Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
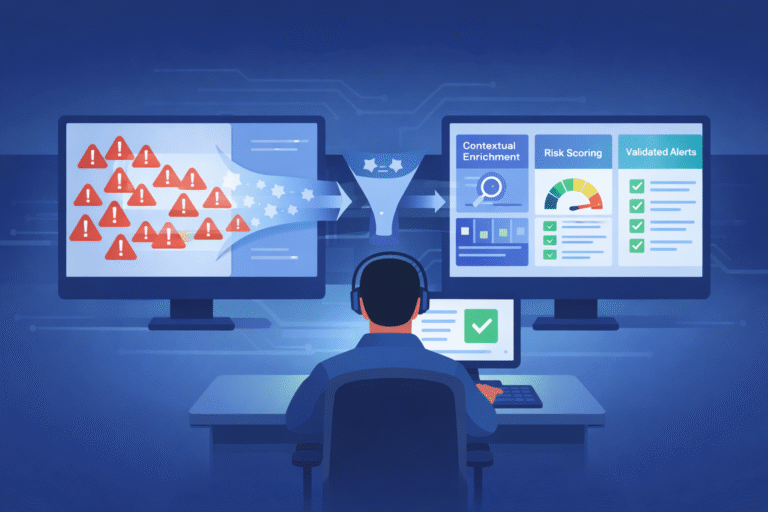
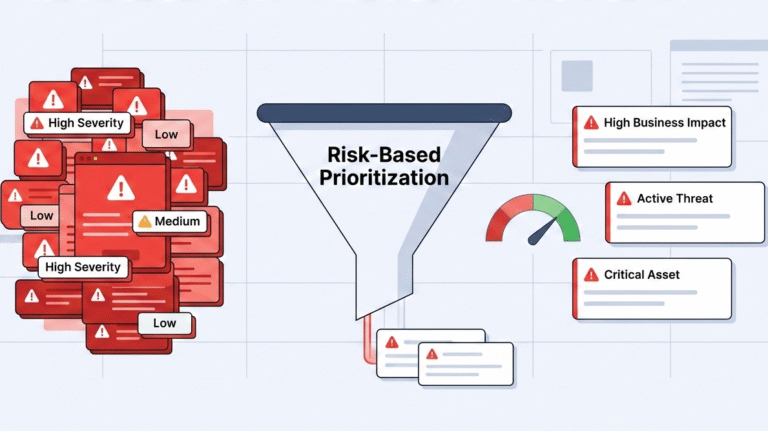
Using threat intelligence triage cuts through alert noise. It uses external data, like known malware…
You’re staring at a dashboard blinking with a thousand identical red warnings. Which one is…
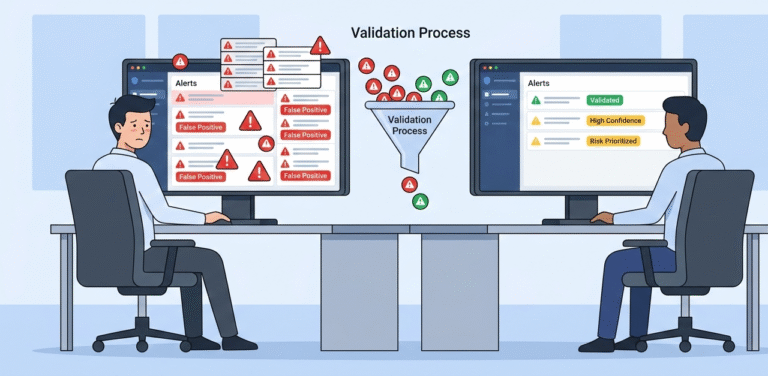
The noise is drowning out the signal. You’re not just getting security alerts; you’re getting…
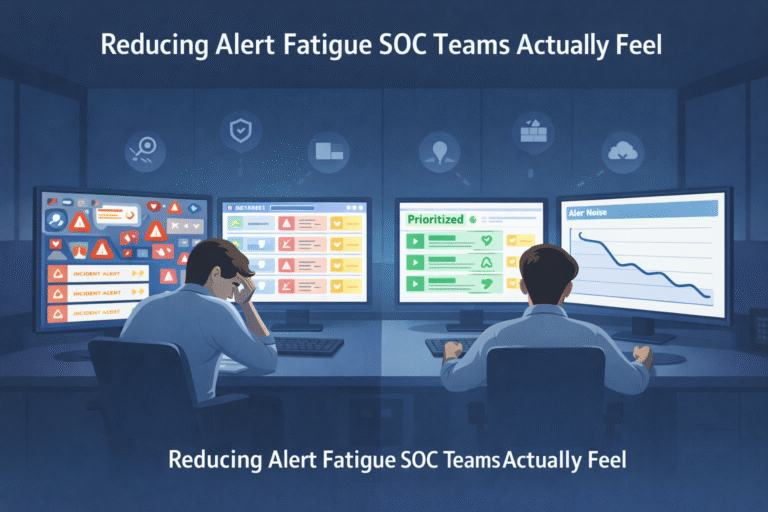
Alert fatigue is the slow, grinding burnout that happens when your security team drowns in…