A phishing incident response playbook is one of the most critical tools for modern security teams. We’ve seen how a single phishing email can escalate into credential theft, lateral movement, and full compromise within minutes. Without a clear response process, teams often react too slowly.
This guide breaks down practical steps, real-world workflows, and proven strategies to help you respond faster and reduce risk. If you want a structured way to handle phishing attacks, keep reading.
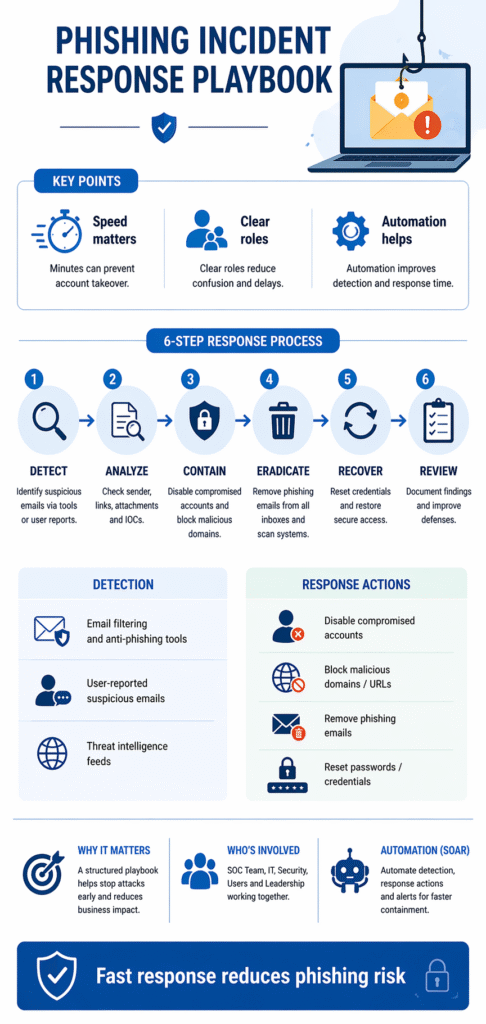
Key Insights: Phishing Incident Response Playbook That Works
A strong phishing incident response playbook ensures teams act quickly and consistently when threats occur.
- Speed is critical, minutes can prevent account takeover
- Clear roles reduce confusion during incidents
- Automation improves detection and response time
What Is a Phishing Incident Response Playbook
A phishing incident response playbook is a structured set of actions designed to detect, analyze, contain, and recover from phishing attacks. It provides clear instructions so teams can act immediately without hesitation.
“Phishing is the fraudulent attempt to obtain sensitive information by disguising oneself as a trustworthy entity in electronic communication.” – Wikipedia
From our experience in MSSP Security, organizations without a defined security response playbook often miss early warning signs. A well-designed playbook includes:
- Detection triggers
- Response workflows
- Escalation paths
- Communication plans
This ensures a consistent and effective response every time.
Phishing Incident Response Playbook Steps
Credits: TECHtalk
A practical phishing incident response playbook should follow a clear sequence of actions:
- Detect the Threat
Identify suspicious emails through user reports or security tools. - Analyze the Email
Check sender details, links, attachments, and indicators of compromise (IOCs). - Contain the Incident
Disable compromised accounts and block malicious domains. - Eradicate the Threat
Remove phishing emails from all inboxes and scan endpoints. - Recover Systems
Reset credentials and restore secure access. - Post-Incident Review
Document findings and improve defenses.
We’ve seen that organizations following these steps can stop attacks before they spread.
Phishing Detection and Analysis Techniques
Early detection is the most important phase in any phishing incident response playbook.
“User awareness and training are critical components in reducing the likelihood and impact of phishing attacks within organizations.” – NIST
- Email filtering and anti-phishing tools
- User-reported suspicious emails
- Threat intelligence feeds
- URL and attachment sandboxing
In MSSP Security operations, combining automated detection with user reporting significantly increases success rates.
Containment and Remediation Actions
| Phase | Action | Owner |
| Containment | Disable compromised accounts | IT/Security |
| Blocking | Block malicious domains/URLs | SOC Team |
| Cleanup | Remove phishing emails | IT Ops |
| Recovery | Reset credentials | Security |
| Validation | Ensure systems are clean | SOC |
Quick containment prevents attackers from gaining deeper access into systems.
Creating Effective SOAR Playbooks for Phishing
Creating effective SOAR playbooks helps automate phishing response actions. Reviewing security response playbook examples helps teams understand how to structure these automated flows.
- Auto-detect phishing indicators
- Trigger account lockout workflows
- Remove emails across organization
- Alert security teams instantly
At MSSP Security, we’ve learned that automation reduces response time dramatically, but human validation is still necessary to avoid false positives.
Testing Incident Response Playbooks
Testing incident response playbooks ensures your phishing playbook works in real scenarios.
- Conduct phishing simulations
- Run tabletop exercises
- Measure response time
- Identify gaps and improve
Organizations that test regularly respond faster and with greater confidence.
Customizing Playbooks Specific Threats
Customizing playbooks specific threats makes phishing response more effective.
- Targeted phishing (spear phishing)
- Business email compromise (BEC)
- Credential harvesting attacks
- Malware-based phishing
We always tailor playbooks based on actual attack patterns seen in MSSP Security environments.
Playbook Driven Incident Response for Phishing
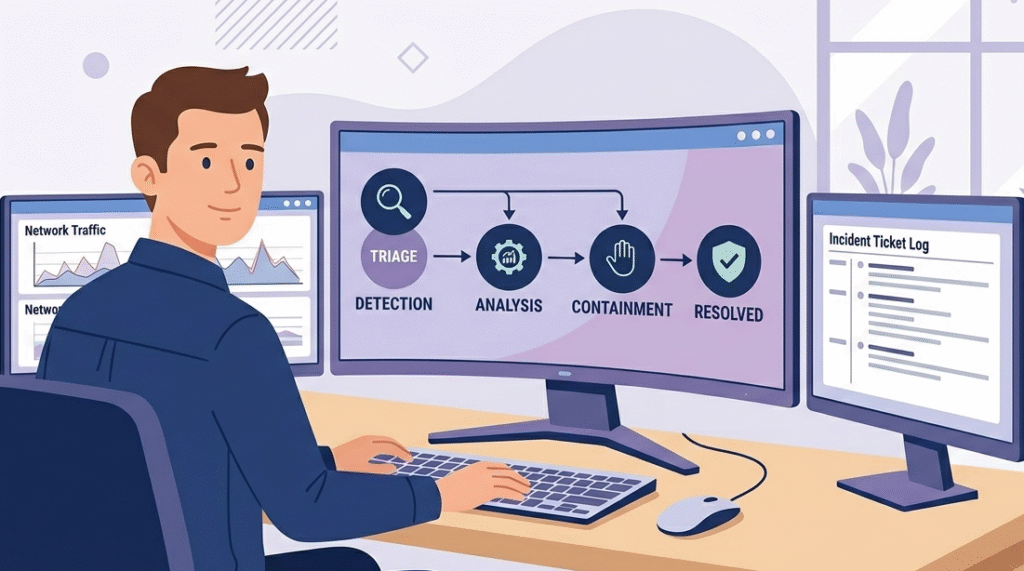
Playbook driven incident response ensures phishing incidents are handled consistently and efficiently. Implementing robust incident response playbooks allows organizations to scale their defenses against sophisticated social engineering.
- Guides analysts step-by-step
- Reduces decision-making delays
- Improves coordination across teams
- Scales security operations
From what we’ve seen, this approach significantly reduces the impact of phishing attacks.
FAQ
How does a phishing incident response playbook integrate with existing security tools like SIEM and EDR?
A phishing incident response playbook integrates with tools such as SIEM and EDR by using them as detection and execution layers. SIEM platforms aggregate alerts (e.g., suspicious email activity), while EDR tools validate endpoint impact.
In a mature setup, SOAR connects these systems to automate actions like isolating endpoints or disabling accounts. From our experience in MSSP Security, tight integration significantly reduces response time and eliminates manual handoffs between teams.
What are the biggest challenges when implementing a phishing incident response playbook?
The most common challenges include lack of clear ownership, over-reliance on manual processes, and poor integration between tools. Many organizations also struggle with keeping playbooks updated as phishing tactics evolve.
We’ve seen that without continuous refinement and testing, even well-designed playbooks become outdated quickly, reducing their effectiveness during real incidents.
How can organizations measure the effectiveness of their phishing incident response playbook?
Effectiveness can be measured using key metrics such as mean time to detect (MTTD), mean time to respond (MTTR), number of incidents contained before escalation, and user reporting rates. Regular simulation exercises also provide insight into team readiness.
In practice, we’ve found that organizations tracking these metrics improve both speed and accuracy over time.
How do you adapt a phishing incident response playbook for advanced attacks like spear phishing or BEC?
Advanced attacks like spear phishing and business email compromise (BEC) require more contextual analysis and stricter verification steps. Playbooks should include executive account monitoring, anomaly detection for email behavior, and multi-level approval for sensitive transactions.
Based on what we’ve handled in MSSP Security environments, adding identity protection controls and communication validation steps is critical for minimizing financial and reputational damage.
Final Thought: Strengthening Security with a Phishing Incident Response Playbook
A phishing incident response playbook is essential for reducing risk and improving speed. By combining structured workflows, automation, and regular testing, organizations can stop attacks before they escalate. Simple playbooks prevent major breaches when applied consistently.
To stay ahead of evolving threats, focus on structured processes and continuous refinement. We offer expert consulting for MSSPs to streamline operations and reduce tool sprawl. Join us to optimize your security stack.
References
- https://en.wikipedia.org/wiki/Phishing
- https://nvlpubs.nist.gov/nistpubs/SpecialPublications/NIST.SP.800-50.pdf
