You’re staring at a dashboard blinking with a thousand identical red warnings. Which one is the real fire? Traditional alerting doesn’t know. It treats a vulnerability on a public database the same as one on a developer’s test machine. The result is a deluge of noise that buries critical threats and burns out your team.
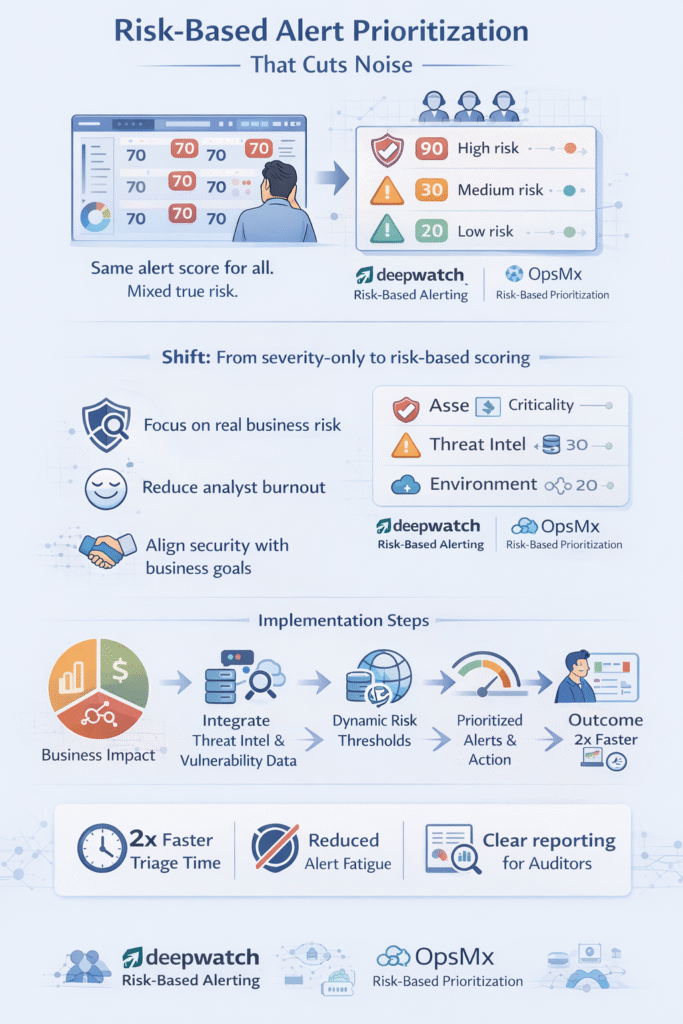
Risk-based alert prioritization changes that. It’s the shift from reacting to every ping to responding to what truly threatens your business. It answers the only question that matters: “So what?” We’ve seen teams cut their triage time in half by making this move. Keep reading to learn how you can stop fighting the tide and start directing it and learn risk based alert prioritization.
What You’ll Gain from Risk-Based Prioritization
- Focus on Critical Threats: Your team will spend time on alerts that could actually cause a data breach or downtime, not theoretical risks.
- Reduce Analyst Burnout: Automatically filtering out low-risk noise gives your SOC room to breathe, think, and hunt.
- Align Security with Business: You’ll demonstrate security’s value in terms of protecting revenue and reputation, not just closing tickets.
The Flaw in the Old Way of Thinking
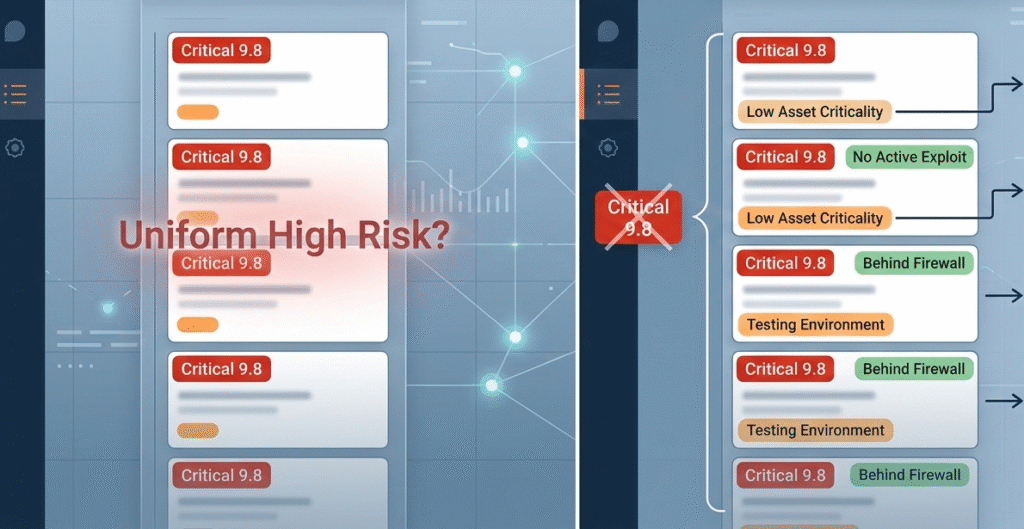
We’ve seen the dashboard scream. A hundred alerts, each scored a critical 9.8. Teams scramble, patch furiously all weekend. Later, they learn most were on retired servers. The one medium-severity alert on the live payment system, lost in the shuffle, got exploited on Tuesday.
This is the failure of severity-only scoring. CVSS gives a technical number, but it doesn’t know your business. A 10/10 flaw in a sandbox isn’t a 10/10 risk to your company. Treating it like one creates a strategic backlog.
With teams only able to fix a fraction of findings each month, they choose poorly, chasing the loudest alarm, not the most dangerous one.
- Severity is not risk.
- Volume is not urgency.
- A patched test server doesn’t prevent a breach.
The old model creates an illusion of security. You’re busy patching, but are you safer? It’s like fixing every shingle on the shed while the house door hangs open. Analysts glaze over. Real threats slip through because they look like yesterday’s false positives. You need context.
Building Your Risk Calculation: The Core Factors
Credits: DefectDojo
Most teams start with CVSS Base scores from the Common Vulnerability Scoring System. We’ve seen how that creates alert fatigue fast. A 9.8 score looks scary, but without context, it’s just noise. Real Risk-based prioritization begins with asset criticality.
“Risk-Based Alerting (RBA) represents a paradigm shift in cybersecurity operations by introducing context-aware, dynamic risk scoring, helping SOC teams prioritize threats more effectively.” – Deepwatch
What would actually hurt the business? In our consulting work with MSSPs, we push for a clean asset inventory first, cloud assets, SaaS tools, code repositories, even MIoT devices.
Threat intelligence and the Threat Landscape matter just as much. If threat actors actively exploit a flaw listed in Common Vulnerabilities and Exposures, that changes risk levels overnight. We combine Exploit Prediction Scoring System data with vulnerability management insights to guide Risk-based vulnerability prioritization.
Environmental context closes the loop. Exposure across cloud environments, weak security controls, or internet-facing Public Facing VMs reshape the risk assessment. That’s risk-based security in practice.
| Factor | What It Answers | Source Example |
| Business Impact | “How much would an exploit cost us?” | Asset Inventory, Compliance Data |
| Threat Likelihood | “Is someone actually trying to hack this?” | EPSS, Threat Intel Feeds |
| Environmental Context | “How hard is it to reach this asset?” | Network Maps, Control Logs |
From Theory to Practice: Implementing in Your SOC
On paper, risk scoring sounds clean. In real security operations, alerts pile up before lunch. We help MSSPs translate Risk-based vulnerability management into a streamlined alert triage prioritization process that security operations centers can actually run.
It starts with asset discovery and asset classification. Without that, vulnerability scanner results are guesswork. We integrate threat intelligence, vulnerability assessment data, and cloud security tools into one security ecosystem. Risk thresholds then adjust dynamically as patch management progresses or new zero-day responses emerge.
Automation helps, but we never treat it as autopilot. Whether using agentless scanning in cloud-native technologies or tuning managed detection and response workflows, human review stays central.
Over time, automated prioritization improves Mean Time to Detect and Mean Time to Respond, while reducing unnecessary vulnerability response cycles and wasted resource allocation.
The Tangible Payoff for Your Team
Once Risk-based vulnerability prioritization takes hold, the change feels immediate. Analysts stop chasing low-impact software vulnerabilities and focus on security risks that threaten business continuity. We’ve watched MSSPs succeed at reducing alert fatigue dramatically just by aligning risk scoring with business criticality.
“By identifying and addressing the most critical vulnerabilities first, teams can dramatically reduce the attack surface before hackers have the chance to exploit it… It’s about working smarter, not harder, and ensuring that your security efforts are directed where they will have the greatest impact.” – OpsMx Blog
Security leaders start seeing clearer reporting. Instead of listing hundreds of security flaws from a vulnerability catalog, teams show which attack vectors across the attack surface were neutralized. Visualized reporting tied to frameworks like MITRE ATT&CK or the NIST Risk Management Framework makes conversations with ISO 27001 auditors easier.
Operationally, alert prioritization improves developer efficiency and reduces talent shortage pressure. Risk analytics grounded in FAIR Institute thinking shift the focus from volume to impact. The security posture strengthens because the work finally matches the real risk.
Navigating the Common Pitfalls
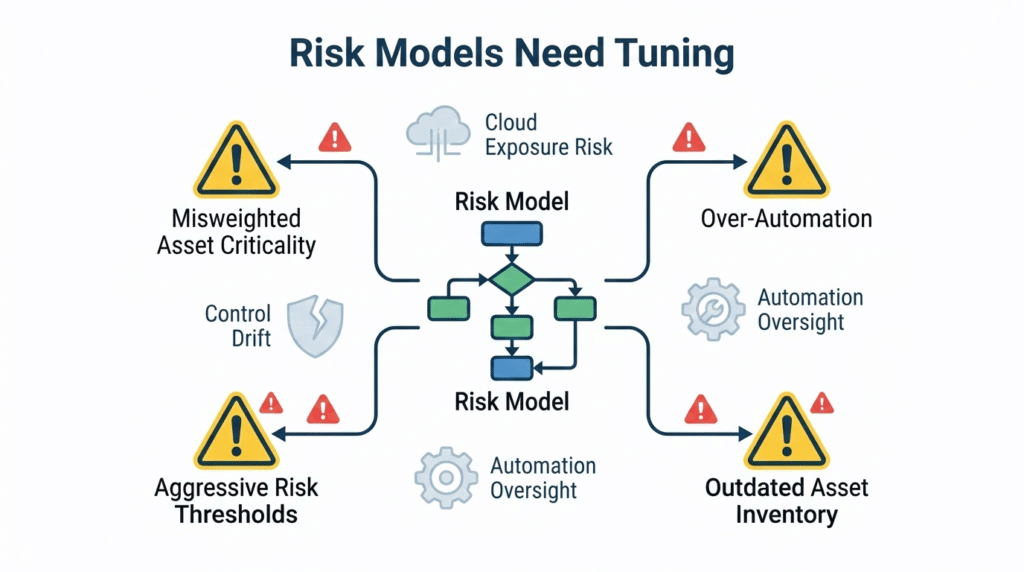
We’ve audited enough risk-based security programs to know where they break. One common mistake is misjudging asset criticality. If application architecture or container images are tagged incorrectly, the prioritization matrix skews everything. That leads to weak vulnerability prioritization and missed unauthorized access risks.
Another issue is ignoring configuration drift in cloud environments or OT security setups like Industrial control system networks. Cloud assets, IoT Security, and Medical IoT expand the attack surface fast. Without ongoing vulnerability management and clear patching cycles, risk levels quietly rise.
Automation platforms and AI automation tools help, but blind trust creates gaps. Risk thresholds must be reviewed regularly. Strong governance, continuous vulnerability assessment, and security alert validation techniques within a Zero-Trust architecture mindset keep risk-based security grounded in reality.
FAQ
How is risk based alert prioritization different from CVSS scoring?
Risk based alert prioritization goes beyond CVSS Base scores from the Common Vulnerability Scoring System. CVSS shows severity, but not business criticality or exploit reachability.
A proper risk assessment adds asset criticality, threat intelligence, and Exploit Prediction Scoring System data. This creates real risk scoring tied to your security posture, not just generic severity ratings.
How does risk based alert prioritization reduce alert fatigue?
Risk based prioritization filters alerts using risk levels instead of raw volume. By aligning vulnerability management, vulnerability prioritization, and alert prioritization with asset inventory and attack surface exposure, security operations centers focus on genuine security risks.
This reduces alert fatigue, improves resource allocation, and helps teams respond faster to high-impact security challenges.
What data sources improve risk scoring accuracy?
Accurate risk scoring combines vulnerability scanner results, threat intelligence, and insights from the Threat Landscape. It should include Common Vulnerabilities and Exposures data, vulnerability threat signatures, and MITRE ATT&CK mapping.
Adding asset classification, cloud assets visibility, and exploit reachability analysis provides holistic context for better Risk-based vulnerability prioritization.
How does this approach support compliance and leadership reporting?
A risk-based security program helps security leaders align with ISO 27001 and the NIST Risk Management Framework. Instead of listing software vulnerabilities, teams show how they reduced security risks that threaten business continuity.
Visualized reporting, risk analytics, and structured vulnerability response demonstrate measurable improvement to executives and auditors.
Making Risk-Based Prioritization Your Reality
Building a risk-based practice requires a pragmatic mindset. Start with a simple audit of your last major incident. Would your system have flagged it? If not, begin there. Layer in context like asset tags to a single data stream, then build your logic gradually.
This approach respects your team’s time and your business’s unique needs, shifting from frantic reaction to calculated response. You stop chasing every blinking light and start seeing the real path to your door.
The next step? Choose one critical asset group and apply this lens tomorrow. If you’re ready to operationalize this and optimize your MSSP stack for real risk, our team can help. Schedule a consultation to get started.
References
- https://www.deepwatch.com/glossary/risk-based-alerting-rba/
- https://www.opsmx.com/blog/risk-based-prioritization-a-proactive-approach-to-application-security/
