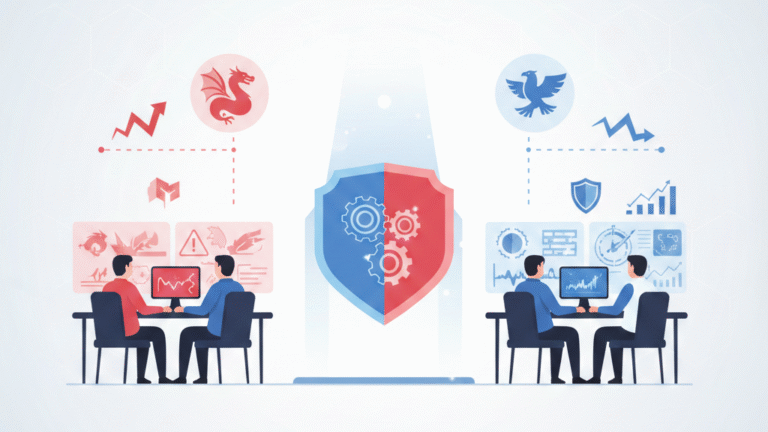
Coordination transforms a chaotic cyber fight into a useful training exercise. It’s the shift from…