Security teams today face constant pressure to respond quickly while managing an overwhelming number of alerts. Without structure, response efforts often become inconsistent and inefficient. SOAR playbooks help solve this by turning complex processes into clear, repeatable workflows.
From our experience in MSSP Security, we’ve seen how well-designed playbooks bring order to chaos. They allow organizations to respond faster, reduce manual effort, and maintain consistency across incidents, even as threats continue to evolve. Keep reading.
Key Insights
Effective SOAR playbooks are not just about automation, they are about clarity, adaptability, and real operational value.
- Focus on real, repeatable incidents first
- Combine automation with human judgment
- Keep workflows simple and modular
What Is a SOAR Playbook?
Understanding what is a security response playbook starts with viewing it as a predefined workflow that guides how an incident is handled from detection to resolution. It combines automation, orchestration, and decision logic to ensure responses are consistent and efficient.
From a broader perspective, organizations use playbooks to standardize processes. From our side, as part of MSSP Security operations, we design them to reduce response time while still preserving analyst oversight where it matters most.
Why Effective SOAR Playbooks Matter
Many organizations invest in automation tools but fail to see meaningful improvements. In most cases, the gap lies in how playbooks are designed.
We’ve observed that when playbooks are aligned with real workflows, they can:
- Reduce response time significantly
- Improve consistency across teams
- Lower analyst fatigue
- Enable smaller teams to handle larger workloads
At the same time, MSSP Security providers often help bridge capability gaps by bringing tested playbook frameworks that organizations can adapt quickly.
“Automation applied to an inefficient operation will magnify the inefficiency.” – Wikipedia
This is why thoughtful design is critical.
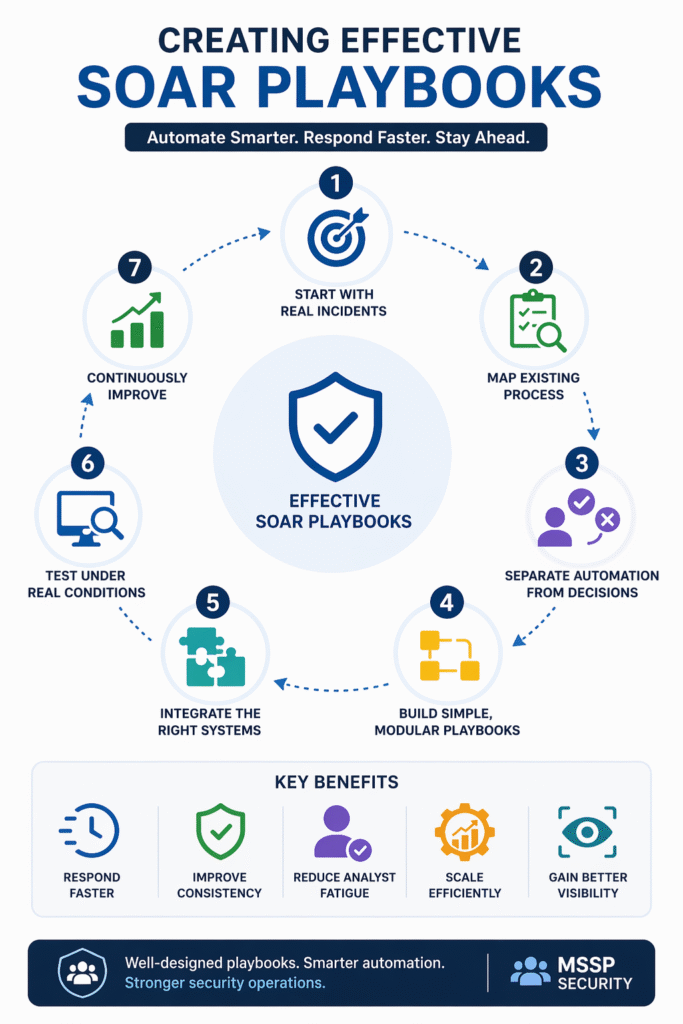
Step-by-Step Guide to Creating Effective SOAR Playbooks
Credits: Rajneesh Gupta
1. Start with Real Incidents, Not Assumptions
One common mistake is designing playbooks based on theoretical scenarios. Looking at real-world security response playbook examples, such as phishing attempts or suspicious logins, is far more effective because these reflect actual operational pressure.
We always begin with actual incidents, phishing attempts, endpoint alerts, or suspicious logins, because these reflect real operational pressure. MSSP Security teams often have broader visibility across environments, which helps identify the most impactful use cases faster.
2. Map the Existing Response Process
Before automation, there must be understanding.
Organizations typically document:
- What analysts do step by step
- Where delays occur
- Which actions are repetitive
From our experience, this stage often reveals inefficiencies that can be fixed even before automation is introduced.
3. Separate Automation from Human Decisions
Not everything should be automated.
Effective playbooks clearly divide:
- Automated actions: enrichment, correlation, notifications
- Human decisions: escalation, containment approval, risk judgment
Within MSSP Security workflows, we intentionally preserve human checkpoints to maintain control and accuracy.
4. Build Simple and Modular Playbooks
Complex playbooks often fail in real environments.
Instead, we design:
- Short, focused workflows
- Reusable modules (e.g., IP checks, file analysis)
- Scalable structures that can evolve over time
Organizations that follow this approach find it easier to maintain and expand their playbooks.
5. Integrate the Right Systems
A playbook is only as effective as the systems it connects.
Typical integrations include:
- SIEM platforms
- Threat intelligence feeds
- Email and endpoint security tools
From the MSSP Security perspective, integration is where much of the value is unlocked, as it allows seamless data flow across tools and reduces manual effort.
6. Test Under Real Conditions
Testing is often underestimated.
We recommend:
- Simulating real attack scenarios
- Testing failure paths and edge cases
- Measuring response improvements
“In practice, theory and practice are the same. In practice, they are not.” – Wikipedia
This reflects what we consistently see, playbooks must prove themselves under pressure.
7. Continuously Improve the Playbooks
Threat landscapes evolve quickly, and playbooks must keep up.
Organizations should track:
- Execution success rates
- False positives
- Analyst feedback
- Response time metrics
From our side in MSSP Security, continuous improvement is part of daily operations, not a periodic task.
Example: Phishing Response Playbook in Practice
Many examples of incident response playbooks follow a specific pattern; for instance, a typical phishing workflow includes alert ingestion, indicator extraction, and threat intelligence enrichment to reduce manual workloads.
- Alert ingestion from email security tools
- Indicator extraction (URLs, attachments, sender data)
- Threat intelligence enrichment
- Sandbox analysis of attachments
- Automatic quarantine of suspicious emails
- Notification to affected users
- Escalation for high-risk cases
We’ve seen this type of playbook reduce manual workload dramatically while improving response consistency across teams.
Common Mistakes to Avoid
Over-Automation
Automating everything can remove necessary human judgment. Balance is key.
Poor Documentation
Even automated workflows need clear explanations for maintenance and onboarding.
Ignoring Analyst Feedback
Playbooks must reflect how teams actually work, not how they are expected to work.
No Iteration Process
Without continuous updates, even the best playbooks become outdated.
Best Practices for Long-Term Success
- Start small and scale gradually
- Collaborate across security and operations teams
- Measure outcomes, not just activity
- Keep workflows transparent
- Use MSSP Security as a strategic extension when internal resources are limited
From both organizational and MSSP Security perspectives, the most successful playbooks are those that evolve continuously and stay aligned with real threats.
FAQ
How do we know which SOAR playbook to build first?
Start with high-frequency incidents like phishing or malware alerts. These provide the quickest return on effort and are easier to standardize.
Can SOAR playbooks fully replace human analysts?
No. They are designed to support analysts, not replace them. Human judgment remains essential for complex decisions.
How does MSSP Security support SOAR playbooks?
MSSP Security helps design, implement, and optimize playbooks based on real-world experience, allowing organizations to scale faster without building everything from scratch.
What is the biggest challenge in SOAR playbook implementation?
The biggest challenge is not technology, it’s aligning playbooks with real workflows and continuously maintaining them as threats evolve.
Turning Automation into Real Impact
Creating effective SOAR playbooks requires more than automation, it demands alignment with real workflows and continuous refinement. From our experience in MSSP Security, success comes from balancing technology with human judgment while scaling operations efficiently.
For teams looking to accelerate results, our consulting approach helps simplify decisions and improve integration. Explore how we support MSSPs in optimizing their security operations.
References
- https://en.wikipedia.org/wiki/Automation
- https://en.wikipedia.org/wiki/Theory
