Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

You can reducing human error risk security by accepting that people will always make mistakes and building a system that accounts for it. The goal isn’t perfection, it’s resilience. This means moving beyond annual training videos to a layered defense combining culture, smart technology, and clear processes.
We see it work every day. When you stop blaming the user for clicking a link and start asking why the link got through in the first place, you start winning. The data is brutal, human factors are involved in 60% of breaches, but the solution is practical. Keep reading to see how to build your human firewall.

I watched a CFO approve a six-figure wire last year. The email looked like the CEO’s, the story was urgent and plausible. It felt real until we made a phone call. That simple, second-channel verification stopped it. No AI required.
That moment defined the problem. You can have the best technical defenses money can buy, but a stressed, trusting person becomes an open gate. Verizon’s data has shown for years that the human element drives most breaches. The latest report puts it at 74%.
In our work with MSSPs, we see this firsthand. The push for new awareness training platform options is relentless, but evaluations often skip the human impact. We help audit not just the tool, but how it affects an analyst’s real workflow.
A “better” product that increases fatigue might just automate failure. Our job is to make sure new technology closes gates, not creates them.
Credits: Smartsheet
It’s not malice. It’s distraction. An employee gets 120 emails a day. One slips through the filter, it looks like a shipping notification from a real vendor, and they click. That’s it. The IBM Cost of a Data Breach Report notes breaches caused by human error average $4.44 million. The cost isn’t just financial, it’s operational chaos and lost trust.
“While human error may never be completely eliminated from the tasks they perform due to poor situational awareness, or a lack of adequate training, the first step to make improvements over the status quo is to establish a unified scheme to classify such security errors.” – Kennesaw State University
The common failures follow a pattern we see repeatedly:
The psychology is simple. Attackers exploit urgency, authority, and our natural desire to be helpful. Your security awareness training has to speak to that, not just list threats.
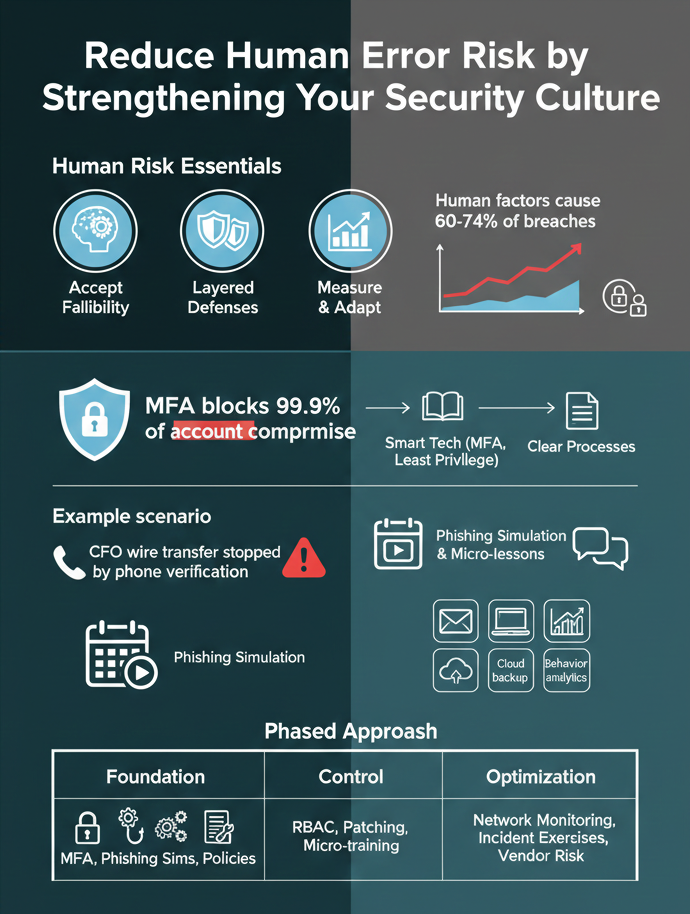
This is where philosophy meets practice. If you assume people will err, your security architecture changes. You stop relying on them to be the single point of failure. At an MSSP like ours, we build layers so that one slip doesn’t mean a breach.
First, you enforce multi-factor authentication (MFA) everywhere you can. Microsoft says it blocks over 99.9% of account compromise attacks. It’s the single most effective technical control. Second, you adopt the principle of least privilege. Does your accounts payable clerk need access to the entire HR database? No. Limit access by role.
Third, you automate the tedious stuff. Automated patch management, automated alerts for suspicious logins, automated blocking of phishing domains. You take the memory task away from the human.
We helped a mid-sized manufacturer implement just these three steps. Their incident response logs showed a 40% drop in actionable security alerts within six months. The noise went down, and their team could focus on real threats.
Annual, hour-long, mandatory training modules are close to useless. People click through them. The knowledge doesn’t stick. Effective training is continuous, contextual, and consequence-free.
We run phishing simulation training for our clients. Not to shame employees, but to gather data. Not to shame employees, but to gather data. When someone fails a simulation, they get a 60-second micro-lesson right then, why that email was suspicious, what to look for next time.
This is key: the training happens at the “teachable moment.” Over a year, we’ve seen phishing click rates drop from an industry average of about 30% to under 5% for engaged clients.
The content can’t be theoretical. Use examples from your own industry. For a healthcare client, we simulate HIPAA-related phishing. For a law firm, we mimic client impersonation. Make it real. And crucially, reward reporting. If an employee forwards a suspicious email, thank them publicly. That positive reinforcement builds a culture where security is everyone’s job.
Technology is your force multiplier. It provides the consistency that human attention cannot. We deploy a suite of tools designed to create safety nets.
“Human error can only occur where there is opportunity for it to do so. That may seem obvious, but the point is that the more opportunities there are for something to go wrong, the higher the chance that a mistake will be made at some point.” – uSecure
Email defense software with advanced filtering catches the majority of malicious messages before they hit the inbox. Endpoint Detection and Response (EDR) tools on every device look for strange behavior, like a spreadsheet suddenly trying to run a script. Cloud Backup solutions ensure that if ransomware does get triggered, your data isn’t held hostage.
Perhaps most importantly, network monitoring and behavioral analytics platforms establish a baseline of normal activity. They can flag when a user account starts accessing files at 3 a.m. or downloading huge volumes of data.
These tools aren’t set-and-forget. They require tuning. That’s a core part of our service, interpreting the alerts, reducing false positives, and making sure the security team is alerted to genuine risks, not just noise.

You don’t need to do everything at once. This table outlines a phased approach that balances immediate impact with sustainable culture change.
| Phase | Primary Actions | Expected Outcome |
| Foundation (Months 1-3) | Enforce MFA on all critical systems. Implement weekly phishing simulations with instant feedback. Draft clear data handling policies. | Rapid reduction in credential theft and successful phishing. Clear rules of engagement for staff. |
| Control (Months 4-6) | Roll out least-privilege access controls (RBAC). Deploy automated patch management. Begin formal security awareness micro-training program. | Reduced attack surface. Faster mitigation of known software vulnerabilities. Measurable improvement in staff security IQ. |
| Optimization (Ongoing) | Deploy advanced network & user behavior monitoring. Conduct quarterly tabletop incident response exercises. Integrate risk assessments into vendor onboarding. | Proactive threat hunting. Prepared and practiced response team. Systemic understanding of third-party risk. |
Start with the Foundation. The ROI is almost immediate. The Control phase solidifies your gains, and Optimization turns your program from defensive to resilient.
Reducing human error in cyber security starts with realistic employee training and layered controls. Security teams should combine security awareness training, phishing simulation, and clear security policies.
Add multi-factor authentication, strong password management, and role based access control. Regular risk assessment and behavioral analytics help spot risky behavior patterns early, improving error prevention and strengthening your overall cyber environment.
Human error continues to drive data breaches because attackers exploit distraction and trust through phishing email and social engineering testing. Many organizations still rely too heavily on annual employee training without reinforcing cyber hygiene daily.
Weak password protocols, shadow IT, and poor identity management also increase exposure. Stronger operational risk culture and continuous monitoring reduce cybersecurity incidents significantly over time.
Security teams should focus on building systems that expect employee error, not punish it. That means improving security infrastructure with network monitoring, email defense software, and Endpoint Detection and Response.
They should also guide security policies, vendor onboarding, and risk frameworks. Fast incident response and better security response times help contain cyber incidents before they escalate into serious cybersecurity breaches.
Multi-factor authentication and two-factor authentication protect user identities even when passwords fail. When combined with identity provider controls, conditional rules, and network permissions, they block most unauthorized access attempts.
This extra verification layer is one of the most reliable defenses against cyber threats. It significantly lowers risk management exposure across modern software and systems environments.
Cutting down on human error isn’t about finding perfect employees. It’s about building a better system around the people you have. You need to accept that mistakes happen, and then put the right culture, processes, and tools in place to catch them.
Start by changing your perspective. Don’t treat security as a list of rules for your team to follow. Treat it as a set of useful habits that help them work safely.
When your staff feels like part of the solution, when they can spot a threat and aren’t scared to report something odd, you’ve built something strong. That’s your human firewall. They stop being the weak link and become your first defense.
Ready to see where your human error risks are hiding? Let’s talk.