Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Real data protection begins with data discovery, classification, and DLP working together, not with a…

Data Loss Prevention (DLP) today isn’t just about checking boxes for compliance. It’s about stopping…
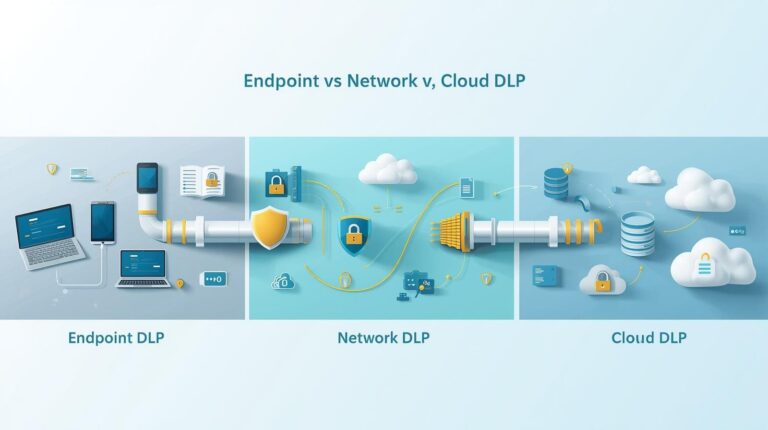
Endpoint DLP, network DLP, cloud DLP aren’t just add-ons anymore, they form the core defense…

Data protection compliance means making sure organizations handle personal data according to the laws that…