Incident response playbooks only work when they’re tested under pressure. We’ve seen teams with well-documented plans struggle during real incidents simply because those plans were never validated.
Testing incident response playbooks ensures your team can act quickly, consistently, and effectively when it matters most. It turns theory into action and uncovers hidden gaps before attackers do. If you want a response strategy that actually performs in real scenarios, keep reading.
Key Insights: Testing Incident Response Playbooks Effectively
Testing incident response playbooks is not just a technical exercise, it’s an operational necessity. Organizations that regularly test their playbooks respond faster, reduce errors, and improve coordination.
- Playbook testing identifies gaps before real incidents occur
- Simulations improve team readiness and confidence
- Metrics from tests help refine response strategies
Why Testing Incident Response Playbooks Matters

We’ve observed that untested playbooks often fail at critical moments. Teams may know their roles in theory but struggle with execution under stress.
Testing provides:
- Real-world validation of procedures
- Improved communication across teams
- Faster decision-making during incidents
- Reduced downtime and business impact
According to Wikipedia,
“An incident response plan is a set of instructions designed to help organizations detect, respond to, and recover from network security incidents.” – Wikipedia
Without testing, those instructions remain unproven assumptions.
Common Methods for Testing Playbooks
Different testing methods serve different maturity levels, often utilizing diverse security response playbook examples. We typically recommend combining multiple approaches.
- Tabletop Exercises: Discussion-based scenarios for strategic alignment
- Simulation Drills: Realistic attack scenarios with active response
- Red Team Exercises: Adversarial testing to uncover weaknesses
- Automated Testing: Using SOAR tools for repeatable validation
Each method provides unique insights. For example, tabletop exercises reveal communication gaps, while simulations expose technical weaknesses.
Sample Testing Framework
Credits: Open Security Summit
A structured framework ensures consistency, specifically when validating ransomware response playbook steps to ensure measurable outcomes.
| Phase | Objective | Example Activity |
| Preparation | Define scope and scenarios | Select phishing or ransomware case |
| Execution | Run the test scenario | Simulate attack and response |
| Observation | Capture performance data | Track response time and errors |
| Analysis | Identify gaps and improvements | Review missed steps |
| Optimization | Update playbooks and processes | Refine escalation procedures |
This cycle helps organizations continuously improve their response capabilities.
Metrics to Evaluate Playbook Effectiveness
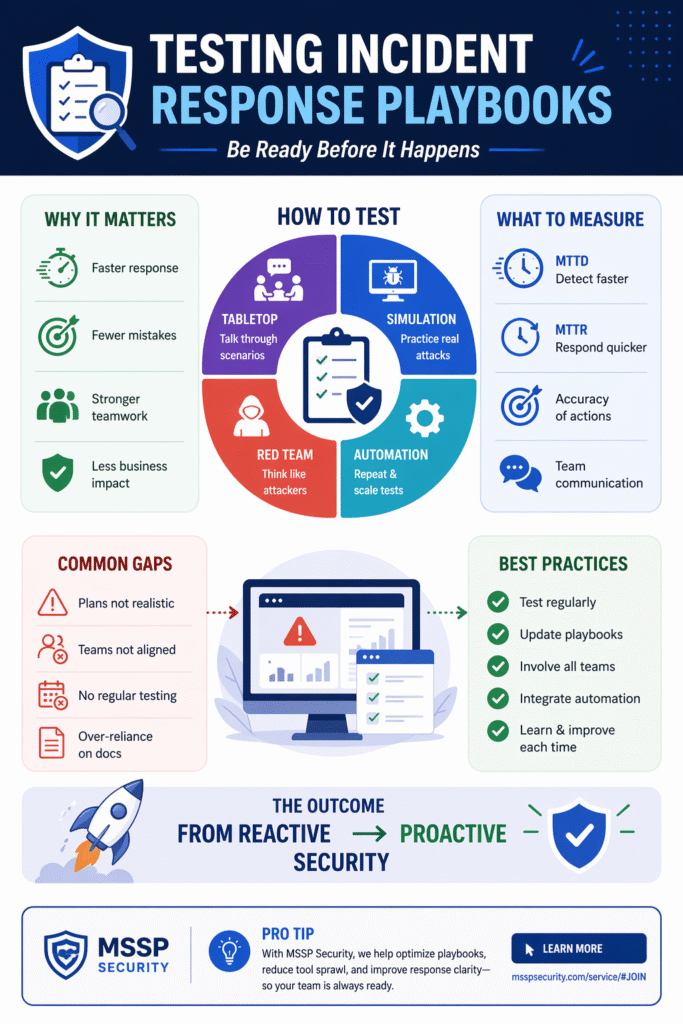
Testing without measurement is guesswork. We focus on metrics that reflect real performance.
- Mean Time to Detect (MTTD)
- Mean Time to Respond (MTTR)
- Accuracy of response steps
- Communication efficiency
- Number of escalations required
A study from research literature highlights:
“Regular incident response exercises significantly improve detection and containment capabilities in organizations.” – ResearchGate
Tracking these metrics allows teams to move from reactive to proactive security.
Challenges in Testing Incident Response Playbooks
Even mature teams face challenges when testing playbooks.
- Limited resources or time constraints
- Lack of realistic scenarios
- Resistance from stakeholders
- Over-reliance on documentation instead of execution
We’ve found that organizations often underestimate the importance of realism when practicing with a data breach response playbook template; without realistic testing, results can be misleading.
Working with experienced partners like MSSP Security helps align testing with real-world threat landscapes while keeping processes practical.
Best Practices for Continuous Improvement
Testing should never be a one-time activity. Strong programs evolve continuously.
- Schedule regular testing cycles
- Update playbooks based on new threats
- Involve cross-functional teams
- Integrate automation where possible
- Document lessons learned after every test
We emphasize iterative improvement, each test should make the next response stronger and faster.
FAQ
How often should incident response playbooks be tested?
Playbooks should be tested at least quarterly, but high-risk environments may require monthly simulations. Frequency depends on threat exposure, regulatory requirements, and organizational maturity. Regular testing ensures playbooks stay aligned with evolving threats and internal changes.
What is the difference between tabletop and simulation testing?
Tabletop exercises are discussion-based and focus on decision-making and communication, while simulations involve active execution of response steps in realistic scenarios. Both are valuable, but simulations provide deeper technical validation.
Who should be involved in playbook testing?
Testing should include security teams, IT operations, legal, communications, and management. Incident response is not just technical, it requires coordination across the organization to be effective during real events.
Can small teams effectively test incident response playbooks?
Yes, even small teams can conduct effective testing using lightweight tabletop exercises and targeted simulations. The key is consistency and focusing on realistic scenarios rather than complex setups.
Strengthening Security Through Tested Incident Response Playbooks
Testing incident response playbooks transforms them from static documents into reliable operational tools. Regular testing improves speed, coordination, and confidence during real incidents. Organizations investing in continuous validation are better prepared for evolving threats.
If you are looking to refine your strategy, we offer expert consulting to streamline operations and boost service quality. Our vendor-neutral guidance ensures you build a resilient tech stack aligned with your goals. Strengthen your response with MSSP Security.
References
- https://en.wikipedia.org/wiki/Incident_response
- https://www.researchgate.net/
