Visibility into OT network traffic means clearly seeing how industrial systems communicate so teams can spot risks, prevent downtime, and protect safety. In manufacturing, energy, and water utilities, most incidents start with unseen or misunderstood traffic inside ICS networks.
We have worked with operators who assumed their environments were “quiet” until passive monitoring proved otherwise.
This article explains what real OT traffic visibility looks like in practice, where common tools often fall short, and how teams can build confidence step by step. Keep reading to understand what truly matters in your network and what you can safely ignore.
Key Takeaways
- OT network traffic visibility is about understanding normal behavior, not just spotting threats.
- Passive monitoring is essential because active scanning can disrupt fragile systems.
- Practical visibility combines standards, operator knowledge, and realistic tooling choices.
What is OT network traffic visibility?
OT network traffic visibility is the ability to see and understand the communication between industrial assets. It’s about knowing which PLC is talking to which HMI, how often, and what commands are being sent. This understanding is the foundation for detecting risks, keeping systems running, and ensuring safety.
In practice, it means passively watching the deterministic traffic on control networks, things like Modbus or DNP3 commands. These protocols don’t log events, so you have to see the raw packets. As NIST guidance points out, continuous monitoring tailored to OT is essential.
From our work helping MSSPs evaluate products through advanced specialized services, we’ve learned visibility is more than a tool. It’s a shared understanding between engineers and security teams. When you can map traffic to Purdue Model levels, you quickly spot segmentation gaps and unmanaged devices you didn’t know existed.
Key aspects include:
- Covering industrial traffic from sensors (Level 0) up to supervisory systems (Level 3).
- Using passive network profiling, not intrusive agents that can disrupt operations.
- Providing the clear, factual evidence needed for both safety audits and security investigations.
This clarity becomes the baseline for everything else, from anomaly detection to figuring out what happened during an incident.
Why is visibility into OT network traffic critical for security and uptime?

Without visibility into OT network traffic, you’re essentially running your plant blind. You can’t see abnormal behavior until it’s too late, which directly increases safety risks, unplanned downtime, and cyber exposure. Many facilities have minimal logging because their primary focus is on keeping things running.
Industry analyses consistently show that most incidents involve assets that weren’t properly documented or managed. As noted by industry experts regarding the MITRE ATT&CK framework:
“The process of asset evaluation is a key part of establishing data visibility, which is the first phase of the Continuous Detection/Continuous Response (CD/CR) workflow… [using] the MITRE ATT&CK framework helps you uncover exactly where your detection and response capabilities fall short.” – Google Cloud Security [1]
This visibility is critical because it:
- Enables early detection of anomalies, like a device behaving strangely.
- Supports fast root cause analysis when something does go wrong.
- Protects uptime by identifying misconfigurations or failing devices before they cause a shutdown.
From our consulting work with MSSPs, we’ve seen the consequences firsthand. In one case, a single misconfigured PLC began flooding the network with traffic, slowing down critical HMIs.
How does OT traffic differ from IT network traffic?
OT network traffic is fundamentally different from IT traffic. It’s predictable, repetitive, and built for reliability above all else. A PLC might poll a sensor every 100 milliseconds, and an HMI will request the same data register thousands of times a day.
The core differences boil down to a few key points:
- Primary Goal: OT prioritizes safety and uptime; IT focuses on confidentiality and user productivity.
- Change Tolerance: OT networks change very infrequently; IT networks are in a constant state of flux.
- Response to Interference: Unexpected traffic in OT can cause a shutdown; IT systems are built to handle it.
Here’s a quick comparison:
| Aspect | OT Networks | IT Networks |
| Main Goal | Safety & Uptime | Confidentiality & Productivity |
| Traffic Pattern | Predictable, cyclic | Bursty, user-driven |
| Common Protocols | Modbus, DNP3, EtherNet/IP | HTTP, DNS, SMTP |
| Change Frequency | Very low | Constant |
In our work evaluating products for MSSPs delivering OT security monitoring, we see these differences cause constant friction. An IT security tool that sends unexpected packets or causes latency can crash a process. Effective OT visibility requires tools that passively understand these industrial protocols and respect the static, unchanging nature of the environment.
What protocols matter most for OT network traffic visibility?

For OT traffic visibility, the protocols that matter are the ones that actually run the factory floor. This means industrial standards like Modbus, DNP3, PROFINET, and EtherNet/IP. They are often decades old, send commands in plain text, and have little to no built-in authentication or encryption.
Understanding them requires specialized decoders. A generic IT monitoring tool will just see raw packets. An OT-aware tool can extract meaning, it knows the difference between a “read” and a “write” command, or if a function code is out of place.
In our product audits for MSSPs supporting managed OT monitoring, we’ve seen systems trigger false alarms because they flagged a normal maintenance change to a register value as suspicious.
Effective monitoring looks for anomalies within these predictable protocols, such as:
- An unexpected function code appearing in a command.
- A new device starting to “talk” on the network.
- A sudden change in the timing or frequency of polling.
These deviations often point to a misconfiguration or human error, not an attack, but both can disrupt production. The key is that protocol literacy turns network noise into actionable insight. Without it, you’re just collecting data, not gaining visibility.
How do passive monitoring and SPAN ports enable OT visibility?
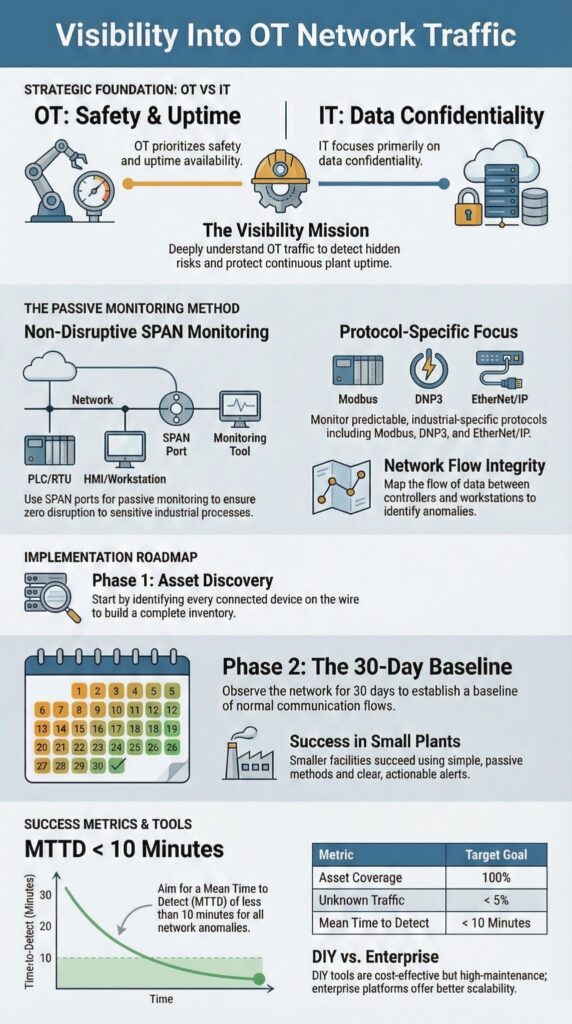
Passive monitoring is the standard for gaining OT visibility because it’s completely safe. It works by using a SPAN port or a network tap to copy traffic to a monitoring sensor. The sensor analyzes the packets, but never sends any traffic back onto the network. This means zero impact on fragile controllers or PLCs.
This approach aligns with the “Passive Techniques” mentioned in NIST SP 800-82. As highlighted in recent industrial guidance:
“One quick way to achieve a high-fidelity level of inventory is to use a tool that passively collects data on every connected device within your ICS. This same tool not only can tell you what’s on your network, but can also baseline normal network communication… so you can determine if there are any deviations.” – Tripwire [2]
This approach provides several key benefits:
- No agents required on any industrial endpoints.
- Complete safety for legacy equipment that can’t be modified.
- Long-term baselining to detect subtle changes over time.
In our work evaluating products for MSSPs, we rely on this method. We’ve seen a single mirrored switch port uncover undocumented devices and strange communication paths in a matter of hours.
DIY tools vs enterprise platforms: what are the real tradeoffs?
Credits: Critical Infrastructure Defenders
When choosing tools for OT visibility, you face a classic trade-off: build it yourself or buy an enterprise platform. DIY tools, often built on open-source software, are attractive for their low upfront cost and hands-on control. For a small plant or a tight budget, spending a few thousand dollars to start capturing packets can make perfect sense.
The core trade-offs come down to a few points:
- Ownership: DIY gives you full control; a platform hands off maintenance.
- Scalability: DIY works for a few sites; platforms are built for distributed operations.
- Expertise: DIY requires in-house skill; a platform provides vendor support.
Here’s a breakdown of the key differences:
| Factor | DIY Approach | Managed Platform |
| Cost | Low upfront | Predictable subscription |
| Setup Time | Fast to start | Longer implementation |
| Maintenance | High (your team’s time) | Low (handled by vendor) |
| Compliance Support | Limited, manual | Built-in reporting |
Enterprise platforms reduce that maintenance load and come with support, but they assume you have the budget and infrastructure to support them. The right choice isn’t about which is better, but which fits your specific situation.
FAQ
What does visibility into OT network traffic mean for daily industrial operations?
Visibility into OT network traffic means clearly understanding how data flows between PLCs, HMIs, and control systems in real time.
It relies on OT network monitoring, ICS visibility, and industrial control traffic analysis to show which devices communicate, when they communicate, and how often. This insight helps teams maintain stable operations, identify abnormal behavior early, and reduce operational blind spots.
How does OT network traffic visibility improve security without disrupting operations?
OT network traffic visibility improves security by using passive network profiling, traffic mirroring ICS, and network flow telemetry instead of active scans.
It observes Modbus TCP inspection, DNP3 protocol analysis, and HMI traffic visibility without touching live systems. This method enables reliable anomaly detection ICS, supports OT threat hunting, and strengthens the OT security posture without interrupting production processes.
Why is protocol-level analysis critical for understanding OT network behavior?
Protocol-level analysis shows exactly how industrial protocols behave inside the network. Deep packet inspection OT, legacy protocol decoding, and industrial protocol decoders expose command structures and field values.
SCADA traffic analysis, Ethernet/IP sniffing, and Profibus traffic capture help teams detect misuse, configuration errors, or unsafe commands, enabling accurate baselining and faster OT forensics logging during investigations.
How does OT network traffic visibility support asset discovery and network mapping?
OT network traffic visibility identifies assets by analyzing flow data OT networks and passive OT fingerprinting. This process builds a reliable OT asset inventory, including unmanaged or forgotten devices.
OT network mapping, asset tagging ICS, and endpoint visibility OT improve Purdue model segmentation and network segmentation visibility, helping teams maintain accurate ICS network diagrams and support ongoing OT risk assessment.
Can OT network traffic visibility detect abnormal behavior and insider threats?
OT network traffic visibility detects abnormal behavior by comparing live activity to established traffic pattern baselining.
Network behavior analytics, device behavior correlation, and lateral movement detection reveal unusual commands or communication paths. Traffic volume anomalies and ICS event correlation help security teams identify insider threats, compromised devices, or unsafe changes before they escalate into operational incidents.
Visibility Into OT Network Traffic as an Ongoing Practice
Visibility into OT network traffic is a continuous practice, not a one-time setup. It blends passive monitoring, standards alignment, and real operational insight. Start small and focus on steady progress, not perfection. This builds a sustainable foundation for safer operations and a calmer, more confident response to network changes.
Need a partner to guide your strategy?
Get expert guidance from MSSP Security
We offer vendor-neutral consulting to help MSSPs select the right tools and build a resilient security program.
References
- https://security.googlecloudcommunity.com/community-blog-42/beyond-the-matrix-reloaded-3935
- https://www.tripwire.com/resources/guides/navigating-industrial-cybersecurity
