Bridging the IT OT security gap means aligning your company’s cybersecurity with the factory floor so digital threats can’t stop physical processes. This problem became clear after the 2021 Colonial Pipeline attack halted fuel delivery.
As IT and OT networks merge, the risk grows due to old equipment, safety rules, and a shortage of skilled people. We’ve helped industrial clients manage this convergence while keeping systems online.
This article explains the root of the gap, why it’s so hard to close, and how to lower risk without stopping production. Read on for practical steps.
Key Takeaways
- IT–OT security gaps stem from conflicting priorities between data protection and operational safety.
- Segmentation, visibility, and cross-team alignment reduce ransomware and process disruption risk.
- Managed, OT-aware security operations help organizations mature faster with fewer mistakes.
What Is the IT–OT Security Gap?
The IT-OT security gap is the mismatch between standard cybersecurity and the protections needed for industrial control systems, highlighting the importance of advanced specialized services that bridge IT and OT expertise.
In IT, teams focus on data confidentiality and can apply patches quickly. In OT, the only priorities are keeping physical processes safe and running, often using equipment that’s 20 years old and can’t be updated. According to CISA, most industrial incidents now start with a breach in the IT network that then spreads to OT.
We’ve seen plants where modern servers sit next to PLCs installed decades ago. Applying IT tools here, like active scans or sudden patches, can literally stop production.
The gap shows up in a few key areas:
- Different risk models: IT protects data; OT protects physical safety and uptime.
- Poor OT visibility: Many teams don’t have a full list of their industrial assets.
- Insecure legacy protocols: Systems like Modbus lack basic authentication.
This separation is by design, illustrated by the Purdue Model which layers networks from the sensor (Level 0) to the corporate office (Level 5). Ignoring these boundaries makes security tools a liability instead of a safeguard.
Why Do IT and OT Security Priorities Conflict?

IT and OT security priorities conflict because their core missions are different. IT security protects data and systems, while OT security must keep physical processes safe and running. In a factory or power plant, a security change that causes a shutdown isn’t just an inconvenience, it can cost millions and risk safety.
As noted :
“Bridging the IT/OT gap isn’t just about the technology; it’s about the people and the processes. The biggest hurdle is often cultural: IT focuses on data protection, while OT focuses on physical safety and process continuity. To secure the modern enterprise, companies must move beyond the ‘air-gap’ mentality and implement a shared governance model where security is baked into the operational lifecycle from the start.” – Forbes Technology Council [1]
Common friction points include:
- Patching: IT pushes for immediate updates; OT must schedule months in advance.
- Network Access: IT enforces strict rules; OT needs predictable, uninterrupted traffic.
- Credentials: IT uses individual logins; OT often relies on shared accounts for shift work.
We’ve seen IT teams deploy an endpoint agent with good intentions, only to have it consume a PLC’s memory and halt a production line.
What Risks Emerge When IT and OT Converge?
IT-OT convergence creates significant new risks, primarily around ransomware, safety, and operational disruption, which can be mitigated using proactive OT security monitoring to track anomalies without affecting operations.
As companies connect their industrial networks for remote monitoring or data analytics, they expose previously isolated systems to the same threats that target the corporate office.
Ransomware groups now actively target these pathways because taking down a factory is more lucrative than encrypting office files.
In our incident response work, we’ve seen cases where attackers used stolen VPN credentials to move from an office laptop directly into the control network, no fancy exploit required.
The typical threats from convergence include:
- Ransomware spreading from IT servers to OT systems.
- Misconfigured firewalls that accidentally block critical control traffic.
- Unsecured remote access tools lacking multi-factor authentication.
The biggest risk isn’t a novel piece of malware. It’s the inherited exposure, bringing IT’s dynamic, connected threat landscape into an OT environment built for stability and isolation. While convergence is necessary for business, it demands disciplined security controls, monitoring, and segmentation to manage the new attack surface.
How Does Network Segmentation Reduce IT–OT Risk?
Credits: BCS Hertfordshire
Network segmentation reduces IT-OT risk by creating hard boundaries. It limits how far an attack can spread, isolating the corporate network from critical control processes. This is typically done using the Purdue Model and firewalls that understand industrial protocols.
In our work, we always start by mapping the traffic. You need to understand what normal communication looks like between a Level 3 supervisory system and a Level 4 enterprise server before you can safely build a rule to control it.
Effective segmentation follows a few best practices:
- Clear separation between the operations network (Level 3) and the enterprise IT network (Level 4).
- Industrial protocol-aware rules that allow necessary traffic but block everything else.
- One-way data flows (like data diodes) where only information can leave the OT zone, with no path back in.
Here’s a simplified view of what each level protects:
| Purdue Level | Function | Security Focus |
| Levels 0–1 | Sensors & Actuators | Safety & Integrity |
| Level 2 | Control Systems (PLCs) | Deterministic Availability |
| Level 3 | Operations Management | Controlled Access |
| Levels 4–5 | Enterprise IT | Data Protection |
When done right, it enforces least-privilege access and drastically reduces the paths an attacker can take.
Which Tools Help Bridge the IT–OT Security Gap?
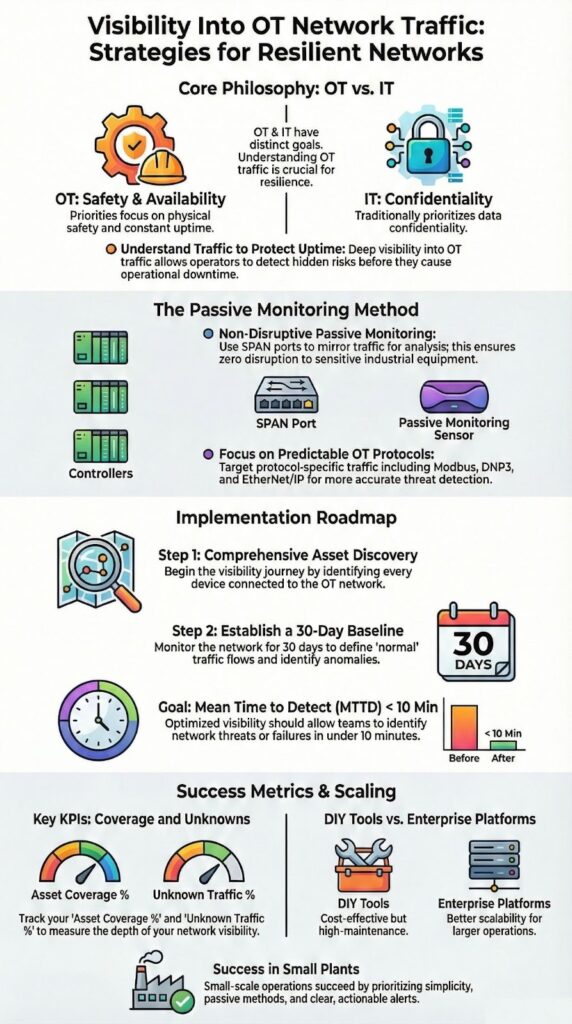
The tools that help bridge the IT-OT gap are built for visibility, not disruption. They focus on passive monitoring, watching network traffic without ever sending a packet to the fragile controllers. These tools decode industrial protocols like Modbus and DNP3, learn what “normal” traffic looks like, and flag deviations.
According to :
“As IT and OT continue to converge, it’s no longer enough to have two separate security teams with two different sets of tools. Organizations need a unified security strategy that provides visibility into both environments. This involves not only technical integration but also cultural alignment, ensuring that IT security professionals understand the unique constraints of OT, where uptime and safety are paramount.” – IBM Security [2]
The key capabilities to look for are:
- OT asset discovery that builds and maintains a live inventory.
- Baseline deviation detection to spot abnormal behavior.
- Protocol parsing that enriches logs for your SIEM.
From our product evaluations for MSSPs, we’ve seen that this passive visibility alone often uncovers 10-20% more devices than the plant’s asset list showed. That accurate inventory is the absolute starting point for any real security.
What Are the Practical Steps to Implement IT–OT Security?
Implementing IT-OT security works best with a phased, practical approach. Trying to move too fast usually backfires in these sensitive environments. Success comes from patience and planning.
We see the most progress when teams follow a clear sequence. The first step is always building an accurate, unified inventory that separates IT servers from OT controllers. You can’t protect what you don’t know you have.
From there, a practical implementation plan looks like this:
- Classify assets by their criticality to safety and production.
- Apply segmentation incrementally, starting with the boundary between IT and OT networks.
- Test all changes in a staging environment that mimics production.
Expand monitoring coverage to gain visibility into OT network traffic before enforcing stricter controls, ensuring decisions are data-driven and risk-aware.
Patching is a major hurdle, as many OT systems can’t be updated. The solution isn’t to force it, but to use compensating controls like virtual patching with intrusion prevention and strict access management. The implementation succeeds when security adapts to the realities of operations, not the other way around.
FAQ
How does IT-OT convergence security reduce real risks in industrial environments?
IT-OT convergence security reduces risk by closing visibility and response gaps between enterprise IT and operational technology systems.
When operational technology cybersecurity aligns with IT monitoring, threats cannot move unnoticed across converged networks. This approach strengthens industrial environments by supporting OT safety and availability priorities while enabling coordinated detection, response, and recovery without interrupting critical operations.
Why is OT network segmentation critical for industrial control systems protection?
OT network segmentation is critical because it limits attacker movement inside industrial control systems. Purdue model segmentation and microsegmentation industrial networks separate critical processes from less trusted zones.
This structure reduces ransomware OT protection risks, contains breaches faster, and helps prevent OT process disruption while keeping production systems reliable and controlled.
What challenges make legacy OT systems security harder to manage today?
Legacy OT systems security is difficult because many devices were not designed for modern cybersecurity controls. IT security patching OT constraints, unsupported software, and insecure protocols increase exposure.
These IT OT integration challenges require compensating controls, virtual patching OT systems, and disciplined OT change management to reduce risk without causing downtime.
How can organizations improve visibility using OT asset inventory management?
OT asset inventory management improves visibility by identifying every device, connection, and protocol on OT networks. Asset discovery OT networks combined with passive OT monitoring tools reduce operational risk.
Accurate inventories support baseline deviation detection OT, strengthen OT vulnerability management automation, and enable informed security and operational decisions.
What skills and processes help bridge the IT-OT security gap long term?
Bridging the IT-OT security gap requires coordinated skills development and shared processes. Cross-training IT OT teams reduces cybersecurity knowledge gaps and improves communication.
OT engineer training programs, unified incident response OT IT, and clear OT security governance frameworks create consistent practices that strengthen security without compromising operational reliability.
Bridging the IT–OT Security Gap for Long-Term Resilience
Bridging the IT-OT gap means managing convergence safely, not forcing it. Respect OT constraints, invest in passive visibility, and align your teams to cut risk and avoid disruption. The lessons from past incidents remain critical.
Achieving resilience requires deliberate action and the right support.
Need a partner to guide you?
Talk to our OT security specialists
We offer vendor-neutral consulting to help MSSPs select the right tools and build a resilient, aligned security program.
References
- https://www.forbes.com/sites/forbestechcouncil/2024/05/22/why-itot-convergence-is-the-next-frontier-for-cybersecurity/
- https://www.ibm.com/blog/bridging-the-it-ot-divide-a-unified-approach-to-industrial-cybersecurity/
