Examples incident response playbooks help teams understand how to act during real cybersecurity incidents. From our experience working with MSSP Security, we have seen that practical examples reduce confusion and improve response speed. Many organizations know the concept but struggle to apply it under pressure.
By learning from real scenarios, teams can respond more confidently and consistently. These examples turn theory into action and improve coordination across teams. If you want to see how incident response works in practice, keep reading.
Key Insights: Examples of Incident Response Playbooks
Understanding examples of incident response playbooks helps teams move from theory to execution. These insights highlight what truly matters.
- Examples of incident response playbooks improve real-world readiness
- Structured steps reduce delays and errors during incidents
- Different threats require different playbook approaches
Why Examples of Incident Response Playbooks Matter
We have observed that having concrete security response playbook examples makes it easier for teams to apply structured processes. Without these documented scenarios, teams may hesitate or make inconsistent decisions when facing a live threat.
“The goal of incident response is to handle the situation in a way that limits damage and reduces recovery time and costs.” – Wikipedia
Organizations benefit when they use examples because they:
- Improve decision-making under pressure
- Reduce response time
- Strengthen team coordination
- Increase confidence during incidents
From a broader perspective, companies using examples of incident response playbooks tend to respond faster and more effectively.
Common Incident Types in Examples of Incident Response Playbooks
Credits: Open Security Summit
Each threat requires a different focus. Examples of incident response playbooks help clarify priorities across scenarios.
| Incident Type | Primary Focus | Key Action Priority |
| Phishing | User protection | Block and educate users |
| Malware | System security | Isolate infected devices |
| Ransomware | Data recovery | Contain and restore |
| Data Breach | Data safety | Secure and investigate |
| Insider Threat | Access control | Monitor and restrict |
We often use this structure when developing examples of incident response playbooks within MSSP Security environments.
Example 1: Phishing Attack in Incident Response Playbooks
Phishing remains a top entry point for attackers, making a dedicated phishing incident response plan a critical component of any defense strategy. Fast action prevents these initial emails from turning into widespread network compromises.
Typical response includes:
- Detect suspicious email reports
- Analyze sender and links
- Contain by blocking emails
- Eradicate by resetting credentials
- Recover secure access
- Review user awareness
From our experience, combining user training with structured playbooks improves outcomes significantly.
Example 2: Malware Infection in Incident Response Playbooks
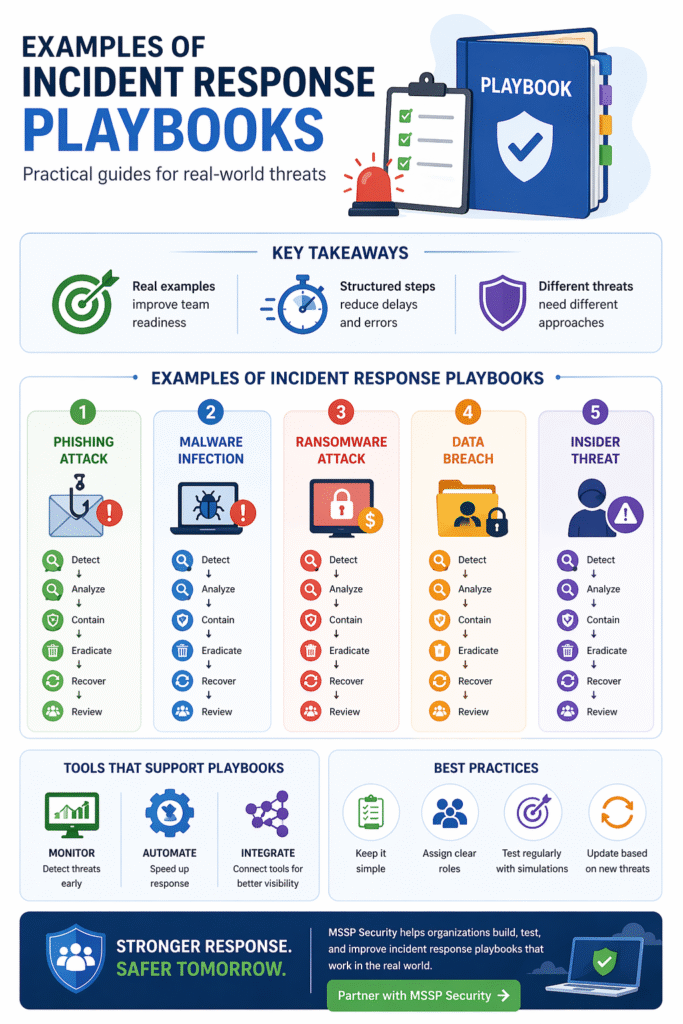
Malware incidents are frequently included in examples of incident response playbooks due to their rapid spread.
“An incident response capability allows an organization to respond to incidents in a systematic manner, ensuring appropriate steps are taken to minimize impact.” – NIST
Response steps usually involve:
- Detect endpoint alerts
- Analyze malware behavior
- Contain by isolating systems
- Eradicate threats and patch systems
- Recover from backups
- Review vulnerabilities
We have seen that early isolation is the most critical step in preventing further damage.
Example 3: Ransomware in Incident Response Playbooks
Ransomware scenarios are essential in examples of incident response playbooks because of their high impact.
Key response actions include:
- Detect encryption activity
- Analyze affected systems
- Contain by disconnecting networks
- Eradicate vulnerabilities
- Recover data from backups
- Review backup strategies
Organizations with tested backups perform much better during these incidents.
Example 4: Data Breach in Incident Response Playbooks
Data breaches are critical scenarios in examples of incident response playbooks, often involving compliance requirements.
Typical process includes:
- Detect unauthorized access
- Analyze compromised data
- Contain by securing systems
- Eradicate attacker access
- Recover operations
- Review and notify stakeholders
We ensure coordination between teams when handling these incidents within MSSP Security workflows.
Example 5: Insider Threat in Incident Response Playbooks
Insider threats are also common in examples of incident response playbooks and require careful handling.
Common response steps include:
- Detect unusual behavior
- Analyze user activity logs
- Contain by limiting access
- Eradicate unauthorized actions
- Recover normal operations
- Review monitoring policies
Strong visibility and monitoring are essential for managing insider risks.
Tools and Best Practices in Examples of Incident Response Playbooks
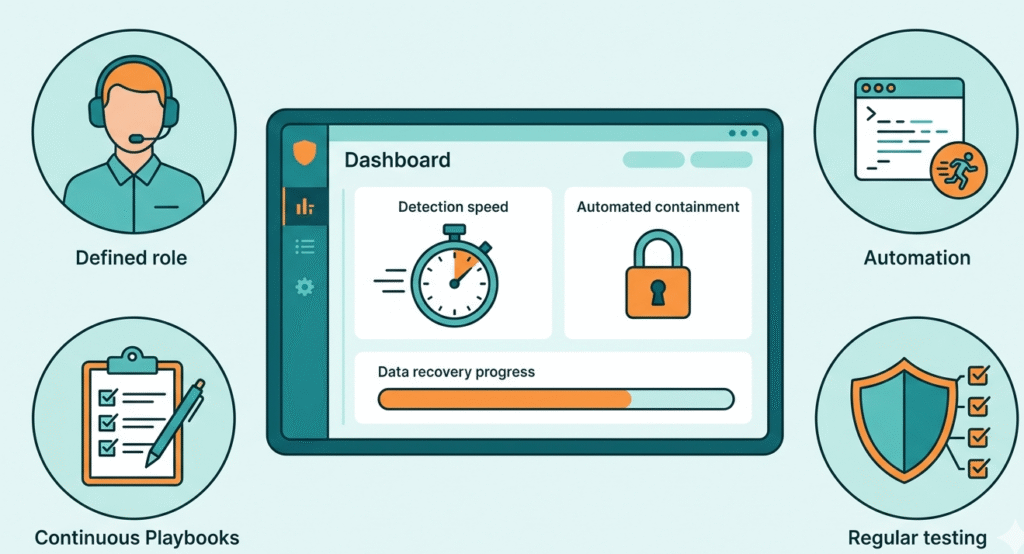
Even the most detailed security response playbook is more effective when supported by modern automation and clear internal practices. From our experience, simplicity in the workflow improves execution when the stakes are high.
Best practices include:
- Using monitoring tools for detection
- Automating repetitive actions
- Assigning clear roles
- Testing playbooks regularly
- Updating based on new threats
Within MSSP Security environments, we prioritize clarity to ensure teams can act quickly under pressure.
FAQ
How do examples of incident response playbooks improve team performance?
Examples of incident response playbooks give teams a clear reference for handling real situations. Instead of guessing what to do, teams can follow proven steps, which reduces hesitation and improves response speed. From our experience, teams trained with real examples perform more consistently and make fewer critical mistakes during incidents.
What should be included in effective examples of incident response playbooks?
Effective examples of incident response playbooks should include clear phases such as detection, analysis, containment, eradication, recovery, and review. They should also define roles, tools, and decision points. We have found that including real scenarios and expected outcomes makes these playbooks easier to follow in practice.
How often should examples of incident response playbooks be updated?
Examples of incident response playbooks should be updated regularly, especially after incidents, system changes, or new threat developments. In our experience, continuous updates ensure that playbooks remain relevant and aligned with current risks, which improves overall response effectiveness.
Can small teams benefit from examples of incident response playbooks?
Yes, small teams can gain significant advantages from examples of incident response playbooks. Even with limited resources, structured examples help reduce confusion, improve coordination, and speed up response. We have seen smaller organizations achieve strong security outcomes by adopting simple but well-defined playbook examples.
Strengthening Security with Examples of Incident Response Playbooks
Examples of incident response playbooks help organizations turn plans into real action during cyber incidents. They improve speed, consistency, and team coordination under pressure. From our experience, teams that continuously refine their playbooks achieve better outcomes and reduce risk.
To build stronger, more effective incident response strategies, working with MSSP Security can help your organization develop and optimize playbooks for real-world success.
References
- https://en.wikipedia.org/wiki/Computer_security_incident_management
- https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-61r2.pdf
