Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
You’re staring at a wall of alerts. A SIEM blips about weird outbound traffic, an EDR pings on a strange process. Alone, each is just noise. Together, they’re a story. Using SIEM EDR investigation in tandem isn’t just best practice, it’s the only way to see the full attack chain, from the first network probe to the final payload execution on an endpoint.
It turns reactive guesswork into a directed hunt. This method slashes the time it takes to find and contain a breach. Keep reading to see the exact workflow that connects the dots.
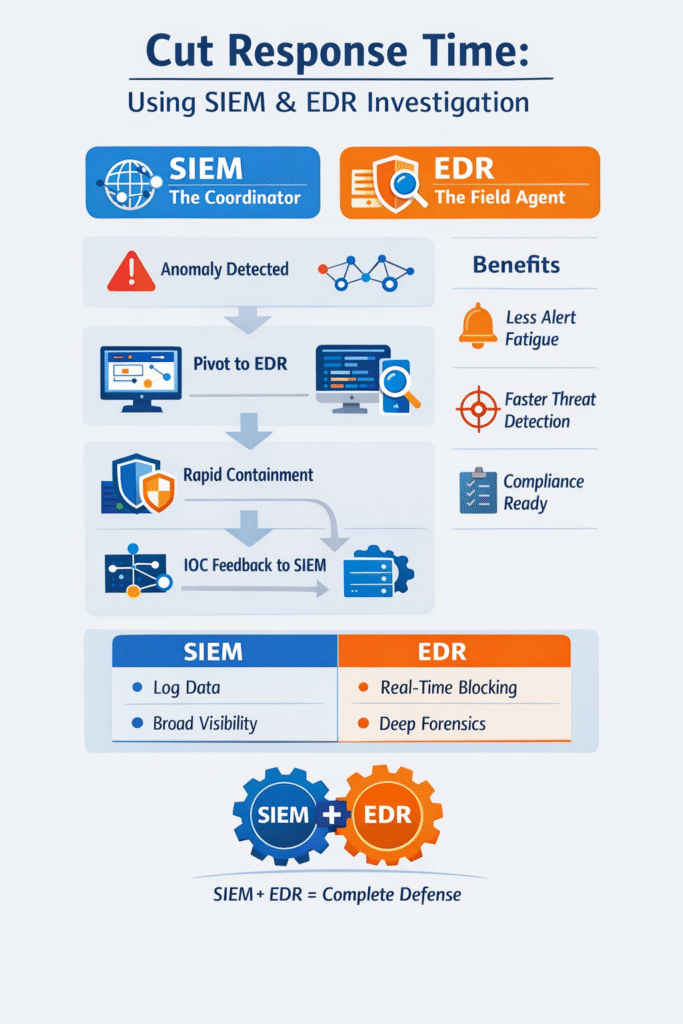
When we help an MSSP pick tools, we look for how they’ll work together in a real crisis. Think of a SIEM and EDR like a detective team. The SIEM is the coordinator with the map, watching traffic patterns across the city. The EDR is the field agent who can kick down a door and dust for fingerprints.
In our work, we see this play out constantly. The SIEM spots the macro-level anomaly, like a login from Prague followed minutes later by a database query from Hanoi. It raises the flag, but that’s just the symptom. Then we pivot. We take the hostname from that alert and jump into the EDR console.
Now we’re on the endpoint. We can see the process tree, the legitimate software spawning a hidden PowerShell instance, the fileless malware living in memory. The SIEM showed us the smoke. The EDR found the fire and the arsonist.
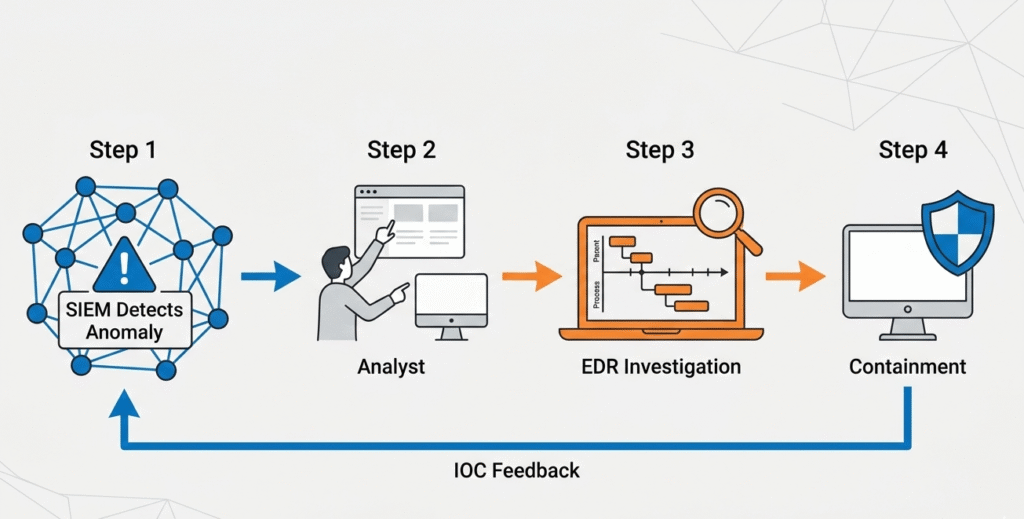
This creates the closed loop we need:
Credits: Pro Tech Show
Investigations rarely move in straight lines. In our consulting work with MSSPs, we help teams refine their incident investigation analysis steps to ensure they start wide, then tighten the scope as evidence builds.
“EDR enables rapid containment and remediation of endpoint threats, while SIEM provides a greater context for broader incident response efforts. When implemented in tandem, EDR and SIEM help MSPs achieve a complete picture of threats targeting your clients in real time.” – ConnectWise
Triage usually begins in the SIEM. A correlation rule fires: repeated failed admin logins from a new country, one success, then traffic to a known bad IP. That’s the thread. The SIEM cuts through massive log volume and hands the analyst something worth pursuing, timestamp, user, source IP.
From there, teams pivot to EDR. This is where the story sharpens. We review the endpoint timeline with clients and often spot the trigger, a spawned PowerShell instance, a fileless payload, registry edits. EDR confirms what the SIEM suggested.
Containment follows quickly. The host gets isolated, IOCs feed back into the SIEM, and the hunt expands. That loop is what turns response into resilience.
One replaces the other? That assumption gets MSSPs into trouble. When we audit stacks, we often find overlap, but not duplication.
A SIEM brings breadth. It collects logs across firewalls, cloud services, SaaS platforms, and identity systems. It’s excellent for correlation, reporting, and compliance evidence. But it doesn’t live on the endpoint. It can’t stop encryption mid-ransomware.
EDR works differently. It sits on the device, tracking behavior in real time. We’ve seen it catch credential dumping and lateral movement that never surfaced clearly in centralized logs. It can isolate a host or kill a malicious process instantly.
Strong programs don’t debate which is better. They design workflows that use both deliberately, macro visibility from SIEM, micro forensics and action from EDR.
| Feature | SIEM (The Coordinator) | EDR (The Field Agent) |
| Primary View | Network-wide, macro-level patterns | Endpoint-specific, micro-level activity |
| Best For | Log aggregation, compliance, correlation | Real-time blocking, deep-dive forensics |
| Data Source | Logs from hundreds of different systems | Telemetry from endpoint agents |
| Response Action | Alerts and orchestration playbooks | Automated isolation and process kill |
Disconnected tools create blind spots. During product audits, we often discover SIEM and EDR running in parallel but not sharing intelligence. That gap is where attackers operate.
“Here’s the key distinction: EDR provides depth on managed endpoints. SIEM provides breadth across all infrastructure. Neither alone provides complete visibility. At UnderDefense, our managed SIEM service combines both data streams with 24/7 analyst correlation.” – UnderDefense
Consider cloud data theft using stolen API keys. No endpoint artifact. EDR sees nothing. A properly tuned SIEM, ingesting audit logs, flags unusual access patterns. On the other hand, fileless malware may leave minimal log traces but trigger behavioral alerts on the endpoint.
When integrated, the tools reinforce each other. We help MSSPs configure automated IOC sharing, malicious hashes, IPs, domains flowing between platforms. Once EDR confirms compromise, the SIEM hunts enterprise-wide. Clients move from isolated response to coordinated defense in minutes.
For MSSPs evaluating new products, this interoperability is not optional. It’s one of the first controls we assess.Strong programs don’t debate which is better. They design workflows for correlating events that use both deliberately, macro visibility from SIEM and micro forensics from EDR.

Deployment is the easy part. Keeping it effective takes discipline, especially when documenting incident investigation findings to identify where alert fatigue traces back to neglected rule tuning.
Correlation rules need regular adjustment. Default content rarely fits a client’s environment. We recommend monthly reviews, retire noisy rules, refine thresholds, and add detections aligned to current threat patterns.
Agent health is another blind spot. An offline EDR agent on a critical server quietly erodes visibility. We push MSSPs to monitor agent coverage as a core service metric. You can’t defend what you can’t see.
Threat intelligence should also feed the system continuously. When new malware indicators surface, both SIEM and EDR must ingest them. An integrated stack should evolve. Otherwise, it slowly drifts from defense tool to compliance checkbox.
Using SIEM and EDR together improves threat detection by connecting log data with endpoint behaviour. Security Information and Event Management highlights unusual patterns across the corporate network, while Endpoint Detection and Response inspects malicious processes on devices.
This combined view strengthens incident investigation, reduces visibility gaps, and helps security analysts confirm real threats faster with stronger security telemetry and forensic analysis.
Yes, using siem edr investigation helps reduce alert fatigue through better alert triage and data enrichment. Instead of reviewing raw data from multiple security platforms, analysts see correlated security data tied to real risk.
Behavioral analytics and machine learning filter noise, while response automation supports faster incident response. This keeps the security operations center focused on meaningful threat detection.
Using siem edr investigation supports threat hunting by combining cloud API activity, log analysis, and endpoint security insights. It allows teams to track lateral movement, fileless malware, and LotL attacks across cloud-native environments and endpoint environments.
Threat intelligence feeds and IOC detection improve visibility into threat actor behavior, helping security analysts investigate zero-day exploits and suspicious container activity.
This approach strengthens compliance reporting for ISO 27001, PCI DSS, and SOC 2. Security Information & Event Management centralizes log data, while Endpoint Detection & Response provides forensic investigation evidence from endpoint environments.
Together, they create detailed incident investigation records, improve security policies enforcement, and demonstrate consistent cybersecurity measures across the enterprise’s infrastructure and cloud workloads.
Tools don’t win investigations, people and process do. We’ve seen MSSPs cut dwell time dramatically when SIEM and EDR function as one workflow, not separate consoles. The shift happens when teams stop clearing alerts in isolation and start tracing connected events across systems.
If you’re rethinking your stack or integration strategy, join us here. We help MSSPs select, audit, and optimize tools to reduce sprawl, improve visibility, and strengthen real-world investigations.