Security response playbook examples show how structured actions can transform chaotic incident handling into a controlled, repeatable process. We’ve seen organizations struggle not because they lack tools, but because they lack clarity during incidents.
By applying proven playbooks, teams respond faster and with fewer mistakes. This article explores real-world approaches, templates, and strategies you can apply immediately. If you want to strengthen your incident response with practical guidance, keep reading.
Security Response Playbook Examples That Actually Work
Before diving deeper, here’s what matters most when building effective playbooks based on our experience and industry practice:
- Playbooks reduce response time and decision fatigue
- Each threat requires a tailored playbook, not a generic one
- Automation (SOAR) enhances speed but needs human oversight
What Is Security Response Playbook
Understanding what is security response playbook is essential before building one. It is a structured, step-by-step guide that defines how to detect, respond to, and recover from cybersecurity incidents.
“An incident response plan is a set of instructions designed to help organizations prepare for, detect, respond to, and recover from network security incidents.” – Wikipedia
From our experience in MSSP Security, organizations without defined playbooks often delay decisions during critical moments. A strong playbook includes:
- Defined triggers
- Clear roles and responsibilities
- Response procedures
- Escalation paths
This structure supports a reliable playbook driven incident response model.
Examples Incident Response Playbooks
Credits: Struggle Securit
Organizations should maintain multiple playbooks to address different threats. Common examples incident response playbooks include:
- Phishing attacks
- Ransomware incidents
- Data breaches
- Insider threats
- Malware infections
From our experience, the biggest improvement comes when teams move beyond static documents and integrate these playbooks into automated workflows.
Phishing Incident Response Playbook
A phishing incident response playbook focuses on stopping credential theft quickly.
“Organizations that implement formal incident response capabilities are able to detect incidents faster and reduce the overall impact and cost of breaches.” – NIST
Typical steps:
- Detect suspicious email activity
- Disable compromised accounts
- Reset credentials
- Scan endpoints for payloads
- Block malicious domains
We’ve handled cases where response within 10 minutes prevented full account takeover, speed is everything here.
Ransomware Response Playbook Steps
Ransomware response playbook steps must prioritize containment first.
- Detect abnormal encryption activity
- Isolate infected systems immediately
- Disable network access
- Identify ransomware variant
- Restore from backups
- Conduct forensic investigation
Organizations we’ve supported recover significantly faster when these steps are predefined and rehearsed.
Data Breach Response Playbook Template
| Phase | Key Action | Responsible Team |
| Detection | Identify breach source | SOC |
| Containment | Limit data exposure | Security Team |
| Notification | Inform stakeholders/regulators | Legal & PR |
| Recovery | Restore and secure systems | IT Ops |
| Review | Post-incident analysis | Management |
A solid data breach response playbook template must align with regulatory obligations from the start.
Creating Effective SOAR Playbooks
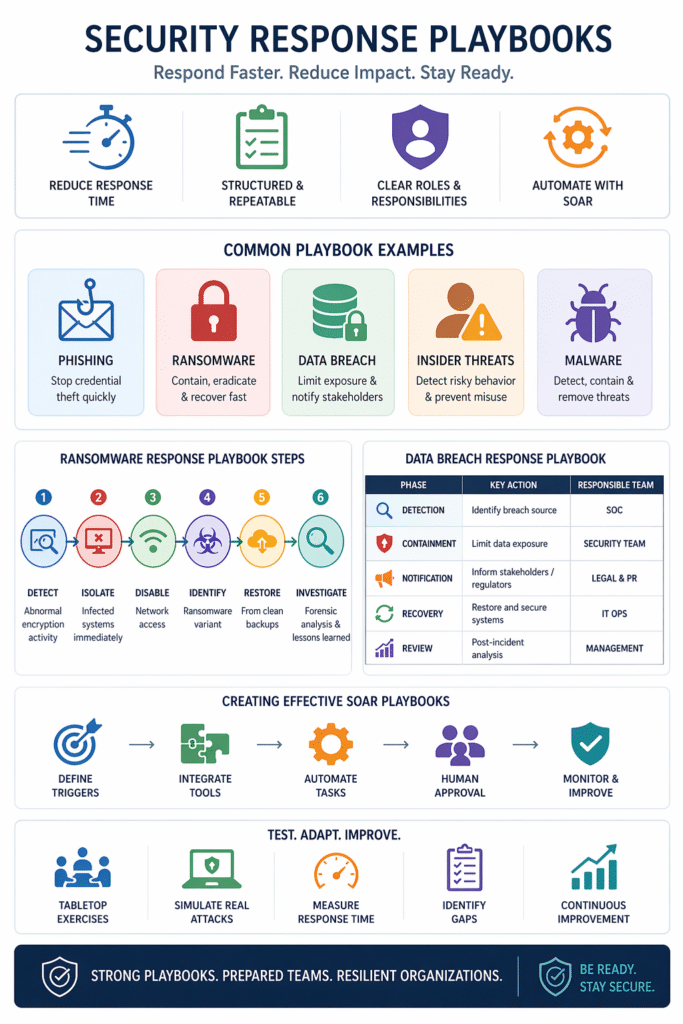
Creating effective SOAR playbooks means combining automation with logic.
- Define clear triggers
- Integrate SIEM, EDR, and email systems
- Automate repetitive tasks
- Add human approval checkpoints
At MSSP Security, we’ve learned that over-automation without context can create new risks, balance is key.
Testing Incident Response Playbooks
Testing incident response playbooks ensures they work under pressure.
- Conduct tabletop exercises
- Simulate real attack scenarios
- Measure response time
- Identify gaps
We’ve seen measurable improvements when teams test quarterly rather than annually.
Customizing Playbooks Specific Threats
Customizing playbooks specific threats makes them effective in real environments.
- Adapt to industry-specific risks
- Align with infrastructure
- Incorporate threat intelligence
- Reflect compliance needs
Generic playbooks rarely succeed in high-pressure incidents, we always tailor them based on real attack patterns.
Playbook Driven Incident Response

Playbook driven incident response enables organizations to act faster and smarter.
- Guides analysts step-by-step
- Improves consistency across teams
- Supports scaling security operations
- Reduces reliance on individual expertise
From what we’ve seen, this approach significantly improves overall security maturity.
FAQ
What is security response playbook?
A security response playbook is a structured, step-by-step guide that helps teams detect, respond to, and recover from cybersecurity incidents. It ensures consistency, reduces response time, and minimizes errors during high-pressure situations.
Why are security response playbook examples important?
Security response playbook examples provide real-world guidance that teams can adapt quickly. From our experience, using proven examples helps organizations avoid delays and respond more effectively during incidents.
What are ransomware response playbook steps?
Ransomware response playbook steps include detecting encryption activity, isolating affected systems, disabling network access, restoring from backups, and conducting forensic analysis to prevent recurrence.
How often should you test incident response playbooks?
Testing incident response playbooks should be done regularly, ideally every quarter, using simulations and tabletop exercises to ensure teams are prepared for real-world attacks.
Building Stronger Security with Response Playbooks
Security response playbooks are essential for modern cyber defense. By combining structured workflows, real-world testing, and SOAR automation, organizations respond faster and more effectively to threats.
Even simple playbooks dramatically improve outcomes when consistently applied. Whether refining processes or starting fresh, the key is continuous improvement and readiness. We offer expert consulting for MSSPs to streamline operations and reduce tool sprawl. Optimize your tech stack and boost service quality today.
References
- https://en.wikipedia.org/wiki/Incident_response
- https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
Related Articles
- https://msspsecurity.com/phishing-incident-response-playbook/
- https://msspsecurity.com/what-is-security-response-playbook/
- https://msspsecurity.com/examples-incident-response-playbooks/
- https://msspsecurity.com/creating-effective-soar-playbooks/
- https://msspsecurity.com/ransomware-response-playbook-steps/
- https://msspsecurity.com/data-breach-response-playbook-template/
- https://msspsecurity.com/testing-incident-response-playbooks/
- https://msspsecurity.com/customizing-playbooks-specific-threats/
- https://msspsecurity.com/playbook-driven-incident-response/
