An alert flashes. Your gut says it’s real. The real work, analyzing a security incident, starts now. It’s not about checking boxes from a NIST guide. It’s a messy, urgent hunt for truth in logs and memory dumps. You’re piecing together a story an attacker tried to erase, moving from confusion to clarity, from impact to root cause.
This process separates a contained event from a recurring nightmare. The goal isn’t just to clean up. It’s to learn, adapt, and build something stronger. Keep reading to transform your next incident from a firefight into your most valuable teacher and know steps analyze security incident.
What Matters Most in Incident Analysis
- Validate and scope the breach immediately to focus resources and prevent wasted effort on false alarms.
- Preserve volatile evidence and build a forensic timeline to understand the attacker’s exact path and methods.
- Conduct a blunt root cause analysis to fix systemic flaws, not just symptoms, stopping the same attack from happening again.
Reddit’s EDR Triage Realities
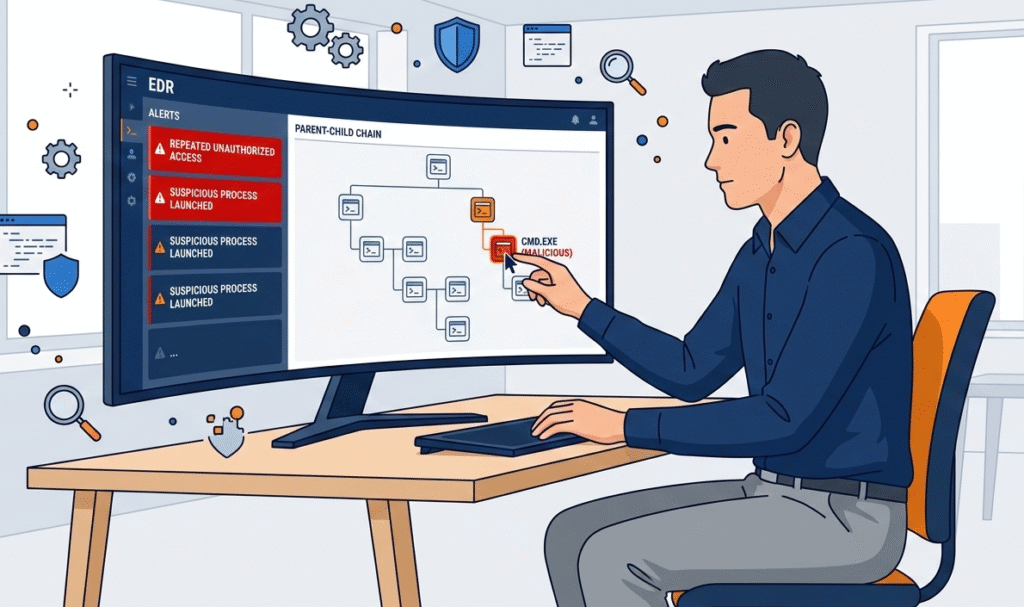
In most MSSP environments we audit, the first seconds after a security alert matter more than teams admit. An Endpoint Detection and Response console flags a suspicious process, and the disciplined analysts immediately trace the parent-child chain.
We’ve watched strong Incident Response Teams pivot from EDR into Security Information and Event Management views, correlating system logs before making any call. That early incident investigation step often decides whether a security incident becomes noise or a real escalation.
What separates mature security operations centers is speed with structure. Our reviews repeatedly show the same winning pattern:
- Correlate EDR telemetry with SIEM systems and identity events
- Validate indicators of compromise against threat intelligence feeds
- Confirm affected assets and sensitive data exposure
- Prioritize based on business risk, not raw tool scoring
Get this wrong, and incident response effort spirals fast.
YouTube Timelines vs. Hype
Credits: Mike Chapple
Videos love a clean story. Real Cybersecurity Incidents rarely cooperate. When we support MSSPs during Incident Analysis, the data is messy, system logs, firewall telemetry, cloud audit trails, and identity noise all competing for attention. Good analysts impose order. They hunt for the earliest security event, then build forward through the attacker’s path.
“Identification should answer the five W’s of a security incident, such as: Who discovered the incident and how? What is the scope of the incident? When did the event happen? Where did the incident occur, and have any other areas of operation been impacted? Why did the incident occur?” – Pax8
From what we’ve seen in the field, narrative building is where many teams either shine or stall. Strong investigators typically:
- Reconstruct the timeline from initial access to lateral movement
- Map behaviors to MITRE ATT&CK for attacker intent
- Cross-check network traffic and authentication anomalies
- Document indicators of potential compromise clearly
This forensic storyline becomes the backbone of the broader security incident investigation process.
The Critical Step Everyone Rushes
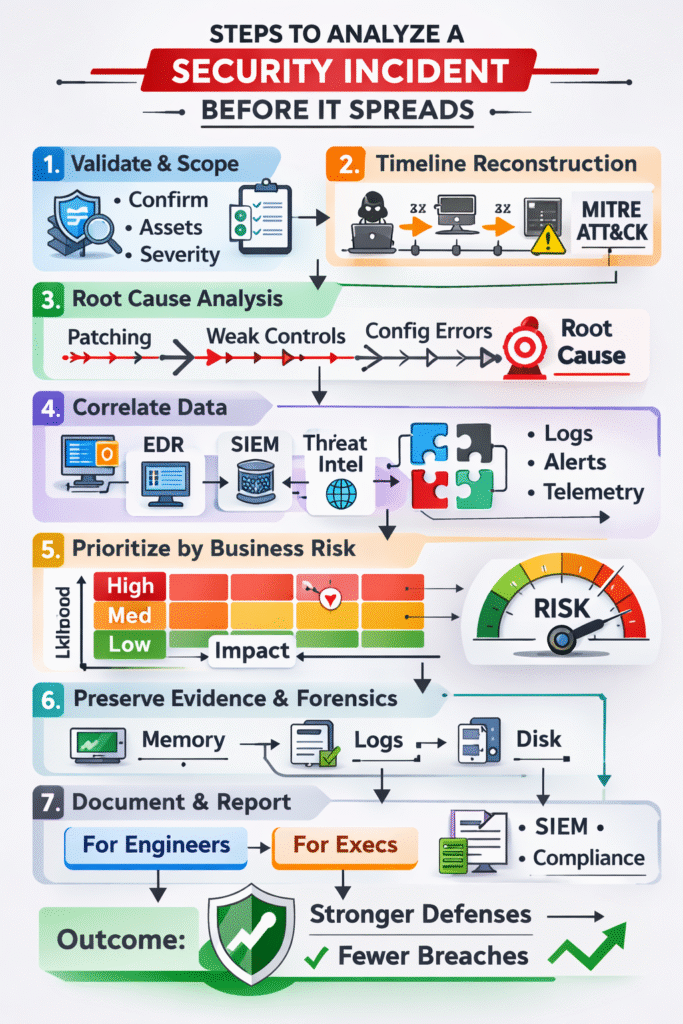
Containment feels satisfying, we’ve seen teams isolate hosts, reset credentials, and declare victory within minutes. But during our Managed Security Service Provider assessments, the repeat breaches usually trace back to weak root cause analysis. Fixing the trigger is easy; fixing the system that allowed the cyber attack is harder.
“Detection identifies potential security incidents while analysis determines their validity and severity. … Analysis validation separates true security incidents from false positives and benign anomalies. Security analysts evaluate indicators of compromise (IOCs), assess behavioral patterns, and determine threat actor intent.” – VMRay
Effective incident response frameworks force uncomfortable questions. In our consulting work, we push MSSPs to dig deeper using methods like fault tree analysis or even a simple fishbone diagram. Common systemic gaps we uncover include:
- Delayed vulnerability patching processes
- Weak identity controls enabling account compromise
- Over-privileged service accounts
- Gaps in phishing training and user awareness
Real resilience comes from honest lessons learned, not fast closure metrics. Too many teams treat documentation as a box to check rather than refining analyst alert investigation steps for future detection.
Building a Case, Not Just a Report
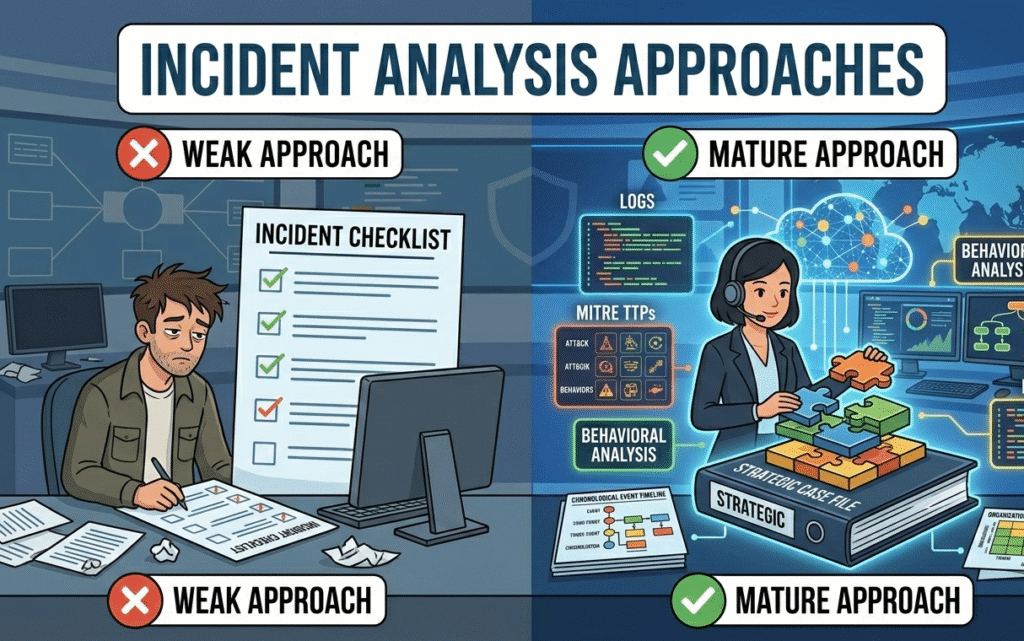
Too many incident response teams still treat documentation like a box to check. In our work with MSSPs, we’ve seen how that habit quietly weakens long-term cyber security outcomes. Mature teams treat incident documentation as part of the incident response process, not an afterthought.
When we audit incident response capabilities, the pattern is clear: high performers write for engineers and executives at the same time.
A strong report should feed detection improvements back into SIEM systems and intrusion detection systems while also supporting Data Privacy Regulations and enterprise risk management reviews. That dual purpose is what strengthens the Cyber Security Incident Response Plan over time.
The teams that improve fastest translate Incident Analysis into business impact. When personal data or financial data is involved, clear context, not raw logs, drives smarter incident management and better long-term defense.
| Analysis Phase | Primary Question | Key Output |
| Validation & Scoping | Is this real, and what’s touched? | Confirmed incident, asset list, severity level. |
| Timeline Reconstruction | How did the attacker move? | Chronological event map, MITRE ATT&CK TTPs. |
| Root Cause Analysis | Why were they able to do this? | Technical trigger and systemic security gap. |
FAQ
How do steps analyze security incident improve incident response outcomes?
Following clear steps analyze security incident helps the Incident Response Team act faster and with less confusion. A structured incident response process improves threat detection, speeds up incident classification, and reduces wasted effort.
Over time, better Incident Analysis also strengthens risk assessment, supports information security goals, and helps security operations centers handle complex Cybersecurity Incidents more confidently.
What evidence should teams collect during a security incident investigation?
During incident investigation, teams should gather system logs, network activity, and indicators of compromise tied to the security incident. Good detection and reporting also includes Behavioral Analysis results and suspicious IP address activity.
This evidence supports accurate incident classification, improves response protocols, and ensures incident documentation stands up to regulatory authorities if a data breach involves sensitive data.
How can organizations reduce mean time to identify breaches?
To lower mean time to identify breaches, security teams must tune SIEM systems, intrusion detection systems, and endpoint security telemetry together. Strong threat intelligence feeds and Machine Learning models improve early threat detection.
Regular Log Analysis and Network Traffic Analysis Tools also help security officers spot indicators of potential compromise faster across complex digital systems.
Why is root cause analysis critical after Cybersecurity Incidents?
Root cause analysis prevents repeat security breaches. Instead of only containing malware attacks or account compromise, teams examine why controls failed. Techniques like fault tree analysis or a fishbone diagram reveal gaps in the incident response framework.
These lessons learned improve preventive measures, strengthen the cybersecurity program, and reduce the likelihood of future cyber attackers succeeding.
From Lessons to Lasting Defense
An incident analysis that ends in a drawer is a miss. Real progress comes from institutionalizing what you learned. We help MSSPs turn attacker TTPs into tighter detection rules, stronger IAM controls, and smarter phishing defenses. The goal is simple: fewer repeat incidents and faster response next time.
If you’re ready to streamline tools and strengthen outcomes, join our MSSP consulting program to get vendor-neutral guidance backed by 15+ years and 48K+ projects.
References
- https://www.pax8.com/blog/cybersecurity-incident-response-guide/
- https://www.vmray.com/incident-response-steps/
