The noise is drowning out the signal. You’re not just getting security alerts; you’re getting buried by them. Alert validation is the systematic process of verifying which of those pings are genuine threats and which are just digital ghosts. It’s the difference between a team chasing every shadow and one that acts decisively on real danger.
Without it, your best people burn out on false positives, and real attacks slip through the noise. We’ve seen it happen, and the fix isn’t more tools, it’s a smarter process. Keep reading to learn security alert validation techniques that cut burnout.
Principles That Cut Burnout
- Context is everything. A raw alert is just data; enriching it with user behavior and threat intelligence reveals the real story.
- Automation handles the routine. Let machines correlate logs and run simulations, freeing your team to investigate complex breaches.
- Continuous tuning is non-negotiable. Your environment changes, and so must your detection rules to prevent control drift.
Why Your Team is Drowning in False Alerts
The console lights up with another critical alert. It’s just a developer testing a script. This happens hundreds of times a day. The problem isn’t the alert, it’s the total lack of context. Most tools are designed to be overly sensitive, catching everything in a wide net, including normal activity.
“The key to eliminating scan noise is proof-based validation, confirming which vulnerabilities are truly exploitable before escalation… When a scan detects a potential weakness, the system automatically replays the exploit in the live client environment to verify real-world impact.” – Indusface Blog
This creates a cascade of problems. Analysts can spend over half their day verifying false alarms, draining productivity and morale. It leads to alert fatigue, where teams start ignoring warnings. A real attack gets lost in the noise. Security weakens because the signal is buried.
We see the same primary noise sources repeatedly:
- Automated system tasks
- Authorized user behavior that looks odd
- Overly broad detection rules
The financial cost is steep. Budget is wasted on non-issues instead of real threats.
We’ve worked with teams buried under thousands of daily alerts. The turning point is always the same: they stop trying to catch everything and start focusing on catching the right things. That shift starts with validation.
Core Techniques: From Noise to Knowledge
Credits: Silva Kumar
You need a clear method. Good validation checks every alert from several angles, establishing a robust alert triage prioritization process that functions like a detective building a case.
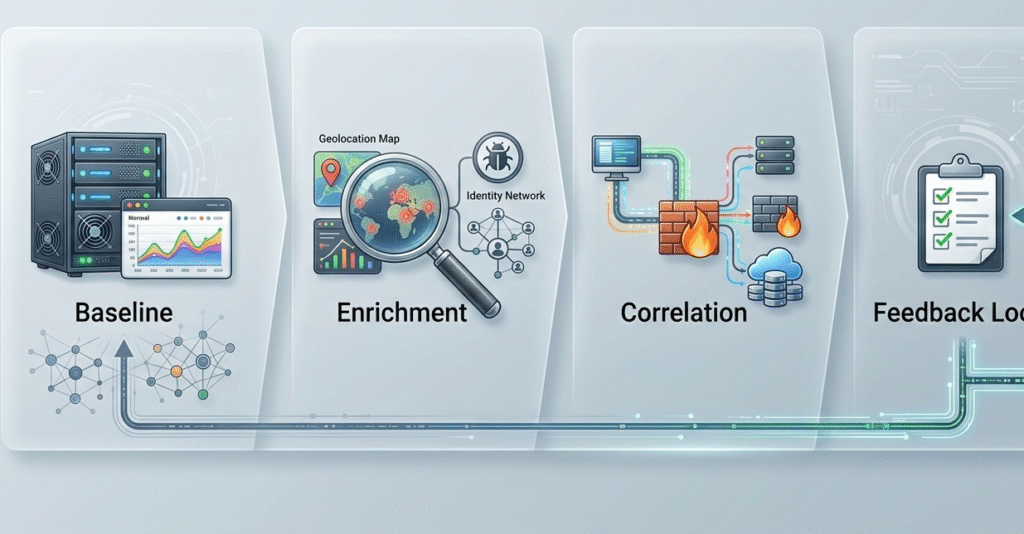
Start with baselining. Know what “normal” is for your own network. How many failed logins are typical? What does traffic look like overnight? Setting thresholds based on your reality, not a vendor’s guess, stops many false alerts.
Next, add context. An alert alone means little. Pull in threat intelligence: is this IP on a blocklist? Check the user’s role: is this activity normal for them? This turns a generic “failed login” into something specific and actionable.
Finally, correlate logs. Understanding how security alerts are prioritized across different layers is key. If your network logs show that data was immediately sent to an external server following a suspicious download, you have a real incident. Connecting events across your SIEM, firewalls, and identity tools reveals the full story a single alert can’t tell.
| Validation Technique | What It Does | The Outcome |
| Contextual Enrichment | Adds threat intel, user identity, and asset value to the raw alert. | Transforms a generic event into a risk-assessed incident. |
| Log Correlation | Searches for related events across different security tools and systems. | Confirms a broader attack pattern, separating targeted attacks from isolated noise. |
| Threshold Tuning | Adjusts detection rules based on your environment’s unique “normal” baseline. | Dramatically reduces repetitive false alarms from routine business activity. |
How Automation Transforms the Workflow
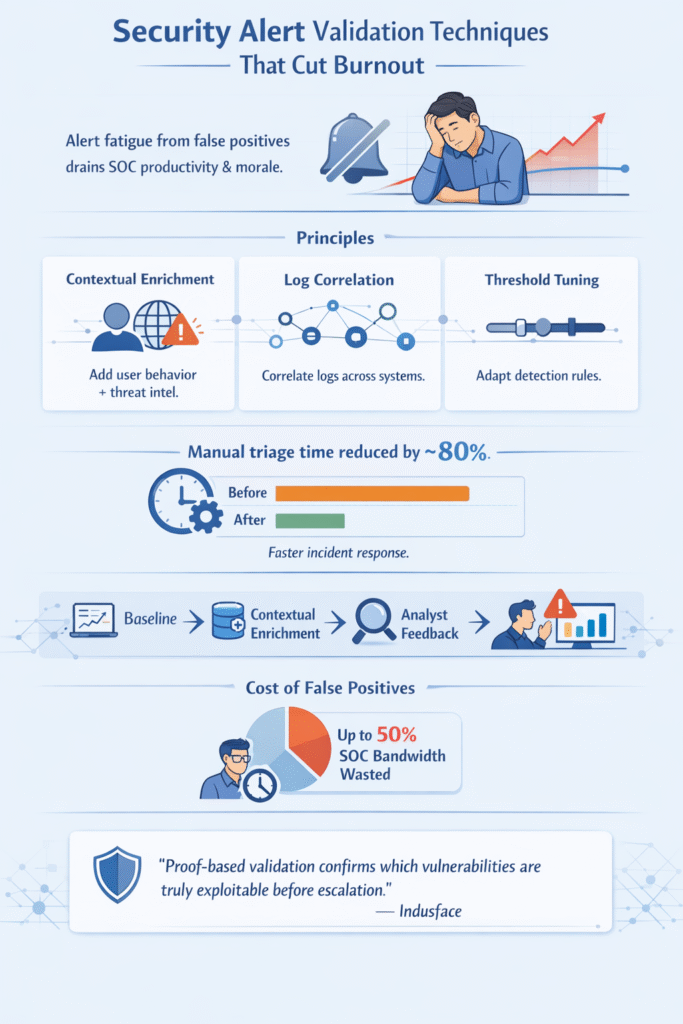
Manual validation is slow and doesn’t scale. Automation becomes a force multiplier for reducing alert fatigue SOC teams often endure. It handles the initial, repetitive checks on every alert, around the clock.
“Knowledge of the threat environment is necessary to know which log sources to attach to your siem alerts. With the right log sources attached, we can validate that the alert is an actual threat and not a false positive. Logs add data context to alerts… Besides log sources, we can improve siem alert validation with technology that leverages AI/ML personalized to the unique threat environment.” – Seculyze
Consider breach and attack simulation (BAS). Instead of waiting for an alert, these tools proactively mimic real attacks. They test your controls and show you which vulnerabilities are actually exploitable. It’s a continuous health check for your defenses.
Then there are automated playbooks. When a specific alert fires, the system can run a validation workflow automatically: isolate the endpoint, pull the suspicious file for analysis, check the process against threat feeds. By the time an analyst sees it, the alert arrives with a verdict and evidence. We’ve seen this cut manual triage time by over 80%.
This automation also enables continuous validation. It constantly checks if your security controls are performing as intended, catching configuration drift in real-time. This provides the proof of effectiveness that leadership needs, turning security ops from a cost center into a clear value protector.
Building Your Validation Framework: A Phased Approach
Trying to fix everything at once leads straight to burnout. A structured, phased rollout is the only practical path forward.
Start with your crown jewels, the systems that would cause the most damage if compromised. Focus your initial validation efforts there. This delivers quick, visible wins and builds team confidence.
- Phase One: Review and Baseline
Document what normal activity looks like for those critical assets. Tune their detection rules specifically to eliminate obvious false positives, like allow-listing expected admin traffic. - Phase Two: Cross-Validation
Implement automated enrichment and correlation for alerts on these systems. A simple playbook can pull threat intelligence and check related logs, starting to build a “case file” for each alert. - Phase Three: Classification and Feedback
Every alert disposition gets fed back into the system. This analyst feedback trains models and informs tuning, creating a self-improving loop that learns your environment. - Phase Four: Escalation and Measurement
Automated workflows ensure a fast response to true positives. Now you measure what matters: false positive rate, mean time to validate, mean time to respond. You’re running a program, not just fighting fires.
FAQ
How do security alert validation techniques strengthen security controls?
Security alert validation techniques test whether your security controls actually stop real-world threats. Instead of trusting default settings, security teams validate detection between security stack layers and confirm security control effectiveness. This improves security posture and gives evidence of security effectiveness.
Over time, validation highlights gaps in security controls implementations and supports smarter security investments and budget allocation.
How does Continuous security validation reduce exposure to cyber threats?
Continuous security validation checks your defenses against active threats across the entire attack surface. It uses automated testing, attack simulation techniques, and breach and attack simulation to mirror adversary tactics.
This helps security teams see real attack paths, reduce configuration drift, and respond to emergent threats before damage spreads across critical systems or cloud resources.
Why align validation with the MITRE ATT&CK framework?
Mapping validation to the MITRE ATT&CK framework ensures your testing reflects real attack techniques used in today’s threat landscape. It helps teams analyze the entire attack chain, including identity attack paths and multi-stage attacks.
By aligning with known adversary tactics, security validation becomes structured, measurable, and tied directly to real-world emulated attacks.
What role does threat intelligence play in validation?
Integration of threat intelligence adds context to security alerts and attack simulations. Threat intelligence helps teams prioritize genuine threats based on industry-specific attack trends and active attack scenarios.
When combined with vulnerability scanning and automated real-world attacks in a controlled environment, it improves security control performance and sharpens insight into security control gaps.
The Final Verification
Security alert validation turns data into decisions. It moves you from being overwhelmed by sirens to focusing on verified threats. The method isn’t magic, it’s enrichment, correlation, automation, and tuning. It’s about working smarter with what you already have.
The result is a quieter console and a team with regained focus. It proves your security investments work and provides confidence you’re chasing real adversaries. Start by validating alerts on your most important system.
For expert help building this capability, our consulting provides vendor-neutral product selection, auditing, and stack optimization. Start with a clearer strategy.
References
- https://www.indusface.com/blog/mssp-false-positive-mitigation/
- https://seculyze.com/learning-hub/increase-the-quality-of-siem-alerts/
