Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

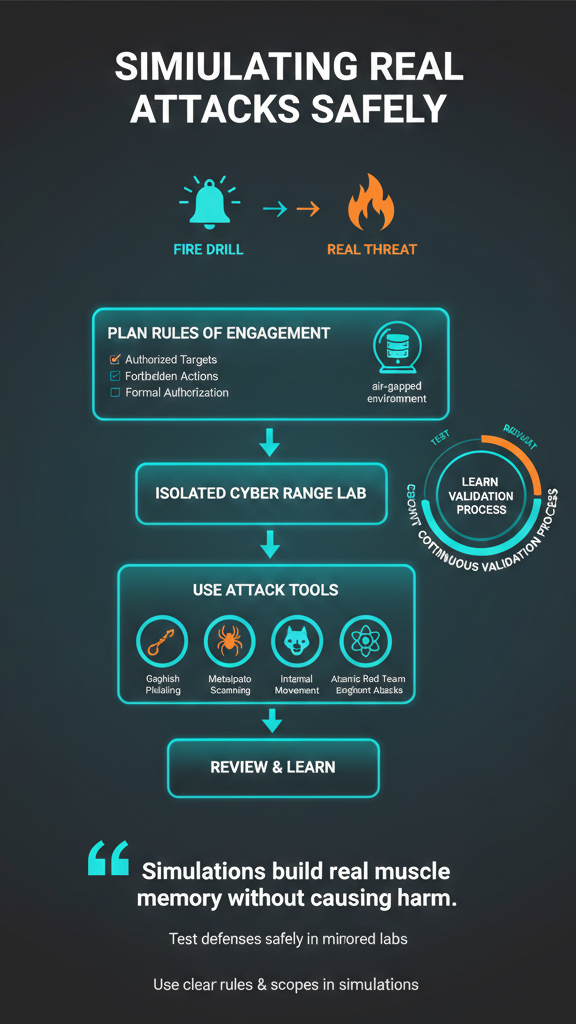
You simulating real world attacks safely to find security gaps before real attackers do. Think of it like a fire drill versus a real fire; it’s the only reliable way to know if your team and tools will hold up. Done poorly, it can cause the very breach you’re trying to prevent. The key is a controlled, repeatable process that builds muscle memory without causing harm.
At MSSP Security, we use a specific framework to validate client defenses, turning theoretical risk into measurable, actionable data. Here’s how you can build this capability for your own organization. Keep reading to learn how.

The foundation is a written contract: the Rules of Engagement (RoE). Clear compliance testing requirements are defined here to specify exactly what’s in and out of bounds.
“SightGain can safely initiate threat emulations within the production environment with tools analysts use every day.” – SightGain Blog
Vague goals lead to vague results. We define objectives you can actually measure.
This precision ensures every test has a definitive finish line and yields actionable data, not just a list of vulnerabilities.
Credits: SanRocker
Simply put, because simulations are designed to be messy. You’re intentionally breaking things to find weaknesses, so you absolutely must contain the explosion. Testing in a live production environment is a terrible idea, it’s like practicing surgery on a patient who needs to clock in for their shift in an hour.
The risk of accidentally taking down a critical server or corrupting data is unacceptably high. A simulated ransomware test should never touch real financial records.
The solution we implement for our clients is a dedicated cyber range. This is an isolated lab that mirrors the real production setup perfectly: the same Active Directory, firewall rules, and server builds. But it’s completely air-gapped from the live network.
We build these using virtualized snapshots. If a test run completely destroys a system, you just revert to the snapshot. You’re back to a clean slate in about a minute. In our view, it’s the only responsible way to practice failing safely.
You need a toolkit that mimics the adversary’s playbook. Strong penetration testing coordination between red and blue teams makes open-source frameworks far more effective for learning and emulating real attack techniques.
For a holistic view, especially for ongoing validation, specialized Breach and Attack Simulation (BAS) platforms can automate much of the process. The key is to match the tool to the threat you’re emulating.
| Attack Vector | Tool Example | What It Tests |
| Phishing & Social Engineering | Gophish | Employee awareness and email gateway controls. |
| Network Exploitation & Scanning | Metasploit, Nmap | Vulnerability management and intrusion detection systems. |
| Internal Movement | BloodHound | Active Directory security and attack path management. |
| Endpoint Attacks | Atomic Red Team | Endpoint Detection and Response (EDR) efficacy. |
Gophish, for instance, lets you safely send phishing emails to your own staff, tracking who clicks. It’s a controlled way to measure the strength of your human firewall. These tools let you safely execute the tactics from frameworks like MITRE ATT&CK, providing a common language for your red and blue teams to discuss what happened.
Most manual penetration tests freeze risk in a single moment. We’ve seen it ourselves, a clean report on Friday, a fresh exposure by Monday. That gap is where continuous validation earns its keep. Instead of waiting months for the next engagement, automated simulations run around the clock, pressing on defenses the same way a real attacker would.
“Rather than having to hope they remember processes and policies during live events, they can practice in realistic attack simulations that replicate the actions of a real-world cyber threat without putting any of your infrastructure at risk.” – CloudShare
Over time, patterns emerge. A rule change closes one door but quietly opens another. Drift shows up fast. When we audit security products for MSSPs, this steady stream of data changes everything.
It stops vague debates about posture and replaces them with clear, current proof of what’s holding and what isn’t. Resilience becomes measurable, not theoretical.

The report alone doesn’t make anyone safer. Real progress happens in the review room. We usually bring red and blue teams together, walk the timeline, and replay the breach like a game film. Someone always spots the missed alert. Another control failed in a way no one expected.
From there, fixes turn into process. Prioritizing high-risk findings and fast remediation becomes the focus. Detection rules get tuned. Incident response steps tighten up. Training focuses on the exact tactic that slipped through.
We track how long it took to spot and stop the attack, then test again later to see real improvement. That loop, test, learn, adjust, is how defenses actually mature over time.
Attack simulation safely recreates real threats across your attack surface to reveal how cyber adversaries move through systems. By testing realistic attack vectors like phishing emails, malware attacks, and network infiltration attacks, teams see which security controls fail.
This form of security validation shows weak attack paths before data breaches happen and helps strengthen overall cybersecurity defenses.
Yes. Running breach and attack simulation exercises exposes gaps in incident response plans before a real crisis hits. Red teams trigger realistic scenarios such as ransomware attacks or data exfiltration while SOC analysts practice detection and containment.
The results shorten dwell time, improve coordination, and strengthen cyber resilience across security operations and response workflows.
Social engineering tests the human side of cyber security using spear phishing, deepfake voice calls, and email spoofing scenarios. These simulations measure how employees handle malicious links and CEO fraud attempts.
The results guide security awareness training, build a stronger human firewall, and reduce success rates of real-world phishing attacks over time.
Attack simulation tools run frequent tests against evolving attack techniques mapped to frameworks like MITRE ATT&CK. This approach validates security measures, endpoint controls, and intrusion detection systems as the threat landscape changes.
Continuous security validation helps teams catch new exposure fast instead of waiting for yearly penetration testing reports.
Building your adaptive defense isn’t about playing hacker. It’s a disciplined method to stress-test your people, processes, and technology. This practice turns abstract threats into concrete, fixable problems.
The framework is simple: plan meticulously, isolate completely, execute precisely, and learn relentlessly. This cycle replaces guesswork with real knowledge, moving you from reactive fear to proactive confidence. Ready to test your defenses? Let’s build your perfect tech stack.