Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Securing industrial control systems (ICS) means protecting the physical processes in factories, power grids, and water utilities from cyber threats. The objective is to maintain safety, stability, and continuous operation, because failures here have real-world consequences.
We have worked with operators for whom any downtime, even for security updates, is unacceptable. This guide breaks down how ICS security functions in practice and how a layered defense approach reduces risk without halting production. Keep reading to learn what actually holds up in operating plants.
Industrial Control Systems (ICS) are the hardware and software that run physical processes in factories, power grids, and water plants. They prioritize keeping things running and safe over keeping data secret.
Protecting these environments often requires advanced specialized services that understand how cyber actions translate directly into physical outcomes. A cyber problem here can stop production or cause real damage.
First, much of the equipment is decades old and can’t be updated. Second, the industrial protocols they use, like Modbus, were designed for reliability, not security, they lack basic authentication. Third, any unexpected delay or behavior from a security scan can trigger an automatic, costly shutdown.
The main risks stem from:
This is why standard IT security tools, which often cause latency or reboots, simply don’t work in an ICS environment.

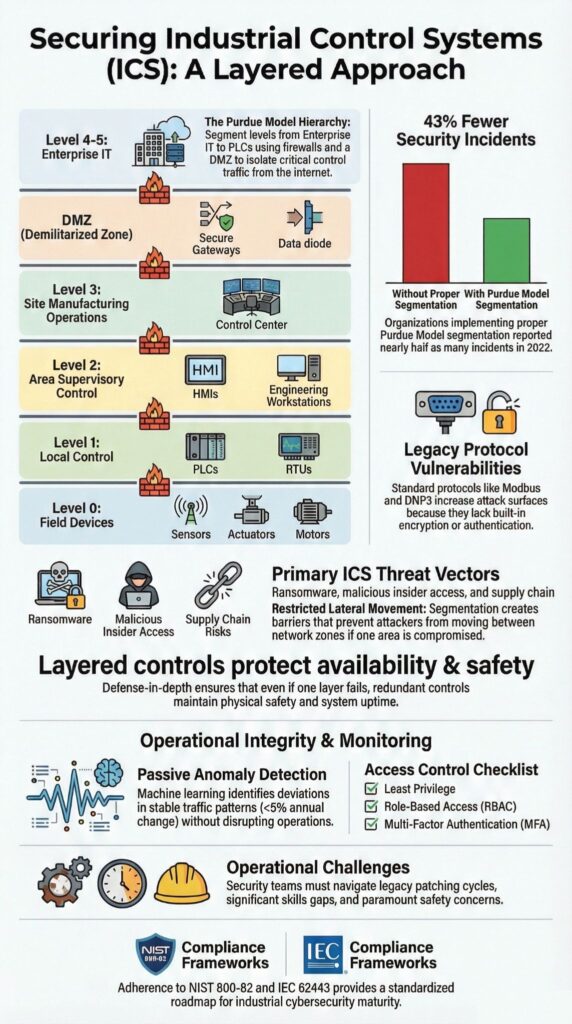
The most common threats to ICS are ransomware, unauthorized access, and targeted attacks designed to disrupt or manipulate physical processes. Continuous OT security monitoring is critical for detecting these threats early, especially when legacy systems cannot support endpoint protection or frequent patching.
Ransomware is particularly disruptive. We’ve seen cases where attackers didn’t even touch the PLCs. Instead, they encrypted the historian servers or engineering workstations, which was enough to stop production completely. In OT, an outage isn’t about lost data, it’s about millions in lost output per day.
Other major threats include:
The risk is heightened by common weaknesses in these environments. Flat networks and shared login credentials let attackers move easily from an office computer to a critical control system.
In our security assessments, we frequently find that third-party vendor accounts have permanent, poorly monitored access that bypasses security controls. This kind of exposure, combined with legacy systems that can’t be patched, makes ICS a high-value target for both criminals and state-sponsored groups.
Credits: Operational Excellence Mastery
Network segmentation cuts risk in ICS security by creating strict boundaries. It isolates operational technology from the corporate IT network, limiting how far an attacker can move if they get in.
Good segmentation uses:
When complete isolation isn’t possible, one-way data diodes are a strong alternative. They allow necessary data, like production reports, to flow out to IT while completely blocking any inbound traffic from reaching the OT network, maintaining a critical layer of protection.
| Purdue Level | Typical Systems | Primary Function | Security Purpose |
| Level 4 | Enterprise IT Systems | Business operations, email, ERP | Isolate IT threats from OT environments |
| Level 3 | Operations & Control | Historians, OT servers | Control data flow between IT and OT |
| Level 2 | Supervisory Control | HMIs, SCADA servers | Prevent unauthorized control actions |
| Level 1 | Basic Control | PLCs, RTUs | Maintain real-time control integrity |
| Level 0 | Physical Process | Sensors, actuators | Ensure safe physical operation |
Strong access control is about limiting who can touch critical industrial equipment, which directly reduces the risk of unsafe or unauthorized actions.
Many operators support these controls with managed OT security monitoring to detect credential misuse, unauthorized sessions, and risky access patterns that traditional logging often misses. Credential misuse is a huge problem; NIST notes over 80% of breaches involve stolen or misused logins, and OT environments are just as vulnerable.
Effective controls must work with operational reality. Engineers need access during emergencies, and overrides must still function. The goal is to manage risk, not create new bottlenecks.
Key practices include:
Shared accounts are still common due to shift work and old systems that don’t support individual logins. We’ve seen plants where removing them too quickly caused delays.
The practical approach is gradual: start by improving logging on shared accounts, then slowly introduce role-based access for key systems. This balances security with the need to keep production running safely.
Monitoring and anomaly detection can protect ICS without causing problems because the best approach is entirely passive. It watches network traffic without ever sending commands to the equipment, so there’s zero risk of disrupting a running process.
ICS networks are remarkably stable. Studies show less than 5% of their behavior changes in a typical year. This predictability is what makes anomaly detection so powerful. This is particularly vital as the threat landscape evolves due to connectivity; as noted :
“The integration of industrial legacy systems with advanced IT networks has introduced new types of vulnerabilities and changed the behaviour of attacks. The lack of a unified hunting solution for integrated IT and OT networks is the gap that is considered in our paper.” – IEEE Access [1]
The key capabilities to look for are:
Anomaly detection spots the unusual pattern, like a write command sent at 3 a.m. from an engineering station that’s usually read-only. This method, especially when enhanced with machine learning tuned for predictable OT traffic, focuses on real risk and keeps false alarms to a minimum.
Implementing an ICS security framework faces real-world hurdles. Operational needs, tight budgets, and a lack of skilled people often slow things down.
From our consulting work with MSSPs, we see a few consistent roadblocks, particularly the “skills gap” between IT and OT. Managed services play a crucial role in bridging this divide. According to :
“Managed industrial security services can contribute to stabilize the industrial system… The CSOC [Cyber Security Operations Center] acts as an essential delivery platform for MSSPs to manage the complexity of today’s challenges for managers of this technical transition.” – AI & SOCIETY [2]
From our consulting work with MSSPs, we see a few consistent roadblocks:
Success requires bridging the gap between control engineers, who know the process, and security analysts, who know the threats. Effective programs build a shared language and foster collaboration between these teams, which takes dedicated time and training.
ICS security prioritizes system availability and operational integrity over data confidentiality. OT security protects SCADA systems, PLCs, and DCS environments that control physical processes and cannot tolerate downtime.
Many ICS networks use legacy devices and insecure protocols like Modbus, so controls such as network segmentation ICS, industrial firewalls, and anomaly detection ICS must work without interrupting operations.
Network segmentation ICS restricts how data and threats move across Purdue model levels. Proper Purdue level segmentation and demilitarized zones ICS separate IT and OT networks.
This design limits lateral movement, reduces ransomware ICS impact, and enforces least privilege OT access. Segmentation also supports zero trust ICS by clearly defining and controlling trusted communication paths.
When legacy system patching is not possible, organizations must use compensating controls. These include PLC hardening, protocol whitelisting, deep packet inspection OT, and strict network isolation.
Asset inventory OT and role-based access ICS reduce unnecessary exposure. Continuous OT intrusion detection helps identify abnormal behavior without affecting real-time OT constraints.
Frameworks such as NIST 800-82, IEC 62443 compliance, ISA99 standards, and NERC CIP compliance provide structured guidance for ICS security.
They define requirements for risk assessment ICS, vulnerability management ICS, incident response OT, and secure remote access ICS. These standards help organizations manage OT-IT convergence while maintaining safe and reliable operations.
Modern detection relies on OT intrusion detection, behavioral analytics OT, and industrial protocol analysis.
Anomaly detection ICS monitors PLC commands, ladder logic security changes, and protocol behavior such as DNP3 encryption misuse. SIEM for ICS and threat hunting OT enable early identification of denial of service OT and man-in-the-middle ICS attacks.
Securing industrial control systems is a long-term discipline. It requires layered, practical defenses that respect operational reality, better segmentation, tighter access controls, and passive monitoring. We’ve seen these steady improvements cut risk without disrupting production. Effective security evolves with new threats and isn’t a one-time project.
Need a partner to guide your strategy?
Partner with MSSP Security for expert guidance
We offer vendor-neutral consulting for MSSPs, from product selection to stack optimization, helping you build a resilient security program.