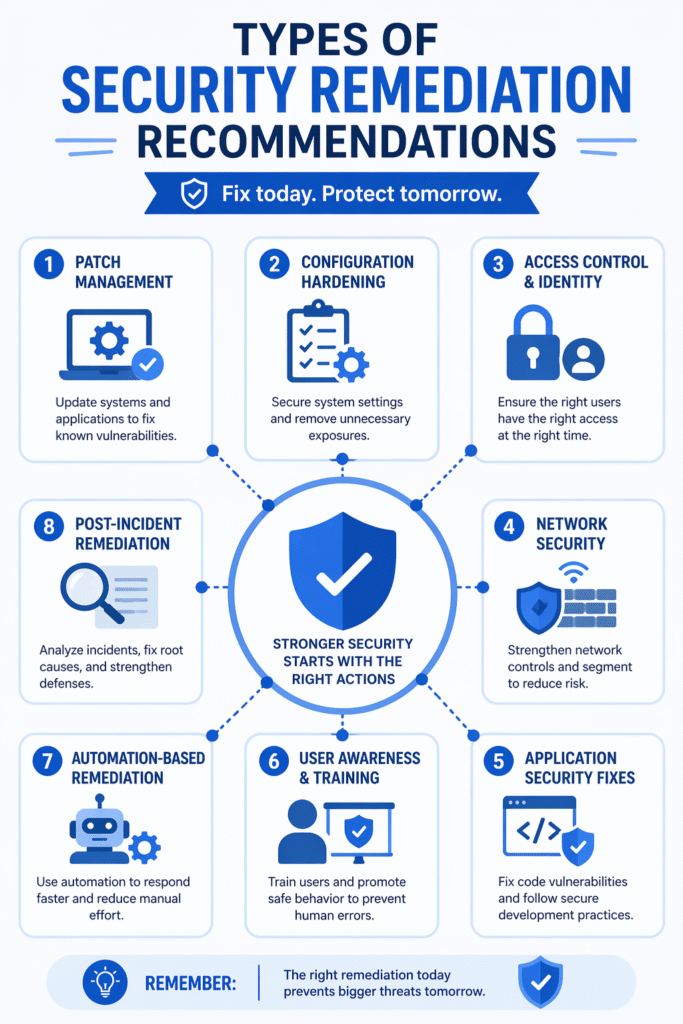
Understanding the types security remediation recommendations is essential for organizations aiming to strengthen their cybersecurity posture. Detecting vulnerabilities is only the first step, knowing how to fix them properly is what truly reduces risk.
Different threats require different remediation strategies, from patching systems to improving access controls. Without clear guidance, teams may apply the wrong fixes or delay critical actions. This article explores the key types of remediation recommendations and how they help organizations respond effectively. Keep reading to learn more.
Key Insights on Types of Security Remediation Recommendations
Security remediation recommendations provide structured ways to eliminate vulnerabilities and prevent future threats.
- Multiple approaches: Different threats require different remediation strategies
- Risk-focused actions: Recommendations are based on severity and impact
- Continuous improvement: Fixes help strengthen long-term security posture
Patch Management Recommendations
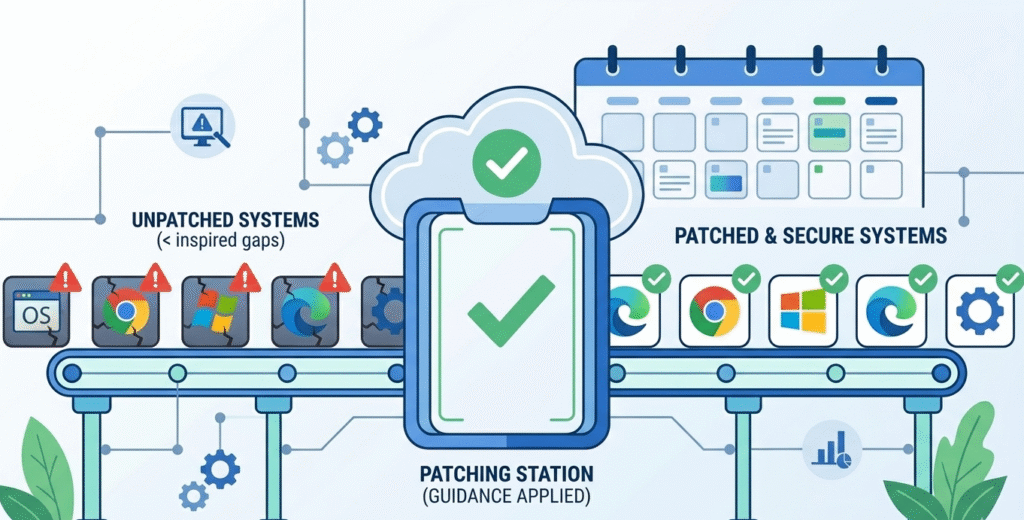
One of the most common remediation strategies is applying security patches to fix known vulnerabilities.
Key actions include:
- Updating operating systems
- Installing software patches
- Fixing outdated libraries
Timely patching reduces the risk of exploitation and keeps systems secure.
Configuration Hardening Recommendations
Misconfigurations are a major source of security risks. Hardening recommendations focus on securing system settings.
Typical actions:
- Disabling unnecessary services
- Enforcing secure configurations
- Applying baseline security standards
“In computer security, hardening is the process of securing a system by reducing its surface of vulnerability.” – Wikipedia
Proper configuration ensures systems are less vulnerable to attacks.
Access Control and Identity Management
Credits: Josh Madakor
Managing who has access to systems is critical in preventing unauthorized activities.
Recommendations include:
- Implementing least privilege access
- Enforcing multi-factor authentication (MFA)
- Reviewing user permissions regularly
These actions reduce insider threats and limit attacker movement within systems.
Network Security Improvements
Network-level remediation focuses on protecting communication channels and isolating threats.
Common actions:
- Segmenting networks
- Configuring firewalls
- Monitoring traffic
Network improvements help contain threats and prevent them from spreading across systems.
Application Security Fixes
Applications often contain vulnerabilities that require specific remediation.
Typical fixes:
- Updating insecure code
- Fixing input validation issues
- Addressing injection vulnerabilities
Secure coding practices play a key role in reducing application-level risks.
Endpoint and System Remediation
Endpoints such as laptops and servers are frequent targets for attackers.
Remediation actions:
- Installing endpoint protection tools
- Removing malware
- Updating system defenses
These steps ensure devices remain secure and resilient against threats.
User Awareness and Training
Human error is a major factor in cybersecurity incidents. Remediation can involve improving user behavior.
Key actions:
- Security awareness training
- Phishing simulations
- Policy education
“Human factors remain a significant contributor to cybersecurity incidents.” – ScienceDirect
Educating users reduces the likelihood of succeThe impact of excluding common blocks for approximate matching – ScienceDirectssful attacks.
Automation-Based Remediation
Automation helps organizations respond quickly to threats. Understanding how MSSPs provide remediation guidance through automated workflows can significantly reduce manual workload and ensure consistent responses.
Examples:
- Auto-patching systems
- Blocking malicious IPs
- Triggering response workflows
Automation improves efficiency and ensures consistent responses.
Post-Incident Remediation Actions
After a security incident, organizations must strengthen defenses to prevent recurrence. Once remediation guidance is explained through a root cause analysis, teams can update security policies and improve monitoring systems more effectively.
Actions include:
- Root cause analysis
- Updating security policies
- Improving monitoring systems
These steps turn incidents into opportunities for improvement.
Tracking and Measuring Remediation Effectiveness
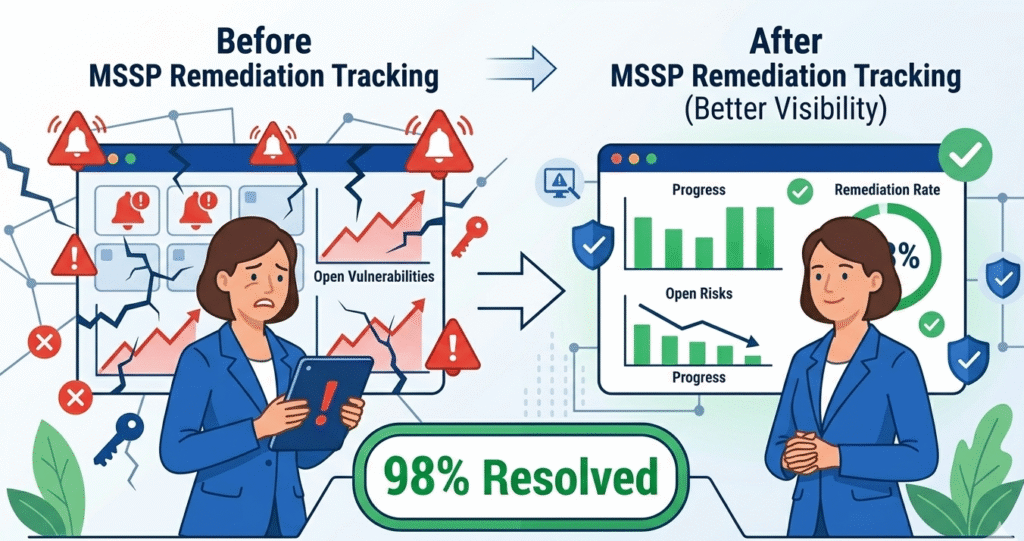
To ensure success, organizations must track outcomes and focus on prioritizing remediation steps that offer the highest risk reduction. This level of tracking ensures accountability and continuous improvement.
| Metric | Purpose | Benefit |
| Time to Remediate | Measures response speed | Improves efficiency |
| Vulnerability Closure | Tracks resolved issues | Ensures completeness |
| Risk Reduction | Evaluates security improvement | Demonstrates effectiveness |
Tracking ensures accountability and continuous improvement.
FAQ
What are security remediation recommendations?
Security remediation recommendations are structured actions designed to eliminate vulnerabilities after they are identified. These recommendations go beyond simple fixes, they often include a combination of technical solutions (like patching or configuration changes), process improvements, and sometimes user-related actions.
The goal is not only to resolve the current issue but also to reduce the likelihood of similar vulnerabilities appearing in the future.
Why are there different types of remediation?
Different vulnerabilities arise from different sources, such as outdated software, misconfigurations, weak access controls, or human error. Because of this, a single approach cannot address all risks effectively.
For example, a software flaw requires patching, while a misconfigured system needs hardening. Using the correct type of remediation ensures that the root cause is addressed, not just the symptoms of the issue.
Which remediation type is most important?
There is no single “most important” type because the priority depends on the specific risk context. However, patch management and access control are often considered critical because they directly impact system exposure and attacker access.
In practice, organizations should prioritize remediation based on risk level, business impact, and exploitability rather than relying on a fixed hierarchy of importance.
Can remediation be automated?
Yes, many remediation tasks can be automated, especially repetitive and well-defined actions such as patch deployment, blocking malicious IP addresses, or isolating compromised devices. However, automation is not a complete solution.
Complex vulnerabilities, business-critical systems, and strategic decisions still require human expertise to avoid unintended consequences and ensure that remediation aligns with organizational goals.
Strengthening Security Through the Right Remediation Strategies
Effective security requires more than just finding flaws; it demands precise action. By balancing patching, configuration fixes, and access control, organizations can transform vulnerabilities into resilience. MSSP Security provides the specialized consulting necessary to streamline operations and reduce tool sprawl.
With 15 years of experience and 48,000+ projects completed, we offer vendor-neutral auditing and stack optimization to ensure your technology aligns with your operational maturity. Ready to build a more efficient cybersecurity practice? Join MSSP Security today.
References
- https://en.wikipedia.org/wiki/Hardening_(computing)
- https://www.sciencedirect.com/science/article/abs/pii/S0167404819302159?via%3Dihub
