Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Coordination transforms a chaotic cyber fight into a useful training exercise. It’s the shift from random attacks to a planned session where everyone learns. By coordinating red team blue team exercises together, you build a common understanding across your security team.
We know the exact moment it clicks, when a defender grasps how an attacker actually moves through the network, that’s when defenses genuinely improve. This guide explains how to stop playing “gotcha” and start building a unified, resilient security posture. Read on for the practical framework.

We learned the hard way that you can’t just unleash a red team. One poorly planned test for an MSSP client triggered a major production alert at 2 AM. Planning is everything. It starts with a scope everyone signs off on, whether it’s aligning teams through penetration testing coordination across cloud workloads or focusing tightly on an external portal.
That box becomes your rulebook, the formal Rules of Engagement. This document lists every authorized technique, every system that’s off-limits, and the emergency stop procedure. It’s a binding contract.
“Executive sponsorship ensures that the exercise is aligned with organizational priorities and not treated as a side project for the security team. Their buy-in is critical for converting identified weaknesses into funded remediation projects and long-term security improvements.” – CyCognito
Without a signed ROE, trust evaporates instantly. We always insist on this step; it’s what separates a professional security assessment from reckless behavior. You need clear objectives. Secure a controlled environment. Brief every participant.
Finally, pick your teams carefully. The red team needs thinkers who emulate real adversaries. The blue team needs the analysts who know the SIEM and EDR consoles cold. And you absolutely require a neutral white cell to manage the clock and inject realistic surprises.
Credits: Let Me Study
When the clock starts, the atmosphere changes. The red team might launch a phishing campaign based on real data they’ve gathered. Meanwhile, the blue team is glued to their dashboards, watching for the first sign of something wrong. This is where your planning gets tested.
The best exercises aren’t silent. We often build in structured pauses. After a critical move, like the red team gaining a foothold, we’ll huddle. The red team explains their method, and the blue team immediately checks their logs. Did they catch it? If not, why? This live feedback loop, this real-time purple teaming, is where understanding deepens fast.
| Exercise Phase | Red Team Focus | Blue Team Focus | Coordination Goal |
| Initial Access | Gaining a foothold via phishing or exploits. | Alert triage and initial containment. | Validate detection signatures and response playbooks. |
| Lateral Movement | Pivoting across the network, privilege escalation. | Log correlation, hunting for unusual east-west traffic. | Identify visibility gaps in internal network monitoring. |
| Exfiltration | Staging and stealing simulated data. | Forensic analysis, containing the breach. | Measure full incident response timeline and impact. |
The objective isn’t for the red team to simply “win.” It’s to apply enough pressure to expose real weaknesses. You might find the EDR missed a common living-off-the-land technique, or that the handoff between the SOC and network team during an incident is unclear. Those are the critical findings you’re after..
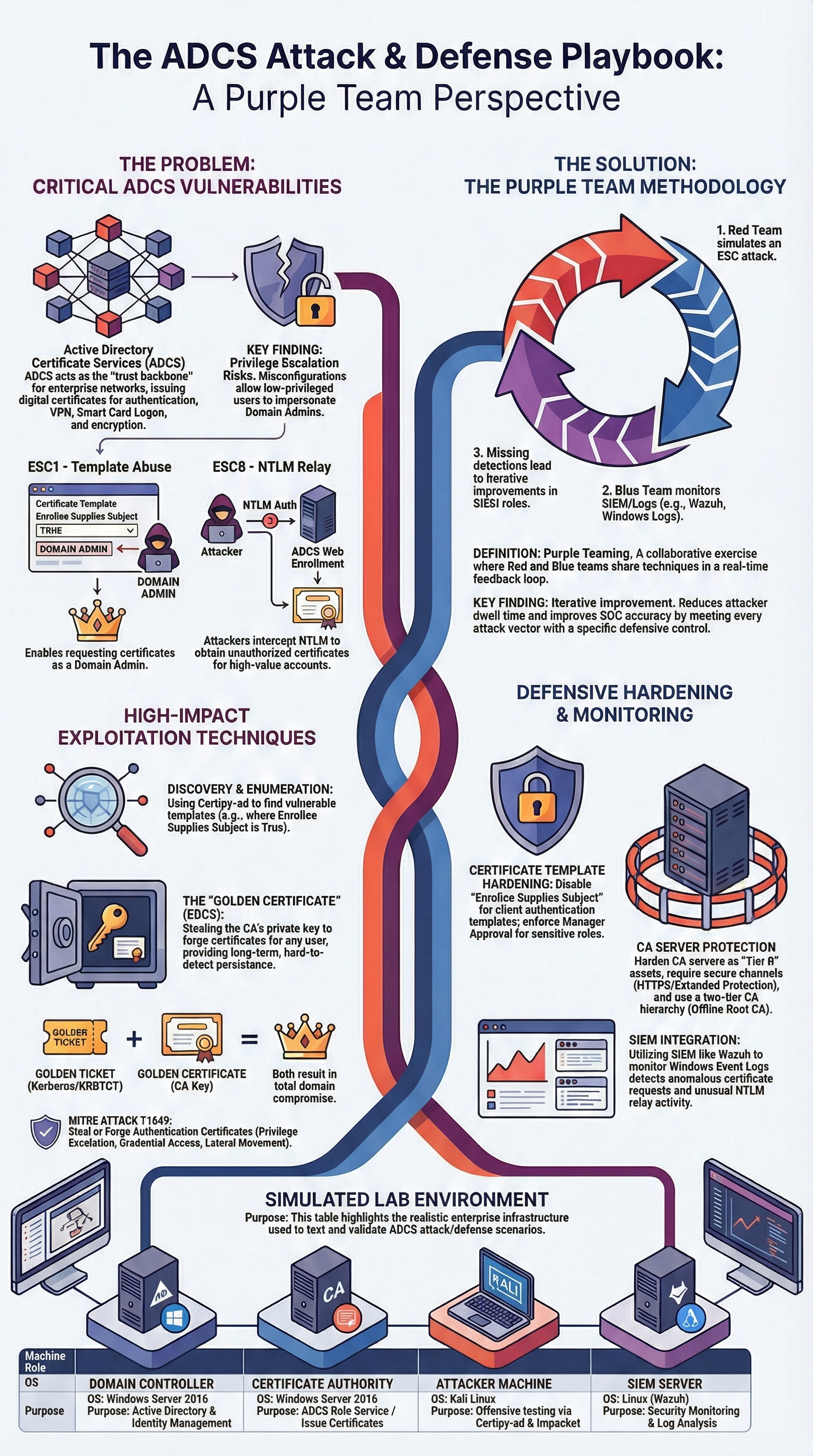
alt text: Coordinating red team blue team exercises shown as continuous security cycle with attack simulation and defense response
When an exercise ends, everyone’s tired, sometimes relieved, and that’s exactly when the real work begins. We’ve seen teams walk away thinking the job is done, only to realize months later that nothing actually improved. The After Action Review is where value is captured or quietly lost.
“The point is not just to succeed or fail in the attack, but to measure detection depth, validate defensive processes, and help both teams learn in real time. It measures not only whether you could be compromised, but whether you would notice it, and whether your team would know how to respond.” – KPMG International
In our debriefs, we rebuild the attack timeline from both sides, treating it as a hands-on process of interpreting penetration test results instead of just reviewing a static report. A blue team may believe they contained the breach early, until red team logs show attackers had already pivoted elsewhere.
Those moments are uncomfortable but incredibly useful. We focus on process and tooling, not blame, asking why visibility failed rather than who missed it.

We’ve watched MSSPs treat these events like checkboxes, then wonder why real incidents still feel chaotic. The real improvement starts when testing becomes part of the operational rhythm.
In our work, we push clients toward smaller, frequent validations. Much like training for endurance, you don’t build strength with one exhausting effort. You build it through repetition. Running focused simulations, validating new detection rules, and checking that patches didn’t introduce blind spots keeps teams ready without burning them out.
Over time, purple teaming stops being a scheduled workshop and becomes how security operates day to day.
Red insights shape stronger controls, blue realities shape smarter scenarios, and the feedback loop keeps getting tighter, and more effective, especially when teams consistently focus on prioritizing pen test findings remediation as part of each validation cycle instead of letting issues pile up between annual exercises.
Coordinating red team and blue team activities exposes how your incident response process works under real pressure. Instead of theory, security teams practice detecting threats, escalating alerts, and coordinating fixes.
These team engagements reveal delays, confusion, and missed signals that normal drills miss. Over time, repeated team exercise sessions strengthen incident detection, communication flow, and decision-making during real-world attacks.
Conventional pen testing focuses mainly on finding technical weaknesses. Coordinated red team blue team exercises go further by testing how a cybersecurity team responds in real time.
They measure alert handling, investigation speed, and teamwork across departments. This approach connects the objective of pen testing with operational readiness, not just vulnerability discovery.
Purple teams help bridge the gap between red team attackers and blue team defenders by sharing techniques and lessons in real time. White teams act as neutral facilitators, keeping the team exercise on track and aligned with goals. Together, they ensure learning stays central, not competition, creating stronger security teams overall.
Effective team assessments involve more than just technical testers. A full team of cybersecurity professionals should include SOC analysts, incident response leads, infrastructure engineers, and sometimes management teams. This ensures detection, escalation, and decision-making are tested across real workflows, not just isolated tools.
Running a red team exercise isn’t just a simulation. It’s a discipline that builds an organization resilient to real attacks. The real value lies in the shared understanding created through planning, the live collaboration during the event, and the honest debrief that follows. This process turns separate teams into a unified, adaptive defense unit.
Ready to build this capability? Our consulting helps MSSPs streamline operations and select the right tools. See how a structured approach can work for your organization.