Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM

You have the report. The real security work starts now. Managed pen test coordination, often handled by a Managed Security Service Provider (MSSP), makes sure those critical findings get fixed.
It turns a one-time security snapshot into an ongoing process that actually reduces risk. Stop letting vulnerabilities sit in a PDF. This is how you close the loop. Read on to learn how Managed Penetration Testing Coordination Prevents Breaches.

Most penetration tests fail right after the report lands. It’s a common story. An organization receives a massive list of vulnerabilities, but then, nothing. The IT department is buried, system owners can’t prioritize, and the security investment seems to vanish.
The critical space between discovery and remediation is where attackers win. We know this because we see it in the aftermath of incidents we’re called to analyze. The issue isn’t finding problems, it’s the complete lack of a process to fix them.
| Area | Traditional Penetration Testing | Managed Penetration Testing Coordination |
| Post-report action | Report delivered and often ignored | Findings tracked through remediation |
| Ownership | Unclear responsibility | Each vulnerability has a defined owner |
| Prioritization | Based on severity scores only | Based on real business impact |
| Remediation speed | Slow and inconsistent | Structured timelines and accountability |
| Retesting | Rare or skipped | Built-in validation and closure |
| Risk reduction | Minimal long-term improvement | Continuous security posture improvement |
This is where managed penetration coordination changes the game. For us, it’s about building a security partnership, not just selling a scan.
A strong MSSP shouldn’t just deliver testers and a PDF. We embed ourselves, managing the complex, human-driven work of translating technical findings into real defensive improvements.

Scoping decides everything. A vague test wastes time and budget. It can miss critical assets or disrupt production. We’ve seen both. The goal is precision.
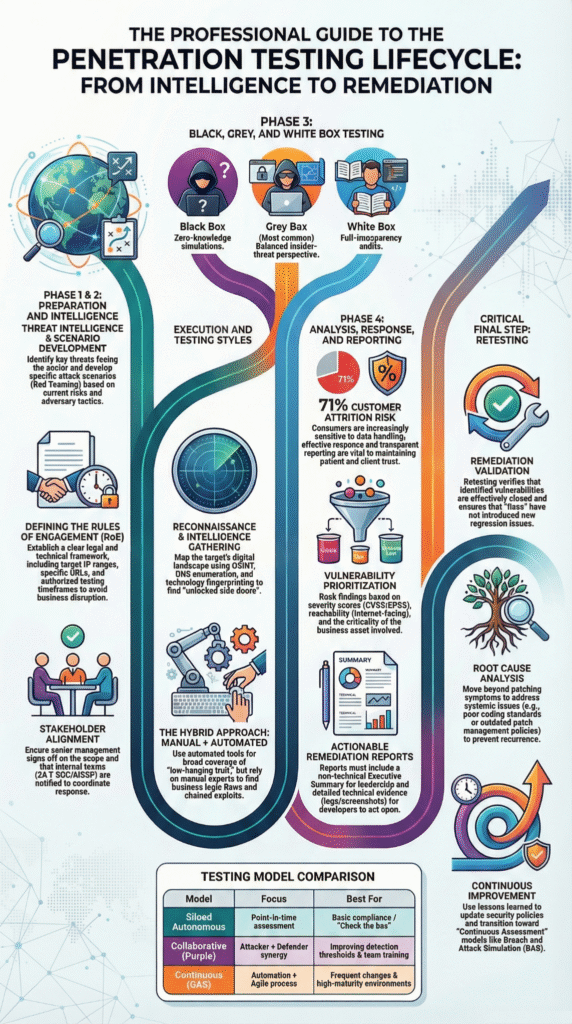
“The single most critical step in any successful penetration test happens before a single packet is sent: defining the scope and the Rules of Engagement (RoE). This isn’t just bureaucratic red tape; it’s the foundational document that separates a professional, ethical security assessment from a chaotic, potentially damaging, and illegal hack.” – MSP Penetration Testing
You must define the battlefield: list specific IPs, apps, and APIs in-scope, and declare what’s off-limits. We document this in the Rules of Engagement. Without it, you’re blind.
Our scoping calls build the strategy. We ask direct questions: What can’t you afford to lose? What compliance standard binds you? Has a past incident shaped your fears?
The answers shape the test. A financial app test targets transaction flows. A hybrid cloud test hunts misconfigured storage. Getting this right gives your test a clear mission, focusing resources on the threats that matter.
Most breakdowns we see don’t happen because of weak testing. They happen because nobody owns the outcome. When roles are unclear, findings drift, deadlines slip, and real risk stays in place. A managed coordination model fixes that by assigning responsibility from leadership down to the technical teams.
In our audits with MSSPs, the provider usually acts as the program lead, scheduling tests, overseeing methodology, and organizing findings. But the real value comes from adding context. Instead of just listing vulnerabilities, we help translate what each flaw actually means in the environment and why it matters.
On the client side, system owners become the drivers of remediation. They track fixes, validate progress, and keep momentum moving. Security leaders provide governance, making sure everything aligns with business risk and compliance goals.
Red and Blue teams also shift from rivals to collaborators. When knowledge flows between testing and defense, attacks stop repeating, and defenses finally improve.
Strong coordination turns penetration testing into a repeatable process instead of a once-a-year scramble. Every effective program we’ve reviewed follows the same rhythm.
1. Planning & Scoping
Stakeholders align on targets, attack paths, and rules of engagement. We often see risk drop immediately just from tightening scope and asset visibility.
2. Execution & Discovery
Testers combine automated tools with hands-on techniques while coordination keeps activity safe and low-impact. High-risk issues are flagged immediately.
3. Analysis & Reporting
Findings are translated into business risk through interpreting penetration results, so instead of raw vulnerability lists, teams receive prioritized issues with clear remediation guidance.
4. Remediation & Handoff
This is where progress happens. Engineers walk through fixes, timelines are assigned, and ownership stays clear.
5. Validation & Retesting
Systems are retested to confirm gaps are closed. Lessons learned feed the next cycle, steadily shrinking the attack surface.
If we’re honest, this is the point where many security efforts stall. A penetration test finishes, a long report arrives, and the IT team, already stretched thin, isn’t sure what to tackle first. We’ve sat in those handoff calls where frustration is obvious. Dozens of “critical” findings, little context, and no clear path forward.
“MSSPs must bridge the gap between vulnerability discovery and resolution by enabling seamless collaboration between testers and client development or DevSecOps teams. By fostering this transparent, two-way collaboration, MSSPs not only report vulnerabilities but also enable faster fixes, strengthening their role as trusted security partners rather than external auditors.”– Indusface
With outsourced pen test scheduling in place, coordinated programs change that dynamic. Instead of overwhelming lists, each major issue comes with:
Suddenly the conversation shifts from volume to priority. One API flaw that exposes customer data becomes more important than fifty low-impact misconfigurations.
This is also why fully automated testing rarely delivers results on its own. Tools find issues. Humans turn them into solved problems. Every strong MSSP program we evaluate puts real effort into this translation layer.

Security leaders often ask how to justify ongoing testing programs. From what we’ve seen across MSSP clients, the answer isn’t report counts, it’s risk reduction.
One properly prioritized vulnerability fixed early can prevent an incident that costs millions. We’ve reviewed cases where a single exposed authentication flaw could have enabled ransomware or data theft. It was found, fixed, and quietly avoided becoming a headline.
Coordination also slashes Mean Time to Remediate. Clear ownership, better reporting, and built-in retesting keep issues from lingering for months.
There’s a compliance upside too. When auditors ask for proof of improvement, coordinated programs can show closed findings, retest evidence, and shrinking attack surfaces over time.
Instead of penetration testing being a checkbox, it becomes a measurable security control. And in our experience, that shift is what separates mature MSSPs from those stuck reacting to the same risks every year.
Managed penetration testing coordination connects penetration testing, remediation, and retesting into one security process. Instead of isolated vulnerability scanning, security professionals track attack vectors, security gaps, and fixes continuously. Ethical hackers test real attack paths while teams close security flaws quickly.
This ongoing loop strengthens security defenses, reduces exposure across cloud environments and web applications, and keeps the organization ahead of the evolving threat landscape.
Basic security assessments rely heavily on automated scanning tools and vulnerability scanners. Coordinated penetration testing combines automated penetration testing with manual penetration testing by penetration testers.
Ethical hacking techniques simulate threat actors using real attack patterns like privilege escalation and lateral movement. The result is clearer insight into security vulnerabilities, network vulnerabilities, and real business risk instead of long technical vulnerability lists.
With managed penetration testing coordination, system owners, Blue teams, and Red teams stay aligned on scope, IP addresses, attack simulation timing, and security controls. Ethical hackers avoid disrupting production systems while still testing attack surfaces.
This structure reduces accidental outages, improves incident response readiness, and ensures exploitation attempts uncover real security threats before malicious threat actors trigger costly security breaches.
Coordinated programs blend black box testing, white box testing, and gray box testing based on penetration testing objectives. Network penetration tests use network diagrams and network mappers, while web application security reviews analyze source code and API endpoints.
Many teams map findings to MITRE ATT&CK to understand attack paths and advanced persistent threats, strengthening overall cybersecurity strategy and regulatory compliance efforts.
Coordination is your security foundation. The real value of a test is the final, verified fix, not the report itself. This turns reaction into resilience.
It creates a clear, accountable process out of chaos, aligning your technical and business teams on risk. In today’s threat landscape, this continuous approach is what prevents breaches. Start your next test by asking not just what will be found, but how it will be fixed.
For MSSPs aiming to streamline operations and build a stronger service foundation, our expert consulting guides product selection, auditing, and stack optimization.
Let’s build your perfect tech stack.