Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

Annual training doesn’t work. You know it, your team knows it, and the data screams it. Employees forget 90% of what they hear in a one-off session within a week, leaving your organization exposed.
The modern threat landscape, powered by AI and relentless social engineering, demands a fundamental shift from a compliance checkbox to a living, breathing security culture. This isn’t about another webinar. It’s about embedding vigilance into the daily workflow. Keep reading to learn why ongoing security education reinforcement stops breaches

We’ve all sat through it. The same slides, the same dramatic voiceover about the dangers of weak passwords. You click through, maybe pass a quiz, and get that certificate for HR. It feels like a task completed, a risk mitigated. But it’s a charade. The forgetting curve, a concept from learning science, shows knowledge evaporates without reinforcement.
“When security behaviors are consistently modeled by leaders, rewarded by the organization, and integrated into daily workflows, they become habits. Over time, these habits evolve into values shared across the organization, making security not just a process, but a part of how work gets done.” – Keepnet Labs
Within days, the specifics of that spear-phishing example are gone. What remains is the dull resentment of another mandated task. This model creates a tick-box mentality, where the goal is to finish, not to understand. It treats security as an annual event, not a daily practice. Meanwhile, threats evolve weekly.
The result is a dangerous gap. Your policies might be perfect, but if your people see security as HR’s yearly nuisance, they’re not a defense layer. They’re a vulnerability. Real change requires a different rhythm.
Credits: Simons Institute for the Theory of Computing
What does a real security mindset look like? In our audits for MSSPs, we see it clearly. It’s not paranoia; it’s practical awareness. It’s the accountant who pauses at an invoice from a domain that’s one letter off. It’s the marketing manager who questions a “Google Docs” link asking for Microsoft login details.
This mindset sees security protocols as sensible habits, like locking a door. You can’t build it with an annual training module. It’s a skill, like learning a language, built through regular, focused practice.
We’ve seen data showing that companies treating training as a mere compliance checkbox have a significantly higher rate of providing no real training at all. That’s negligence, not strategy.
The shift is cultural. Leaders must participate in simulations. You must celebrate the employee who reports a phish, not just reprimand the one who clicks.
It becomes part of “how we do things here,” woven into daily operations through structured security awareness training management that reinforces expectations consistently. That’s the difference between a rulebook and a true culture.
Let’s be blunt. If your training feels like a chore, it’s failing. Engagement isn’t a nice-to-have, it’s the entire mechanism for effectiveness. People tune out boring content. They resent being talked down to.
And they absolutely remember the time they reported a phishing test and never heard a word back from the security team. That silence teaches them that reporting is pointless. These aren’t small details. They are the reasons programs stall.
Consider the content itself. Is it a generic video about “cyber threats” made five years ago? Or is it a 90-second scenario about a fake Slack message from the CEO asking for gift cards, tailored to your industry? One is background noise. The other feels real, immediate. Furthermore, over half of users who spot a threat simply delete it without reporting. That’s a massive intelligence failure.
Your team sees threats and you never know. That gap exists because traditional training doesn’t build the habit of reporting or truly focus on reducing human error risk in daily workflows. It just warns about clicking. The goal must be creating active participants in your defense, not passive avoiders of punishment.
The real change happens with smarter reinforcement, not more training. In our work, we’ve seen micro-learning work best. Think of a 90-second video on spotting vendor impersonation, pushed to your team’s chat every Tuesday. It’s a simple nudge, not a disruption.
This approach fights the “forgetting curve” by delivering small, relevant lessons right in the workflow, where they stick.
Then, add a layer of gamification. We’re not talking about turning security into a game show. It’s about tapping into basic human motivation, recognition and a bit of friendly competition. Award points for reporting simulated phishing emails. Run a simple leaderboard between departments. Use quick, scenario-based quizzes where choices have realistic outcomes.
This transforms a compliance chore into an engaging challenge. When someone correctly flags a tricky phishing test and gets instant, positive feedback, they feel capable. That feeling of competence, knowing “I can handle this”, is what drives people to make secure choices every time, not fear. It’s what builds lasting behavior.
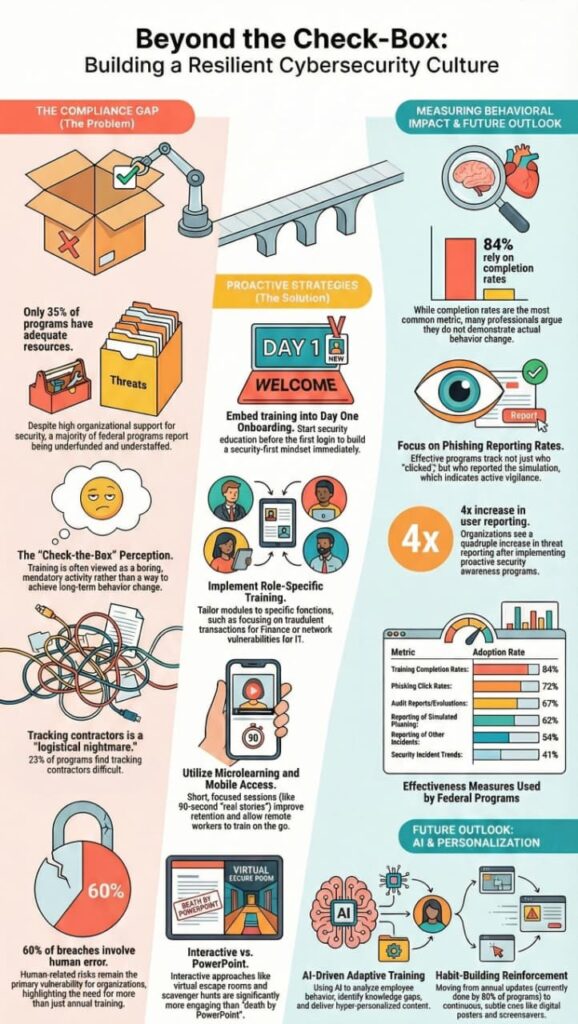
Forget tracking who simply finished a training module. A 100% completion rate with zero behavior change is a complete failure. The metrics that matter are behavioral.
“Humans all learn differently, but one thing is certain: we all learn by repetition. It’s important for awareness of cybersecurity risks and best practices to be frequent and varied… Cybersecurity education that sticks can be the difference between a user who clicks a link and a user who stops to think.” – Center for Internet Security (CIS)
We advise our MSSP partners to watch three things. First, the phishing simulation click rate, aim to keep it consistently under 1%. Second, track how long it takes for a suspicious email to be reported; faster is better. Third, monitor the number of legitimate security reports staff submit. An increase here is a strong sign people are engaged and feel safe speaking up.
In our audits, we see the proof. Click rates drop over time. Reporting rates climb. The ultimate result is a measurable drop in real incidents caused by human error. That’s the real ROI, a direct reduction in risk and cost. Data shows organizations with active awareness programs contain breaches over 50% faster, saving money and protecting their reputation.

Forget the old model. A modern Security Education, Training, and Awareness program is continuous, adaptive, and integrated. It starts with security-first onboarding. Day one, new hires learn not just where the coffee is, but how to handle sensitive data and report concerns.
Then, it continues with a rhythm of reinforcement. Monthly micro-lessons. Quarterly deep-dive sessions on emerging threats like AI voice cloning or QR code phishing. It uses varied content, short videos, infographics, interactive labs, to cater to different learning styles.
Crucially, it’s contextual. The training for your finance team on wire fraud attempts will differ from the training for developers on secure coding and dependency management. This relevance increases buy-in. The program also seamlessly integrates with your existing tools.
Training on how to use the “Report Phish” button in Outlook or the proper way to handle a lost mobile device makes the lessons immediately practical, especially when integrating training with incident response so reporting turns into immediate action.
It’s about closing the loop between knowledge and daily action, building those digital fortifications one habit at a time.
Ongoing security education reinforcement means keeping Security Awareness active all year, not once annually. Instead of one-time Security Awareness Training, you run short training programs, phishing simulations, and reminders that build habit formation.
It strengthens your human firewall, improves phishing resilience, and helps employees respond correctly to cyber threats, social engineering attacks, and daily digital risks.
Ongoing security education reinforcement improves threat identification and phishing prevention skills. Employees learn to spot phishing emails, suspicious phishing correspondence, and social engineering tactics before damage happens.
With regular phishing simulations and clear incident reporting procedures, your security team reacts faster. This lowers the risk of data breaches, ransomware avoidance failures, and costly security incidents.
Security training should happen continuously, not yearly. Use short training modules monthly, supported by Adaptive Learning and Hands-on Training sessions quarterly. Reinforcing Cybersecurity through micro-lessons, phishing simulations, and password hygiene reminders builds automatic actions.
This steady rhythm improves your security posture, strengthens cybersecurity defenses, and supports long-term threat readiness.
Yes, if done right. Positive reinforcement, gamified modules, and practical cybersecurity education boost employee engagement. When staff practice incident recognition, multi-factor authentication, and password management in real scenarios, they feel capable instead of blamed.
That confidence strengthens security culture, supports better incident reporting, and turns the human element into a defensive asset.
Ongoing security education isn’t a one-time project. It’s a core operational discipline, as essential as patching systems. With the human element being the primary target, your staff is your most critical defensive asset. Continuous training builds resilience from within, turning your workforce from a potential weak link into your most reliable human firewall.
The work is never finished, and it shouldn’t be. Threats evolve daily, so our vigilance must be constant.
Ready to build a tech stack that supports this discipline? Let’s Build Your Perfect Tech Stack