Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

OT security monitoring helps keep power plants, factories, and water systems safe by finding problems…
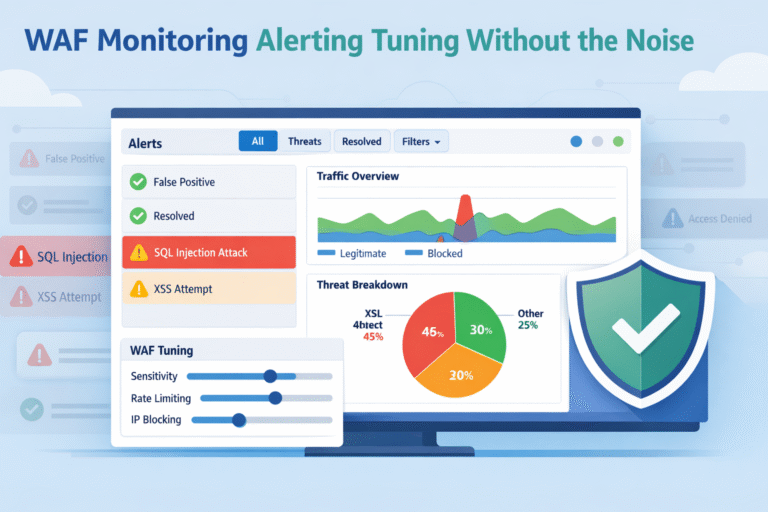
WAF monitoring, alerting, tuning are what make a firewall useful in real life. We can…

Securing web applications compliance should feel like steady engineering, not last-minute chaos. We’ve all seen…

Configuring WAF policies rules means defining how a web application firewall inspects requests and enforces…