A managed OT security monitoring service offers continuous, outsourced protection for industrial networks. It detects threats and anomalies without disrupting operations. Industrial environments face growing risks from ransomware, exposed legacy systems, and compliance demands like NIST 800-82.
In our experience with manufacturers and utilities, we’ve seen how a lack of OT visibility can threaten fragile uptime. This article explains how the monitoring works, why firms outsource it, and how to evaluate services that truly understand operational technology. Read on to see how mature OT monitoring reduces risk while keeping production running smoothly.
Key Takeaways
- Managed OT security monitoring provides 24/7 visibility into ICS and SCADA environments without active scanning.
- Industrial organizations outsource OT monitoring to access OT-native expertise and predictable costs.
- The strongest programs combine passive monitoring, human validation, and compliance alignment.
What Is a Managed OT Security Monitoring Service?
A managed OT security monitoring service is continuous, outsourced protection for industrial networks. It uses passive monitoring and OT-specialist analysts to find threats without ever touching your running equipment. Recent research confirms this is becoming the standard for modern industry:
“As industrial systems become more interconnected, [OT cybersecurity] services enable organizations to build unified security strategies that span both domains… In Omdia’s annual Cybersecurity Decision Maker Survey (2025) of 980 OT cybersecurity decision makers, 100% of respondents surveyed use some form of cybersecurity service, of which fully managed services (e.g., MDR, managed security operations center [SOC]) were the most common at 40% of respondents.” – Honeywell/Omdia 2025 Report [1]
This service is built for OT, where safety and uptime are non-negotiable. Core functions include:
- Passive monitoring of ICS/SCADA traffic (Modbus, DNP3, etc.).
- Continuous OT asset discovery and inventory.
- Anomaly detection based on process behavior, not IT rules.
- A dedicated OT Security Operations Center (SOC).
Unlike an IT SOC, an OT team manually checks every alert before acting to prevent accidental shutdowns. They understand that writing to a PLC is different from reading it, a critical distinction for keeping production safe and online.
Why Do Industrial Organizations Outsource OT Security Monitoring?

Industrial companies outsource OT security monitoring because it’s hard to find and keep the right skills in-house. ISA Secure reports that fewer than 30% of manufacturers have dedicated OT security staff. Most plants depend on controls engineers who are already stretched thin.
A managed service provides expert, 24/7 coverage without the cost and risk of building your own team. It also helps meet compliance rules like IEC 62443 and satisfies demands from insurers.
The main reasons companies choose to outsource are:
- A major shortage of internal OT security expertise.
- The need for continuous monitoring across multiple, often remote, sites.
- Pressure from regulators and insurance providers for proven controls.
Buyers typically worry about cost predictability and vendor lock-in. They also need a provider they can trust. A generic IT security team might misinterpret an OT alert and cause a shutdown, while an OT-native team works alongside your engineers.
Outsourcing turns the unpredictable cost of a security incident into a fixed, manageable operating expense.
What Threats Can Managed OT Monitoring Detect?
Managed OT monitoring is designed to catch the threats that slip past IT security. It identifies unauthorized changes to PLC logic, suspicious traffic crossing from corporate networks to the factory floor, and early signs of compromise on engineering workstations.
The technical necessity of this monitoring is highlighted by current market analysis:
“Managed OT SOC offerings deliver scalable expertise without inflating headcount… Network monitoring captured a 46.05% share of the operational technology security market size in 2025. Deep-packet-inspection engines baseline Modbus, Profinet, and OPC UA traffic, allowing rapid flagging of malicious write commands or rogue firmware uploads.” – Mordor Intelligence 2026 Forecast [2]
The service excels at spotting early indicators, not just active malware. It typically detects:
- Unauthorized logic or firmware uploads to controllers.
- IT-to-OT lateral movement through weak network segmentation.
- Insider misuse on critical HMIs and engineering stations.
Every alert is validated by a human analyst who understands the process, ensuring a response that protects uptime.
Which Industries Benefit Most From Managed OT Security Monitoring?
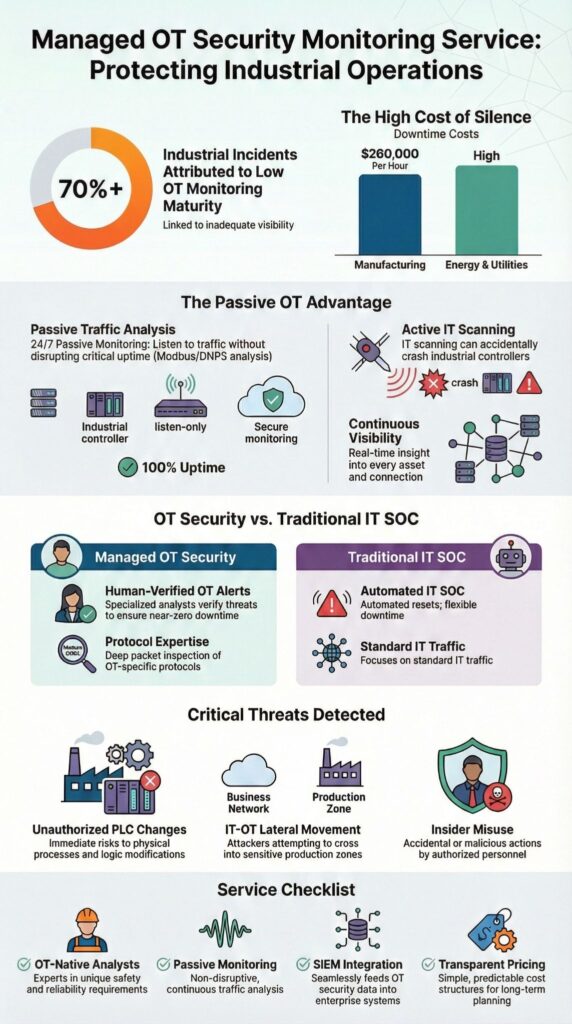
Managed OT security monitoring provides the greatest value in industries where stopping isn’t an option. The financial and safety stakes of downtime make it essential. Manufacturing, energy, and utilities are the clearest beneficiaries.
Manufacturers often adopt it first. The cost of unplanned stoppages is staggering, IndustryWeek estimates an average of $260,000 per hour. From our consulting work with MSSPs, we see that food & beverage and automotive plants are particularly proactive, as a line halt can ripple through an entire supply chain in minutes.
Energy and utility companies are close behind, driven by stringent regulations and the critical need for public safety. High-value OT environments that gain the most include:
- Discrete and process manufacturing plants.
- Power generation, transmission, and distribution systems.
- Water and wastewater treatment facilities.
These sectors typically share high-risk traits: decades-old controllers, remote unmanned sites, and flat, interconnected networks. A managed service addresses these specific weaknesses directly. It provides the necessary visibility and protection without forcing a risky, wholesale technology upgrade that many of these operations simply cannot afford to undertake.
How Does Managed OT Monitoring Integrate With Existing IT Security Tools?

Managed OT monitoring needs to connect with your existing IT security tools, like a SIEM or XDR platform, to create a single view of risk. The goal is unified visibility without compromising the passive, careful approach OT requires.
In our audits for MSSPs, we’ve found the integration works best when OT data is processed first. Raw, unfiltered alerts from the factory floor will overwhelm an IT SOC. Instead, the OT service should normalize and enrich the data, sending only validated, high-fidelity alerts to the central SIEM.
Common integration methods include:
- Forwarding normalized OT logs and alerts to the SIEM.
- Creating workflows for incidents that span IT and OT networks.
- Adapting SOAR playbooks and ticketing systems for OT-specific responses.
The table below shows why this integration must be handled carefully:
| Area | OT Requirement | IT Tool Expectation |
| Scanning | Passive only | Active is acceptable |
| Response | Human-verified first | Often automated |
| Downtime Tolerance | Near-zero | More flexible |
Successful integration respects these fundamental differences. Our role is to help MSSPs select monitoring services that plug into a client’s current SIEM without forcing a costly tool replacement, ensuring the OT data adds clarity instead of chaos.
How Much Does a Managed OT Security Monitoring Service Cost?
Credits: Fujitsu
Pricing for a managed OT security monitoring service isn’t a flat rate. It depends on the number of assets and sites you have, the industrial protocols in use, and the level of response you need. According to SANS Institute research, annual costs typically range from five to six figures, scaling with the size and complexity of the operation.
The main factors that drive the price are:
- The total count of OT assets (PLCs, HMIs, etc.) and the variety of protocols.
- Whether you need 24/7 OT SOC coverage or only business-hours monitoring.
- The scope of managed incident response and forensic support included.
In our experience helping MSSPs evaluate products, we see mid-sized manufacturers often face a challenge with high minimum commitments and rigid multi-year contracts. A practical approach is to look for providers offering flexible models.
Many of our clients start with a basic passive monitoring package to establish a baseline. Once they see the value and build internal trust, they then expand into a full managed detection and response service. This phased rollout helps manage budget and proves ROI step by step.
FAQ
What does OT security monitoring actually do in live industrial environments?
OT security monitoring continuously observes industrial networks, devices, and communications to identify threats in real time. It uses passive OT monitoring, OT protocol analysis, and anomaly detection in ICS environments to detect unsafe behavior early.
This approach improves industrial control system protection, reduces unplanned downtime, and strengthens operational technology security without interfering with production processes or safety-critical systems.
Why choose managed OT services instead of building an in-house OT SOC?
Managed OT services provide access to a dedicated 24/7 OT SOC without the cost and complexity of building internal teams. A managed provider delivers continuous OT monitoring, OT asset visibility, alert triage, and OT incident response.
This model helps organizations maintain strong ICS cybersecurity while allowing operations teams to focus on reliability, safety, and production performance.
How does OT security monitoring support industrial cybersecurity compliance?
OT security monitoring helps organizations meet compliance requirements by tracking assets, logging events, and monitoring controls aligned with NIST 800-82 and IEC 62443. Continuous monitoring supports OT governance, risk, and compliance activities.
It also improves audit readiness by documenting network behavior, enforcing Purdue model security, and supporting secure OT and IT convergence across regulated industrial environments.
Can OT security monitoring protect legacy and air-gapped industrial systems?
OT security monitoring protects legacy and air-gapped systems through passive OT monitoring techniques that do not require active scanning. This approach provides OT asset visibility, traffic analysis, and anomaly detection without disrupting older controllers.
It supports PLC security, legacy OT security, and industrial control system protection while maintaining stability in environments with limited connectivity or modernization constraints.
How does OT security monitoring reduce ransomware impact on operations?
OT security monitoring reduces ransomware risk by detecting abnormal behavior early across industrial networks. Network detection for OT, behavioral analytics, and threat hunting identify lateral movement before operations are disrupted.
When combined with managed OT incident response and forensics, organizations can contain attacks quickly, protect cyber-physical systems, and minimize downtime in manufacturing, energy, and utility environments.
Managed OT Security Monitoring Service for Resilient Operations
A managed OT monitoring service builds industrial resilience with continuous, expert oversight tailored to your operations. It reduces risk without disrupting production, transforming security into a shared discipline that provides lasting confidence.
Need a service that truly understands OT?
Explore continuous OT monitoring with MSSP Security
We help MSSPs select and audit the right tools. Our vendor-neutral consulting, from needs analysis to final recommendations, streamlines your stack to boost service quality and align with your business goals.
References
- https://www.honeywell.com/content/dam/honeywellbt/en/documents/gated/hon-corp-report-omdia-universe-operational-technology-cybersecurity-services.pdf
- https://www.mordorintelligence.com/industry-reports/operational-technology-ot-security-market
