A good MSSP alert handling process cuts through the noise. It uses a standard workflow to separate real threats from false alarms, so your team isn’t swamped by thousands of meaningless alerts.
The real work happens after you invert that ratio. Automation and smart triage filter out the irrelevant, letting your experts handle actual incidents. This review explains how modern MSSPs build this critical workflow. See how to turn alert chaos into a clean, operational defense.
Operational Highlights
- A tiered triage model is essential for efficiently scaling analyst resources and managing alert volume.
- Strategic automation and enrichment are non-negotiable for reducing mean time to resolution (MTTR).
- Continuous process review and tuning are the only defenses against crippling alert fatigue.
What Defines an Effective MSSP Alert Handling Process?
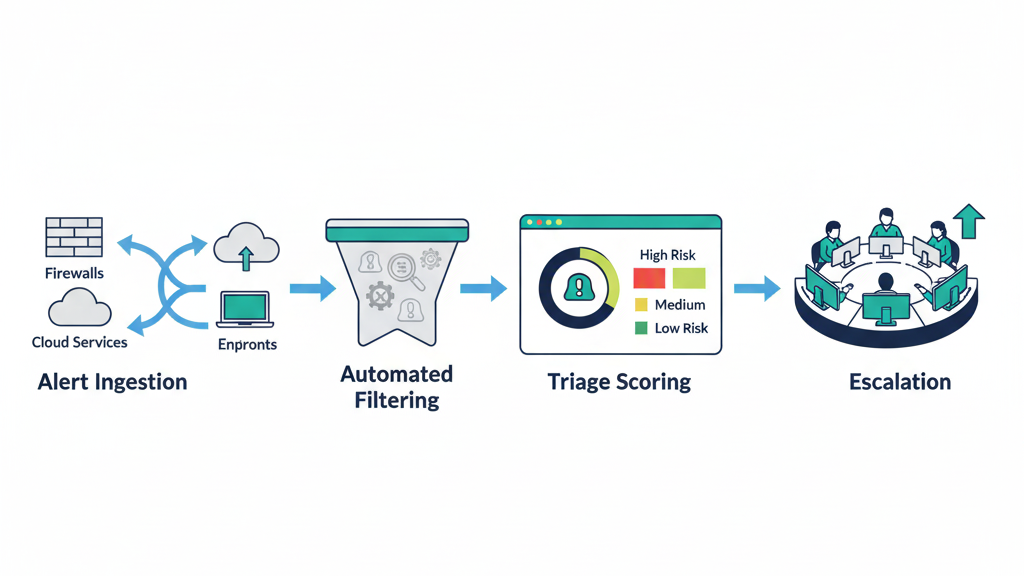
An effective alert handling process is a structured assembly line. At our firm, we see raw alerts from firewalls, endpoints, and cloud tools come flooding in. The goal is to shrink the time from detection to a contained response. We help MSSPs build a tiered model and a robust alert triage prioritization process that moves them from a reactive help desk to a true SOC.
“An MSSP without an actionable feedback loop is useless. An MSSP with an actionable feedback loop is gold. … It’s key to ask these types of questions up front, to ensure that the provider is able to be as responsive as your own resources and time constraints require.” – Red Canary Blog
Chaos means failure. Without this workflow, analysts drown in false positives while real incidents get missed. The core framework is non-negotiable:
- Initial Filtering: Automated rules discard known false positives.
- Triage & Categorization: Alerts are scored for severity and impact.
- Escalation Paths: Clear procedures define who acts and when.
We’ve seen successful operations cut raw alert volume by 90% before human review. That’s the baseline for survival.
How the Tiered Triage Model Structures Incident Response
This model assigns specific responsibilities to different analyst levels. It’s about resource efficiency, ensuring the mssp alert triage process explained to your team is followed consistently. Level 1 handles the initial flood, Level 2 digs into confirmed threats, and Level 3 deals with the most advanced incidents.
We built our process around this because it works. It prevents your most expensive experts from wasting time on simple tickets.
The table below shows how responsibilities break down in a mature MSSP. It creates a predictable, scalable flow.
| Tier Level | Primary Responsibility | Typical Action |
| Tier 1 | Initial Triage & Filtering | Dismissing false positives, basic ticket creation. |
| Tier 2 | Deep Analysis & Investigation | Threat hunting, correlating logs across the SIEM. |
| Tier 3 | Advanced Remediation | Incident response for breaches, forensic audits. |
Tier 1 analysts often handle 80% of the total alert volume. Their job is to be a gatekeeper, escalating only what’s necessary. This structure ensures that a possible data exfiltration gets to a specialist fast, while a misconfigured printer alert gets closed quietly.
Why MSSPs Prioritize Automation in Alert Enrichment

Because the clock starts ticking the moment an alert fires. Automation via SOAR platforms enriches alerts with context instantly, changing the way security alerts are prioritized across the environment.
Was this IP seen in a threat feed last week? Is this user currently on vacation? This data turns a generic ‘suspicious login’ into a high-priority ‘potential compromised credential.Manual lookup adds critical minutes, maybe hours.
We’ve watched automated enrichment cut through the fog of war. It pulls in internal context from your IAM system, external intelligence from feeds, and historical data. This process reduces the “mean time to acknowledge” drastically. It can also trigger predefined actions, like isolating an endpoint, containing the threat before a human even gets the notification.
- Context Injection: Adds user, asset, and threat intelligence data.
- Automated Triage: Scores and prioritizes alerts based on enriched data.
- Initial Containment: Can execute playbooks to block IPs or quarantine devices.
This isn’t about replacing people. It’s about arming them with better information, faster. In our experience, proper enrichment can lower the MTTR by over 40%, a tangible difference during a crisis.
How MSSPs Mitigate the Impact of Alert Fatigue
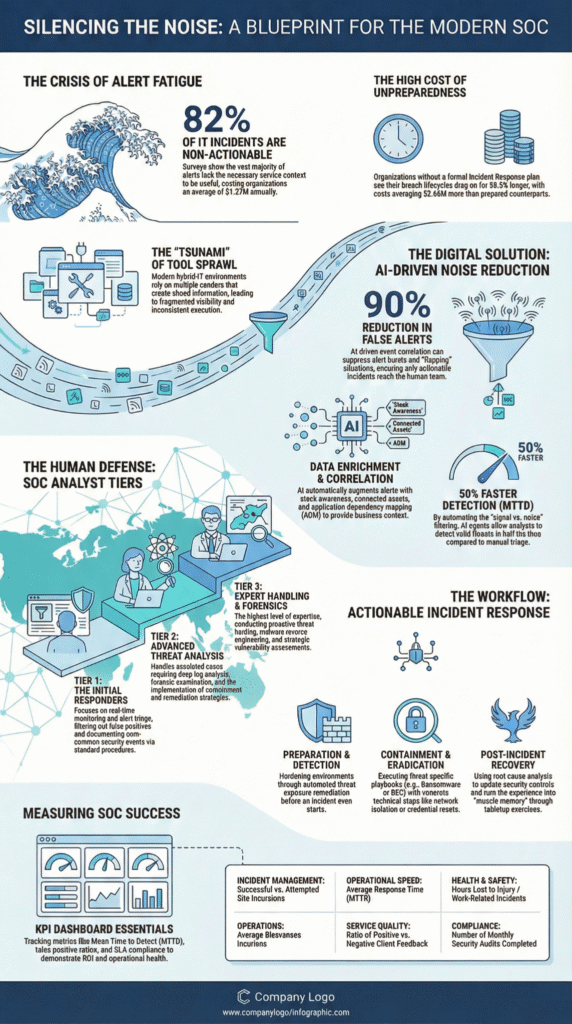
It’s the silent killer of SOC productivity. Alert fatigue happens when analysts are bombarded with low-value notifications. They become desensitized, start skipping details, miss critical signals. We’ve felt that numbness ourselves after long shifts. The mitigation isn’t a one-time fix, it’s a discipline of continuous tuning.
You fight fatigue by aggressively reducing noise. This means regularly reviewing and adjusting detection rules. It means implementing logic to deduplicate identical alerts from multiple sensors.
Sometimes, the simplest static rules, like ignoring alerts from a specific test server, make the biggest dent. Operators in forums often report that 95% of event reduction comes from these diligent, basic tuning efforts, not from complex AI promises.
The goal is to ensure every alert that reaches a human requires a decision. If an alert can be handled automatically, it should be. If it’s consistently a false positive, the rule needs adjustment. This constant refinement protects your team’s most valuable asset: their attention.
What Are the Essential Components of a Client-Facing Alert Report?
Transparency builds trust. Clients don’t just want to be protected, they want to see it. A good report translates technical metrics into business risk. It answers the question, “What are you doing for my retainer?” At MSSP Security, our reports focus on demonstrating value and proving we’re meeting our SLAs.
“Documented resolution details and times are included in reports and used for future review and improvement. This can be aided with diagrams and flowcharts showing how different alerts progress. For example, you might show how an initially low priority alert is escalated as thresholds are reached.” – NinjaOne Blog
The report must show activity and outcome. It’s not enough to list thousands of blocked threats. You need to show response times, incident severity breakdowns, and the remediation steps taken. Highlighting uptime and compliance posture turns your security service from a cost center into a business enabler.
These reviews are where partnership is solidified, where clients understand the scale of threats faced and neutralized.
How Multi-Tenancy Complicates the Alert Handling Workflow

Managing multiple clients in one platform is the ultimate MSSP challenge. A “one-size-fits-all” alert rule is a recipe for failure. What’s normal for one client, say, a marketing firm transferring large video files, could be a critical data exfiltration alert for a law firm. The workflow must account for these unique baselines.
This complexity demands strict data segregation and client-specific tuning. You need isolated data silos for confidentiality, and customized alert thresholds tailored to each environment’s normal behavior. In 2025, over 70% of MSSPs moved toward per-client threshold management to improve accuracy.
It’s more work upfront, but it’s the only way to provide precise, relevant security for each business you protect. The alternative is drowning everyone in irrelevant noise.
FAQ
How does an MSSP alert handling process review improve response times?
An MSSP alert handling process review improves response times by tightening alert triage, automation, and response coordination. Security Operations Centers gain centralized visibility across security tools and SIEM platforms, helping security analysts focus on validated alerts.
This structured approach reduces alert volume, speeds incident response, and strengthens the overall security posture against evolving online attacks and potential cyber attack scenarios.
What should security leaders evaluate during an alert handling review?
Security leaders should review performance metrics, alert management quality, and current security infrastructure health. Focus areas include alert correlation capabilities, effectiveness of security automation solutions, and gaps in incident response efforts.
Reviewing communication methods and predefined communication protocols also reduces the risk of communication gaps and improves security team productivity across daily security activities and broader security operations.
How does automation help modern MSSPs manage alert fatigue?
Modern MSSPs use artificial intelligence and SOAR platforms to filter Automated Alerts and reduce alert fatigue. Automation platforms enrich alert signals with threat intelligence, Network Traffic context, and endpoint detection and response data.
This improves effective response and lets the Security Team concentrate on real security incidents instead of noise, boosting daily efficiency and overall performance efficiency.
Why is centralized visibility critical for scalable MSSP services?
Centralized visibility gives managed security service providers maximum threat visibility across cloud security, network security, and endpoint protection services. With a scalable multi-tenant platform or cloud-native platform, security services providers can monitor the full attack surface and detect potential security threats faster.
This holistic security approach supports proactive security monitoring and improves response tools coordination across multiple client environments.
The Continuous Review of Your Alert Process
Your alert process needs constant care. Threats change, clients upgrade, tools get added. A static workflow becomes a weak spot. Top MSSPs treat triage as a living system. They review rules monthly, analyze metrics quarterly, and dissect every major incident. This cycle prevents stagnation.
It asks hard questions: Are escalations too high? Can we automate more? Are client reports clear? This commitment to refinement turns adequate security into exceptional security. It keeps your team sharp and your clients protected. Start with one alert today.
Need a hand optimizing your entire security stack? We help MSSPs cut tool sprawl and boost service quality through vendor-neutral selection, auditing, and workflow optimization.
Get expert guidance for your stack.
References
- https://redcanary.com/blog/security-operations/five-guidelines-evaluate-mssps/
- https://www.ninjaone.com/blog/alert-handling-process/
