24/7 SOC monitoring process means continuous security monitoring that detects, analyzes, and responds to threats across networks, endpoints, and cloud systems in real time. Many organizations underestimate how long attackers can stay hidden. Research suggests, breaches can remain unnoticed for more than 200 days when monitoring is weak.
Threats rarely follow business hours. In practice, strong monitoring depends less on tools and more on clear workflows, analyst coordination, and consistent escalation. From our work supporting monitoring environments at MSSP Security, those operational details matter most. Keep reading to see how the process works in real SOC operations.
SOC Monitoring in a Nutshell
The 24/7 SOC monitoring process keeps watch over networks, endpoints, and cloud systems to detect threats quickly and respond before damage spreads.
- 24/7 SOC monitoring means watching for cyber threats non-stop, which cuts down the time it takes to find and stop attacks.
- A good security operations center workflow uses machines to handle simple alerts and skilled people for complex investigations.
- Lots of companies use a managed security provider (MSSP) because running a SOC day and night yourself is very hard and expensive.
What Is 24/7 SOC Monitoring, Really?
Think of 24/7 SOC monitoring as a security guard that never sleeps. It’s a system that constantly watches logs from your computers, networks, and cloud apps, looking for anything strange.
Attacks don’t just happen from nine to five. We see them spike late at night and on weekends. Without all-day coverage, a hacker could be inside your systems for hours before anyone notices.
The security operations center workflow starts by gathering data from everywhere, servers, employee laptops, even your email system. This data flows into a central dashboard. Here, real-time threat visibility lets analysts spot weird patterns, like a computer suddenly talking to a server in another country.
What are they looking at? Usually a few key tools:
- A SIEM dashboard that ties different alerts together.
- EDR tools on every company device.
- Threat intelligence feeds that list known hacker tools.
- Behavior analytics to catch insiders doing something odd.
This isn’t just about stopping hackers. For banks or hospitals, it’s the law. Rules like GDPR and PCI-DSS say you have to watch your logs and be ready to respond to an incident, any time of day.
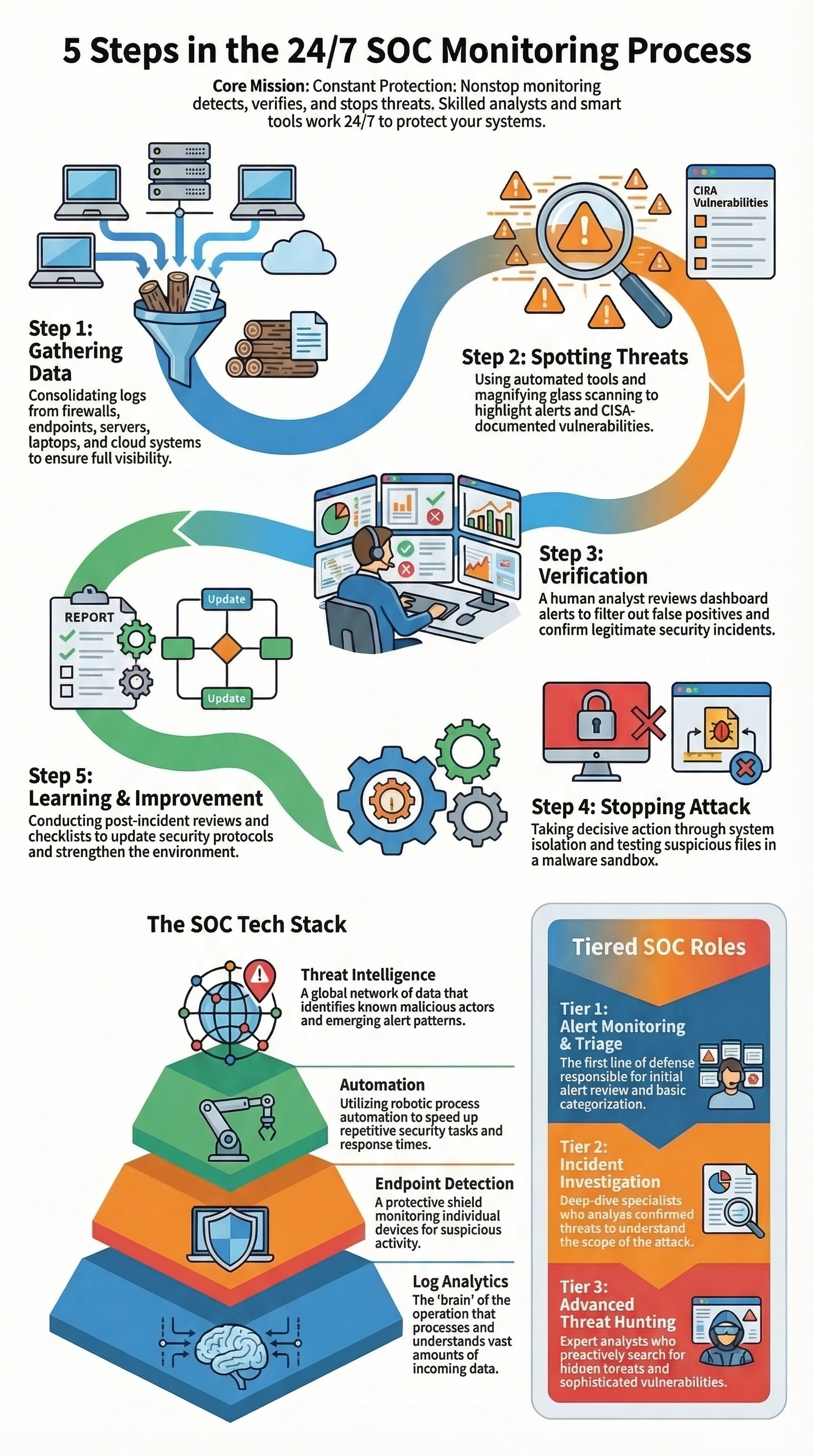
The Step-by-Step Workflow of a SOC
A typical 24/7 SOC monitoring process follows a set path: collect data, spot problems, check if they’re real, then stop the bad guys. It’s built on frameworks like MITRE ATT&CK. Teams that want of how a SOC operates on a daily basis often find that the real work, repeating continuously as new alerts and threats appear.
As noted by TechTarget,
“The SOC process follows a cycle: preparation; detection and analysis; containment, eradication and recovery; and post-incident activity.” – TechTarget
In reality, these systems get millions of signals a day. From our work with MSSPs, we know over 90% of those are just noise, a harmless software update or an employee working late. A clear workflow keeps analysts from drowning in false alarms.
Step 1: Gathering the Data.
First, you pull in logs from every corner of the network. This includes traffic from firewalls, login attempts to cloud apps, and activity on every employee’s computer. We help MSSPs map their clients’ assets, because an alert on the CEO’s laptop is more urgent than one on a test machine.
Step 2: Spotting the Threat.
Detection engines sift through the noise. They look for patterns linked to known attacks, like data theft or lateral movement. A critical tool here is the CISA Known Exploited Vulnerabilities catalog. If an alert is tied to a bug on that list, it jumps to the top of the pile.
Step 3: Checking if It’s Real.
A Tier-1 analyst gets the first look. They might check if a failed login was just a typo or something worse. They’ll compare the alert to threat feeds and see what the user was doing. Most alerts end here, marked as a false alarm.
Step 4: Stopping the Attack.
If the threat is real, it goes to a senior investigator. They dig deeper, maybe running suspicious files in a safe sandbox. Their job is to contain it, often by isolating the infected computer or blocking a malicious website.
Step 5: Learning from It.
After an incident is closed, the team documents everything. They write a report on what happened, how they responded, and what could be done better next time.
This “lessons learned” step is crucial because it feeds improvements into the broader security incident lifecycle in a SOC. The review updates detection rules and refines response playbooks, which makes the next investigation faster and more precise.
The Tools That Make It Possible
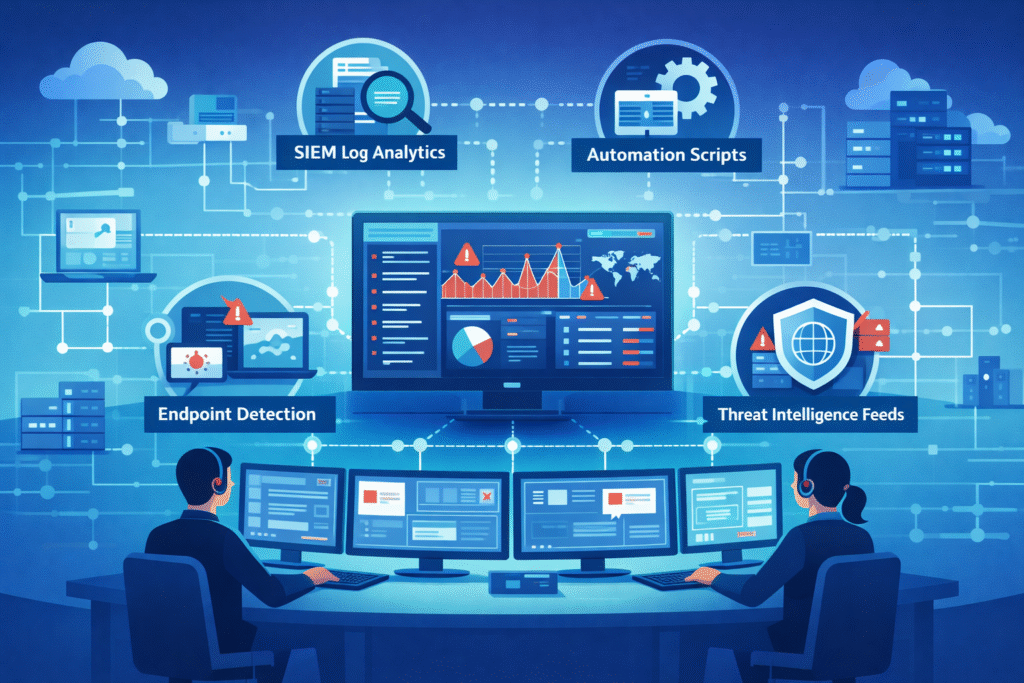
A modern SOC uses a stack of tools that work together. They take in a flood of data and turn it into a few clear alerts for a person to review.
You can break the tech into layers:
- Log Analytics: The brain. It collects and connects events from everywhere.
- Endpoint Detection: The guards on every device, watching for malware.
- Automation: The helper. It does the repetitive tasks, like gathering info about a suspicious IP address.
- Threat Intelligence: The context. It tells you if a detected tool is used by a specific hacker group.
When these tools talk to each other, it’s powerful. An alert from an endpoint can trigger an automated script to check threat feeds and pull related firewall logs. By the time an analyst sees it, they have a full story, not just a blinking light. In a well-run SOC, automation can handle the initial work on most alerts.
The scope keeps growing. It’s not just office computers anymore. Now SOCs are also watching cloud servers, IoT devices like smart cameras, and even industrial SCADA systems. The attacker’s playground got bigger, so the watchtower has to see further.
The People and Shifts Behind the Screens
Credits: SANS Cyber Defense
A SOC runs on people working in shifts. Tier-1 analysts are the front line, Tier-2 handles deeper investigations, and Tier-3 are the expert hunters and forensic specialists.
Data from SANS Institute demonstrates,
“To maintain a 24/7/365 operation, it generally takes a minimum of five to six people to cover one ‘seat’ at all times, accounting for the 168 hours in a week, plus time for hand-offs, training, and leave.” – SANS Institute
Keeping the lights on 24/7 requires careful planning. Teams use on-call rotation schedules and strict shift handover protocols. At the MSSPs we consult for, a messy handoff is a major risk.
| SOC Role | Main Responsibility | Typical Tasks | Skill Focus |
| Tier-1 Analyst | Initial alert monitoring and triage | Review alerts, check login anomalies, escalate incidents | Log analysis, threat identification |
| Tier-2 Investigator | Deep incident investigation | Trace attacker movement, analyze malware, coordinate response | Incident response, forensic analysis |
| Tier-3 Expert | Advanced threat hunting and detection engineering | Build detection rules, investigate sophisticated attacks | Threat hunting, malware reverse engineering |
It’s not just analysts. A full team includes managers, engineers who tune the detection tools, and intelligence researchers. This structure makes sure a serious threat never gets stuck with someone who can’t handle it.
The Real-World Headaches
The biggest challenge in any SOC is alert fatigue. When analysts are bombarded with thousands of mostly false alarms, they get tired. They might miss the one real threat buried in the noise.
We’ve helped MSSPs who were drowning in false positives. Early on, their analysts wasted hours each day closing alerts that turned out to be nothing, a scheduled backup or an employee accessing a personal website. This burns people out fast.
Common problems we see:
- Too many noisy, poorly tuned detection rules.
- Alerts with no context, forcing analysts to hunt for clues.
- Missed handovers between shifts, letting issues fall through the cracks.
- Simple boredom and exhaustion from repetitive work.
The fix is usually a mix of better tech and better habits. Tuning the rules (Sigma rule tuning) cuts the noise. Automation handles the boring data gathering. A clear escalation matrix and a good knowledge base wiki make sure everyone knows what to do.
But you have to care for the people, too. Modern SOCs are thinking about analyst burnout prevention. Things like comfortable chairs, quiet headsets, and cross-training programs to keep the work interesting. A tired analyst is an ineffective one.
How Companies Actually Set This Up
Most organizations don’t build their own 24/7 SOC from scratch. The cost is huge, you need at least a dozen analysts to cover all shifts, plus expensive software. The three main paths are: build it yourself, hire a managed provider, or use a hybrid of both.
Many companies we advise start with the dream of an in-house SOC. They want total control. But they often hit a wall with cost and staffing. Finding enough qualified people willing to work overnight shifts is hard.
Operational realities become clearer when organizations examine what happens inside a real MSSP SOC workflow. Where monitoring, triage, escalation, and investigation run continuously across multiple clients.
A co-managed model is getting popular. The client’s internal team handles high-level strategy and major incidents, while the MSSP’s team does the 24/7 threat monitoring and initial triage. It splits the workload and the cost.
Heavily regulated industries need to prove they’re monitoring. They also use resources like the CISA exploited vulnerabilities list to focus on the most dangerous bugs. Whether you do it yourself or hire help, the goal is the same: find the bad guys before they do real damage.
FAQ
What are the most important SOC analyst duties in a 24/7 SOC monitoring process?
SOC analyst duties focus on monitoring alerts, verifying suspicious activity, and escalating confirmed threats. In a typical 24/7 SOC monitoring process, analysts review SIEM dashboard monitoring alerts, examine EDR endpoint detection activity, and compare events with a threat intelligence feed.
They also document findings, update the ticketing system, and follow the escalation matrix so incidents reach the right investigation tier quickly.
How does the alert triage process work during 24/7 threat monitoring?
The alert triage process helps analysts sort thousands of alerts into a small number that require investigation. During 24/7 threat monitoring, analysts review SIEM dashboard monitoring alerts, compare them with threat intelligence feeds, and check network anomaly detection signals. They verify the context of each alert, remove clear false positives, and escalate confirmed threats for deeper analysis.
Why is a shift handover protocol critical in the security operations center workflow?
A shift handover protocol keeps investigations moving when analysts rotate between shifts. In a security operations center workflow, analysts record incident severity levels, current containment procedures, and unresolved alerts before ending their shift.
This clear documentation allows the next team to continue monitoring without losing context and helps maintain real-time threat visibility during the continuous monitoring cycle.
How do SOC teams reduce false positives without missing real threats?
SOC teams reduce false positives by improving detection rules and adding more context to alerts. Analysts review firewall log analysis results, refine XDR correlation rules, and adjust Sigma rule tuning when alerts trigger too often. They also use UEBA behavioral analytics and vulnerability scan results to confirm suspicious activity before escalation, which helps improve MTTD metrics over time.
What happens after an incident response playbook is triggered in a SOC?
After an incident response playbook is triggered, analysts follow structured steps to control and remove the threat. The team applies containment procedures, performs eradication steps, and verifies system recovery.
Analysts may isolate compromised devices, block indicators with IOC blocking rules, and investigate lateral movement hunting activity. When the incident ends, the team conducts a post-incident review and records findings in an AAR after action report.
The Reality of Running a 24/7 SOC
Running a 24/7 SOC sounds simple until alerts keep piling up and your team is staring at dashboards late at night, trying to decide what matters. Tools help, but they don’t fix the pressure. Without clear workflows and steady review, analysts end up reacting instead of responding.
If you’re looking to simplify operations and strengthen detection, see how your team can streamline SOC operations with our MSSP support solutions and build a process that actually works every day.
References
- https://www.techtarget.com/searchsecurity/definition/Security-Operations-Center-SOC
- https://www.sans.org/white-papers/39975/

