Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

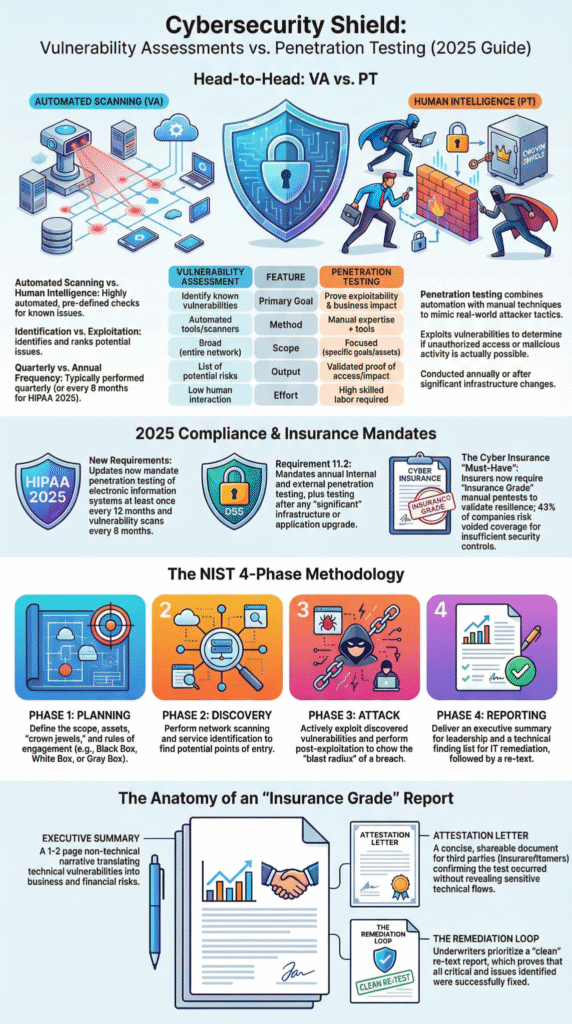
Your last penetration test report likely won’t pass an audit. Most standards, like PCI DSS or HIPAA, require documented proof that your key security controls can stop a real attack, not just a list of vulnerabilities. Many technically sound tests fail because they don’t explicitly map their findings to a specific regulatory control.
This guide shows how to structure your 2026 testing program to provide that undeniable evidence, satisfying both security teams and auditors. Read on to compliance penetration testing requirements that save audits

We’ve been in that exact spot with an auditor. Our team had run a comprehensive pen test, finding critical issues in a legacy system. We were sure we’d covered everything.
The auditor just pointed at our report. “Where’s the validation for CDE segmentation?” he asked. The work was technically thorough, but it failed the compliance check. That lesson was expensive.
“PCI DSS requires penetration testing to be conducted at least annually or after any significant changes in infrastructure or application. … When businesses use segmentation controls to isolate the Cardholder Data Environment (CDE) from other networks, PCI DSS requires penetration testing or segmentation testing to validate their effectiveness.” – AMATAS
This is the gap we help MSSPs bridge. Compliant testing isn’t just vulnerability hunting. It’s about running properly penetration testing coordination across regulated environments so teams target the right assets, follow the required methods, and document fixes auditors actually accept.
Our service audits the testing methodologies of security vendors you’re evaluating. We verify their process maps directly to the control evidence your clients’ auditors demand, transforming a technical report into a defensible audit artifact.
Credits: Chandra Bhanu Sonu
Running a basic scan isn’t enough. Each compliance framework demands a specific, documented approach.
PCI DSS 4.0 is explicit. Requirement 11.4 isn’t optional; it mandates three tests on the Cardholder Data Environment (CDE):
| Compliance Framework | What Must Be Tested | Required Frequency | Key Audit Expectation |
| PCI DSS 4.0 | Cardholder Data Environment (CDE), segmentation controls | Annually and after major changes | Proof that CDE is isolated and attack paths are blocked |
| HIPAA Security Rule | Systems handling ePHI | Periodic (moving toward annual by 2026) | Risk-based testing with documented methodology |
| SOC 2 | Controls tied to security and confidentiality | Risk-driven, typically annual | Evidence mapping findings to control objectives |
| ISO 27001 | Technical vulnerability management scope | Ongoing with formal assessments | Demonstrated effectiveness of security controls |
We’ve reviewed tests that included unrelated servers, which auditors immediately dismissed as out-of-scope noise. Their focus is solely on the walls protecting payment data.
HIPAA’s “periodic technical evaluations” are famously vague. The 2025 updates want annual testing as the 2026 standard. Right now, if your “periodic” schedule isn’t backed by a formal risk analysis, it’s a major liability. The auditor needs your logical defense, not just a checkbox.
These frameworks work differently. They don’t have a simple requirement labeled “penetration test.” Instead, they set broad objectives through SOC 2’s Common Criteria or ISO 27001’s Annex A controls. Your job is to prove you meet them. A well-run penetration test provides that proof.
“The AICPA, which governs SOC 2, explicitly lists penetration testing as a prime example of a ‘separate evaluation’ used to determine if security controls are functioning under criterion CC4. … A test performed outside this window [the audit review period] will not be considered valid evidence by your auditor.” – CYBRI
For SOC 2, it directly supports the Security and Confidentiality trust principles. It demonstrates to an auditor that you didn’t just install a firewall; you actively tried to break through it. When we evaluate a security product for an MSSP, we structure tests to map findings directly to controls like CC7.1 for monitoring.
We don’t just deliver a list of CVSS scores. We help teams focus on clearly interpreting penetration test results, mapping each finding directly to audit controls like CC7.1 so technical data becomes evidence auditors actually accept.

This is the critical part. The final report isn’t for your security engineers. It’s for a compliance officer, an external auditor, or legal counsel. It must tell a clear story: what you protected, how you tested it, what you found, and how you fixed it.
Start with an executive summary that explains risk in business language. A CISO needs to understand that an XSS flaw in the customer portal could trigger a GDPR breach notification. Detailed findings require proof, screenshots, system responses, packet captures, to show it was a real attack simulation, not an automated scan.
The remediation section is most important. It must show clear prioritizing remediation based on risk, listing each critical finding, the applied fix, and closure date. Including retest evidence closes the loop completely and demonstrates documented due care.
Compliance penetration testing requirements go far deeper than basic Vulnerability Scanning or a simple vulnerability scan. They test real attack vectors against web applications, network security, segmentation controls, and user access.
Ethical hackers attempt credential theft, social engineering, and exploitation of internal vulnerabilities to measure real data security. The goal is proving security controls truly protect customer data and sensitive systems under realistic cyber attack conditions.
Penetration tests provide evidence that security posture meets regulatory compliance expectations across compliance frameworks like SOC 2, ISO 27001, and Payment Card Industry Data Security Standard.
They validate risk management, network segmentation, incident response readiness, and protection of payment card data. Auditors use penetration test reports to confirm security assessments go beyond policies and into real-world defense.
Most regulatory bodies expect penetration tests annually and after major system changes, cloud computing services migrations, or new third-party connections. Risk analysis may require more frequent testing for critical systems handling electronic protected health information or payment card information.
Some oversight expectations are influenced by agencies such as the Department of Health and Human Services, emphasizing continuous risk assessment and strong incident response planning.
A compliant penetration test report documents scope, Rules of Engagement, tested attack vectors, CVSS scores, and proof of exploitation. It should clearly link findings to security controls, network segmentation, and risk management actions.
Auditors look for remediation timelines, retesting results, and business impact explanations. Strong reports transform penetration testing into formal security audits evidence rather than raw technical output for the security team.
Start planning now. Define your test scope around the specific compliance framework, target the CDE for PCI, all ePHI systems for HIPAA. Choose testers with credentials like OSCP that auditors recognize. Build a report for both your tech team and your compliance officers.
The 2026 deadlines are approaching. Proactive, compliant testing is your insurance policy. It ensures you walk into an audit with a bound report that answers every question, instead of scrambling to justify a generic scan.
Schedule your free consultation to get started.