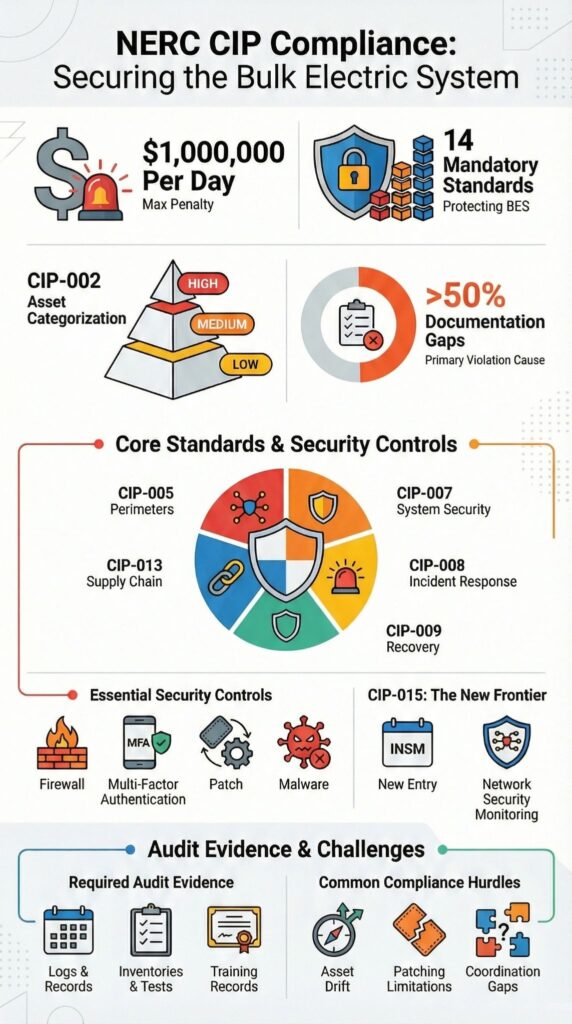
NERC CIP sets mandatory cybersecurity controls for protecting the Bulk Electric System across North America, with enforcement authority backed by penalties of up to $1 million per day per violation. These requirements directly affect how OT networks, SCADA systems, and field assets are built, secured, and restored after incidents.
In day-to-day utility operations, CIP obligations influence access control, system design, monitoring practices, and recovery planning. Understanding who must comply and what the standards actually demand is essential for running secure operations without slowing the business. Keep reading to see how NERC CIP works in practice.
Key Takeaways
- NERC CIP establishes enforceable OT security requirements for BES Cyber Systems, not optional guidance.
- Asset categorization under CIP-002 drives nearly every downstream technical and procedural control.
- Strong compliance programs integrate monitoring, documentation, and recovery testing into daily operations.
What are NERC CIP compliance requirements?
NERC CIP defines 14 enforceable cybersecurity standards that protect the Bulk Electric System across North America. MSSPs integrate operational technology OT security monitoring to ensure OT networks, SCADA, and BES cyber systems remain compliant without disrupting operations.
Day to day, compliance cuts across policy, technology, and people. Organizations must document governance, restrict access to Electronic Security Perimeters (ESPs), monitor activity, and prove they can recover from cyber incidents. Enforcement flows from FERC through NERC and the Regional Entities, using audits and spot checks.
Where we see problems is rarely tooling. During product audits and assessments, gaps usually come from unclear asset scope, weak evidence, or inconsistent execution between IT and OT teams.
Key characteristics of NERC CIP requirements include:
- Asset identification and impact categorization
- Prescriptive controls for BES Cyber Systems
- Continuous audits and self-certifications
Understanding how these requirements work in practice makes compliance achievable without slowing operations.
Who is required to comply with NERC CIP?

Owners and operators of BES assets classified as high, medium, or low impact must comply with NERC CIP. MSSPs often leverage choosing an OT security monitoring provider in California to ensure local OT expertise aligns with regulatory and operational requirements.
That includes generation owners, transmission operators, balancing authorities, and reliability coordinators. Which CIP requirements apply depends on asset impact ratings defined under CIP-002. We regularly help MSSPs validate how those ratings affect tooling choices and audit readiness.
Impact level matters, but none are exempt. High impact assets carry the most restrictive controls. Medium impact systems require strong technical and monitoring measures.
Low impact assets still demand documented policies, access controls, training records, and incident response plans. We often see audit findings where teams assumed “low impact” meant minimal effort.
Entities typically subject to CIP include:
- Transmission substations above defined voltage thresholds
- Control centers supporting BES operations
- Backup control facilities and supporting data centers
NERC maintains the registry and audit schedule, while Regional Entities handle enforcement on its behalf, as outlined by NERC. From our assessments, clarity on scope early on prevents costly rework later.
What are the core NERC CIP standards (CIP-002–CIP-014)?
Fourteen NERC CIP standards define how BES assets are identified, protected, monitored, and restored after a cyber event. In our assessments for MSSPs, weaknesses in these two almost always surface first and often explain downstream findings.
“Vulnerability management is mapped to NERC CIP-007 and NERC CIP-010. NERC CIP-007 provides guidelines on managing security updates, including evaluating every 35 calendar days security updates applicable to assets in the OT environment. NERC CIP-010 provides guidelines on securely handling system configurations, avoiding exposing systems to attacks.” – Semantic Scholar / ECCWS 2023 [1]
Below is a high-level overview of commonly enforced standards:
| Standard | Focus area | Primary requirement |
| CIP-002 | Asset categorization | Impact-based BES Cyber System inventory |
| CIP-005 | Electronic Security Perimeters | Controlled electronic access points |
| CIP-007 | System security | Patch management, malware prevention, logging |
From what we see during product audits, coordination between standards is where compliance breaks down most often:
- CIP-010 depends on accurate inventories defined under CIP-002
- CIP-008 reporting timelines rely on logging required by CIP-007
- CIP-013 vendor reviews often lack evidence tied back to system impact
A control that satisfies one standard but fails to support another usually creates more audit risk, not less.
How are BES Cyber Systems identified and categorized?
CIP-002 requires organizations to classify BES Cyber Systems as high, medium, or low impact based on potential effect on grid reliability. MSSPs often rely on advanced specialized services to validate asset categorization, maintain audit readiness, and implement controls that satisfy CIP requirements without operational disruption.
When categorization works, it follows a disciplined and repeatable process aligned with NERC risk criteria. Teams that succeed treat it as an engineering exercise, not a paperwork task. In audits we support, the strongest programs are consistent year over year and easy to explain.
The typical process includes:
- Identifying BES functions and the cyber assets that support them
- Mapping those assets into defined BES Cyber Systems
- Assigning impact ratings using NERC’s published criteria
- Documenting assumptions, exclusions, and boundary decisions
Auditors expect traceability at every step. Each inclusion or exclusion must be backed by diagrams, written rationale, and change records. In many NERC findings we review, the issue is not missing security tools, it is missing justification.
What technical security controls are required by NERC CIP?
Unlike enterprise IT, CIP controls must account for availability, legacy firmware, and operational limits of industrial control systems. In our product reviews for MSSPs, we evaluate whether a control can function without disrupting operations. A technically correct control that causes outages will not survive either an audit or production use.
“As utilities have upgraded ICS and electric grid technology to meet present-day needs, the practicality of digital automation and data transfer has become necessary. A variety of vulnerabilities have emerged, particularly related to greater accessibility as a result of advanced communication means and Internet connectivity.” – U.S. Department of Energy [2]
Common mandated controls include:
- Electronic Security Perimeters with documented access points
- Multi-factor authentication for interactive remote access
- Malware prevention tailored to BES and OT systems
- Patch management with compensating controls when patches are not available
We often recommend internal network security monitoring to support CIP-015 monitoring expectations. This gives teams better event correlation, forensic readiness, and faster response without adding operational risk. When MSSPs support these environments, the goal is balance. Controls must satisfy auditors while remaining invisible to operators.
What are NERC CIP audit and evidence requirements?
Credits: Dragos: OT Cybersecurity
NERC CIP audits are driven by evidence. Entities must retain documented proof for each applicable requirement, often covering 12 to 36 months, to satisfy audits and spot checks. In our experience supporting MSSPs during assessments, teams that understand this early avoid last-minute scrambles.
Evidence spans both technical and procedural areas. Logs, access records, training attestations, vulnerability assessments, and recovery testing results all come into play. When we audit tools for MSSPs, we focus on whether those tools can produce usable, time-aligned evidence, not just alerts or dashboards.
Common evidence categories include:
- Cyber asset inventories and network diagrams
- Baseline configurations and documented change records
- Incident response exercises and test results
- Physical access control logs
Strong programs centralize documentation and automate retention wherever possible. Weak programs rely on manual collection and memory. According to NERC, documentation gaps remain one of the most frequent causes of violations, a pattern we continue to see in audits.
What penalties apply for NERC CIP non-compliance?
NERC CIP non-compliance can result in fines of up to $1 million per day per violation, enforced by FERC through NERC oversight. In practice, the headline number matters less than how violations accumulate. When we review enforcement cases with MSSPs, penalties usually grow because issues linger undetected or unresolved.
How penalties escalate depends on both risk and duration. A single control failure can multiply into several violations if it spans reporting periods or applies across multiple BES Cyber Systems. We often see this happen after routine changes that were never reassessed against CIP scope or evidence requirements.
Beyond direct fines, enforcement brings additional consequences:
- Mandatory mitigation and corrective action plans
- Increased audit frequency and follow-up reviews
- Public enforcement notices for regulated utilities
In cases we have examined firsthand, penalties were rarely driven by complex attacks. They were more often tied to incomplete documentation, unmanaged change, or assumptions that small gaps would go unnoticed. For MSSPs supporting these environments, preventing those gaps is usually far more effective than reacting after enforcement begins.
FAQ
What does NERC CIP compliance require for OT security in the bulk electric system?
NERC CIP compliance sets mandatory OT security requirements to protect the bulk electric system. It covers critical infrastructure protection, BES cyber systems identification, asset categorization, and grid security standards.
Organizations must secure industrial control systems, SCADA cybersecurity, electronic security perimeters, and physical security perimeters. Compliance also requires regular cybersecurity audits and controls to prevent violations and reduce the risk of NERC penalties.
How are BES cyber systems categorized under CIP-002 standards?
CIP-002 standards require organizations to categorize BES cyber systems based on their impact.
Assets are classified as high impact, medium impact, or low impact. This categorization determines the level of OT security controls required, including cyber asset inventory, temporary asset identification, and documentation. Proper categorization ensures alignment with bulk electric system cybersecurity requirements and minimizes the risk of compliance violations.
What controls are required for electronic and physical security perimeters?
Electronic security perimeters must include ESP controls such as OT network segmentation, firewall configurations, access control lists, and interactive remote access protections.
Physical security perimeters require PSP access controls, badge systems, video surveillance, and perimeter fencing. These measures protect industrial control systems, prevent unauthorized access, and ensure compliance with CIP-005 electronic access and CIP-014 physical security standards.
How do incident response and recovery plans support NERC CIP compliance?
CIP-008 incident response and CIP-009 recovery plans require clearly defined incident reporting timelines, recovery plan testing, and forensics readiness.
Organizations must implement malware prevention, backup strategies, disaster recovery, and business continuity planning. These plans reduce operational impact during incidents, satisfy NERC regulatory enforcement requirements, and support successful outcomes during cybersecurity audits.
How can organizations prepare for cybersecurity audits and regulatory enforcement?
Organizations must maintain audit evidence, compliance program documentation, and change management controls. Internal network security monitoring, logging and monitoring, and CIP-015 monitoring help maintain continuous visibility.
Regular vulnerability assessments, patch management for OT, personnel risk assessments, and security awareness training strengthen defenses and ensure compliance. These measures reduce the risk of NERC penalties and address FERC oversight requirements.
NERC CIP Compliance Requirements in Practice
NERC CIP compliance is an operational discipline, not a yearly checklist. Organizations that build controls into daily OT operations adapt faster and face fewer audit surprises. In our work with MSSPs, we see better outcomes when security supports operators first and compliance follows as a result.
As grid technology and standards evolve, staying aligned requires consistent evidence and realistic design. To assess readiness and simplify your stack, schedule a NERC CIP readiness conversation with MSSP Security.
References
- https://pdfs.semanticscholar.org/0874/72829181dd52c98dd52e57f587978064cbc2.pdf
- https://www.energy.gov/sites/prod/files/2017/01/f34/Cyber%20Threat%20and%20Vulnerability%20Analysis%20of%20the%20U.S.%20Electric%20Sector.pdf
