Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
Address
304 North Cardinal St.
Dorchester Center, MA 02124
Work Hours
Monday to Friday: 7AM - 7PM
Weekend: 10AM - 5PM
You’re staring at a screen full of alerts. A firewall block here, a failed login there. Alone, they’re just noise. But when you start correlating events, those disjointed data points snap together into a story. It’s the difference between seeing a single suspicious character and uncovering the entire heist plan.
This process turns overwhelming log data into actionable intelligence, letting your team move from reactive panic to controlled response. We’ll show you how it works, why context is everything, and how to implement it without drowning in complexity. Keep reading to transform your investigative approach and correlating events incident investigation.
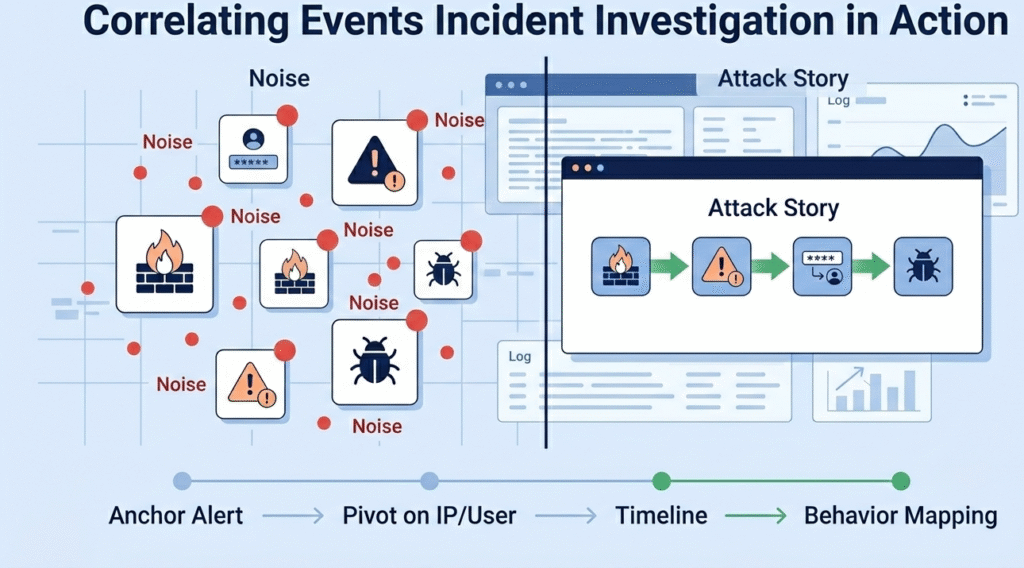
Your security tools are like witnesses. Each one saw something different. The EDR spotted a weird process. The firewall caught an odd connection. The identity system flagged a login at 3 a.m. By themselves, these alerts are just noise.
“Correlation is the key that links alerts and incidents, transforming disparate data points into insightful information… This dynamic approach ensures security teams have an up-to-date view of the threat landscape, enabling proactive threat mitigation.” – Quorum Cyber
But when you bring the stories together, the picture becomes clear. We’ve seen it happen: a stolen credential used after hours, malware launching on a server, and then a try at stealing data. That’s the story.
For us, this work isn’t a nice-to-have. It’s critical. Threats can hide inside a network for months. Connecting these events shrinks that time from months to minutes. You stop chasing false alarms and start dealing with the real problem.
Our job is to turn this theory into practice for MSSPs. We help teams move from a flood of logs to a short list of real incidents. This process:
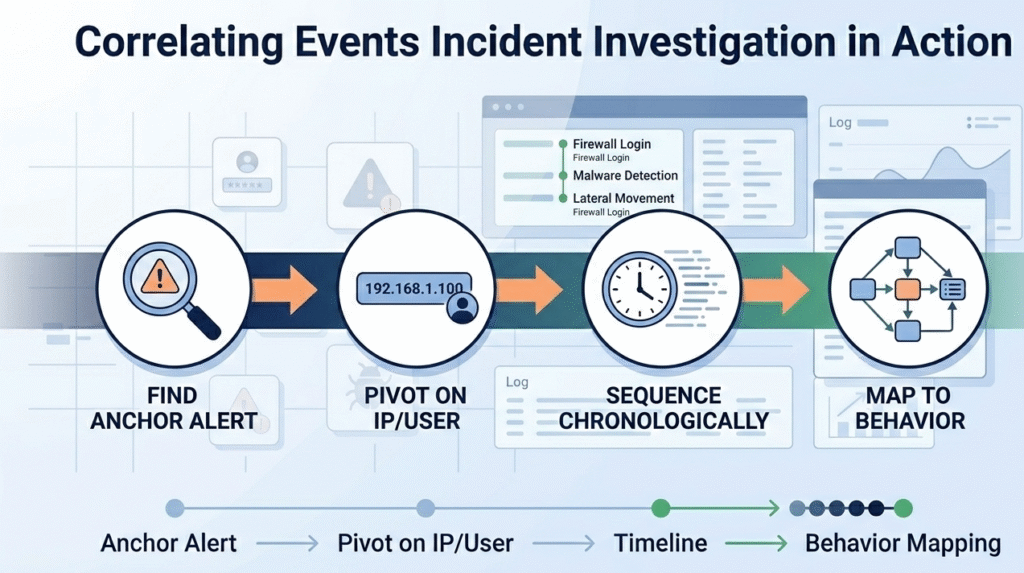
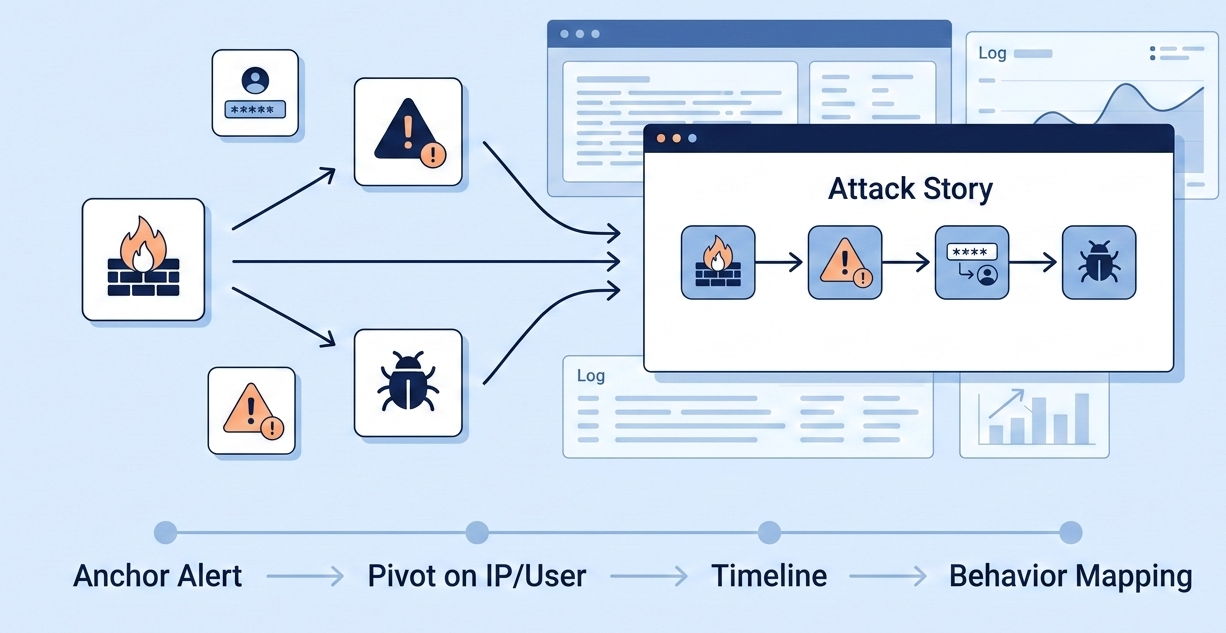
An alert goes off. What’s next? Effective investigation starts with a single point and builds out from there. By following structured incident investigation analysis steps, we begin with the anchor, the alert that started it all.
From there, we pivot. We hunt for the same IP in proxy logs, the username in auth records, and file hashes on endpoints. As we analyze security incident data, we gather every related log and put them in order. Time-based analysis is everything.
A few minutes can rewrite the whole story. Was the config change before the breach? Did a user login from two places at once? Building this sequence shows the attacker’s path. Finally, we visualize it. A timeline graph makes the cause-and-effect clear for everyone.
Our process for MSSPs is simple:
This structured method stops teams from getting lost. It forces you to follow evidence, not a hunch. For teams without a 24/7 SOC, this can feel overwhelming. That’s where our experience comes in. We’ve built our rules and playbooks from seeing these patterns every day, which cuts the learning time down dramatically.
In our experience auditing tools for MSSPs, no two correlation engines behave the same. The right approach depends on the threats a team faces every day. Rule-based correlation still earns its place.
We’ve helped MSSPs write clear logic, like flagging multiple failed logins followed by a success from the same IP, and then tested whether the platform explains that linkage cleanly. When analysts can see exactly why an alert fired, trust follows.
At the same time, attackers rarely stick to patterns. During product evaluations, we often see machine learning separate strong platforms from average ones. Behavioral baselining exposes the subtle moves rules miss: unusual access paths, slow data staging, odd process timing.
The strongest Security Operations Centers layer both approaches, and we guide MSSPs to validate that balance before committing to any new tool.
| Technique | Best For | Real-World Example |
| Rule-Based | Known threat patterns, compliance checks. | Correlating a phishing email click with a subsequent outbound connection to a suspicious domain. |
| Machine Learning | Detecting novel, slow-burn attacks and insider threats. | Flagging a credentialed user slowly accessing unusual fileshares over weeks in preparation for data theft. |
| Graph Analysis | Understanding lateral movement and attack paths across complex networks. | Mapping how an attacker jumped from a user’s workstation to a database server via three intermediate systems. |
The goal is to have your correlation engine do the heavy lifting of sifting through the event collection, so your human experts can focus on the nuanced analysis of the few truly serious incidents that bubble up.

Raw log data is weak. An alert on a server is just an alert. But an alert on a server that hosts your customer database, triggered by an account flagged in a threat intelligence feed, that’s a crisis.
“After a security incident, event correlation is essential for conducting thorough investigations. Analysts can backtrack through correlated events to pinpoint the source of an attack. This helps in understanding how the breach occurred and what vulnerabilities were exploited…” – Alooba
Contextual enrichment is what makes correlation truly intelligent. It’s the process of bolting additional meaning onto every event. This means tagging data with asset value, user roles, geographic location, and threat intelligence indicators.
This enrichment allows for dynamic risk scoring. A detected cryptojacking attack on a development server might be a low-severity incident. The same attack on a production financial server is a critical P1. By integrating context, your correlation reports automatically reflect business impact, not just technical severity.
This stops your team from wasting cycles on low-risk noise and directs them to the incidents that truly matter to the safety and security of the organization. It turns your security tools from simple log collectors into business risk advisors.
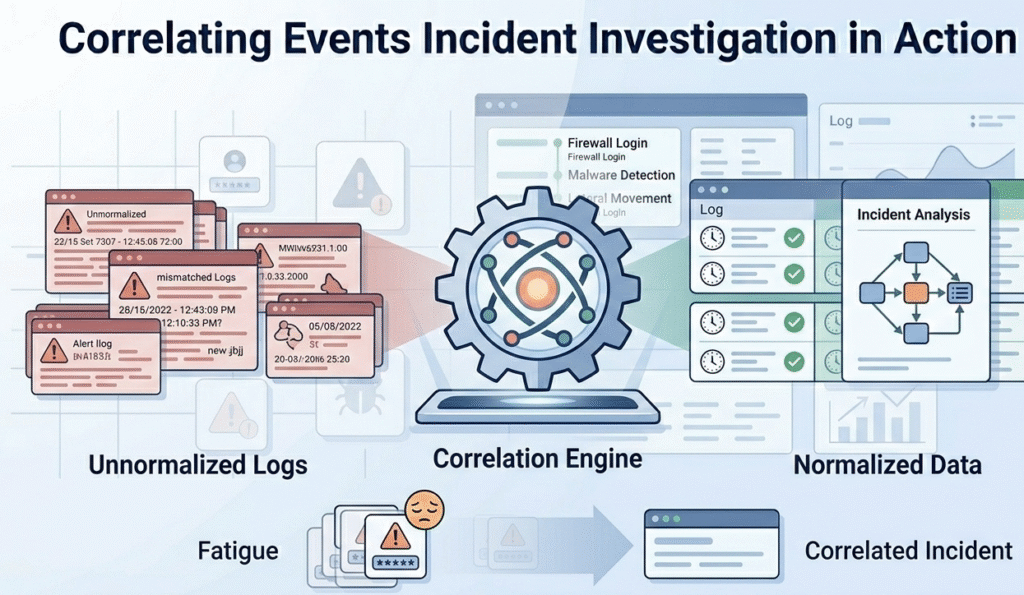
For all its power, correlation isn’t a magic box you plug in. The biggest hurdle is data quality. The principle of “garbage in, garbage out” is absolute here. If your logs aren’t normalized, if one device calls a user “john.doe” and another uses “jdoe”, your correlation engine will see two different people.
If timestamps aren’t synchronized to a common source, your timeline will be fiction. Precise digital evidence collection and normalization are unglamorous but essential foundational tasks.
Then there’s the human factor. Overly broad correlation rules create alert storms, leading to fatigue and missed critical events. Conversely, rules that are too narrow let attacks slip through the gaps.
Tuning is a continuous process. Furthermore, complex machine learning models can become “black boxes,” where analysts don’t trust the incident because they can’t see the logic. Choosing tools that offer explainable AI, showing why events were linked, builds crucial trust with your security expert teams.
Event correlation connects scattered security events into one clear attack story. Instead of chasing single alerts, security teams analyze related log data across network devices and systems.
This speeds incident detection, clarifies incident severity, and reduces alert queue overload. By linking patterns early, teams shorten incident response time and focus on real security breaches instead of isolated noise.
Strong log correlation starts with clean log collection and Data Normalization. Security tools, network infrastructure, and log repositories must send consistent incident data. Without accurate timestamps and standardized fields, a correlation engine can’t connect security events properly.
Good event management ensures every incident detail supports root cause analysis and reliable correlation reports.
Machine learning helps when threats avoid simple correlation rules. It supports Pattern Recognition across large volumes of log data to detect subtle security breaches.
For example, it can surface unusual access patterns or slow malware installation attempts. In a Security Operations Center, combining machine learning with rule-based event correlation strengthens automated investigation and detection risk coverage.
A well-tuned correlation rule links related event triggers instead of flagging isolated activity. By grouping security events into one incident report, security teams avoid duplicate alerts in the alert queue.
Field-level correlation and context, such as asset value at risk, help adjust incident severity. This improves incident management and supports smarter corrective actions.
Event correlation turns digital noise into a clear story. It’s the skill of connecting alerts to see the full attack. This moves you from guesswork to understanding.
Start with one attack pattern, like brute force. Build a rule for it. See how it changes your workflow. The shift to being proactive happens one story at a time. If the gap feels too wide, a partner can help. We guide MSSPs in selecting and tuning the right tools to turn logs into your best detective.