Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
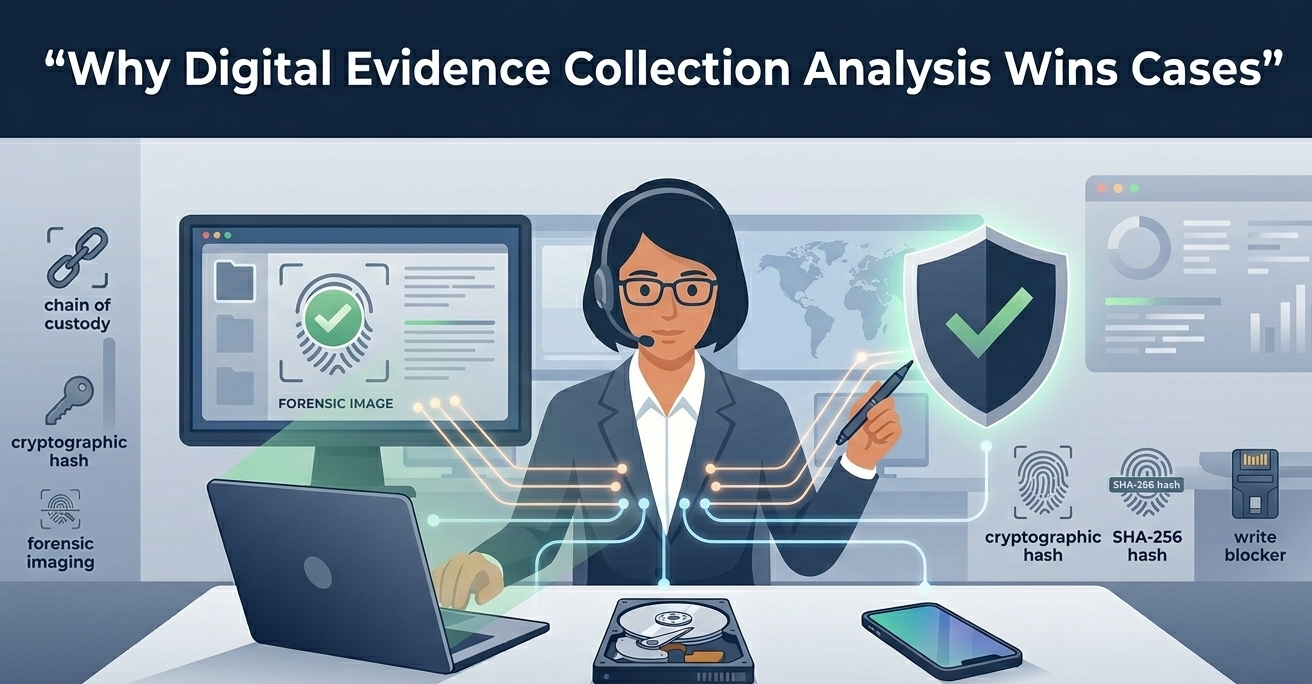
The reliability of digital evidence collection analysis is the most critical factor because it determines admissibility. Without a forensically sound process, the data you collect is just useless bits and bytes in the eyes of the court. We’ve seen strong cases falter over a broken chain of custody or a missing hash verification.
It all comes down to a simple, brutal truth: if you can’t prove the evidence is an exact, untampered copy of the original, it doesn’t exist. This isn’t about technology, it’s about trust. Keep reading to learn the framework that builds that trust from the ground up.
Digital evidence is fragile, more like a footprint in sand than a fingerprint on glass. A device reboot, a network sync, or even improper handling can erase the story it tells. The goal isn’t just to collect data, it’s to preserve its legal weight.
“Digital evidence is now a crucial part of nearly every investigation, changing how cases are handled and solved. Instead of focusing on individual devices, investigative teams are now looking at evidence from a broader perspective. As technology advances, so do the methods for collecting and analyzing digital evidence, with digital forensics constantly adapting to new challenges.” – Cellebrite
Courts demand proof of authenticity and integrity. That means every action, from the moment you approach a device, must be documented with the assumption a defense attorney will pick it apart later.
We approach this with a mindset of verification, ensuring every security incident investigation process stands up to scrutiny. It’s the difference between having evidence and having proof.
Foundational principles we follow:
Credits: Hansani Vihanga
You have to know what disappears first. Think of a computer’s live memory (RAM) like a whiteboard. When the power goes off, that whiteboard gets erased. The hard drive is more like a filing cabinet, it stays. The rule, formalized in guidelines like RFC 3227, is simple: collect the most transient data immediately.
This often means a live acquisition from a running system before you even think about pulling the plug. For persistent data on drives, the method is a forensic image, a bit-for-bit copy made with a write blocker to prevent any changes to the original. Getting this sequence wrong can mean losing the most critical clues.
| Data Type | Source Example | Priority | Key Action |
| Volatile | RAM, Network Connections | High | Live Acquisition |
| Persistent | HDD, SSD, USB Drives | Secondary | Forensic Imaging |
This is the paper trail that gives your evidence its voice. Every person who touches a device, every time it moves, every tool used on it must be logged. A gap here creates reasonable doubt. It starts at the scene: photograph the device in situ, note its make, model, and state.
“Effective Live forensics provides for the collection of digital evidence in an order of collection that is actually based on the life expectancy of the evidence in question. Simply put… the most important evidence to be gathered in digital evidence collection today and for the foreseeable future exists only in the form of the volatile data contained within the computers RAM.” – SANS Institute
Secure it in an anti-static bag, and for mobile devices, a Faraday bag to prevent remote wiping. Each transfer gets a signed and dated entry on the chain of custody form. The final, non-negotiable step is generating a cryptographic hash, like SHA-256, of the evidence. This hash is its unique fingerprint, used to verify it hasn’t changed a single bit.
Essential CoC Log Entries:
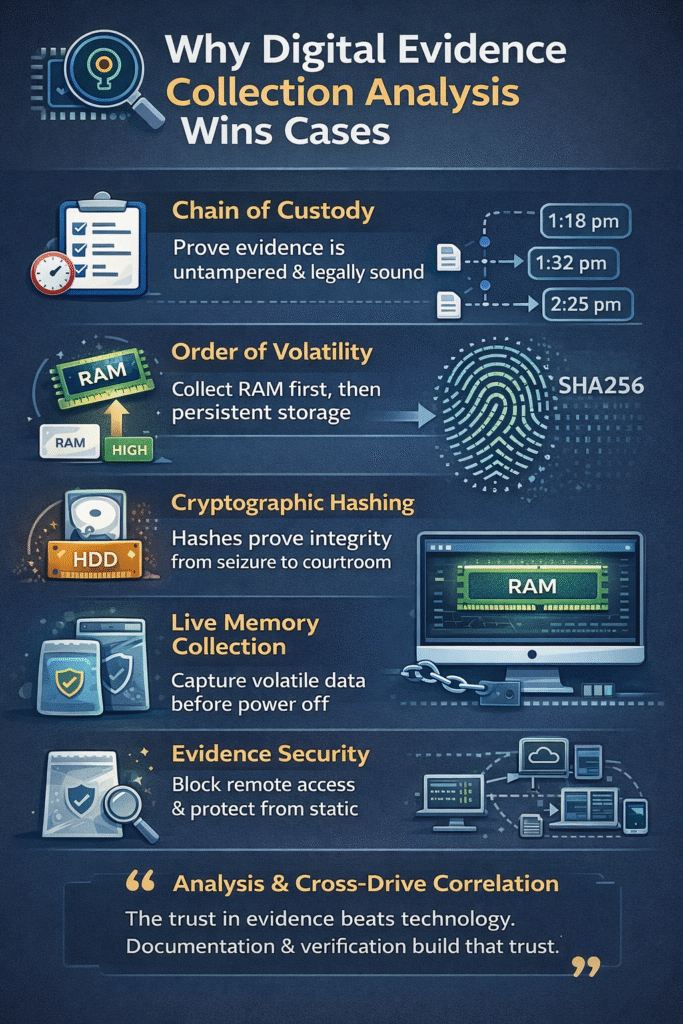
With a verified forensic image in secure storage, the real detective work begins. This is done on a copy, never the original. Tools are used to parse the filesystem, but the analyst’s skill is in knowing what to look for. File carving sifts through unallocated space to recover deleted files.
Timeline analysis uses metadata, Modified, Accessed, Created timestamps, to reconstruct a sequence of events. The analyst looks for anomalies: hidden partitions, files with mismatched extensions, or attempts at data obfuscation.
It’s a painstaking process of following analyst alert investigation steps to connect digital dots and form a coherent narrative of what happened.
Cross-drive analysis correlates data across multiple devices, finding links a suspect hoped would stay separate. This phase answers the “who, what, when, and how.” It transforms raw data into a story that can be presented clearly, often visualized through timelines or relationship maps.
The analyst’s report must be thorough, objective, and written for both technical and non-technical audiences, as it will guide legal strategy and potentially be entered into evidence.
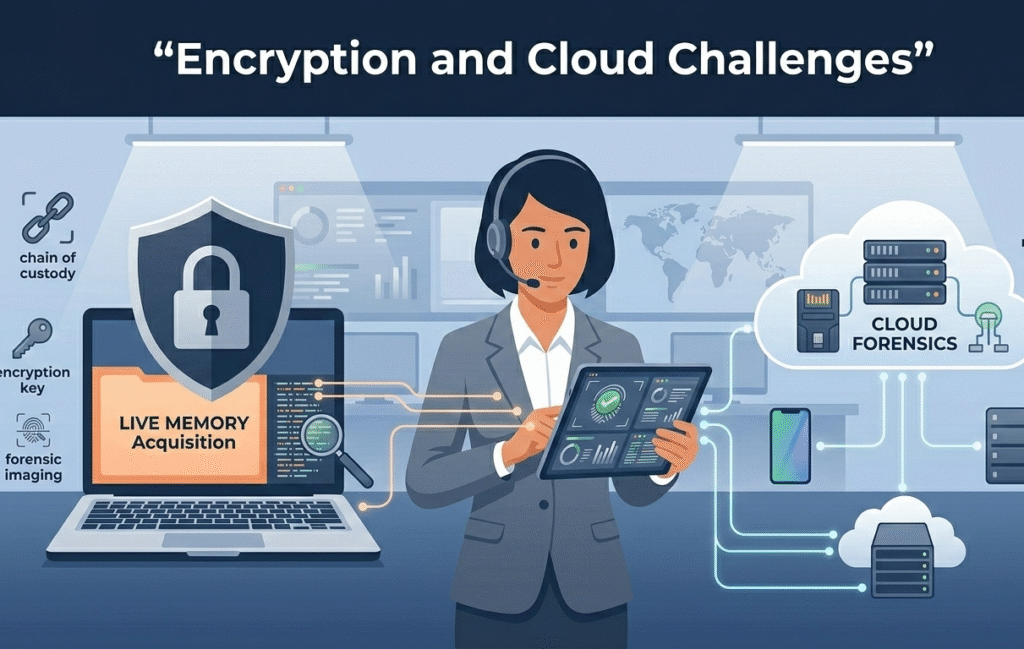
Today’s landscape is tougher. Full-disk encryption means a powered-off device can be a digital brick. Cloud storage places evidence on servers in other states or countries, outside immediate physical control. These aren’t dead ends, they’re shifts in strategy. For encryption, the emphasis moves to live acquisition while the device is on and unlocked.
For the cloud, the collection point becomes the service provider, accessed through legal process like subpoenas or warrants. This requires understanding provider policies and often, international legal cooperation.
The rise of anti-forensic techniques adds another layer. Suspects use wiping tools or timestomping software to deliberately mislead. This makes the initial triage and volatile data collection even more critical.
At MSSP Security, our incident response integrates these considerations from the first alert, following disciplined incident investigation analysis steps to ensure nothing is missed.
Digital evidence collection analysis becomes legally defensible when forensic investigators follow strict legal procedures and maintain a clear chain of custody. Law enforcement and legal teams expect evidence to be collected in a forensically sound manner, verified with cryptographic hash values, and stored securely.
Proper documentation, write protection, and validated digital forensics tools help ensure forensic evidence stands up during criminal investigations or civil disputes.
In digital forensic investigations, forensic analysts treat mobile devices, cloud storage, and social media platforms differently from traditional hard drive evidence.
Mobile device forensics focuses on mobile phone artifacts and mobile device evidence, while cloud forensics relies on legal authorization and provider records. Investigative teams prioritize volatile data, preserve audit trails, and align evidence processing with legal frameworks to protect forensic evidence integrity.
Live memory collection is critical during incident response when investigators suspect active cyber threats, encryption, or in-memory malware. Network forensics and computer forensics teams capture live memory before powering down digital devices because volatile electronic data disappears quickly.
This step supports threat detection, preserves digital activity, and strengthens digital evidence analysis, especially in fast-moving cyber crime and corporate fraud cases.
Write blockers and forensic imaging protect the original hard drive from accidental data tampering during digital evidence collection. Forensic imaging creates a verified forensic image of digital storage media using cryptographic hashing functions.
This write protection preserves metadata analysis accuracy and supports forensic science standards. Without these controls, forensic investigators risk breaking the chain of custody or weakening evidence presentation in court.
To build a defensible case, you need a solid foundation, and that starts with your tools. MSSP Security Consulting offers vendor-neutral guidance to cut through tool sprawl and hidden costs.
With over 15 years of experience and 48,000+ projects, we help with product selection, auditing, and stack optimization. We ensure your tools integrate well, improve visibility, and support your operational goals, making your security services as reliable as the evidence you collect.
Ready to strengthen your stack? Book a free consultation with our team.