Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

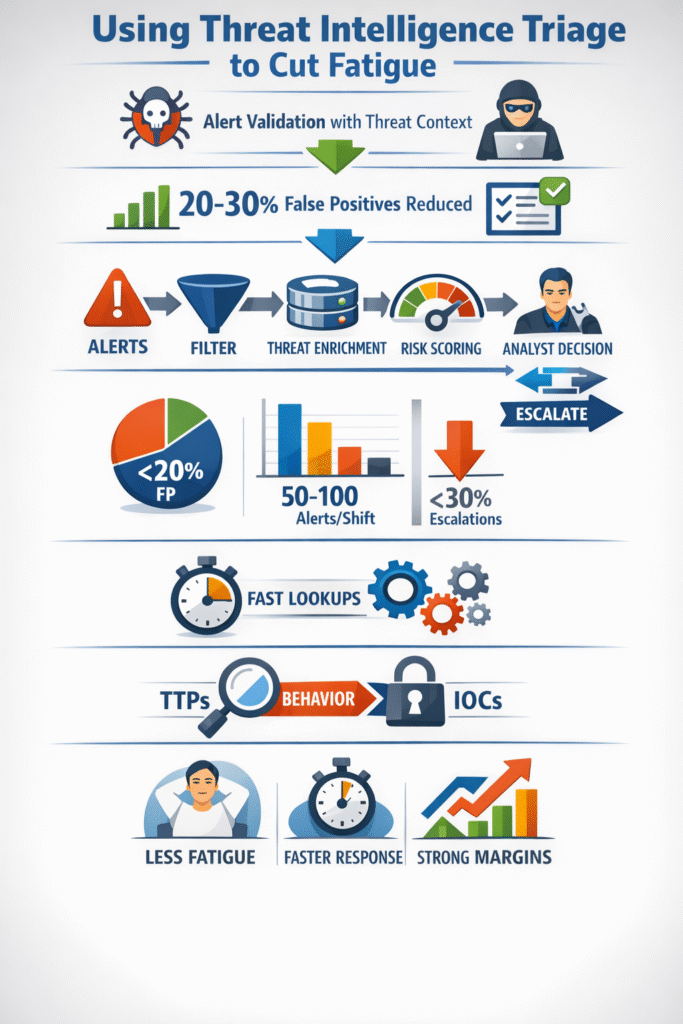
Using threat intelligence triage cuts through alert noise. It uses external data, like known malware or attacker methods, to quickly validate alarms. Good programs see false positives drop by 30%.
This turns a flood of data into a short list of real problems. The goal isn’t more data, but the right context to make a fast decision. See how this approach can give your team time to defend effectively.
Working in a SOC, we know every second counts. Threat intelligence triage makes those seconds meaningful. It’s using external data, like known attacker methods or active campaigns, to filter and prioritize the constant stream of alerts.
“By embedding smart triage practices, security teams can respond to issues in priority order, can respond faster, and reduce breach impact… Integrate triage tools with threat intelligence feeds for enrichment. Automate initial alert scoring, but include human decision-making for escalation.” – SecurityScorecard Blog
Instead of a Tier 1 analyst staring at a suspicious IP, they immediately see it’s tied to a specific ransomware group. That context is everything. It bridges the gap between having data and taking action. High-performing teams use it to focus human effort on the small percentage of alerts that matter, letting automation handle the noise.
The results are real. We see false positives drop by 20-30%, and teams start closing dozens of valid alerts per shift instead of researching just a handful. It moves people from chasing ghosts to stopping real attacks.
Core benefits:
Credits: MyDFIR
Across our audits of MSSP SOC environments, one thing is clear: scale depends on structure. A defined triage workflow keeps real threats from getting buried under noise. Alerts flow from ingestion into a structured alert triage prioritization process that removes known false positives before enrichment begins.
This is where strong platforms separate themselves. A file hash, registry key, or command-line fragment is automatically checked against global intelligence. Once context is added, risk scoring reflects exploit probability and asset value, not guesswork. By the time investigation starts, the analyst has direction.
Teams that follow this model close more alerts per shift and escalate fewer unnecessarily. In our experience, false positives drop below 20%, throughput stabilizes around 50–100 alerts per shift, and Tier 1 accuracy improves significantly. Method beats improvisation every time.
| Triage Metric | Target Benchmark | Why It Matters |
| False Positive Rate | <20% | Directly reduces analyst burnout and alert fatigue. |
| Alert Closure Rate | 50-100/shift | Measures operational throughput and team productivity. |
| Escalation Rate | <30% | Indicates high accuracy in Tier 1 triage decision-making. |
What exhausts analysts isn’t advanced malware. It’s repetitive research. We’ve watched Tier 1 teams struggle without standardized security alert validation techniques, spending 15 minutes on a single process. That doesn’t scale.
In better-integrated environments, lookup is immediate. A suspicious certutil.exe command appears. Instead of switching tabs, the analyst runs a native lookup. Within seconds, it correlates with known malicious behavior and sandbox reports. The decision becomes evidence-based.
When we help MSSPs evaluate new tools, this capability is non-negotiable. Lookups must work consistently across hashes, mutexes, registry keys, and network indicators. It levels the field between junior and senior analysts. Fatigue drops because effort shifts from searching to deciding. That difference compounds over hundreds of alerts.
Many security stacks still rely heavily on static IOCs. We see it often during product reviews. IP blocks and hash matching are useful, but short-lived. Attackers rotate infrastructure quickly.
“Triage is a critical function of MSSPs, and is supposed to help analysts quickly evaluate, prioritize, and act on alerts, separating genuine threats from false positives… Threat-informed response embeds intelligence directly into the alert workflow, so analysts don’t have to hunt for answers. No guesswork. No tab sprawl. No manual lookup.” – ThreatConnect Blog
Behavior tells a longer story. Frameworks like MITRE ATT&CK focus on tactics and techniques: privilege escalation patterns, lateral movement, misuse of native tools. Changing behavior is harder than changing a hash.
When MSSPs shift triage toward TTP-based detection, resilience improves. Instead of blocking one domain, they detect the underlying technique. That reduces false positives and catches new variants of known threats. In our consulting work, we prioritize products that map detections clearly to TTPs, not just feed more indicators into an already noisy queue.
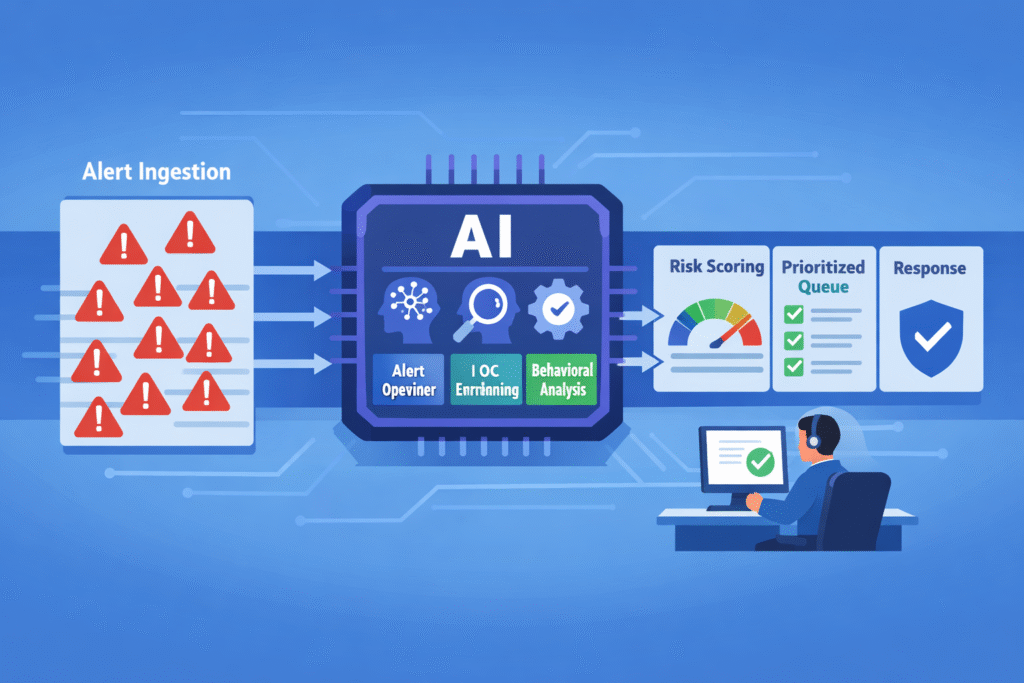
For MSSPs defending multiple client environments, human scale alone isn’t enough. Automation becomes necessary, but only when implemented carefully.
Strong platforms enrich alerts automatically to facilitate risk-based alert prioritization, surfacing intelligence before analysts even engage. Some teams also use retrieval-based AI to structure unorganized threat reports into usable indicators. That reduces manual parsing.
Still, we advise every client to maintain human oversight. Automation should recommend, not decide. In one audit, we saw inaccurate open-source intelligence distort scoring models because no one validated the feed.
AI accelerates workflows, but governance protects them. The right balance allows small teams to operate with the effectiveness of much larger ones, without sacrificing judgment.
Security teams reduce alert fatigue by improving alert triage workflow and cutting false positives early. Start with better alert ingestion rules inside SIEM systems and intrusion detection systems. Use automated enrichment tools to pull contextual information from threat intelligence feeds.
Risk scoring helps prioritize real security incidents. When alert validation is consistent, SOC analysts spend less time chasing noise and more time handling incident response effectively.
Using threat intelligence triage adds context to raw security alerts. Instead of only seeing file hashes or a malicious IP, security teams gain threat data about attack patterns, threat actors, and known threat campaigns.
Contextual enrichment from threat repositories and malware databases helps determine incident severity faster. This improves response time and supports better response and remediation decisions during incident triage.
SOC analysts validate indicators of compromise by combining automated analysis with structured alert management. IOC enrichment pulls data from threat intelligence platforms and monitoring systems, checking file hashes, network traffic, and firewall logs.
Behavioral analysis tied to the MITRE ATT&CK framework reveals malicious activity like lateral movement. This approach shortens response times and improves Cyber Triage accuracy without overwhelming Security Operations Centers.
Artificial intelligence can support AI-enabled incident triage without replacing human judgment. Machine learning models review security alerts, identify attack vectors, and assist with risk scoring.
Automated tuning reduces alert overload in SIEM software and endpoint detection and response systems. However, SOC analysts still handle final alert validation and team coordination. AI strengthens security posture when combined with oversight.
Moving from alert overload to a focused, intelligence-driven posture is a commitment to a smarter process. It requires integrating threat context into your workflow, shifting focus from chasing temporary clues to understanding attacker behavior, and using automation to free your team for critical analysis.
For MSSPs, this is the path to sustainability, transforming a reactive, overwhelmed team into a proactive, resilient one. The threats keep coming, but this approach ensures your energy is spent on the fights that matter.
Ready to build that sustainable, fatigue-free operation for your MSSP? Our consulting team can help you select, audit, and optimize the right tools.