Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

You need a security incident investigation process that works in 2026, not 2016. It’s a structured, blame-free cycle of preparation, detection, containment, and learning, designed to stop the bleed and kill the root cause for good.
The goal isn’t just to clean up a mess, it’s to build an organization that’s harder to hit next time. Forget chasing sci-fi threats; the real work is mastering fundamentals now supercharged by AI and human behavior. This is how you move from reactive firefighting to proactive resilience. Keep reading to map your path.
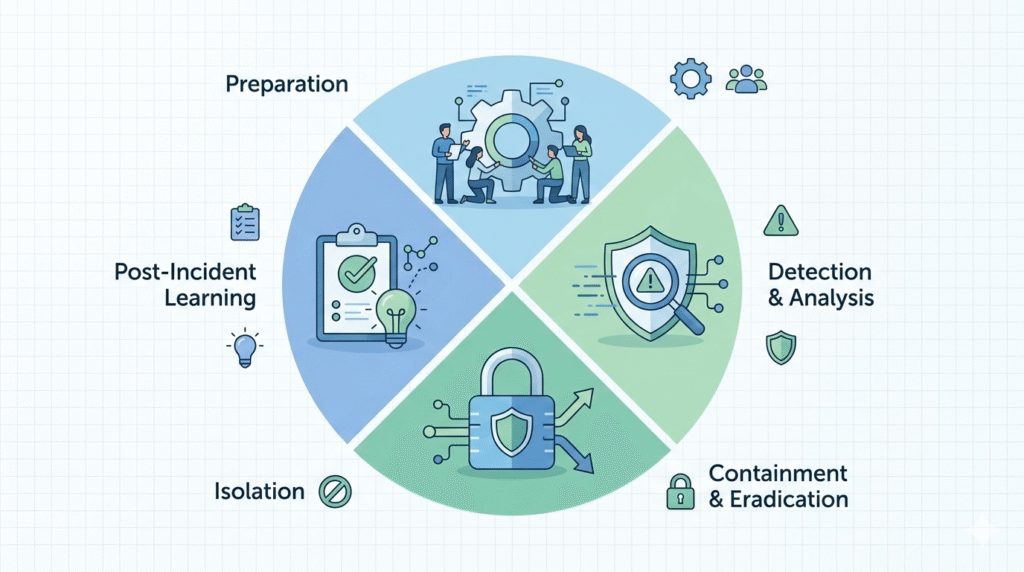
We help MSSPs pick and audit security products, so we see these investigations up close. It’s a four-part cycle, but it’s really a story about closing the loop.
First, you get ready. That’s the preparation phase, where you build your team and baseline your monitoring. No alert has even fired yet; once it does, applying specific steps to analyze a security incident allows the real work of detection to begin. You’re sifting through alerts, checking them against known Indicators of Compromise (IoCs) to figure out if it’s a real breach or just noise.
Then you move fast. Containment is the emergency stop. You isolate affected systems to stop the bleeding. Eradication comes next, which means finding and ripping out the root cause of the incident.
For us, the last phase is everything. Post-incident activity isn’t just paperwork. It’s where you document what happened and why, turning a single event into a permanent upgrade for your defenses. That final step dictates most of your future security posture.
The Core Lifecycle:
Executing a forensic investigation is always a balancing act. Move too slowly and the attacker spreads; move too fast and evidence gets compromised. In our work advising MSSPs on tooling and workflows, we’ve seen solid investigations fall apart because teams skipped basic discipline.
“Procedures for detection and triage should enable analysts to transition from alert to verified incident in minutes, rather than hours. Key principles include: Clear validation criteria: Define what constitutes a true incident, reducing noise from false positives. Prioritization logic: Rank incidents by potential business impact, not just technical severity.” – Sygnia
A standardized workflow keeps everyone grounded when pressure spikes. Following structured incident investigation analysis steps ensures the scene is secured, stakeholders are looped in, and evidence handling stays defensible.
| Investigation Phase | Key Tool/Entity | Primary Goal |
| Triage | SIEM/EDR | Confirm if the alert is a true positive. |
| Forensics | Volatility/FTK | Extract evidence from volatile memory. |
| RCA | NIST 800-61 | Identify the vulnerability exploited. |
Credits: Ascend Technologies
Human error remains one of the easiest ways into any environment. What many organizations miss is how their own culture either speeds up detection or quietly delays it. When teams fear punishment, incidents stay hidden longer. In several MSSP environments we’ve reviewed, delayed self-reporting added hours or days, to attacker dwell time.
A blame-free approach changes the math. It encourages fast reporting and gives investigators a head start. We’ve repeatedly seen stronger outcomes when organizations:
The difference is measurable. When staff speak up quickly, containment happens dramatically faster. Culture becomes an early-warning sensor that no tool alone can replicate, especially with risks like shadow AI usage quietly growing inside modern environments.
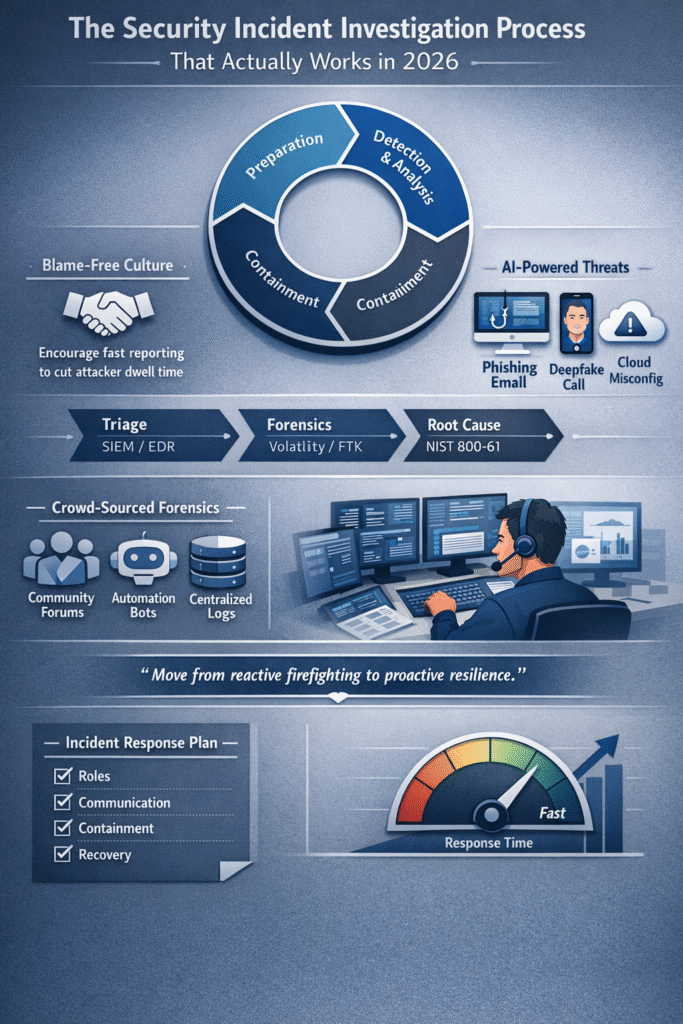
The threats themselves aren’t entirely new; what’s changed is the speed and scale. Across the MSSP clients we support, familiar attack paths are now heavily automated and far more convincing. Investigators in 2026 must assume adversaries are using AI to accelerate reconnaissance and social engineering.
“Security logs undergo evaluation to find the cause of the breach along with data assessment regarding affected information. … MSSPs use comprehensive forensic investigation techniques to extract information about enemy tactics techniques as well as procedures after successful attack containment. Therefore, the analysis of system logs leads to tracking down attack sources while identifying system weaknesses.” – ITButler
We’re consistently seeing three patterns dominate:
AI acts as a multiplier, not a replacement. Attackers still rely on weak processes, over-privileged accounts, and rushed teams.
In our product audits, environments with strong fundamentals, segmentation, monitoring, and identity controls, continue to blunt even AI-assisted campaigns. The lesson is simple: modernize detection, but don’t neglect the basics.
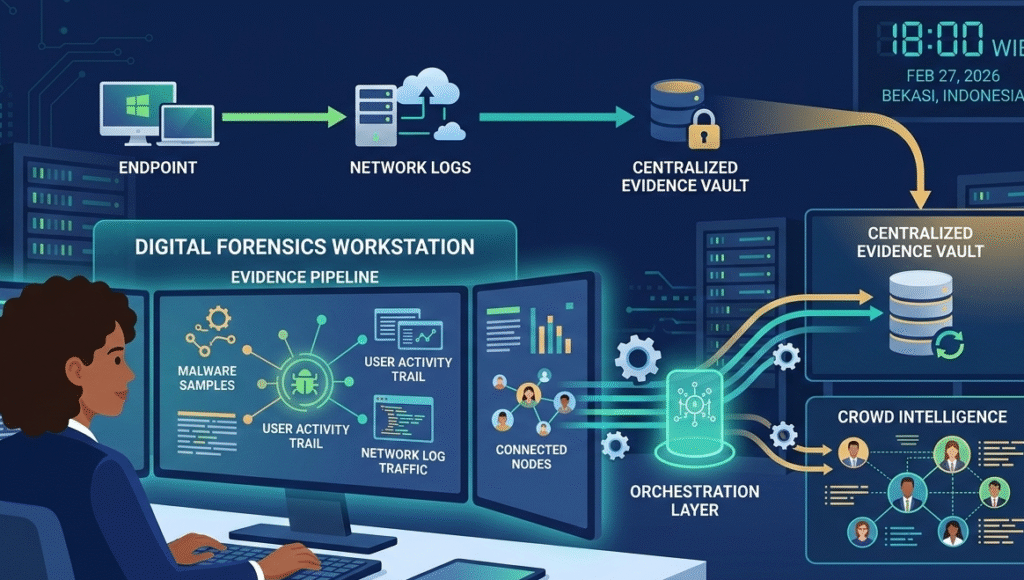
Digital forensics never stands still. Operating systems shift, artifacts move, and traditional playbooks age quickly. When we help MSSPs evaluate investigation tooling, the gap usually isn’t visibility, it’s adaptability. Teams relying only on static guidance often struggle when platforms change underneath them.
What works best today is a hybrid approach: Tap practitioner communities for real-time artifact changes. Integrating faster soc analyst alert investigation steps into your orchestration allows you to automate routine evidence gathering and reduce cross-tool friction.
Crowd-sourced knowledge has become surprisingly practical. We’ve seen investigators resolve mobile artifact issues weeks earlier by monitoring practitioner forums. At the same time, regulatory pressure keeps rising, demanding cleaner audit trails and faster response.
MSSPs that combine automation, community intelligence, and disciplined process are the ones keeping investigations predictable under real-world pressure.
A strong incident response plan defines roles, communication channels, and containment strategies before a security incident occurs. It should guide the incident response team through detection and reporting, assessment and decision-making, and recovery.
Good Cyber Security Incident Response Plan documents also align with regulatory obligations and Incident Response Frameworks, ensuring security incident management stays consistent under real pressure.
SOC analysts validate a suspected security event by reviewing security logs, system logs, and indicators of compromise. They correlate data from security information and event management platforms, intrusion detection systems, and network infrastructure.
Fast log review and threat intelligence analysis help separate noise from true security threats, allowing the investigation process to move forward with confidence.
During Incident Investigations, teams collect forensic artifacts such as system logs, malware samples, IP address data, and physical evidence when relevant. A forensic specialist uses write blocker tools to preserve the chain of evidence.
Proper evidence collection supports forensic analysis, helps legal teams if needed, and ensures the incident report stands up to regulatory scrutiny.
Effective Corrective Actions address the Root Causes behind security breaches, not just the symptoms. Security operations teams update security controls, apply security patches, and improve containment strategies.
Many organizations also adjust their Security Incident Management Policy and run new risk assessment cycles. Over time, these steps strengthen the incident response process and reduce repeat incidents.
That’s the blueprint. The work lies in execution, building an organization that grows stronger from every incident, not just survives them. Start by reviewing your last post-mortem. Was it honest? Did it spark real change?
But refining your process is just one piece. To truly harden your defenses, you need a tech stack that’s built for this new era. That’s where we come in. We help MSSPs cut through the noise, select the right tools, and optimize their operations. Let’s build your resilient foundation together.
Let’s Build Your Perfect Tech Stack