Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Forget vendors that just sell you a pass-fail report. You need choosing penetration testing vendor in Fullerton who thinks like an attacker, finds the cracks in your defenses, and sticks around to help seal them up. Demand specifics on their approach, how they’d target your business specifically.
If they can’t explain their process without jargon, walk away. The outcome should be a genuinely more secure network, not just a document for an auditor. To learn how to spot the real experts from the paper-pushers, keep reading to lock down your selection process.

There’s a tangible benefit to working with a local partner that most sales pitches gloss over. Think about physical security. Could a team from another state realistically test the Wi-Fi in your warehouse near Brea, or try to get past the front desk at your Fullerton office? Often, the travel logistics and cost mean those tests get cut, leaving a major blind spot.
We’ve seen it firsthand. A local team can be on-site tomorrow. They know the quirks of Orange County’s infrastructure and the compliance overlaps that trip up businesses here. They can sit across from your IT staff in a debrief, not just on a video call.
When something goes wrong, geography matters. “Same-day” from a vendor down the street is a real response. “Next-day” from out of state feels like a lifetime when you’re facing a potential breach. At our firm, we’re embedded here because minutes count, not SLA timeframes. The practical advantages are straightforward:
It’s a survival consideration, not just a convenience. We’ve worked with MSSPs who’ve lost clients after a major attack. Your vendor’s location isn’t just a detail; it’s part of your defense.
Credits: CISO Global
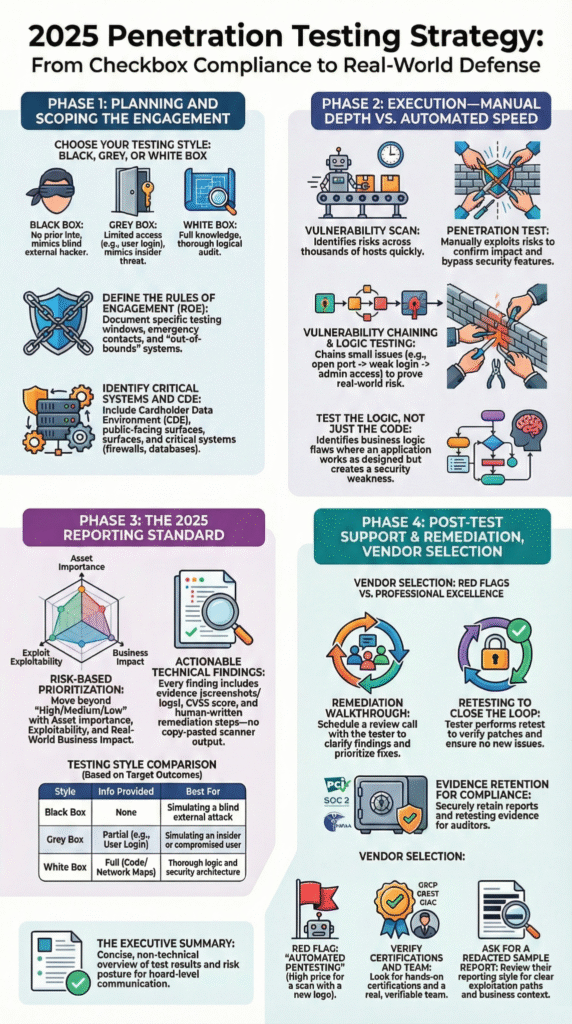
Don’t just check for company logos. Look at the individual tester’s certifications. Anyone can run an automated scan, but a credentialed ethical hacker knows how to think. The OSCP (Offensive Security Certified Professional) is the essential baseline, it’s a grueling, hands-on exam that proves they can manually exploit vulnerabilities, not just click buttons.
“How to Choose a Provider: Focus on tester expertise and manual rigor over buzzwords or scanning tools; demand clear scope, senior consultants, transparent pricing avoid per asset quotes; ensure reports include prioritized fixes and context.” – DeepStrike Blog
We advise MSSPs to look further for OSEP or GXPN credentials. These signal a tester who can chain attacks together and bypass modern defenses, simulating a real threat. CREST accreditation for the firm itself is another strong signal. Be wary of vendors whose teams are heavy on multiple-choice certs like the CEH, without the hands-on counterparts to back them up.
The math is simple. With the average data breach costing millions, paying a bit more for certified, proven skill isn’t an expense, it’s one of the clearest returns on investment you can make for your clients’ security.
You have a choice. On one hand, there are local Fullerton and Orange County boutique firms. They offer high-touch service, deep scoping calls, and a project manager who knows your name. Their strength is customization and physical presence.
On the other, national Penetration-Testing-as-a-Service (PTaaS) platforms offer scale, slick portals, and often subscription models. Their strength is continuous testing and broad resource pools.
The hybrid approach is where many smart businesses in Fullerton land. You might use a local vendor for your annual comprehensive assessment, including physical and social engineering elements, while maintaining strong penetration testing coordination across ongoing security efforts.
This balances deep, manual investigation with ongoing vigilance. The key is to never let the PTaaS platform replace a true manual penetration test. They are complementary tools, not substitutes.
It helps to see the trade-offs laid out plainly. This isn’t about which column is better, but which aligns with your specific needs for a penetration testing vendor in Fullerton.
| Consideration | Local Fullerton / OC Boutique Firm | National PTaaS Provider |
| Testing Depth | Manual-heavy, tailored exploitation chains. | Often blends automated scans with targeted manual checks. |
| On-Site Capability | Core service for physical/wireless tests. | Limited, usually incurs high travel fees. |
| Emergency Response | Potential for same-day local engagement. | Typically follows a 24-48 hour SLA. |
| Cost Structure | Project-based, often 10,000−10,000 – 10,000−30,000+ for a full scope. | Subscription-based, monthly or annual. |
| Primary Advantage | Personalized service, deep local knowledge, physical testing. | Scalability, continuous testing, extensive tooling. |
Your own infrastructure dictates the right mix. A company with a single cloud application might lean PTaaS. A Fullerton manufacturing plant with an on-premise network, a warehouse, and an office needs that local touch.
Here are the red flags we tell every MSSP to watch for. The community calls them “checkbox pentests.” That’s when a vendor bills for a manual test but delivers a report spit out by an automated scanner like Nessus. The findings are generic, missing the complex, business-specific flaws a real attacker would find.
Another major warning is a lack of real remediation help. A line that says “SQL Injection: Critical” is useless if your developers don’t know how to fix it. We’ve seen vendors vanish after sending the PDF, offering no retesting to confirm patches worked.
You’re not buying a document. You’re buying a path to better security. If the vendor doesn’t guide you down it, the budget is wasted.
Your RFP is your control. A vague one gets you vague, expensive proposals. Start by defining scope precisely. List every in-scope asset: your cloud instances, on-prem servers, mobile apps, and API endpoints. Specify the testing method, black-box, gray-box, or white-box, as each reveals different things.
Then, demand a sample report. Skip the marketing slides and focus on interpreting penetration test results that clearly show proof of exploitation, business impact, and practical fixes.
Does it walk through vulnerabilities step by step? Does it rank risks in a way your team can act on? This sample is the best preview you’ll get of the real value behind the engagement.

The test is just the diagnosis. The cure is what happens next. This is where vendors and partners split. A true partner provides more than a PDF. They should hold a remediation workshop to walk your IT and dev teams through the critical issues. They need to answer technical questions and provide a clear fix-first roadmap.
“The penetration testing team should offer an option to rerun the test after you remediate the findings. The last thing you want is to pay for a penetration test, take time fixing items, and then be hacked later on because you did not validate your fix actions.” – CISO Global
Crucially, they must include retesting and a clear process for prioritizing pen test findings remediation so teams fix the highest-risk issues first. Once critical holes are patched, validation confirms the improvements worked. This closes the loop and turns testing into a measurable security upgrade.
Penetration testing simulates real-world attacks like SQL injection, XSS flaws, social engineering, and WiFi cracking to expose hidden security vulnerabilities. Skilled ethical hacking reveals how attackers move through IT systems, web servers, public-facing websites, and network infrastructure.
This hands-on approach improves threat detection, strengthens IT security, and reduces the risk of data breaches and credential leaks.
A quality vendor delivers fast threat response, clear communication support, and forensic expertise when cyber attacks occur. This includes analyzing log trails, containing cloud breaches, restoring data backup, and guiding disaster recovery.
Strong incident response protects business continuity while minimizing downtime, data leaks, and cyber extortion risks across cloud computing and on-premise environments.
IoT & embedded device testing identifies device-level access risks, firmware flaws, and weak authentication that attackers exploit.
Vendors use embedded system reverse engineering and Linux exploitation to uncover threats in smart devices connected to network infrastructure. Without this testing, cyber threats can bypass traditional defenses and lead to large-scale data breaches.
External testing targets public-facing websites, cloud services, and exposed web servers to simulate outside attackers. Internal testing evaluates employee access, identity access management, and lateral movement within IT systems.
Together, they reveal gaps in security measures, improve threat hunting, and provide realistic risk assessments that automated tools often miss.
Your final choice in Fullerton isn’t about technical specs. It’s about trust. Will the vendor tell you the hard truth about a critical flaw in your main application? More importantly, will they help you fix it? Look past the sales talk. Judge their real technical skill, their dedication to remediation, and their roots in your community. Your security hinges on this partnership.
Start with a partner who prioritizes the fix. Talk to Our MSSP Consulting Experts