Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
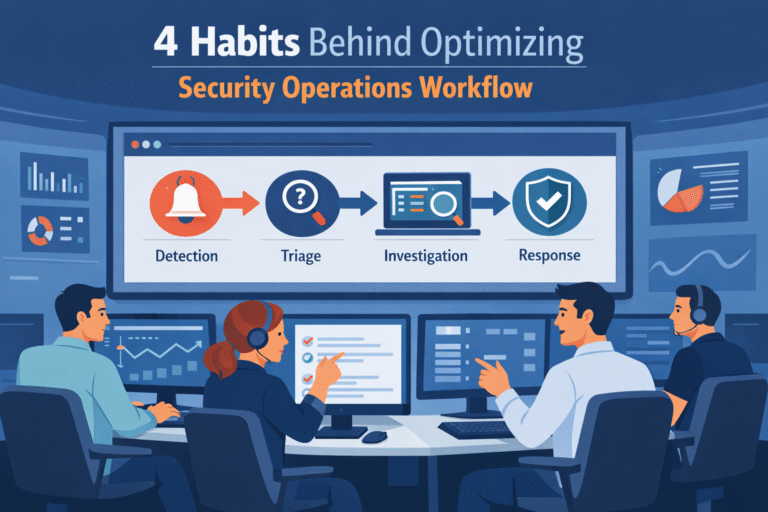
Optimizing security operations workflow starts with fixing the process, not blaming the analysts. When the…
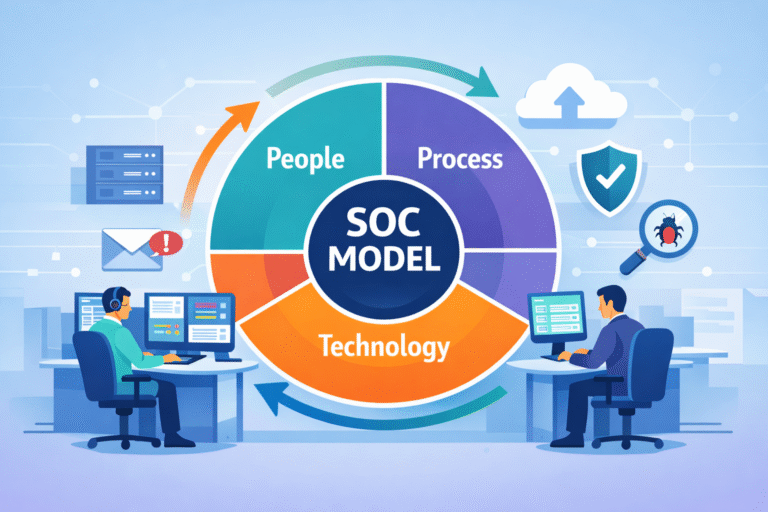
Understanding SOC operations model starts with one idea: structure decides outcomes. A SOC model defines…

Security incident lifecycle SOC is the structured path a SOC follows to handle threats from…

Your newest employee is already inside your network. It works 24/7, talks to your databases,…